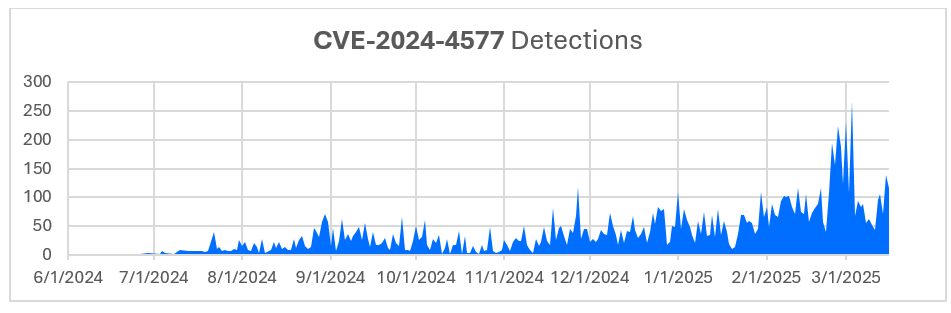
In June 2024, Bitdefender Labs highlighted a critical security vulnerability (CVE-2024-4577) in PHP affecting Windows systems in CGI mode, allowing remote code execution through manipulated character encoding. This vulnerability has seen an increase in exploitation attempts, especially in Taiwan and Hong Kong, with attackers also modifying firewall settings to block known malicious IPs.…
Read More 
 RECONNAISSANCE:
RECONNAISSANCE: