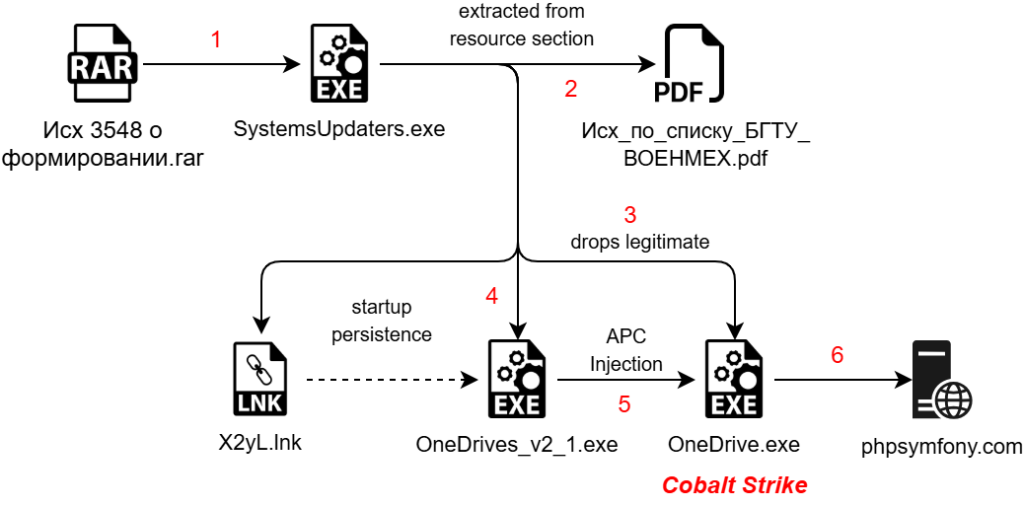
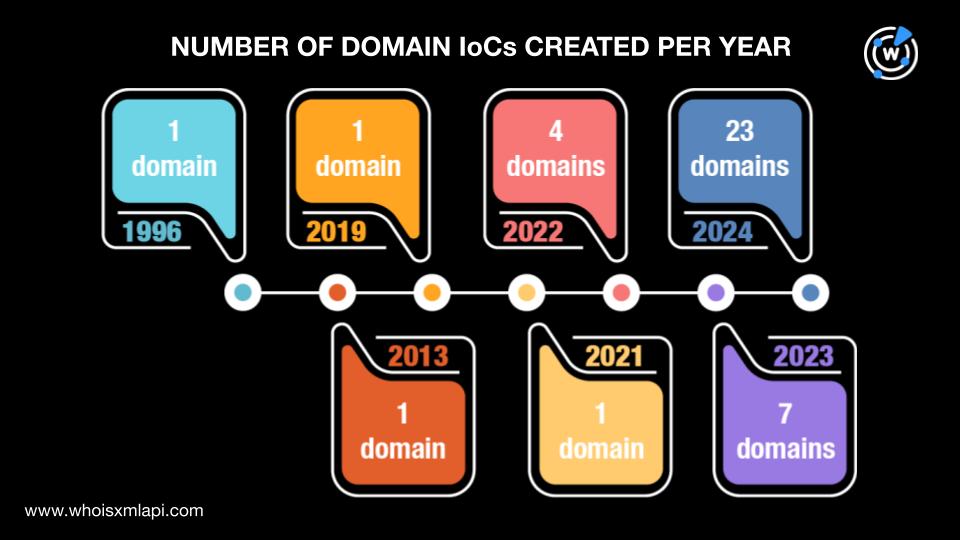
This article explores the infrastructure patterns of two state-linked cyber threat groups based in Russia and China, focusing on Gamaredon and RedFoxtrot. It highlights their use of fast flux DNS techniques for operational stealth and the reuse of TLS certificates among others. Furthermore, it discusses the implications of these patterns for cybersecurity defenses.…
Read More