Summary: The video discusses the rise of AI technologies and how one individual, Robert, created a home-based infrastructure to host various AI models without relying on cloud services. By utilizing his own computer setup, he effectively integrates AI to assist with personal tasks while maintaining control over his data and ensuring security.…
Read More Tag: WINDOWS

Summary: The Acronis Threat Research Unit (TRU) analyzed a complex malware delivery chain demonstrating the use of multiple scripting languages and obfuscation techniques, leading to the deployment of high-profile malware such as DCRat. The infection starts with a deceptive email attachment, escalating through a multi-stage process involving Visual Basic Script, batch files, and PowerShell.…
Read More
Summary: TRUeSentire’s Threat Response Unit has identified an advanced KoiLoader malware intrusion attempting to compromise systems through a phishing email. The attack leverages misleading file formats, manipulates PowerShell commands, and employs multiple anti-detection techniques to deploy the Koi Stealer for extensive data theft. KoiLoader exemplifies sophisticated malware engineering, utilizing custom cryptographic channels for Command and Control (C&C) operations.…
Read More 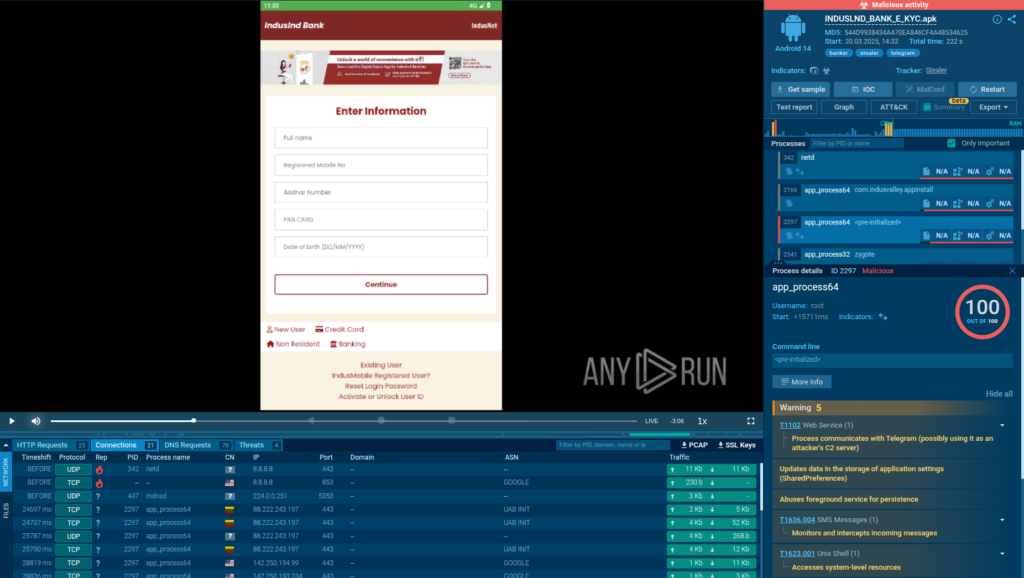
The report discusses Salvador Stealer, a new Android malware posing as a banking application to steal sensitive user data, such as banking credentials and personal information. The malware employs phishing techniques and has multiple methods for exfiltrating data, including SMS interception and real-time communication with a Command and Control (C2) server via Telegram.…
Read More 
In late January 2025, an MSP administrator fell victim to a sophisticated phishing email that mimicked an authentication alert for a remote management tool, leading to a ransomware attack by Qilin actors. This incident emphasizes the vulnerabilities faced by MSPs and their clients to phishing campaigns.…
Read More 
