This blog post discusses the IDAT Loader malware and its unique method of retrieving data from PNG files. It also explores the attack chain observed in two separate incidents involving the IDAT Loader and the BruteRatel C4 framework. The post provides technical analysis of the malware’s behavior and highlights the techniques used by threat actors.
Key Points:
* The IDAT Loader is a malware loader that delivers and executes additional malware onto a victim’s system.
* It retrieves data from PNG files, searching for offsets beginning with “IDAT”.
* The loader was distributed via a FakeUpdates campaign and is associated with financially motivated threat groups.
* The attack chain involves opportunistic infections through malvertising and drive-by downloads.
* The malware utilizes advanced techniques such as Process Doppelgänging and the Heaven’s Gate technique.
* The final payload extracted from the IDAT Loader is the SecTop RAT.
* The SecTop RAT communicates with the IP address 152.89.217[.]215.
* The post also discusses the post-exploitation phase involving the deployment of the BruteRatel C4 framework.
* Rapid7 customers have existing detection coverage for these activities through InsightIDR and Managed Detection and Response.
____________________
Last updated at Mon, 01 Apr 2024 17:06:36 GMT
Rapid7’s Managed Detection and Response (MDR) team continuously monitors our customers’ environments, identifying emerging threats and developing new detections.
In August 2023, Rapid7 identified a new malware loader named the IDAT Loader. Malware loaders are a type of malicious software designed to deliver and execute additional malware onto a victim’s system. What made the IDAT Loader unique was the way in which it retrieved data from PNG files, searching for offsets beginning with 49 44 41 54 (IDAT).
At the time, the loader was seen being distributed via a FakeUpdates campaign. In two recent investigations, Rapid7’s Managed Detection & Response (MDR) observed the loader being used again. Based on the recent tactics, techniques and procedures observed (TTPs), we believe the activity is associated with financially motivated threat groups.
