Summary: The video discusses the challenges faced by beginners in penetration testing and emphasizes the foundational skills necessary for success in the field. It underscores the importance of coding, networking, and system administration as essential pillars that aspiring penetration testers should focus on to enhance their capabilities and effectively identify vulnerabilities.…
Read More Tag: DISCOVERY

Summary: New Android malware campaigns leveraging Microsoft’s .NET MAUI framework have emerged, allowing attackers to disguise malicious apps as legitimate services to evade detection. These tactics, first reported by McAfee, pose a significant security risk, especially as targeting could expand beyond China and India. The use of multi-layered encryption and the unique storage of app logic in binary blob files complicates detection efforts further.…
Read More 
The article discusses the emergence of malware campaigns utilizing .NET MAUI, a new cross-platform development framework, to evade detection and steal sensitive user information. These malicious apps disguise themselves as legitimate services and often target users from unofficial app stores or through phishing links. Recommendations for user protection against such threats are provided.…
Read More 
The Lumma Stealer malware has been observed targeting U.S. State, Local, Tribal, and Territorial (SLTT) government organizations through fake CAPTCHA verification pages that trick users into executing malicious PowerShell scripts. This malware, available as a Malware-as-a-Service, specializes in stealing sensitive data. Cyber threat actors utilize a variety of deceptive tactics and defense evasion techniques to deliver the malware and avoid detection.…
Read More 
This article explores various threat actors known for their significant cyber attacks, detailing their origins, techniques, and famous hacks. It categorizes these actors by their affiliations, such as state-sponsored and financially motivated groups, providing insight into their behaviors and methodologies. Affected: Government networks, financial institutions, healthcare, energy sector, retail, hospitality, media, technology, and more.…
Read More 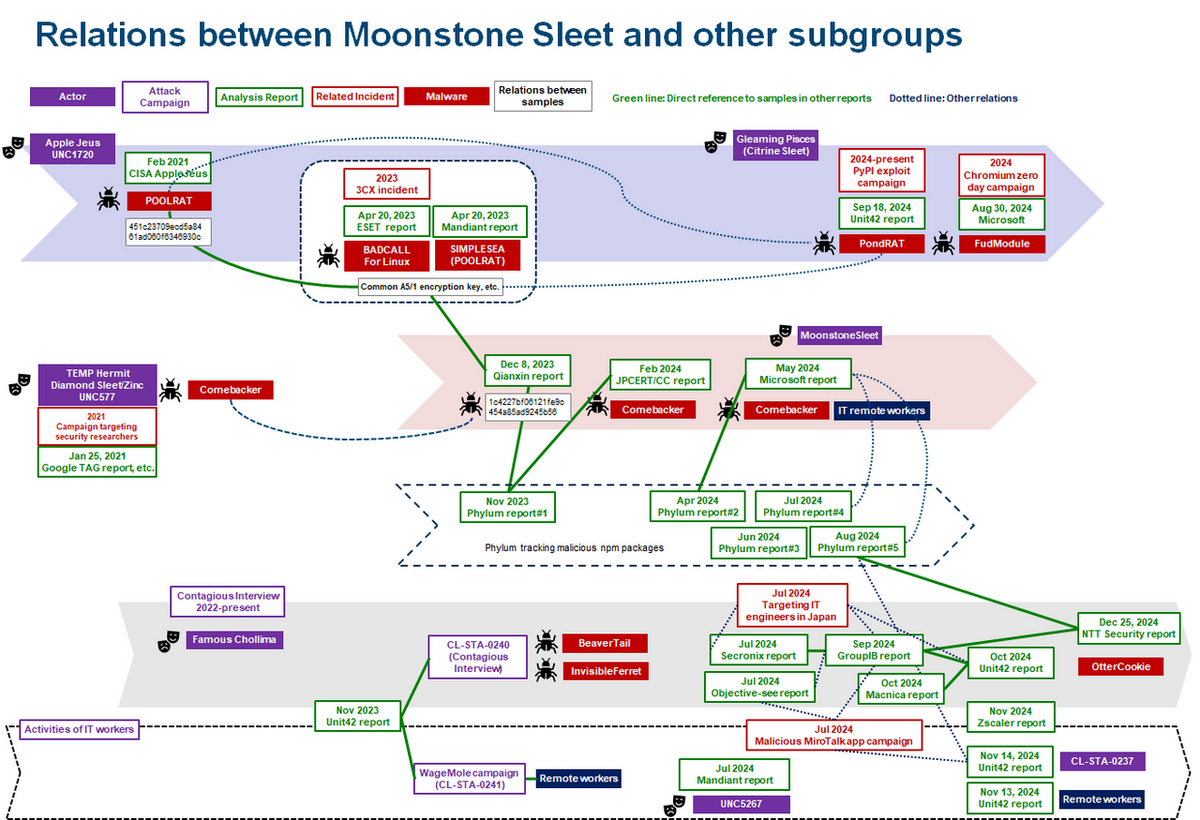