Summary: A new China-linked cyber threat actor, Earth Alux, has emerged, targeting sectors such as government, technology, and telecommunications in the APAC and LATAM regions. This group utilizes sophisticated methods and a diverse toolkit, including the VARGEIT and COBEACON backdoors, to exploit vulnerabilities and maintain long-term access to compromised systems.…
Read More 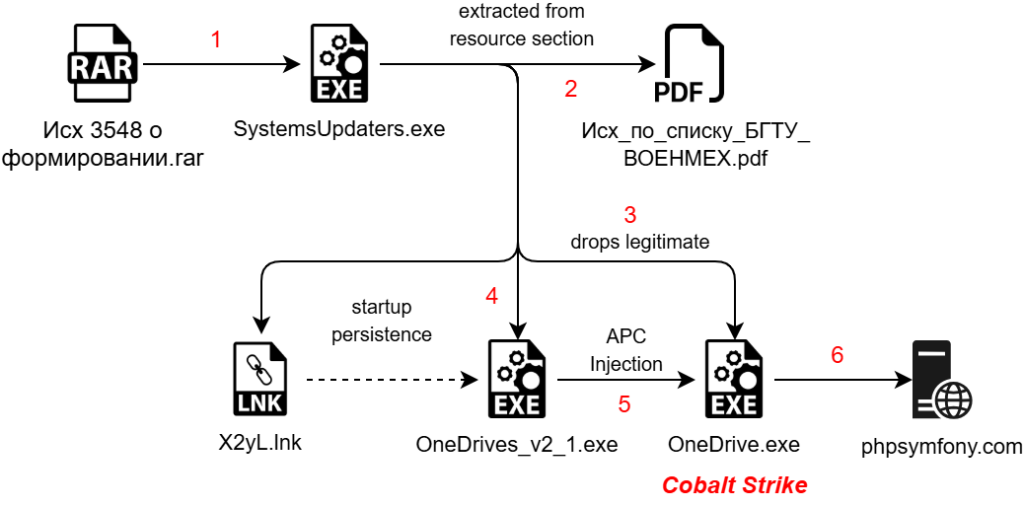
The article discusses Operation HollowQuill, a targeted cyber campaign against the Baltic State Technical University, designed to infiltrate academic and defense networks through weaponized decoy documents. The attack utilizes a multi-stage infection chain, including a malicious RAR file, a .NET malware dropper, Golang shellcode, and a Cobalt Strike payload.…
Read More 
Summary: A recent Intrinsec report highlights the operations of Russian-aligned intrusion sets UAC-0050 and UAC-0006, which are conducting spam campaigns motivated by financial theft and cyber espionage targeting Ukraine and its allies. Their activities include a mix of phishing, malware delivery, and psychological warfare, utilizing resilient infrastructure linked to shadowy hosting providers.…
Read More 
Summary: Trend Micro has uncovered Earth Alux, a sophisticated China-linked APT group targeting strategic sectors in the Asia-Pacific and Latin America. Utilizing advanced tools like the VARGEIT backdoor and COBEACON, they execute cyber-espionage with minimal detection, emphasizing the threat to sensitive data across various industries. The group’s operations highlight a growing emphasis on maintaining persistent access while employing complex evasion tactics.…
Read More 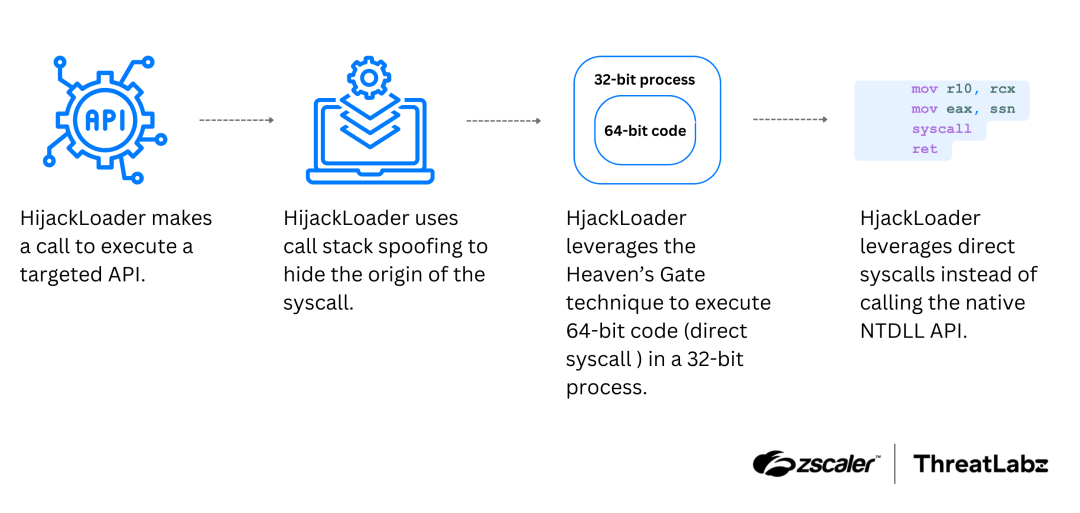
HijackLoader is a modular malware loader discovered in 2023, capable of delivering payloads and employing various evasion techniques. Recently uncovered modules feature advanced tactics such as call stack spoofing, virtual machine detection, and persistence through scheduled tasks. Affected: malware, cybersecurity sector, antivirus software
Read More Keypoints :
HijackLoader is a malware downloader first identified in 2023, continually receiving updates.…