In this two-part blog series, we will examine the attack chain observed in two separate incidents, offering in-depth analysis of the malicious behavior detected. The incidents discussed in the series stem from opportunistic infections, wherein threat groups utilize malvertising and drive-by downloads in order to have their initial malicious payloads executed by users.
This first installment focuses on an incident triggered by a user downloading an application, which subsequently triggered the execution of the IDAT Loader and the BruteRatel C4 (BRC4) framework following initial access to a compromised asset.
Technical Analysis
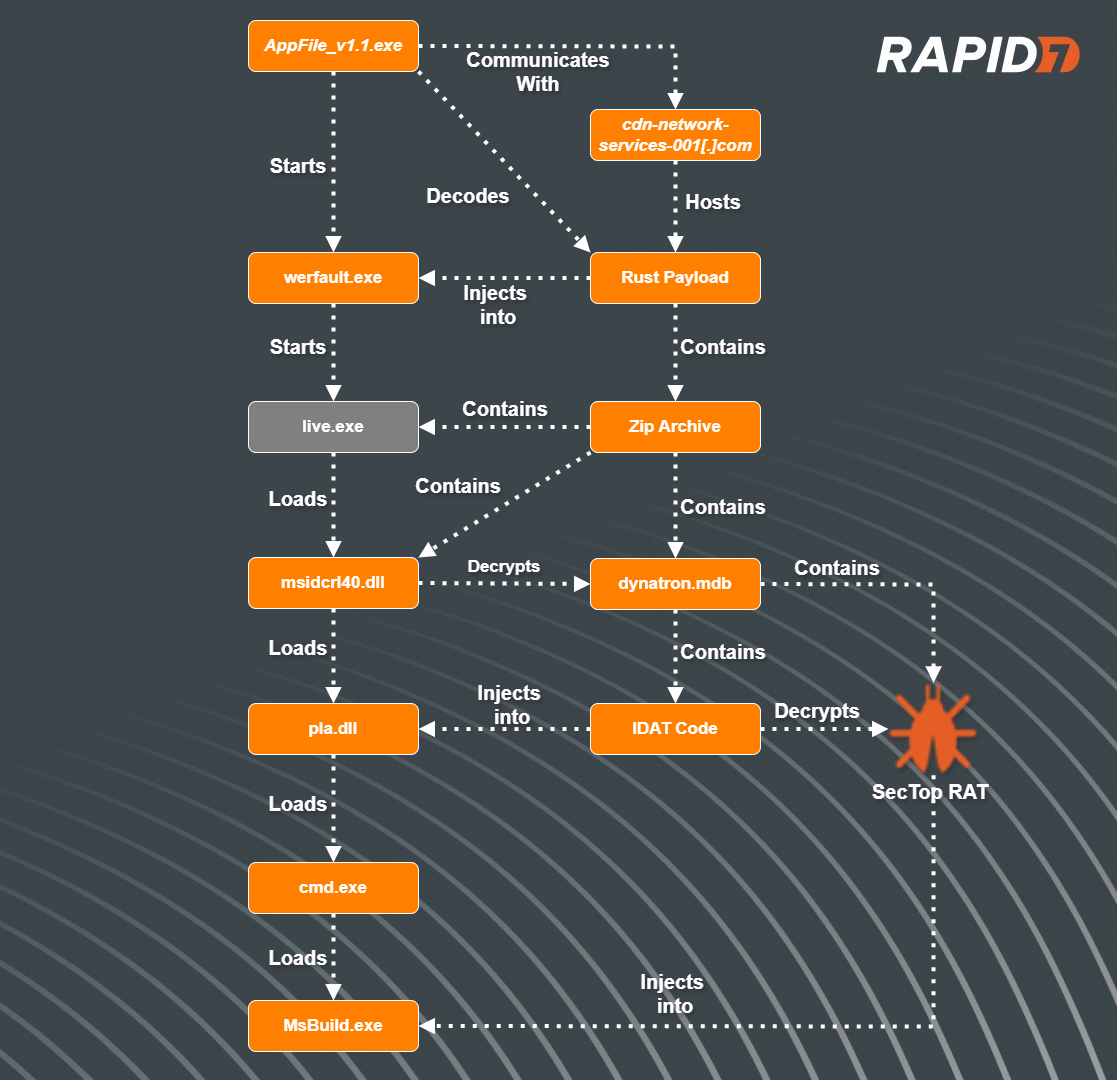
Stage 1: The drive by
In a recent incident, we observed a user navigate to a website that hosted popular Korean shows. Upon attempting to watch the video, the website redirected the user’s browser through multiple websites, eventually leading to the download of an application named AppFile_v1.1.exe. Threat actors utilize website redirection in order to make it difficult for network technologies to scan links for malicious content.
Binary Analysis: Shaking off the Rust
After initial analysis of the binary AppFile_v1.1.exe, we determined the program was written in Rust.
During execution, the program will query the name of the executable. If the executable’s name matches AppFile_v1.1.exe, the program will continue. Most sandboxes will rename the files (sometimes based on the hash) of submitted programs. This technique helps to evade sandboxes, ensuring the malicious functions are not run. If the program name does not match its original intended name, the program will quit and display an error message, showing an image that a web page could not be loaded.
Next, the program will check to see if it resides within a debugger by querying the function IsDebuggerPresent. If the check passes, it will decrypt a hard-coded string that resolves to “Normal”. If not, the program will decrypt another hard-coded string that resolves to “Debugger” and then exit.
Once the anti-debug check passes, the program retrieves an encrypted string and XOR decrypts it, revealing the URL hxxps://cdn-network-services-001[.]com/update/minor/1/release.json.
