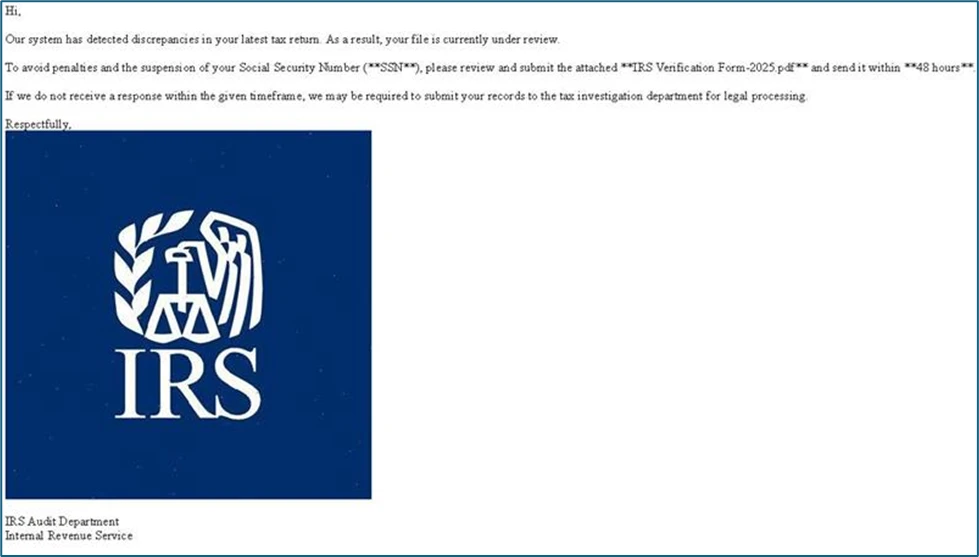
This report outlines various global cybersecurity incidents, including sophisticated spyware targeting Tibetan and Taiwanese communities, scrutiny over Bangladesh’s Cyber Security Act, a DDoS attack on Indonesia’s Tempo.co, and breaches in Australia’s superannuation sector. Other highlights include malware threats in various regions and ongoing efforts to enhance cybersecurity across nations.…
Read More