Summary: A long-running Russian hacking group, Gamaredon, is reportedly behind a campaign aimed at installing a surveillance tool on Ukrainian computers through phishing emails. This campaign has been active since at least November 2024 and leverages themes related to the Ukraine invasion to lure victims. The malicious tool deployed, Remcos, allows unauthorized access and data collection from infected systems.…
Read More 
Summary: A Russian hacking group known as Water Gamayun is exploiting a Microsoft Windows vulnerability (CVE-2025-26633) to deliver the backdoors SilentPrism and DarkWisp. The group uses malicious provisioning packages and signed .msi files to execute commands and steal sensitive data. Their operations have evolved, utilizing sophisticated methods for persistence, command and control, and stealthy data exfiltration.…
Read More 
Summary: The North Korean Lazarus hacking group has innovated its attack techniques, now employing ‘ClickFix’ tactics to target job seekers in the cryptocurrency sector, specifically in centralized finance roles. This method, part of an ongoing campaign known as ‘Contagious Interview,’ utilizes fake website errors to prompt victims to download malware disguised as legitimate fixes.…
Read More 
Summary: Apple has been fined €150 million by French regulators for anticompetitive practices related to its App Tracking Transparency (ATT) tool. The French Competition Authority found that Apple’s implementation of ATT created an unfair market advantage, harming smaller app publishers dependent on third-party data collection. Despite the fine, which is minor compared to Apple’s revenues, the regulation did not require Apple to make changes to the tool.…
Read More 
Summary: The Moscow subway system faced service disruptions on Monday, which may be linked to a cyberattack, as suggested by a message displayed on its website that mimicked a prior incident with Ukraine’s railway operator. While the transport department cited technical maintenance as the cause, passengers struggled to recharge their subway cards and experienced app malfunctions.…
Read More 