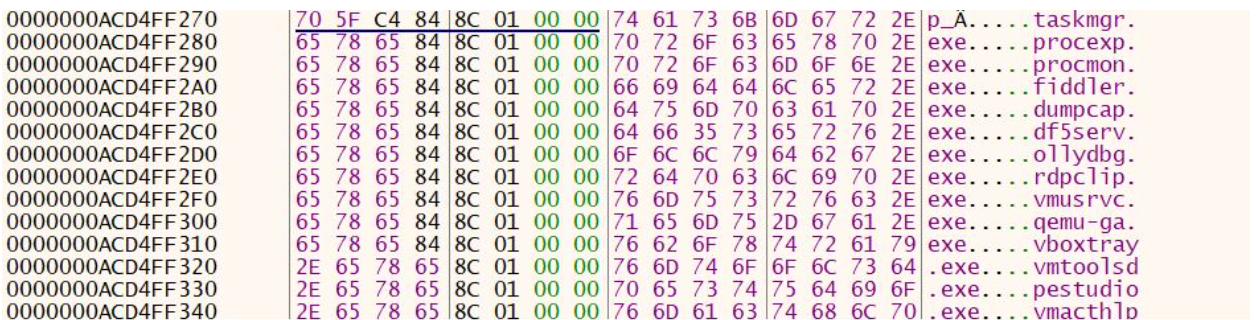
The program will then perform anti-analysis techniques, specifically querying for the username and open process and comparing them to a list of known sandbox usernames and tools. The list of usernames and processes are also XOR-encrypted and are decrypted at runtime. Based on Open Source Intelligence, we determined that another malware known as Serpent Stealer contained a similar table of user names. See Appendix A below for the complete list.
| Usernames | Known Sandbox ToolsProcesses |
|---|---|
| hbyldjtckyn1 | httpdebuggerui.exe |
| lubi53an14cu | immunitydebugger.exe |
| rgzcbuyrznreg | ksdumperclient.exe |
| 8lnfaai9qdjr | httpanalyzerstdv7.exe |
| j6sha37ka | ida64.exe |
If any of the checks fail, the program will exit and display the message box. If the checks pass, the program will then utilize Rust library tokio-1.32.0/src/net/tcp/stream.rs in order to read in data from the decrypted URL and store the contents in memory.
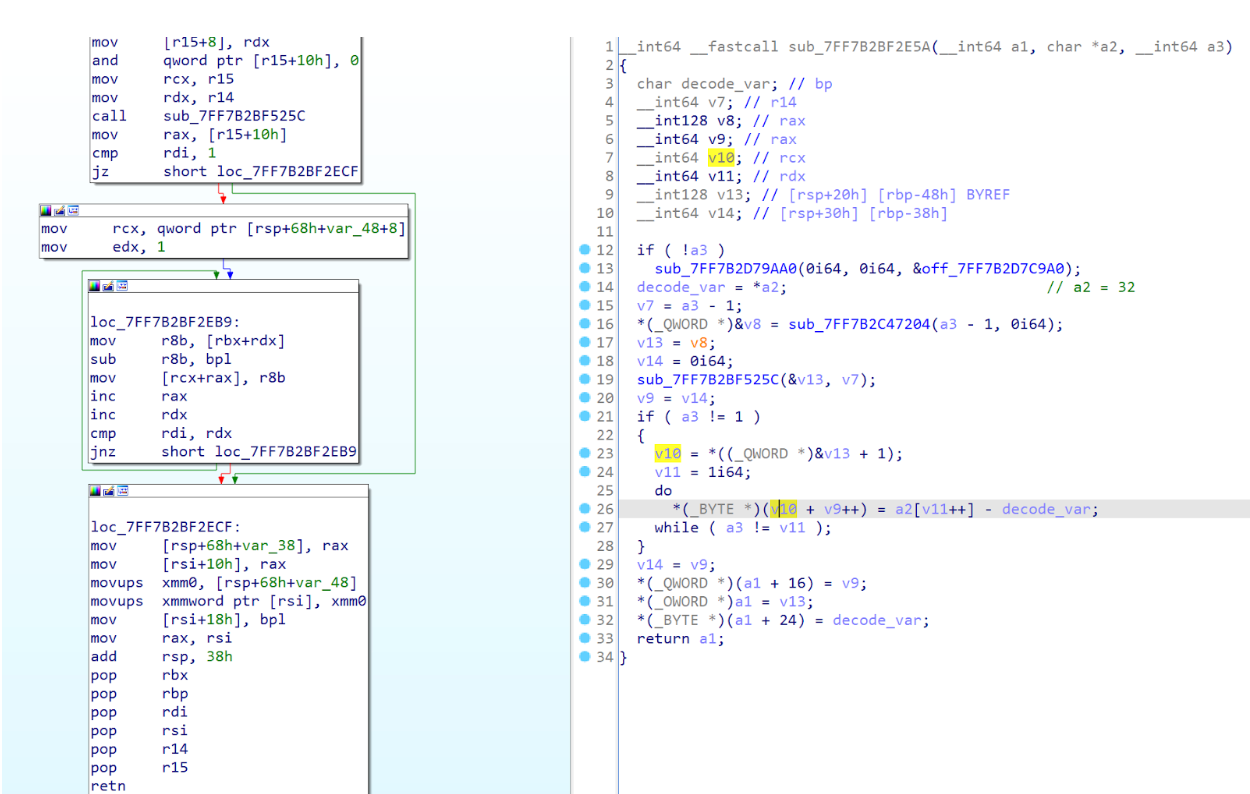