The article discusses the evolution of the Lazarus group, indicating that it has now transformed into a collection of subgroups rather than a single entity. It emphasizes the importance of understanding these subgroups, their tactics, and their individual characteristics for effective cyber defense strategies. Affected: Japan, cryptocurrency sector, defense industry, aviation industry
Read More Keypoints :
The term “Lazarus” has evolved from a singular APT group to multiple subgroups.…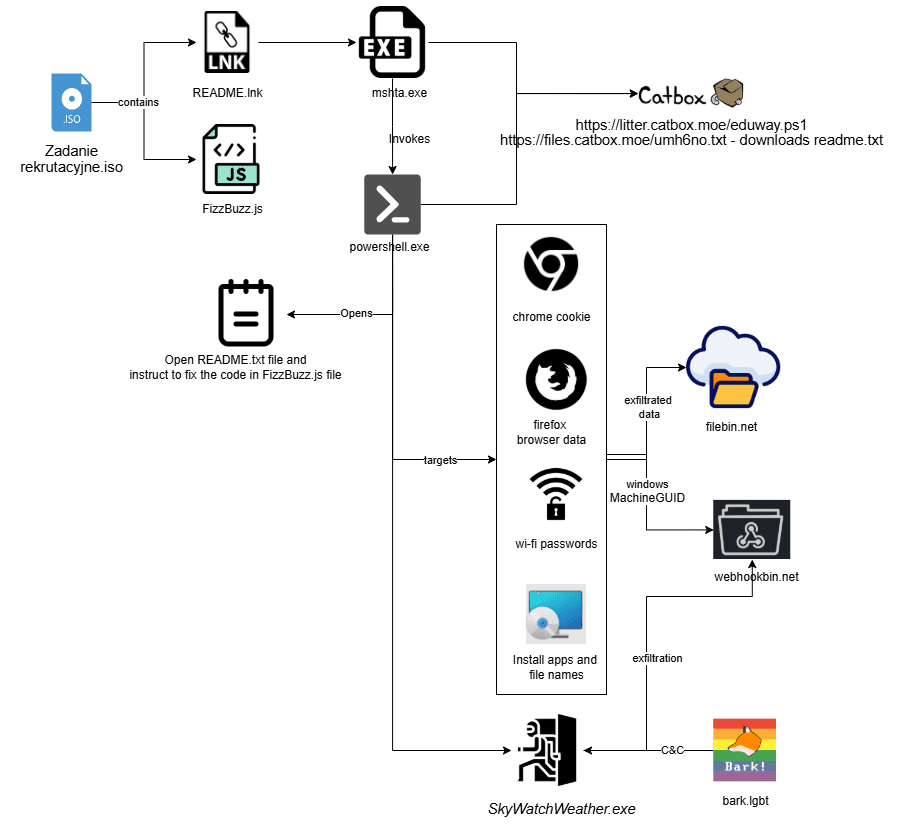
A targeted social engineering campaign has emerged, with a GitHub repository posing as a coding challenge aimed specifically at Polish-speaking developers. The campaign utilizes a malicious ISO file that, when executed, installs a backdoor called “FogDoor,” which collects sensitive information and communicates with a social media platform to execute commands.…
Read More
The blog outlines several critical unauthenticated Remote Code Execution vulnerabilities found in Ingress NGINX Controller for Kubernetes, collectively dubbed #IngressNightmare. These vulnerabilities can grant attackers unauthorized access to all secrets within a Kubernetes cluster, risking complete takeover. With a CVSS v3.1 score of 9.8, it is estimated that 43% of cloud environments, including many Fortune 500 companies, are at risk.…
Read More 
The article discusses a financially motivated cybercriminal campaign utilizing a malicious driver known as ABYSSWORKER, which disables endpoint detection and response systems to deploy MEDUSA ransomware. This driver exploits revoked certificates and incorporates various evasion techniques against EDR systems while showcasing its capabilities to manipulate processes and files.…
Read More 
Summary: A major Asian telecommunications company suffered a four-year-long breach by Chinese government-affiliated hackers known as “Weaver Ant.” The attackers compromised home routers from Zyxel to infiltrate the telco, utilizing various advanced tools and backdoors to maintain persistent access and extract sensitive information. Sygnia, the incident response firm, highlights the sophistication and stealthiness of the threat actors in their campaign targeting critical infrastructure.…