Summary: Threat actors are exploiting the “mu-plugins” directory in WordPress sites to conceal malicious code for persistent remote access and redirecting visitors to fake sites. Three types of rogue PHP scripts found in this hidden directory can execute arbitrary code, inject spam, and deceive users into downloading malware.…
Read More 
The Sandworm Team, a destructive threat group linked to Russia’s military intelligence, has displayed a new trend by using an ASPX web shell in 2024. This web shell, while simple, allows for various malicious activities such as executing system commands, managing files, and creating firewall rules.…
Read More 
Summary: A recent phishing campaign targeting Ukrainian entities has been identified, utilizing social engineering techniques to distribute the Remcos RAT trojan. This campaign, attributed to the Russian hacking group Gamaredon, uses deceptive files related to military movements to trick victims. The campaign highlights ongoing cyber espionage efforts associated with Russian Intelligence Services against Ukraine.…
Read More 
Summary: This week’s cybersecurity insights highlight vulnerabilities in widely used systems like Chrome and Kubernetes, as well as emerging threats from phishing-as-a-service operations. The coverage includes data leaks, ransomware trends, and the importance of vigilance against common oversights that can lead to security breaches. Additionally, the impact of recent legal cases and developments in AI-driven cyber threats are discussed.…
Read More 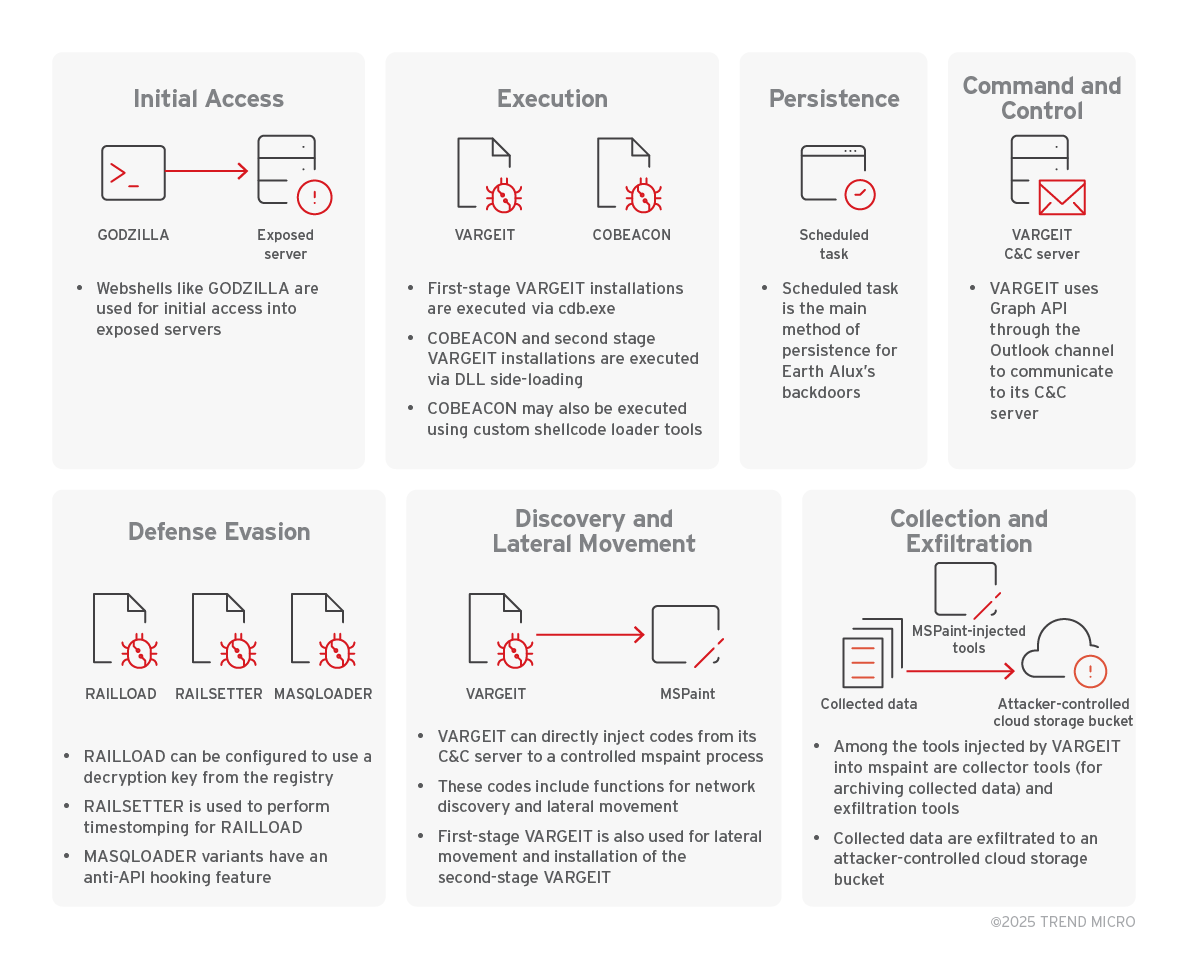
The cyberespionage group Earth Alux, linked to China, employs sophisticated techniques to target critical sectors in the Asia-Pacific (APAC) and Latin America. Their primary backdoor, VARGEIT, facilitates stealthy data exfiltration, affecting vital industries including government, technology, and logistics. To mitigate the risks of such cyber threats, organizations should adopt proactive security measures.…
Read More  Weekly Recap: Chrome 0-Day, IngressNightmare, Solar Bugs, DNS Tactics, and More
Weekly Recap: Chrome 0-Day, IngressNightmare, Solar Bugs, DNS Tactics, and More