Upon initial analysis, the downloaded data appeared to be encoded. Subsequently, the data is passed into a function tasked with decoding it. The decoding process involves reading each byte and subtracting the hexadecimal value 32.
After the downloaded data is decoded, the program XOR decrypts another string, revealing a path to the executable C:Windowssystem32werfault.exe. Using syscalls, the program then does the following:
| Windows API Function | Syscall ID | Description |
|---|---|---|
| NtOpenProcess | 0x0026 | Used to start the process werfault.exe |
| NtCreateUserProcess | 0x00c8 | Used for spoofing Parent Process ID (PPID) |
| NtAllocateVirtualMemory | 0x0018 | Allocate new space within memory, storing the new executable |
| NtGetContextThread | 0x00F2 | Used to retrieve the context of a thread within the target process (werfault.exe). |
| The thread in this case is a pointer to the entry point of the new executable | ||
| NtSetContextThread | 0x0018B | Used to point to the thread from NtGetContextThread |
| NtResumeThread | 0x0052 | Starts the thread set by NtSetContextThread |
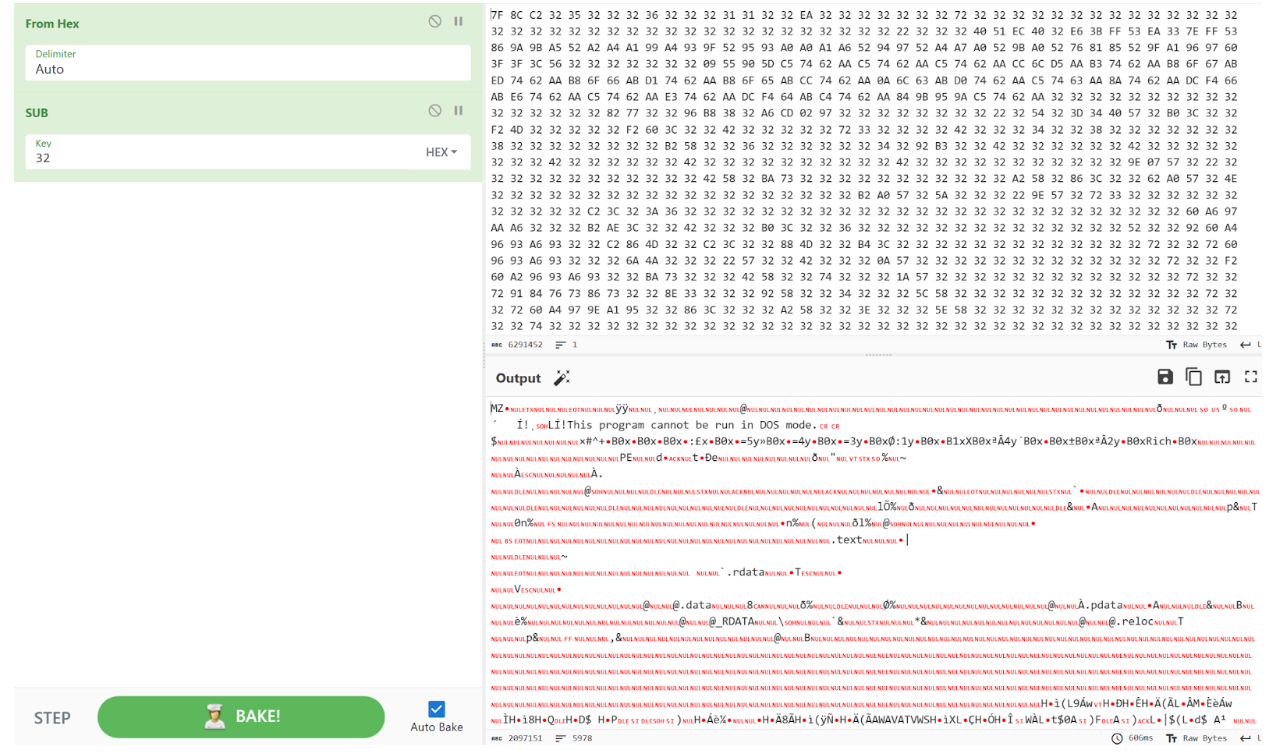
After analysis of the decoded binary, we determined that it was another executable written in Rust. The program’s executable contains a zip archive within the .rdata section. During execution, the program generates a folder with a randomly generated name in the %TEMP% directory and extracts the contents of the archive into this newly created folder.
The archive contained a DLL, msidcrl40.dll, an executable named live.exe and an encrypted file, dynatron.mdb. Initial analysis of the DLL msidcrl40.dll showed that the DLL’s signature was corrupted, indicating the DLL was tampered with. Further analysis showed that the DLL contained code related to the IDAT Loader.
IDAT Loader
After the rust program drops the contents of the zip archive, it then proceeds to execute the binary live.exe, which sideloads the DLL, msidcrl40.dll, containing the IDAT Loader code.
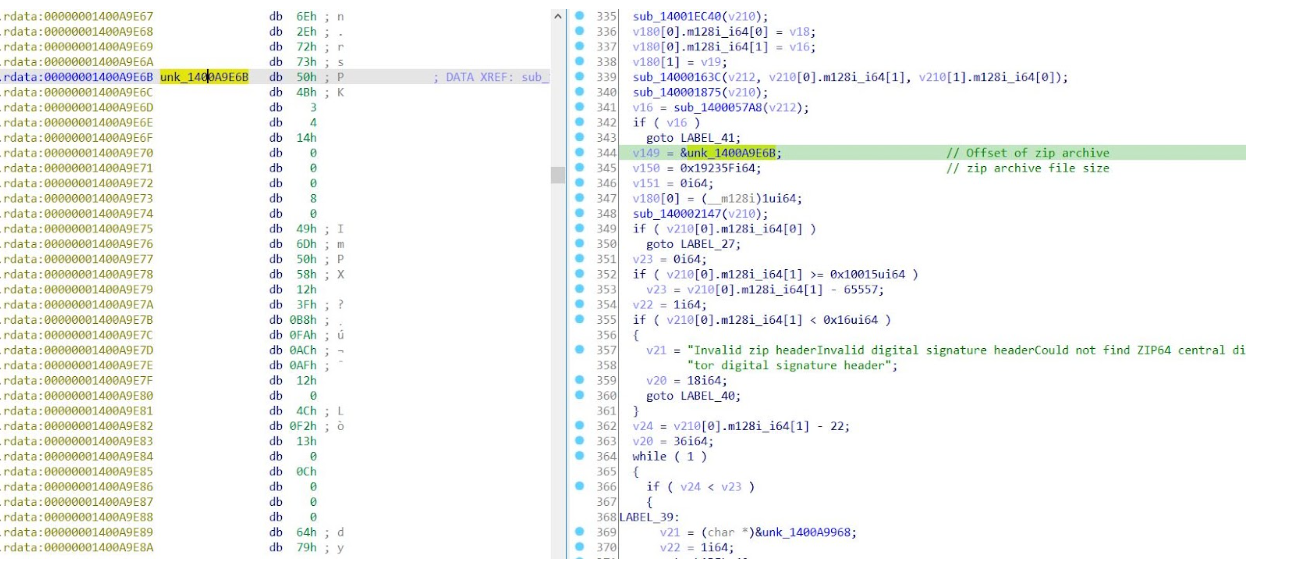
