A new variant of XCSSET malware has been discovered, which is specifically designed to infect macOS Xcode projects. This sophisticated malware utilizes advanced obfuscation, updated persistence techniques, and novel infection strategies to exfiltrate sensitive information, including digital wallet data. It operates in a stealthy manner, often remaining fileless, which complicates detection and removal efforts.…
Read More 





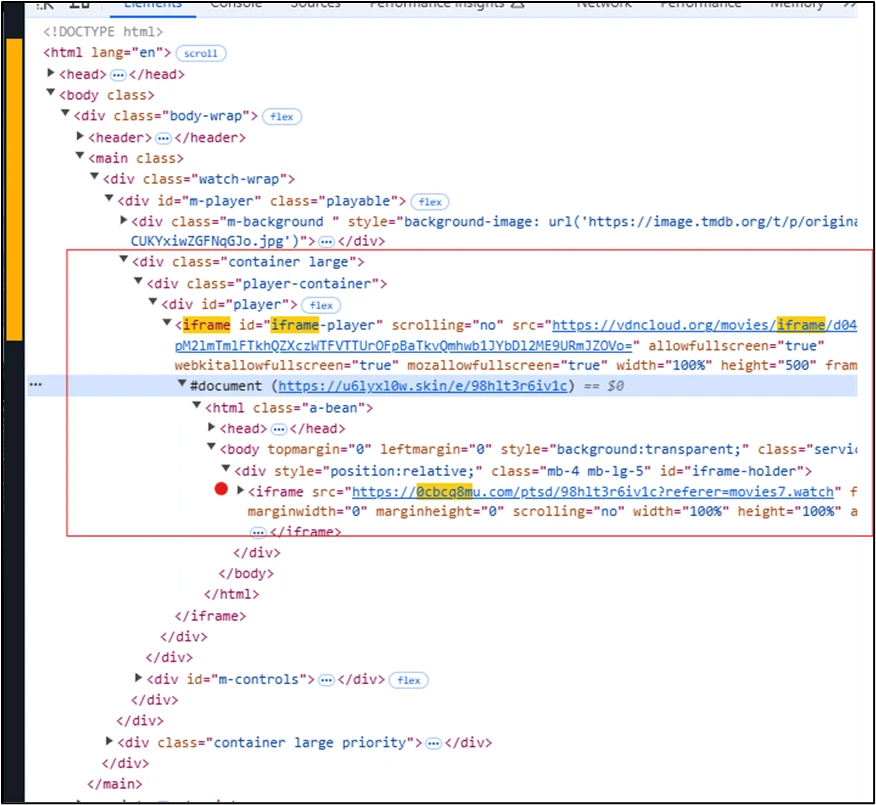
![Microsoft Warns of ClickFix Phishing Campaign Targeting Hospitality Sector via Fake Booking[.]com Emails Microsoft Warns of ClickFix Phishing Campaign Targeting Hospitality Sector via Fake Booking[.]com Emails](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEhM5jI8FVP1tzJaKIu8nlTdOmjGyA2IQAKVRihrTXOM7K3WCMjugET571ivv6PB_-jdsJPrBN7f34R9uF-8JohBpF8ZSey7ZTRmgdpQ8OZ9JwvpBAJujhuOH6zCidExabNOyw2uD7cCscTHAJtzEGLI4KHjHcUbvAunnpfIlm8HjBZVkXPBCCIguGoOfKCB/s728-rw-e365/storm.png)