Keypoints :
Single-page applications (SPAs) are popular for their dynamic interfaces but can introduce security vulnerabilities.…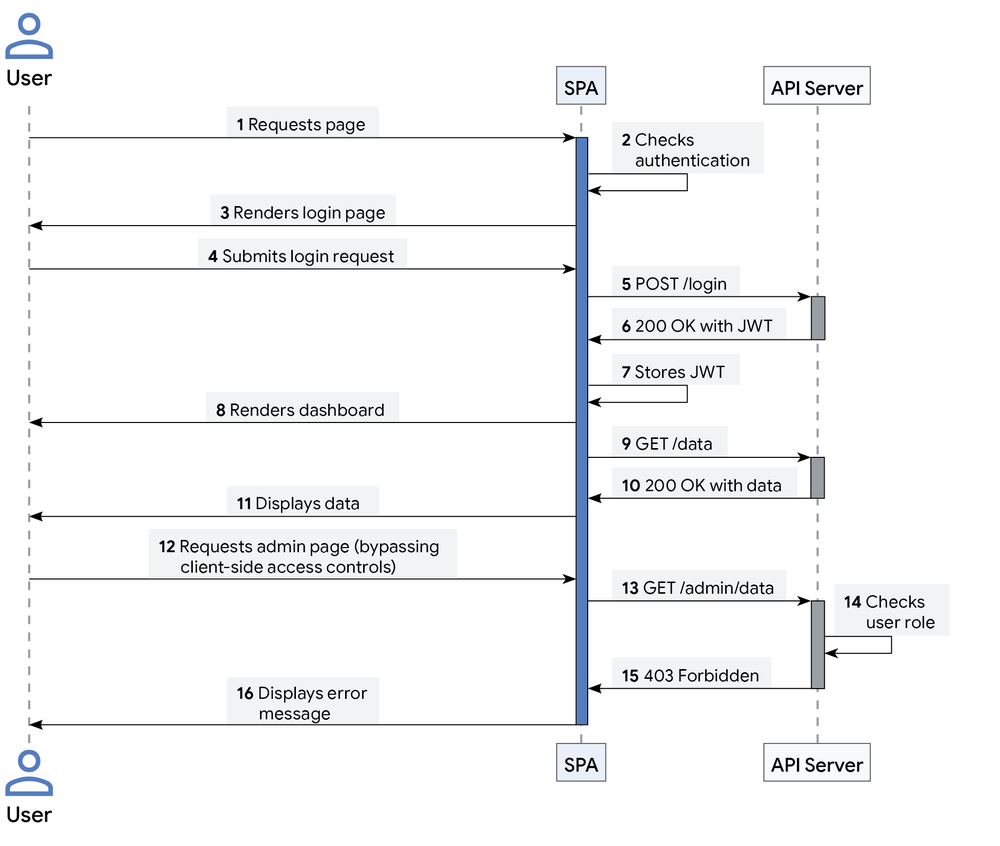
Keypoints :
Single-page applications (SPAs) are popular for their dynamic interfaces but can introduce security vulnerabilities.…

![⚡ THN Weekly Recap: Top Cybersecurity Threats, Tools and Tips [13 January] ⚡ THN Weekly Recap: Top Cybersecurity Threats, Tools and Tips [13 January]](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEh-GVBzJbXbnB628INcZeeGpxnFqxVpcaOaQnUH-g2FpiUGHCsUnPnPNYeuEKDvxOqHzeiB2fZWoNTOO81_P4b77zyyyuaSpWTBjahKirJJMtMXCEIvVUiqsIojlnyGL9pPkB8Dv5-wviS5poLJ_CIYdbkSxjPE4Psyh6mppkjg0M4rWF22fNSR9IgRUqwh/s728-rw-e365/recap.png)
Threat Actor: UNC5337 | UNC5337 Victim: Ivanti | Ivanti
Key Point :
A critical vulnerability in Ivanti Connect Secure appliances has been exploited as a zero-day, allowing for remote code execution.…

Keypoints :
Multiple vulnerabilities discovered in Ivanti products. Most severe vulnerability allows for remote code execution.…
_Igor_Stevanovic_Alamy.jpg?disable=upscale&width=1200&height=630&fit=crop)
Threat Actor: (insider threat) | insider threat Victim: (organizations) | organizations
Key Point :
LCNC and RPA tools can introduce vulnerabilities due to lack of centralized control and oversight.…
Threat Actor: Cybercriminals | cybercriminals Victim: Organizations using Argo Workflows | organizations using Argo Workflows
Key Point :
Default Unauthenticated Access: Many instances lack authentication, allowing unrestricted access to workflows.…Description : [AI generated] Molars.co.ke is a dental practice based in Nairobi, Kenya. The company offers a wide range of oral health services such as general dentistry, orthodontics, and oral surgery, among others.…
Summary: The U.S. Department of Health and Human Services has proposed new cybersecurity requirements for healthcare organizations to enhance protections for electronic patient data against increasing cyber threats. This initiative aims to amend HIPAA regulations to better safeguard sensitive health information and ensure rapid recovery from cyber incidents.…
Keypoints :
FireScam is an information-stealing malware with spyware capabilities.…Description : [AI generated] The website “asjp.cerist.dz” is associated with the Algerian Scientific Journal Platform (ASJP), a digital platform managed by CERIST (Centre de Recherche sur l’Information Scientifique et Technique). It serves as a repository for Algerian academic and scientific journals, facilitating access to scholarly articles across various disciplines.…
We have compiled a list of free and paid AI OSINT tools for efficient research.
Reverse Image OSINT Tools Tool NameDescriptionGeospyAn AI tool that locates where an image was taken by analyzing visual clues and metadata.LensoA platform for Reverse image search , You can search by images for faces , places , duplicates etc .PicartaAn…