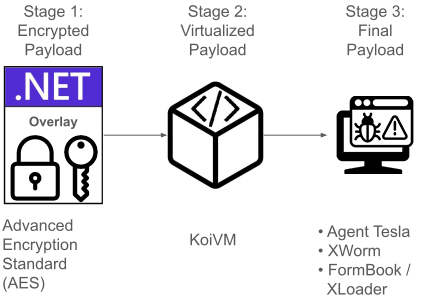
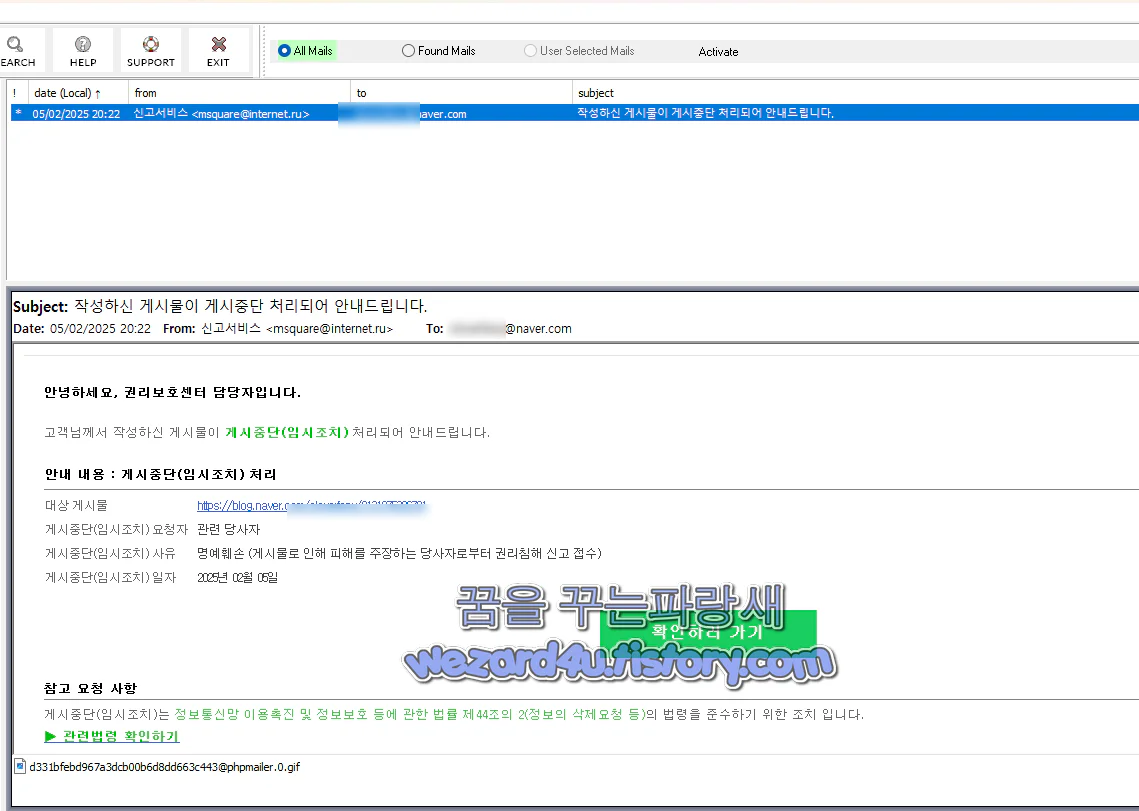
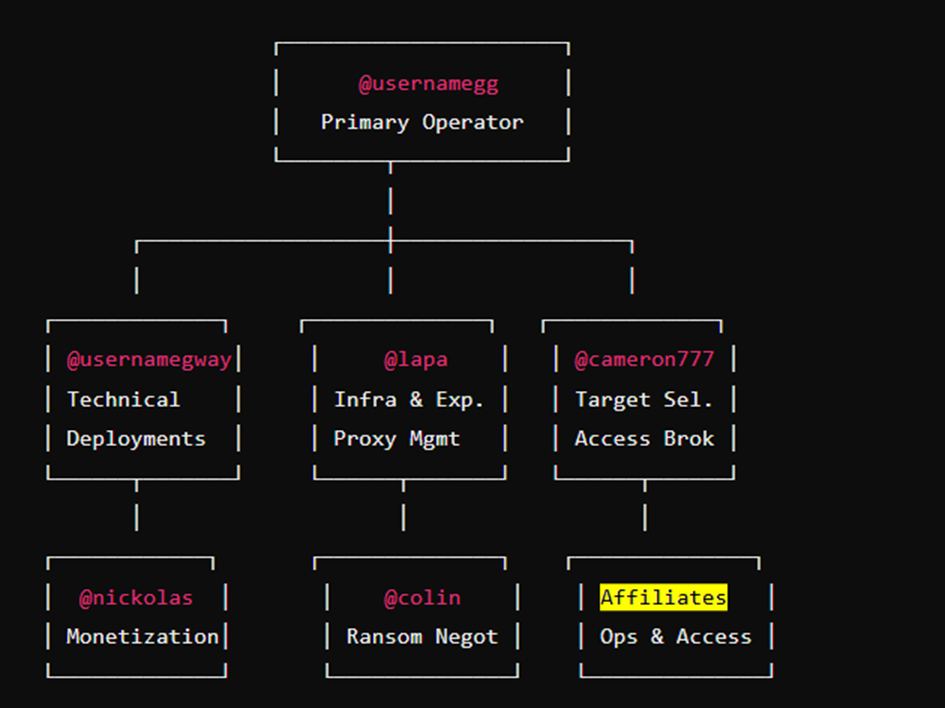
Summary: This week’s cybersecurity insights highlight vulnerabilities in widely used systems like Chrome and Kubernetes, as well as emerging threats from phishing-as-a-service operations. The coverage includes data leaks, ransomware trends, and the importance of vigilance against common oversights that can lead to security breaches. Additionally, the impact of recent legal cases and developments in AI-driven cyber threats are discussed.…
Read More  Weekly Recap: Chrome 0-Day, IngressNightmare, Solar Bugs, DNS Tactics, and More
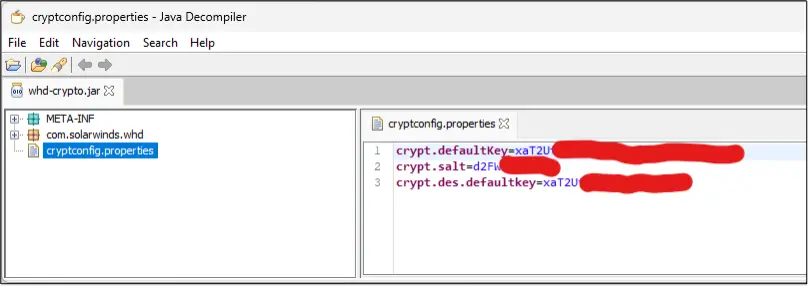
Weekly Recap: Chrome 0-Day, IngressNightmare, Solar Bugs, DNS Tactics, and More