After the binary live.exe loads the DLL msidcrl40.dll, the DLL executes the function containing the IDAT Loader. The loader then reads in encrypted contents contained within the file dynatron.mdb, searching for the offset 49 44 41 54 (IDAT) followed by C6 A5 79 EA. After decrypting the contents, the loader will then decompress the contents using RtlDecompressBuffer and execute additional code into a newly created process, cmd.exe.
The IDAT loader employs advanced techniques such as Process Doppelgänging and the Heaven’s Gate technique in order to initiate new processes and inject additional code.
The code contained within cmd.exe is responsible for decrypting the final payload and injecting it into a newly created process, msbuild.exe.
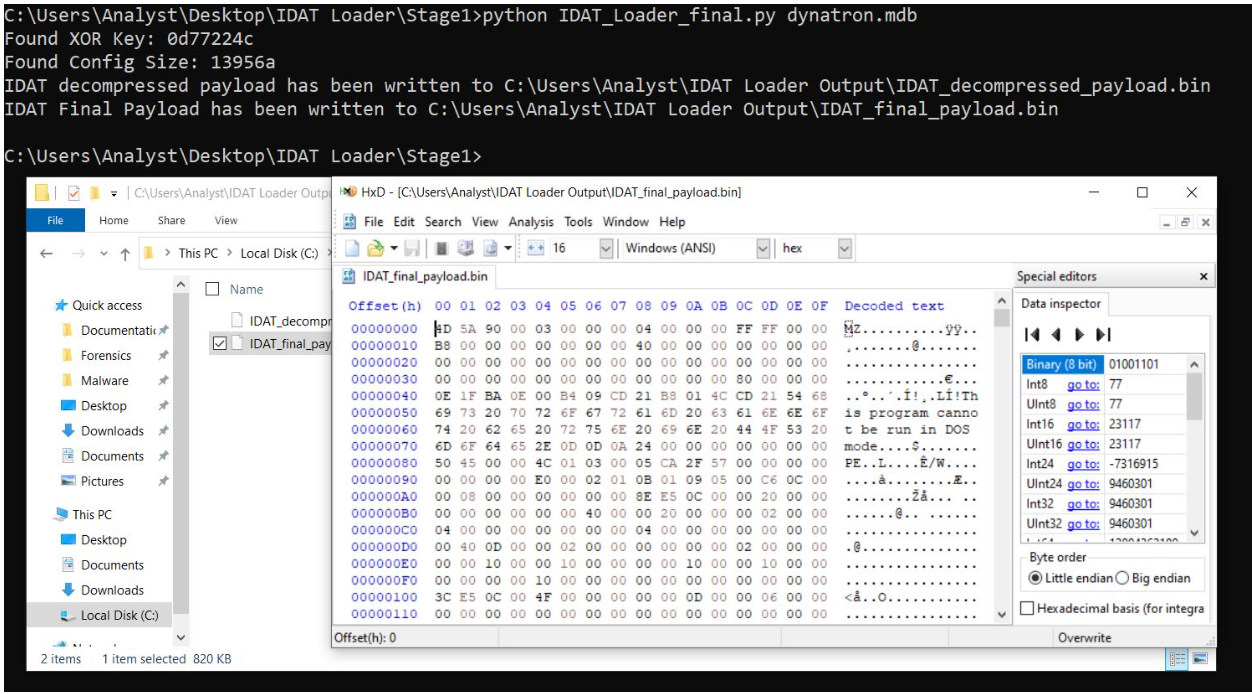
Using our IDAT Loader config extractor, we were able to extract the final payload and determined that it was SecTop RAT. During execution of the SecTop RAT, we observed that it communicated with the IP address 152.89.217[.]215.
