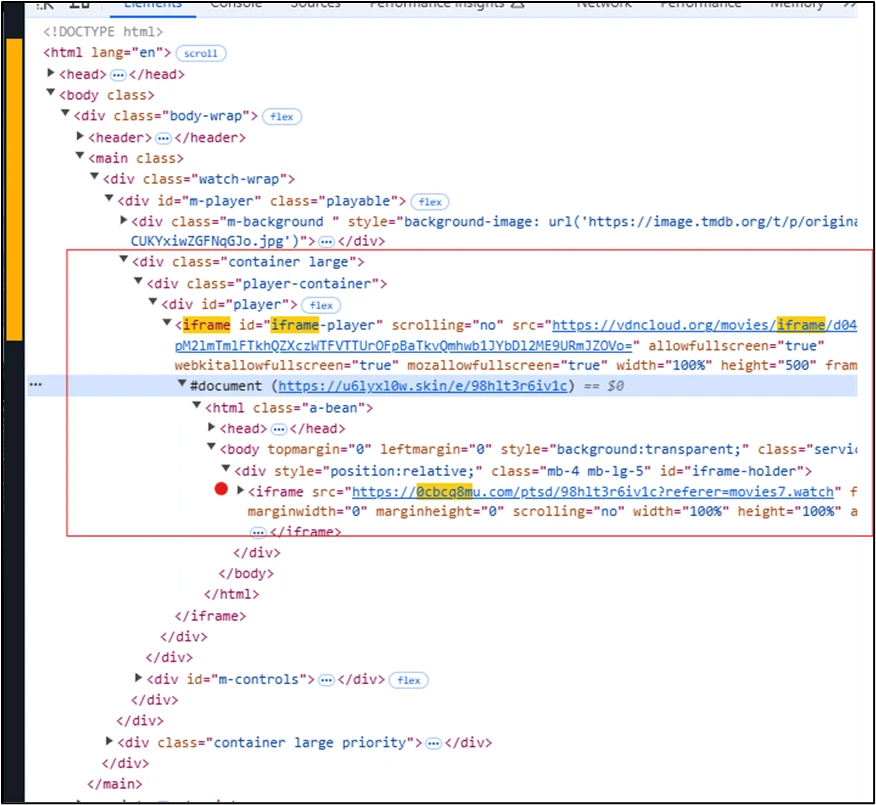
In December 2024, a widespread malvertising campaign was discovered that affected nearly a million devices globally, originating from illegal streaming websites embedded with malicious advertisements. The attack involved a series of redirections leading to GitHub, Dropbox, and Discord, where malware was hosted. This campaign targeted various sectors indiscriminately, highlighting the need for enhanced security measures across devices and networks.…
Read More 




 THN Weekly Recap: Router Hacks, PyPI Attacks, New Ransomware Decryptor, and More
THN Weekly Recap: Router Hacks, PyPI Attacks, New Ransomware Decryptor, and More