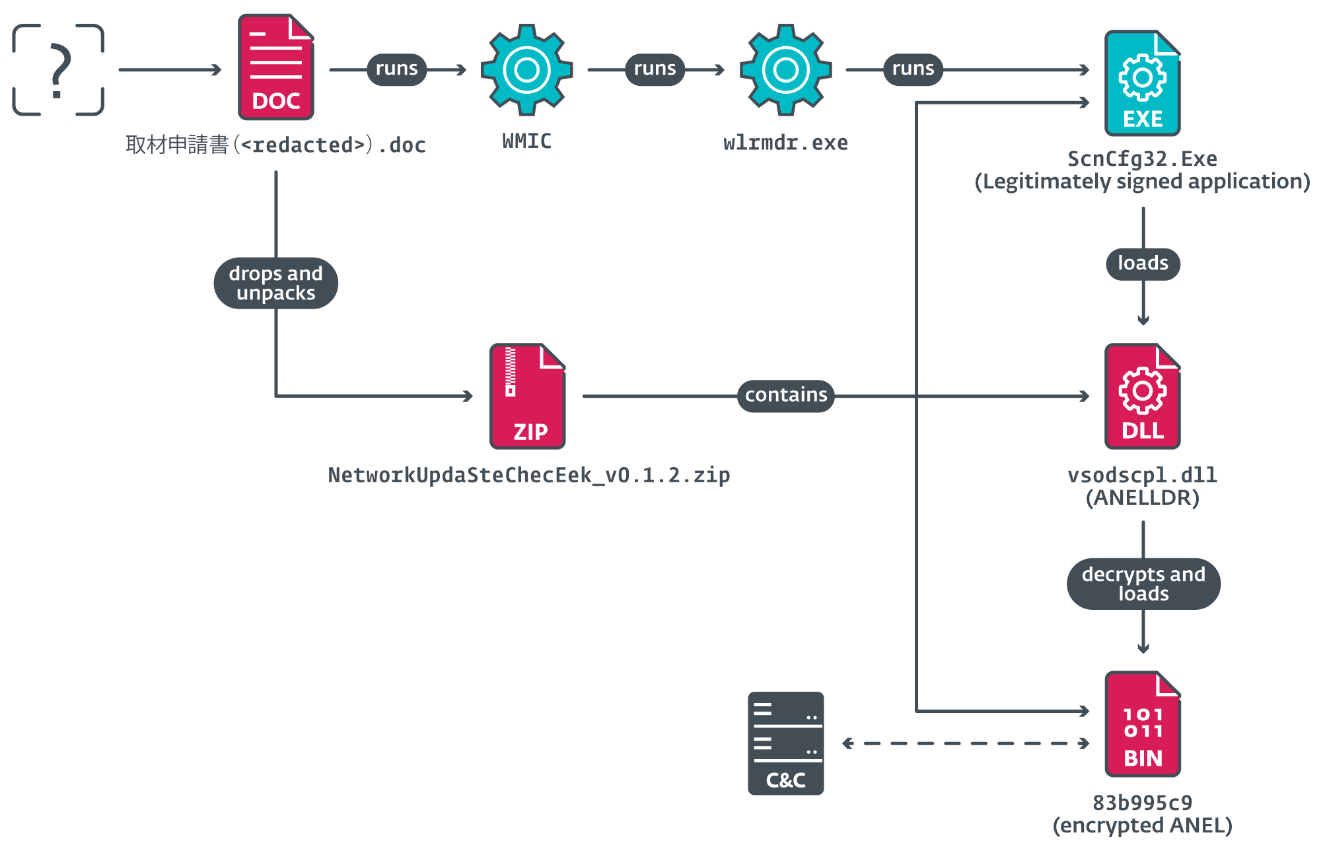
Microsoft Threat Intelligence has revealed that the Chinese espionage group Silk Typhoon is shifting tactics to exploit IT solutions and cloud applications for gaining access to organizations. Despite not directly targeting Microsoft services, they utilize unpatched applications for malicious activities once inside a victim’s network. The article emphasizes the need for awareness and suggests mitigation strategies to defend against this growing threat.…
Read More