This article discusses the advanced obfuscation and multi-layer encryption techniques employed by Xloader versions 6 and 7 to evade detection and complicate analysis by security professionals. The malware utilizes decoy C2 servers and complex algorithms for command-and-control communication. Affected: organizations, cybersecurity sector
Keypoints :
- Xloader versions 6 and 7 employ advanced code and data obfuscation techniques.
- The malware utilizes hardcoded decoy lists for blending C2 communications with legitimate traffic.
- Decoy and real C2 servers are encrypted with different keys and algorithms.
- Both versions share the same network protocol protected by multiple layers of encryption.
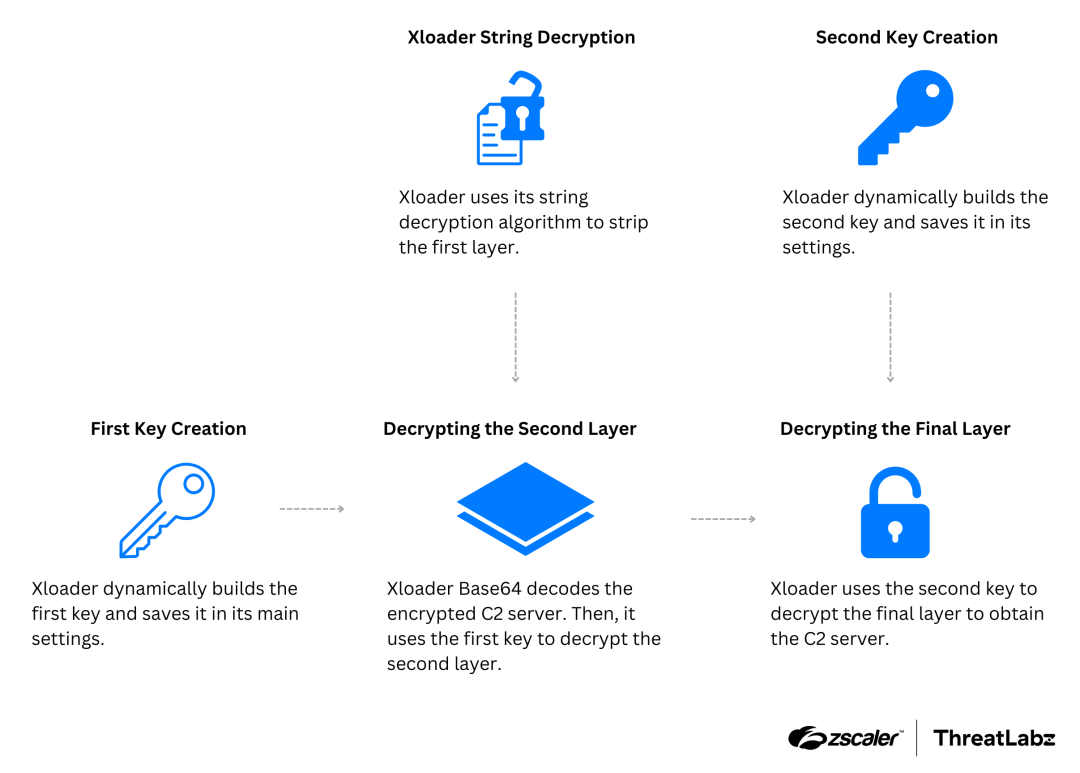
- Xloader’s decryption methods for C2 servers involve complex algorithms and dynamic key generation.
- Newer versions allow the differentiation of C2 URLs and paths.
- The malware continues to be a significant threat due to its evolving capabilities.
- Zscaler’s platform can detect Xloader and similar threats effectively.
MITRE Techniques :
- Data Encrypted (T10240): Xloader applies multiple layers of encryption to conceal C2 data.
- Obfuscated Files or Information (T1027): The malware obfuscates code to prevent analysis.
- Command and Control over C2 (T1071): Xloader uses decoy and real servers for C2 communications.
- Multi-layered Encryption (T1161): The malware implements various encryption techniques for different layers.
Indicator of Compromise :
- SHA-256 66ebf028ab0f226b6e4c6b17cec00102b1255a4e59b6ae7b32b062a903135cc9 (Xloader version 6)
- SHA-256 88909cd27a422da91a651e87f493d16beff1f0e03adcc035f2835a2a25e871e7 (Xloader version 6)
- SHA-256 ad101eef336dc2467ffaf584b272aa82f26711bfba4e2e29e8ad7c6d62bc6ae (Xloader version 7)
- SHA-256 62207c53645346df6f36cf3f7792e5fc4655895b35a6e3477e218e0e0007be9 (Xloader version 7)
- Domain www.iwin[.]exposed (Real C2)
Full Story: https://www.zscaler.com/blogs/security-research/technical-analysis-xloader-versions-6-and-7-part-2