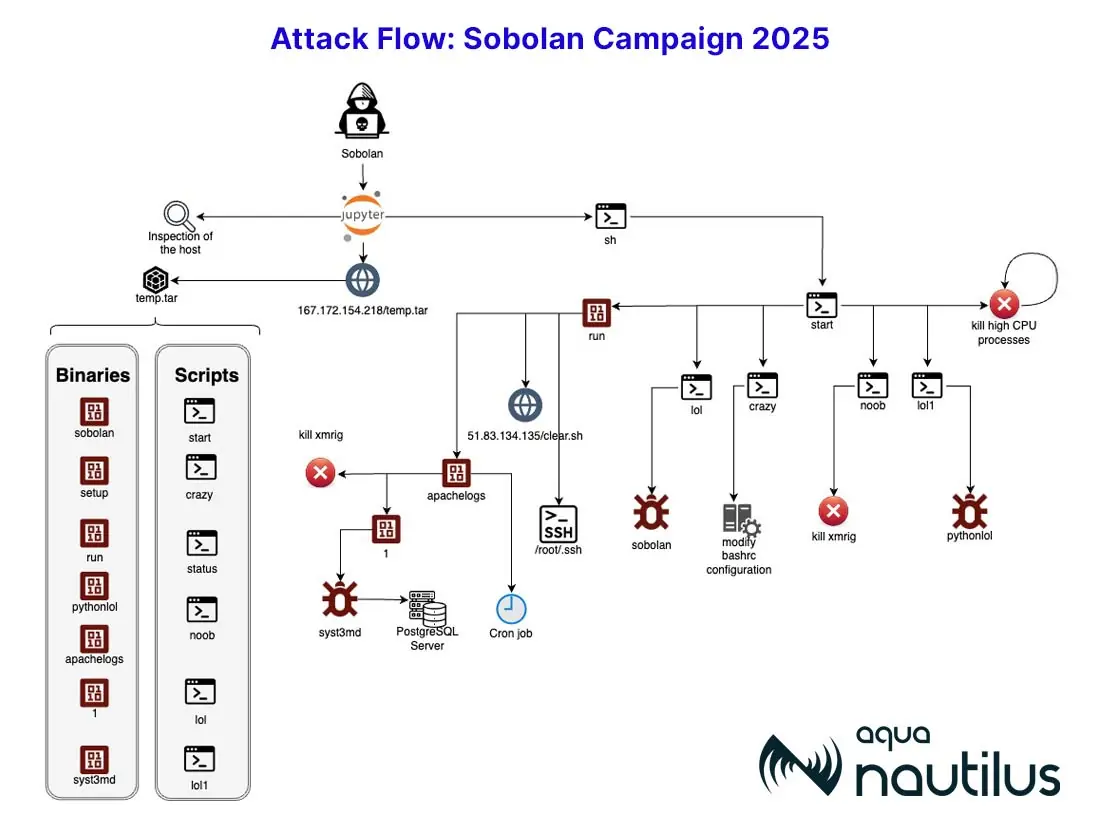
Summary: Grafana path traversal vulnerabilities have been exploited as part of a larger campaign targeting server-side request forgery (SSRF) flaws across multiple platforms, according to GreyNoise. Over 400 IP addresses have been identified as orchestrating these coordinated attacks, reflecting potential automation in their exploitation strategies. The attacks primarily focused on entities in specific countries, suggesting a directed effort in reconnaissance and exploitation of vulnerabilities.…
Read More 





 Cyber Attack Chronicles
Cyber Attack Chronicles