Short Summary:
The ReasonLabs Research Team has identified a widespread polymorphic malware campaign known as the Extension Trojan, which forcefully installs malicious extensions on users’ browsers, affecting over 300,000 Google Chrome and Microsoft Edge users. The campaign has been linked to various domains and IP addresses, with significant findings regarding the indicators of compromise (IoCs) associated with the threat.
Key Points:
- The Extension Trojan installs adware extensions and sophisticated scripts to steal private data.
- At least 300,000 users have been affected across Google Chrome and Microsoft Edge.
- Research uncovered 84 email-connected domains and 28 IP addresses, with 24 identified as malicious.
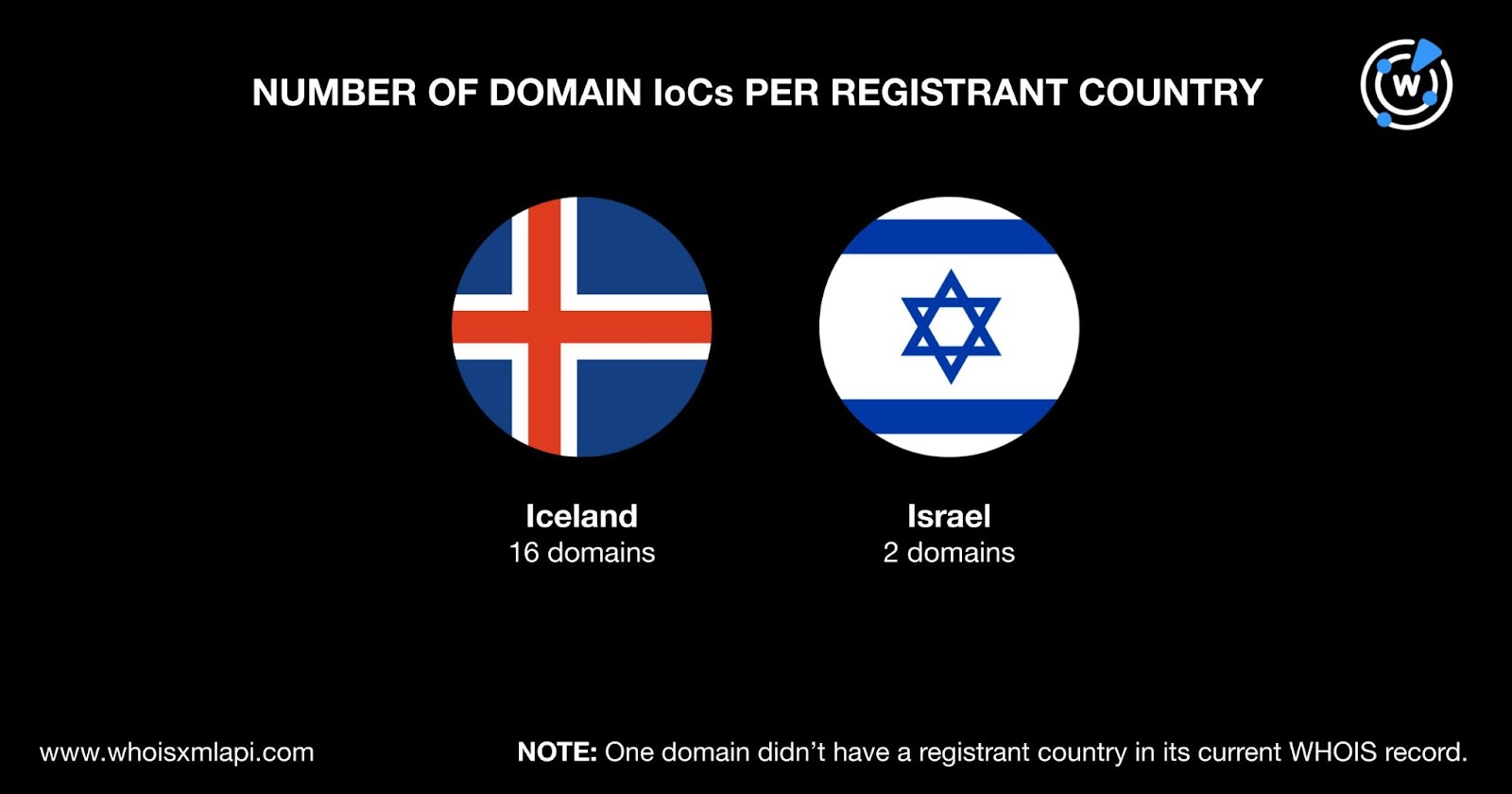
- 19 out of 22 IoCs had public WHOIS records; most domains were registered in Iceland.