Read More 
Summary: The VanHelsing ransomware-as-a-service (RaaS) operation emerged on March 7, 2025, quickly claiming multiple victims through a user-friendly platform that supports a variety of operating systems. The scheme employs double extortion tactics and allows affiliates to profit significantly while only prohibiting attacks on the Commonwealth of Independent States (CIS).…
Read More
The Crazy Hunter ransomware attack exploited Active Directory misconfigurations and utilized Bring-Your-Own-Vulnerable-Driver (BYOVD) techniques to escalate privileges and distribute ransomware through Group Policy Objects. Despite claims of data exfiltration, forensic investigations found no supporting evidence. This attack resulted in significant operational disruptions and highlighted the importance of proactive threat intelligence in cybersecurity.…
Read More 
Summary: Recent cyber threats highlight vulnerabilities in open-source tools, escalating ad fraud through mobile apps, and advanced ransomware tactics targeting critical defenses. Notably, attacks have leveraged AI, and a supply chain breach at Coinbase exemplifies these risks. A rise in stolen credentials further underscores the urgent need for improved cybersecurity measures.…
Read More 
A newly identified malware named “문서열람 인증 앱” (Document Viewing Authentication App), linked to a North Korean-backed APT group, has been detected. This malicious application poses as a legitimate document viewing tool but is designed to perform keylogging and information theft through various malicious functions. Users in South Korea are the primary targets, and the malware has connections to a phishing page that impersonates CoinSwap.…
Read More 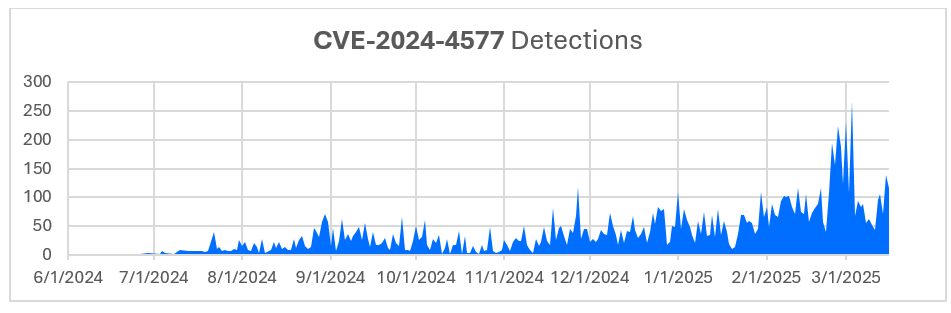
In June 2024, Bitdefender Labs highlighted a critical security vulnerability (CVE-2024-4577) in PHP affecting Windows systems in CGI mode, allowing remote code execution through manipulated character encoding. This vulnerability has seen an increase in exploitation attempts, especially in Taiwan and Hong Kong, with attackers also modifying firewall settings to block known malicious IPs.…
Read More
