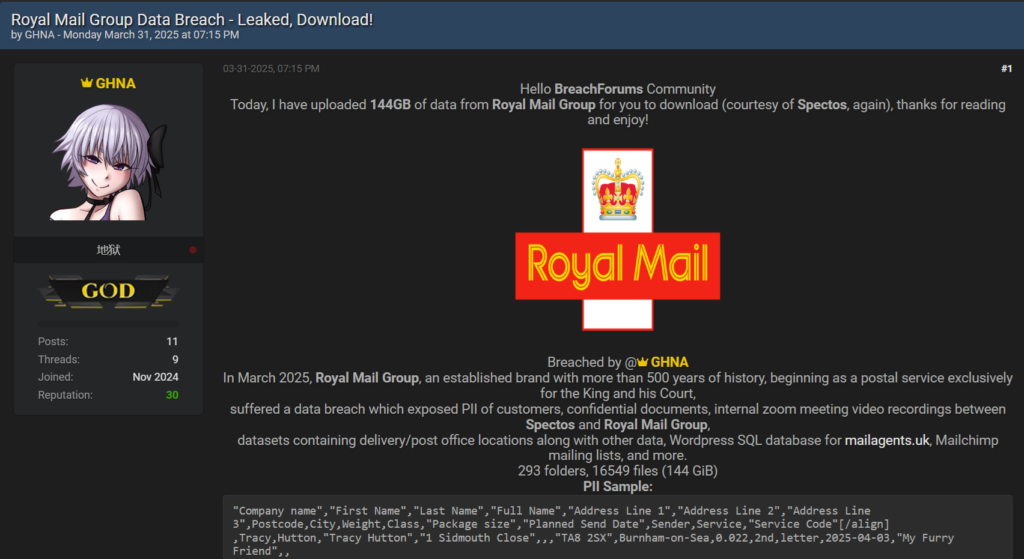
Summary: A massive data breach has exposed 144GB of sensitive information from Royal Mail Group, including personally identifiable information and internal documents, linked to a previous compromise at a third-party service provider, Spectos. The breach, carried out by the threat actor “GHNA,” echoes a recent breach involving Samsung, highlighting a concerning trend in supply chain vulnerabilities exacerbated by AI technologies.…
Read More