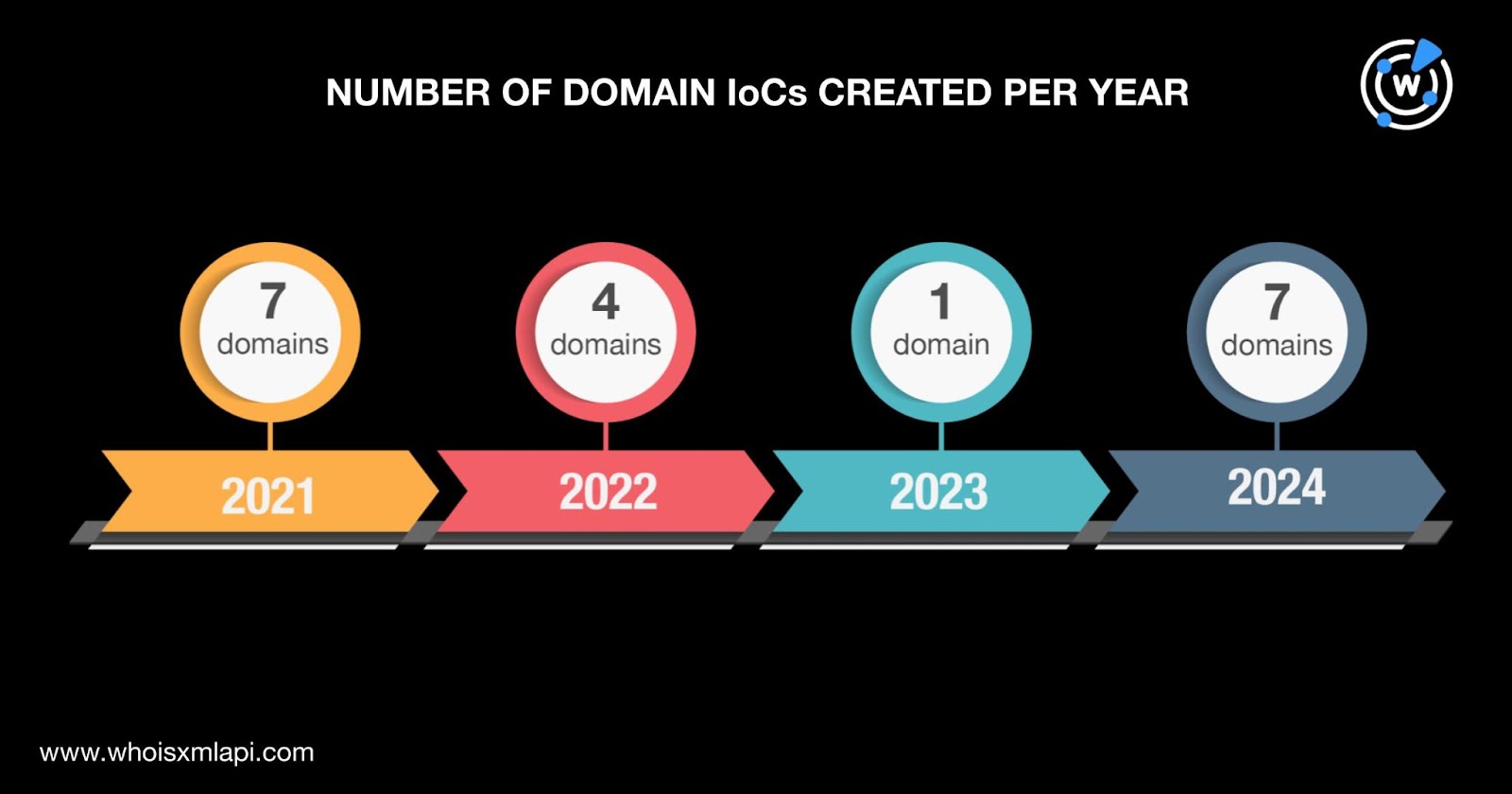
- The threat actors used newly registered domains since 2021, with multiple domains created in 2021 and 2024.