Summary: After a four-year investigation, law enforcement successfully apprehended a cybercriminal known by multiple aliases, including ALTDOS and Omid16B. The criminal, motivated by financial gain, executed various attacks on companies, primarily focusing on extortion through data breaches. Group-IB played a pivotal role in tracking the actor’s activities across different identities until his arrest in Thailand on February 26, 2025.…
Read More 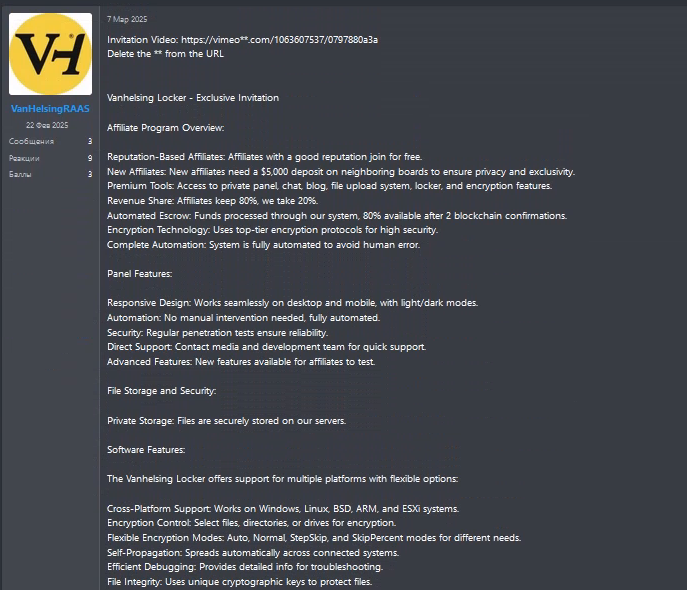
VanHelsingRaaS is an emerging ransomware-as-a-service (RaaS) launched in March 2025, allowing affiliates to initiate ransomware attacks with a low deposit. It targets multiple platforms and has already infected several victims demanding significant ransom payments. The program’s rapid growth and sophisticated capabilities highlight the evolving ransomware threat.…
Read More 
Summary: A targeted supply chain attack involving the GitHub Action “tj-actions/changed-files” was first directed at Coinbase’s open-source projects but escalated into a wider attack compromising 218 repositories. The attacker was able to exploit the CI/CD process, manage tokens, and introduce malicious code without initially triggering significant alarms.…
Read More
Hunt researchers exposed a web server hosting tools linked to an intrusion campaign against South Korean organizations. This server, available for less than 24 hours, encompassed a Rust-compiled Windows executable that deployed Cobalt Strike Cat along with several other open-source tools. The attacker appears to have focused on exploiting vulnerabilities in government and commercial entities.…
Read More 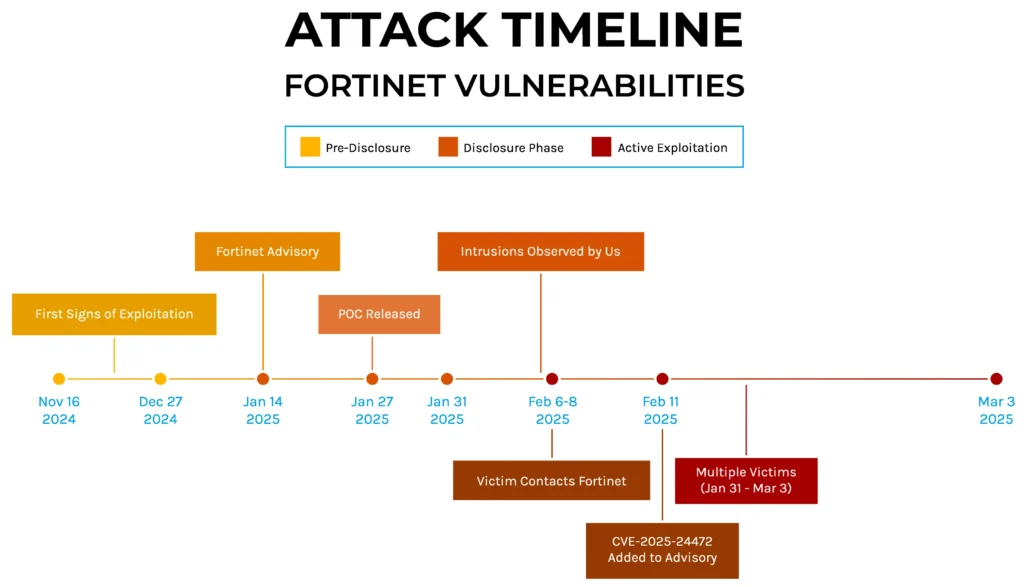
Forescout Research has identified a new ransomware strain, dubbed SuperBlack, linked to the threat actor “Mora_001”, exploiting vulnerabilities in Fortinet devices. This threat actor is connected to the LockBit ransomware ecosystem and demonstrates sophisticated tactics including rapid ransomware deployment, user account creation across victim networks, and the use of modified LockBit tools.…
Read More  THN Weekly Recap: GitHub Supply Chain Attack, AI Malware, BYOVD Tactics, and More
THN Weekly Recap: GitHub Supply Chain Attack, AI Malware, BYOVD Tactics, and More