Notified by: Elz Date: Thu, 24 Oct 2024 22:28:14 +0000 URL: https://crepi.gov.mz/Elz.html Country: Mozambique Sector: Government – This sector encompasses various governmental functions and services, including public administration, policy-making, and regulatory activities.
Check It ! | source:zone-h
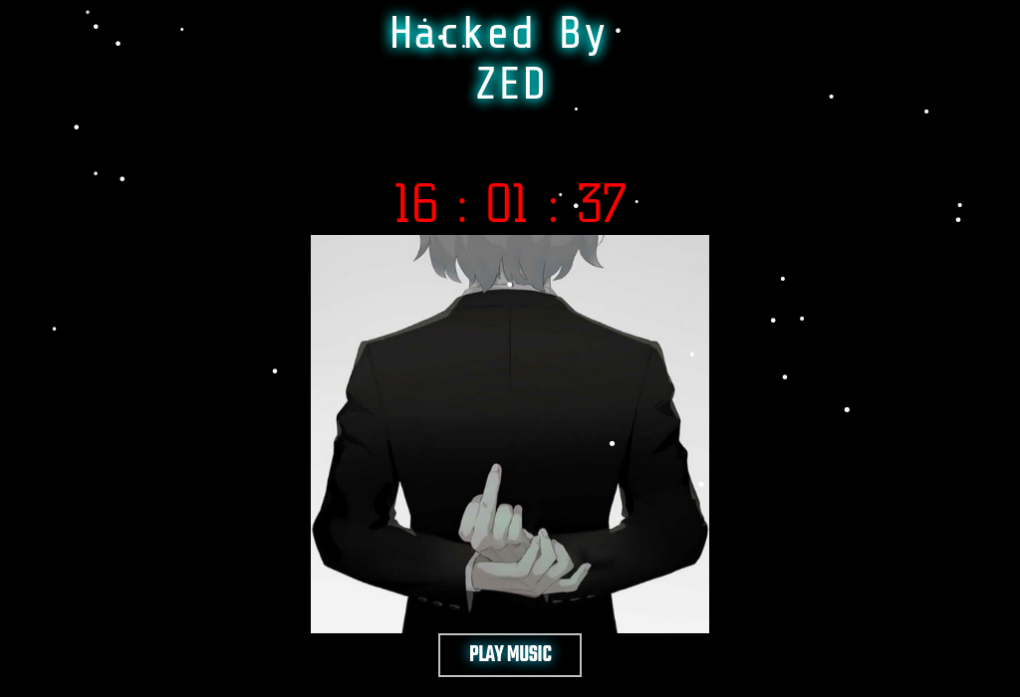
Web Defacement?
“There will be a delay in taking screenshots; there is a possibility that the defacement page has been removed.”…