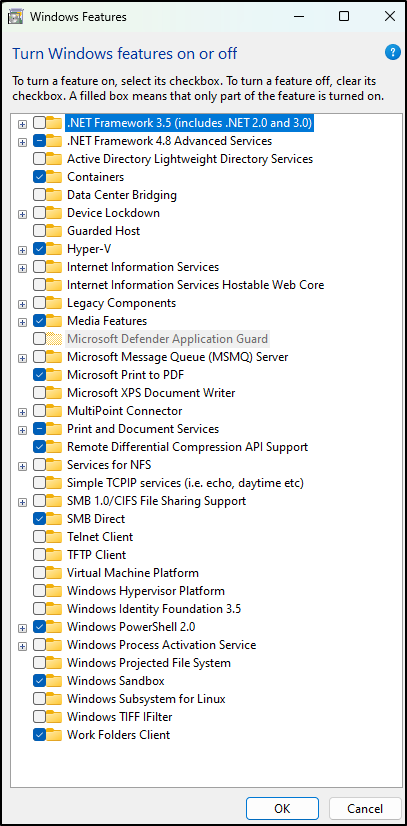
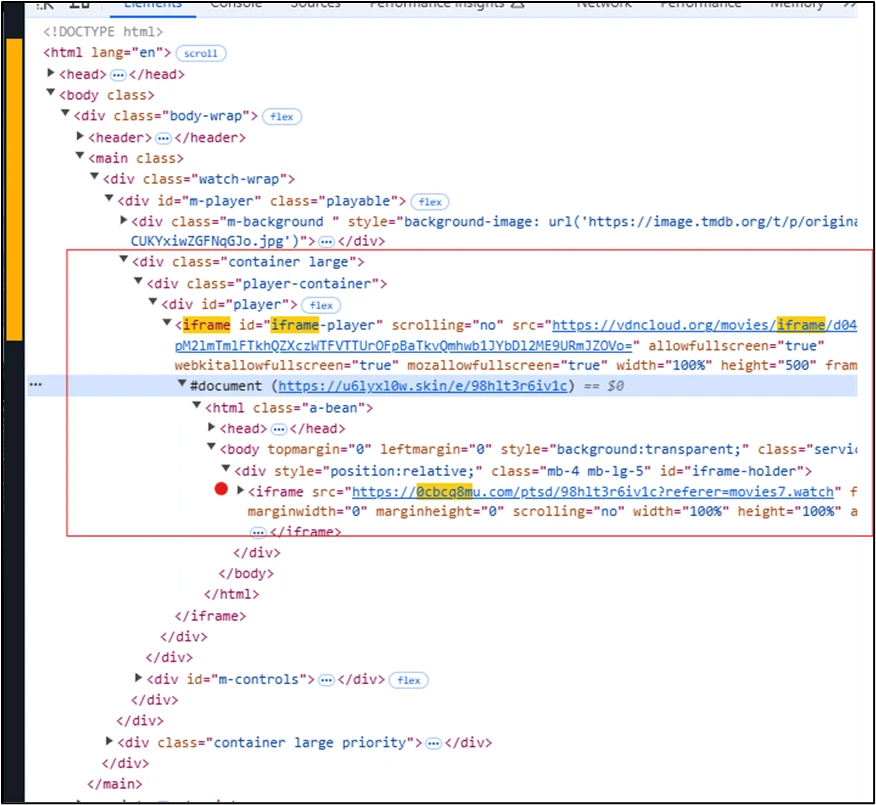
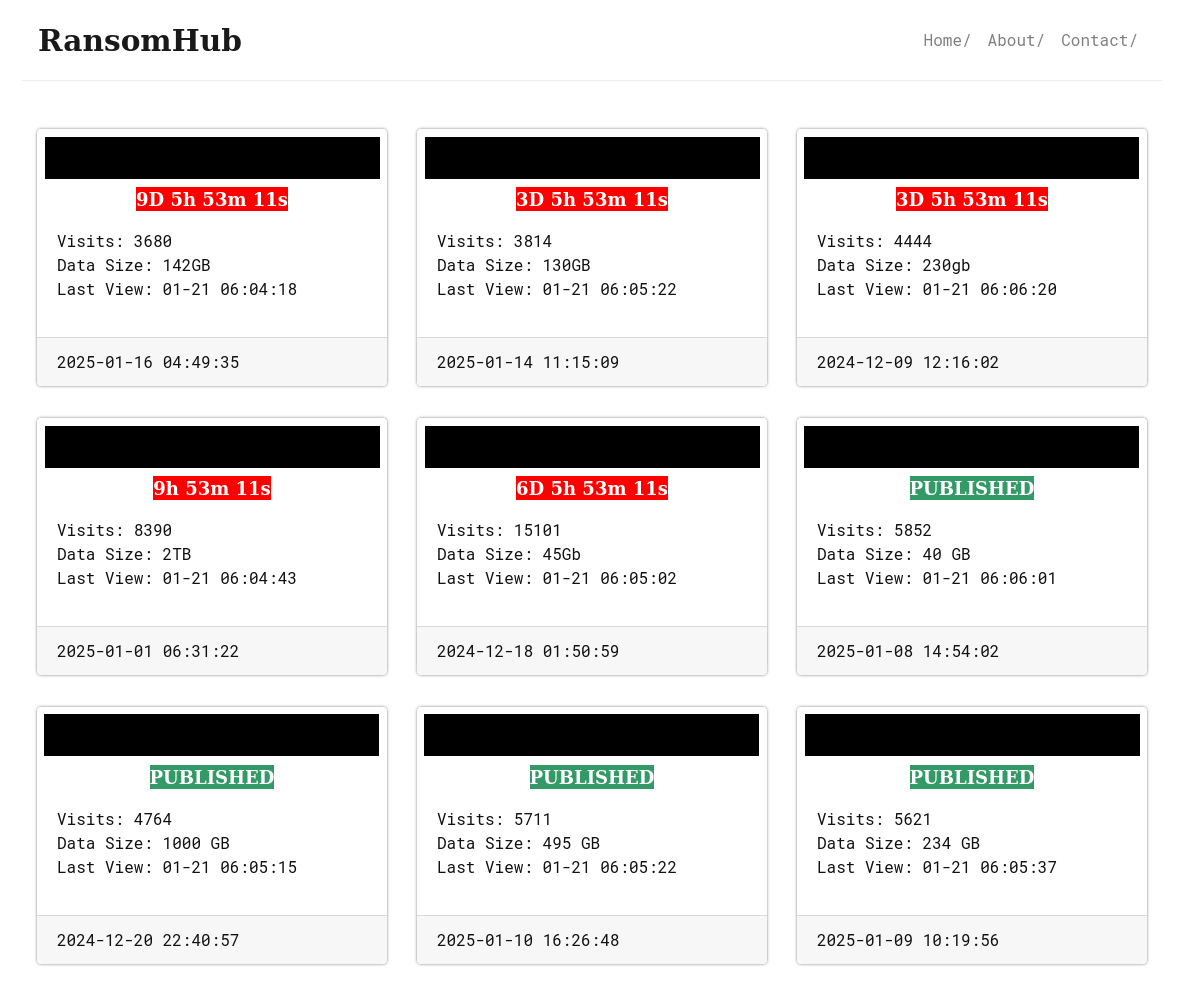
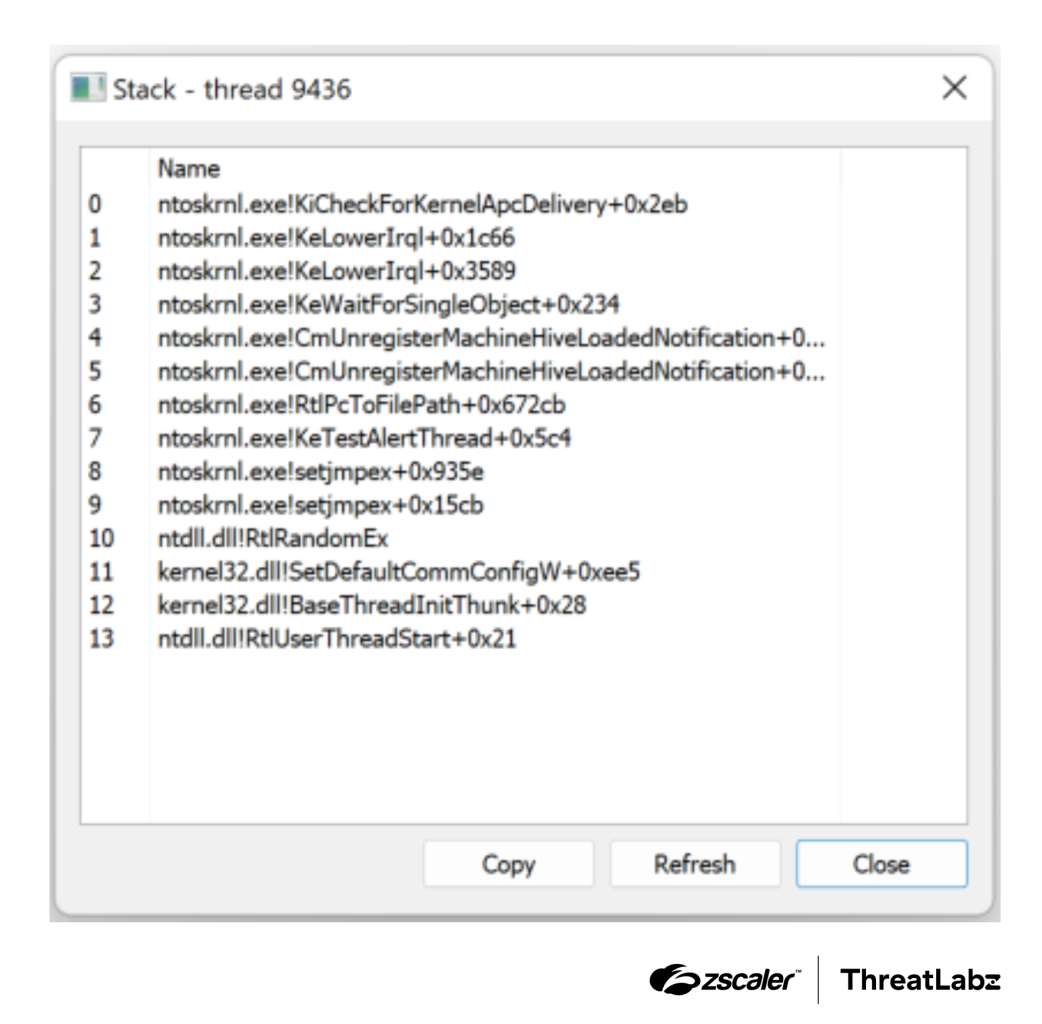
Summary: A recent analysis reveals a connection between RansomHub affiliates and several other ransomware groups through a custom tool called EDRKillShifter, which disables endpoint detection and response software. This tool utilizes a method known as Bring Your Own Vulnerable Driver (BYOVD) to ensure ransomware execution is not flagged by security measures.…
Read More 






 THN Weekly Recap: GitHub Supply Chain Attack, AI Malware, BYOVD Tactics, and More
THN Weekly Recap: GitHub Supply Chain Attack, AI Malware, BYOVD Tactics, and More