This article details a SOC investigation uncovering a sophisticated web shell employed by Chinese-speaking threat actors. The analysis reveals the web shell’s capabilities as a lightweight exploitation framework and outlines practical detection strategies for security teams. Affected: government infrastructure, web servers, Chinese-speaking threat actors
Keypoints :
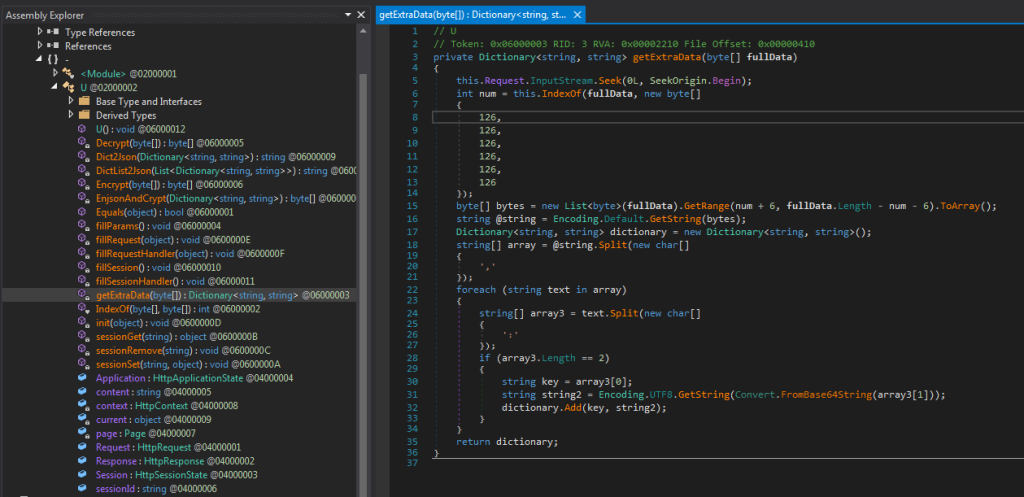
- Web shells have evolved beyond basic command execution to include lightweight exploitation capabilities.
- Investigation revealed detection of a web shell on a Southeast Asian government’s SharePoint server.
- The attackers exploited the web server using a pre-existing web shell or command injection vulnerability.
- Utilized Bashupload for downloading malicious ASPX payloads disguised as 404 pages.
- The incident involved privilege escalation using various Potato tool variants.
- Memory-based payloads can evade traditional signature-based malware detection.
- Continuous learning and proactive threat hunting are essential for security teams.
- YARA rules can be utilized to identify additional malicious samples on platforms like VirusTotal.
MITRE Techniques :
- T1071.001 – Application Layer Protocol: The attackers used standard protocols for C2 communication.
- T1203 – Exploitation for Client Execution: A web shell was deployed through exploiting the SharePoint server.
- T1210 – Exploitation of Remote Services: Command injection vulnerability was utilized to execute commands remotely.
- T1053.001 – Scheduled Task/Job: The attackers potentially used scheduled tasks to execute additional exploits.
- T1068 – Exploitation of Privilege Escalation: Potato tools were leveraged for gaining elevated system privileges.
Indicator of Compromise :
- [MD5] 0xEF153E1E216C80BE3FDD520DD92526F4 (GodPotato)
- [MD5] 0xB8A468615E0B0072D2F32E44A7C9A62F (BadPotato)
- [MD5] 0xB5755BE4AAD8D8FE1BD0E6AC5728067B (SweetPotato)
- [MD5] 32865229279DE31D08166F7F24226843 (BasicInfo.dll)
- [MD5] 0xAA3ACD65232F65C2991061078F33D7C6 (FileOperation.dll)
Full Story: https://securelist.com/soc-files-web-shell-chase/115714/