This article discusses the emergence and threats posed by the Vo1d botnet, which has taken control of millions of Android TV devices worldwide. It highlights a recent incident where unauthorized AI-generated content disrupted broadcasts, stressing the potential risks associated with compromised devices. Vo1d’s evolution involves sophisticated techniques in its operation, communication, and payload delivery mechanisms, which pose significant challenges for cybersecurity. Affected: Android TVs, broadcasting networks, global cybersecurity.
Keypoints :
- The Vo1d botnet has infected approximately 1.6 million Android TV devices globally.
- The botnet’s capability has been enhanced, allowing it to carry out major DDoS attacks.
- Vo1d uses sophisticated algorithms for payload encryption and command and control infrastructure.
- Compromised devices can be manipulated to spread illegal content and facilitate cybercrimes.
- Previous botnets like Mirai have shown the severe impact of compromised IoT devices.
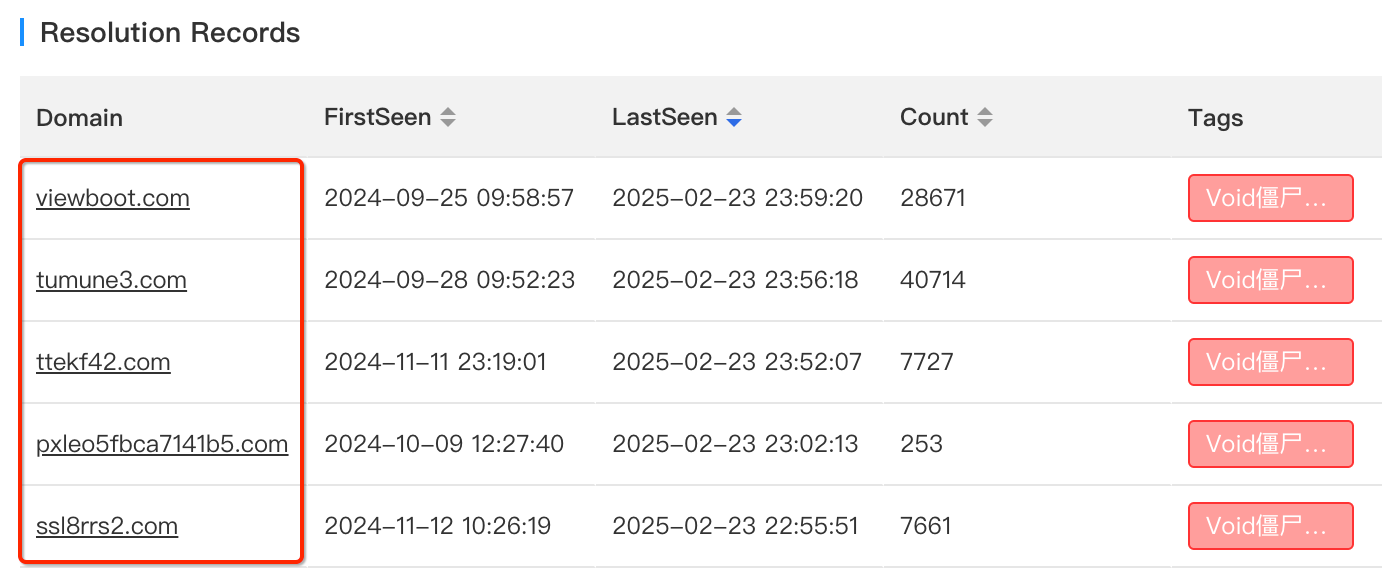
- Vo1d’s infrastructure is built around a complex set of domains and IPs for evasion and load balancing.
- Safety protocols for smart devices are often underestimated, leading to higher infection rates.
- Vo1d has demonstrated a robust ability to evolve despite prior disruptions from cybersecurity efforts.
MITRE Techniques :
- T1071 – Application Layer Protocol: Vo1d uses secure protocols for command and control (e.g., RSA encrypted communications).
- T1041 – Exfiltration Over Command and Control Channel: Vo1d can exfiltrate information via its established channels.
- T1203 – Exploitation for Client Execution: Vo1d relies on exploiting vulnerabilities in Android TV platforms.
- T1027 – Obfuscated Files or Information: Vo1d employs unique encryption mechanisms (asr_xxtea) to conceal its payloads.
- T1532 – Data Encrypted for Impact: The botnet encrypts sensitive communications to protect its operations.
Indicator of Compromise :
- [IP Address] 38.46.218.36
- [Domain] ssl8rrs2.com
- [Domain] ttekf42.com
- [Domain] works883.com
- [Domain] ssl87362.com
Full Story: https://blog.xlab.qianxin.com/long_live_the_botnet_vo1d_is_back_cn/