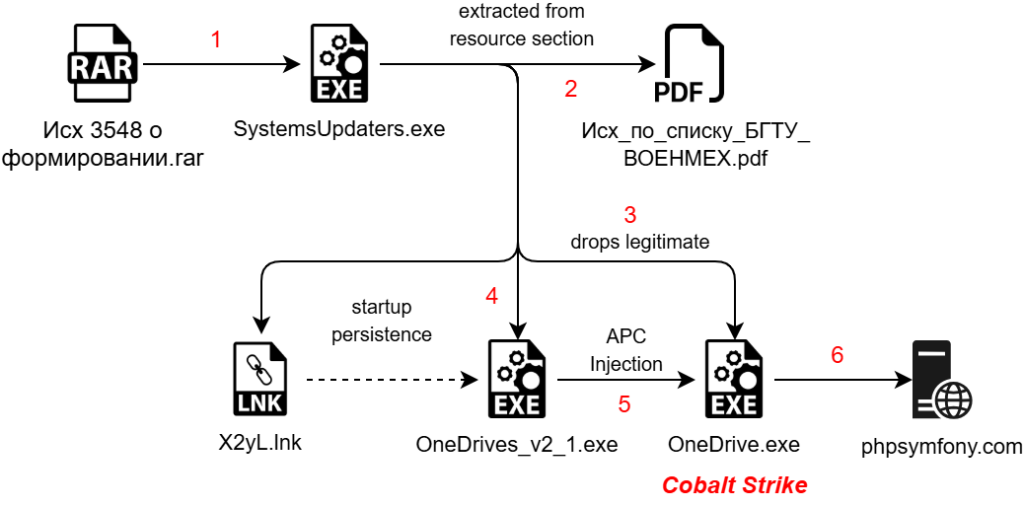
The article discusses Operation HollowQuill, a targeted cyber campaign against the Baltic State Technical University, designed to infiltrate academic and defense networks through weaponized decoy documents. The attack utilizes a multi-stage infection chain, including a malicious RAR file, a .NET malware dropper, Golang shellcode, and a Cobalt Strike payload.…
Read More