- Additional artifacts related to the IoCs are available for download from the research team’s website.
MITRE ATT&CK TTPs – created by AI
- Initial Access (T1071.001)
- Use of malicious browser extensions to gain initial access to user systems.
- Execution (T1203)
- Execution of malicious scripts delivered through browser extensions.
- Credential Access (T1003)
- Stealing private data through malicious extensions.
- Command and Control (T1071)
- Utilizing compromised domains for command and control communications.
- Exfiltration (T1041)
- Exfiltration of sensitive data through malicious extensions.
The ReasonLabs Research Team uncovered a new widespread polymorphic malware campaign that forcefully installed extensions on users’ systems. The Trojan comes in various forms ranging from simple adware extensions that hijack searches to more sophisticated malicious scripts that deliver local extensions to steal private data and execute various commands. The Extension Trojan has reportedly already affected at least 300,000 Google Chrome and Microsoft Edge users.
How far does the reach of the Extension Trojan campaign go in the DNS? The WhoisXML API research team sought to find out by expanding a list of 22 domains identified as indicators of compromise (IoCs). Our DNS deep dive led to the discovery of:
- 84 email-connected domains
- 28 IP addresses, //24 of which turned out to be malicious
- 38 string-connected domains
A sample of the additional artifacts obtained from our analysis is available for download from our website.
More Information about the IoCs
As per usual, we began our analysis by attempting to know more about the IoCs. We queried the 22 domains tagged as IoCs on Bulk WHOIS Lookup and found that:
- Only 19 of them had public current WHOIS record data.
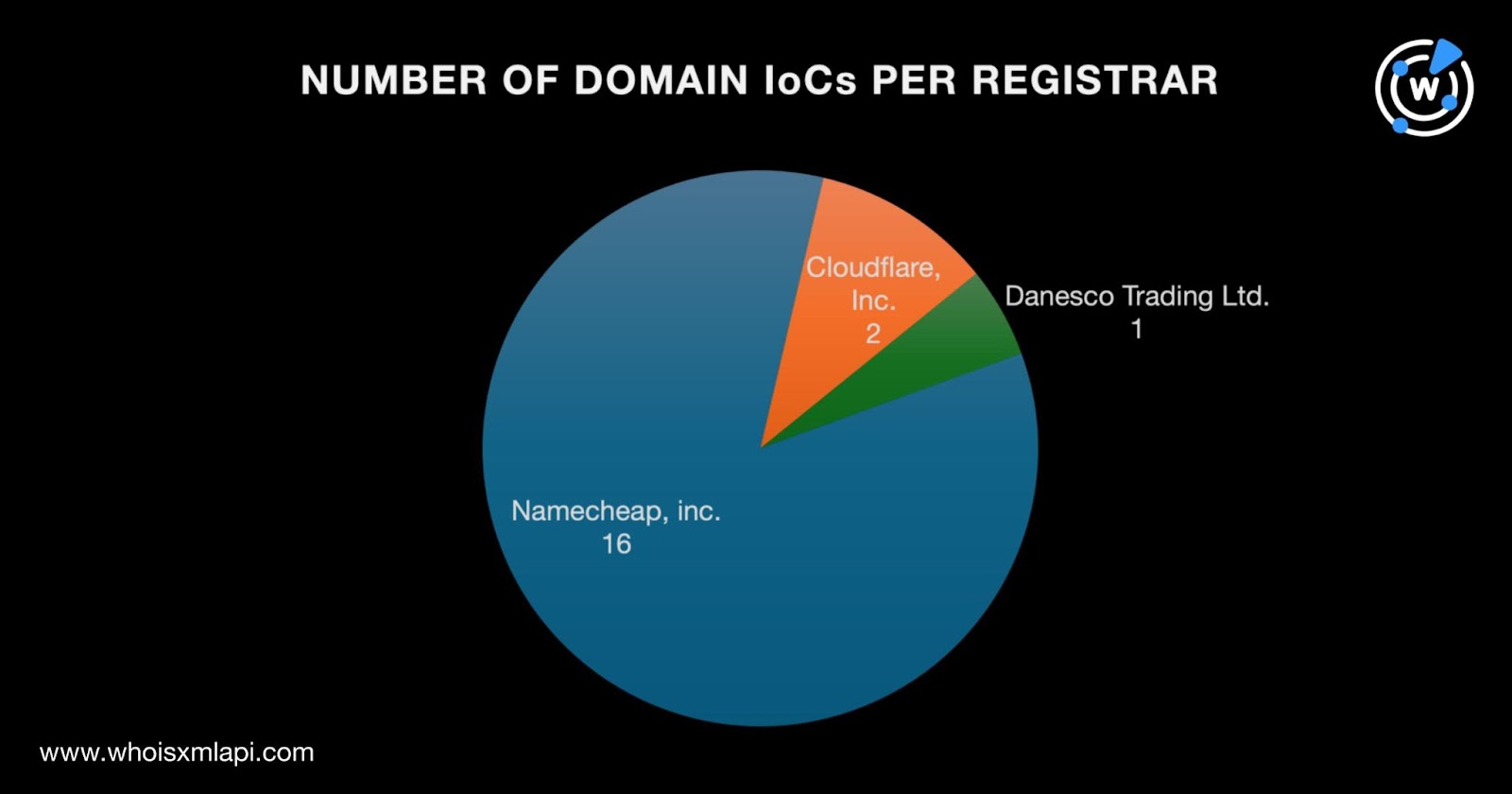
- Namecheap, Inc. was the top registrar, accounting for 16 domain IoCs. The three remaining IoCs were split among two other registrars—Cloudflare, Inc. administered two while Danesco Trading Ltd. managed one.
-
