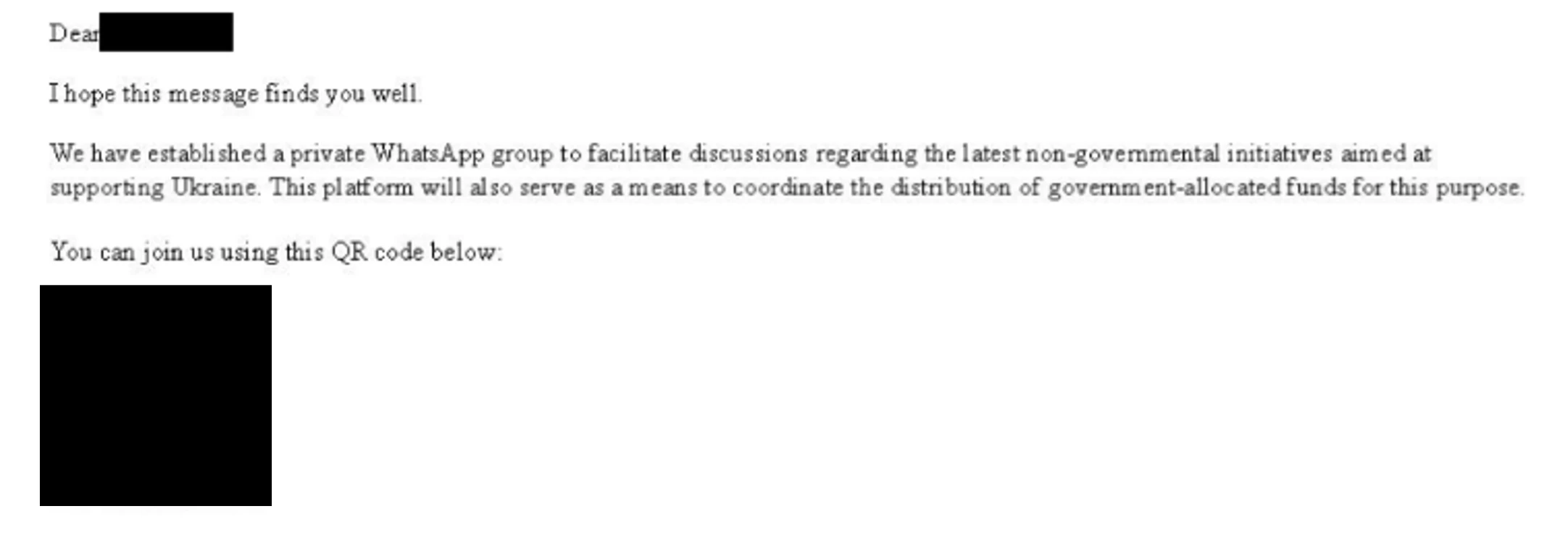
In mid-November 2024, Microsoft Threat Intelligence reported a shift in tactics by the Russian threat actor Star Blizzard, who began targeting WhatsApp accounts through spear-phishing campaigns. This new approach involves impersonating US government officials to lure victims into malicious links that compromise their WhatsApp data. The campaign highlights the actor’s resilience and adaptability in the face of operational disruptions.…
Read More









![⚡ THN Weekly Recap: Top Cybersecurity Threats, Tools and Tips [13 January] ⚡ THN Weekly Recap: Top Cybersecurity Threats, Tools and Tips [13 January]](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEh-GVBzJbXbnB628INcZeeGpxnFqxVpcaOaQnUH-g2FpiUGHCsUnPnPNYeuEKDvxOqHzeiB2fZWoNTOO81_P4b77zyyyuaSpWTBjahKirJJMtMXCEIvVUiqsIojlnyGL9pPkB8Dv5-wviS5poLJ_CIYdbkSxjPE4Psyh6mppkjg0M4rWF22fNSR9IgRUqwh/s728-rw-e365/recap.png)