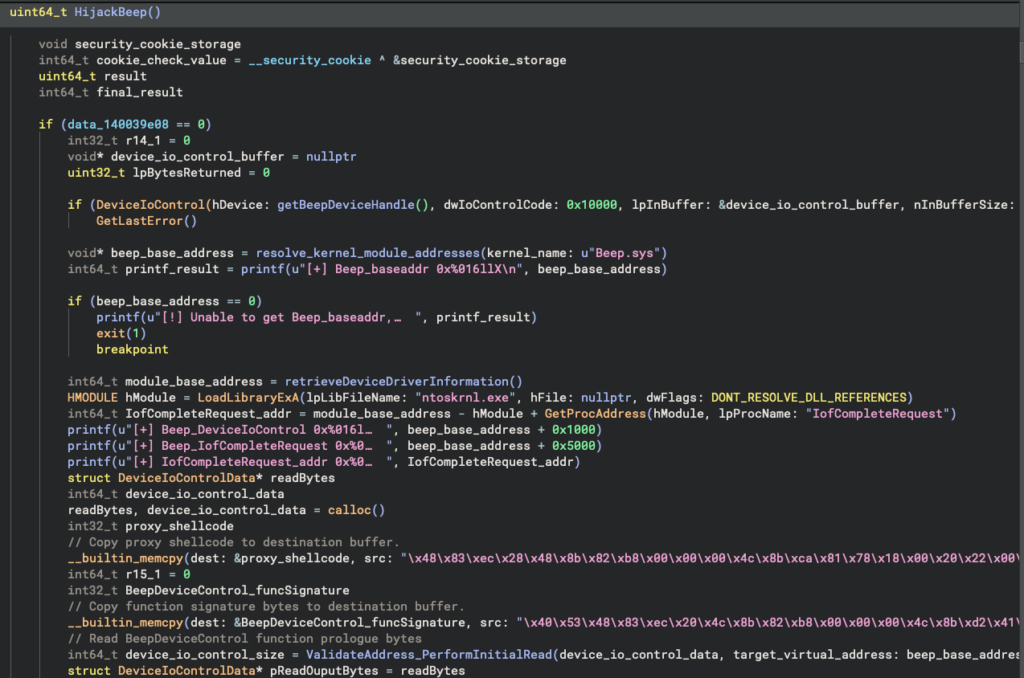
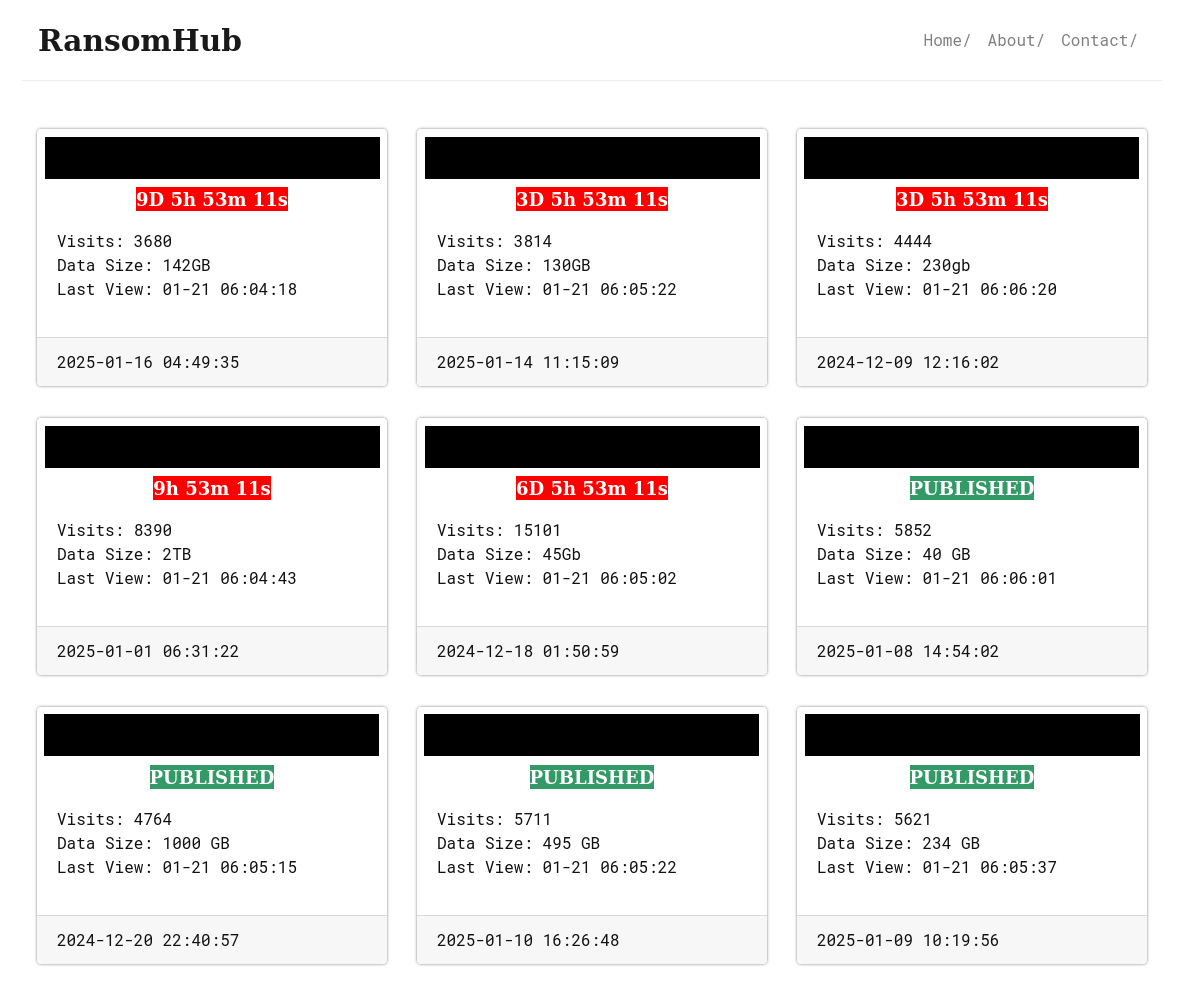
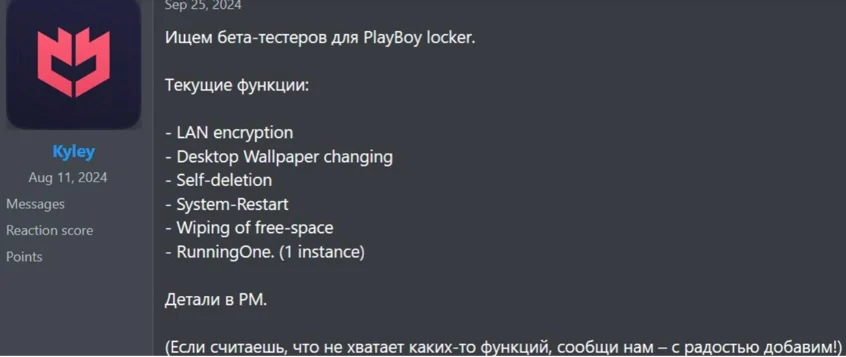
Summary: The Hunters International Ransomware-as-a-Service operation is transitioning to an extortion-only model named “World Leaks” due to declining profitability and increased scrutiny. Launched as of January 1, 2025, this new operation utilizes a self-developed exfiltration tool to automate data theft. Despite its rebranding, the group remains heavily involved in cybercrime, previously claiming over 280 attacks against various organizations.…
Read More