The threat actors used domains newly registered when they were weaponized starting in 2021 around the time the trojan was first seen. Seven domain IoCs each were created in 2021 and 2024. Four were created in 2022 and one in 2023.
-
A majority of the domain IoCs, 16 to be exact, were registered in Iceland. Two were registered in Israel and one didn’t have a registrant country in its current WHOIS record.
IoC List Expansion Results
In a bid to find more artifacts possibly connected to the Extension Trojan, we queried the 20 domains identified as IoCs on WHOIS History API. That led to the discovery of 26 email addresses in their historical WHOIS records, four of which were public.
Querying the four public email addresses on Reverse WHOIS API allowed us to uncover 84 email-connected domains after filtering out duplicates and the IoCs.
Next, we subjected the 20 domain IoCs to DNS lookups that provided us with 28 IP addresses. Threat intelligence lookups for them showed that 24 were associated with various threats. Take a look at five examples below.
| MALICIOUS IP ADDRESS | ASSOCIATED THREAT TYPE |
|---|---|
| 104[.]21[.]3[.]7 | Attack Malware Phishing Suspicious |
| 104[.]21[.]17[.]222 | Generic Malware Phishing |
| 104[.]21[.]24[.]148 | Malware Phishing |
| 172[.]67[.]129[.]252 | Attack Malware Phishing Suspicious |
| 104[.]21[.]32[.]227 | Attack Generic Phishing |
This post only contains a snapshot of the full research. Download the complete findings and a sample of the additional artifacts on our website or contact us to discuss your intelligence needs for threat detection and response or other cybersecurity use cases.
Disclaimer: We take a cautionary stance toward threat detection and aim to provide relevant information to help protect against potential dangers. Consequently, it is possible that some entities identified as “threats” or “malicious” may eventually be deemed harmless upon further investigation or changes in context. We strongly recommend conducting supplementary investigations to corroborate the information provided herein.
Source: Original Post