Post-Exploitation: BRC4 Deployment
After the SecTop RAT was executed successfully, Rapid7 observed follow-on activity in which the threat actor executed another version of the IDAT loader from within the folder path C:ProgramData. We observed the following related files were dropped by the threat actor into C:ProgramData:
| Files | Description |
|---|---|
| glib-2.0.dll | Benign executable loaded by rvm.exe |
| iconv.dll | Benign executable loaded by rvm.exe |
| intl.dll | Benign executable loaded by rvm.exe |
| rvm.exe | Legitimate executable that loads vmtools.dll during execution |
| spank.mpg | Encrypted file containing IDAT sections, read in by vmtools.dll |
| vmtools.dll | Tampered DLL containing IDAT Loader, loaded by rvm.exe |
After analysis of the files, we determined that rvm.exe was a renamed executable rvmsetup.exe, a legitimate tool that is a part of the VMWare Tools toolset. The binary is used to join a VMWare source virtual machine to an active directory domain. We also observed that the binary vmtools.dll had a corrupted signature, indicating the binary’s code was tampered with. We observed that the DLL vmtools.dll contained code related to the IDAT Loader.
During execution of the executable, rvm.exe, the program loads vmtools.dll. After vmtools.dll is loaded, the DLL is directed to execute a function that contains the IDAT Loader. The IDAT Loader proceeds to read in contents from within spank.mpg, searching for the same offset, 49 44 41 54 (IDAT) followed by C6 A5 79 EA. After decrypting the contents within spank.mpg, the IDAT Loader spawns a new process, cmd.exe, injecting additional code that is responsible for decrypting the final payload and injecting it into a newly created process, explorer.exe.
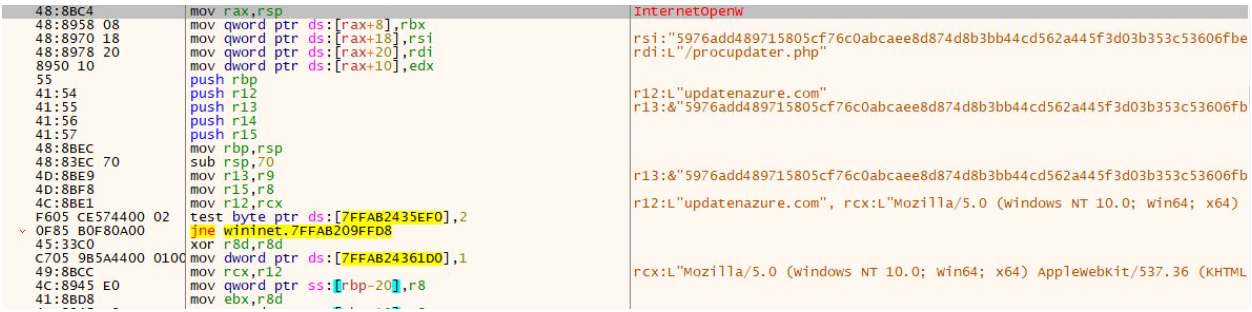
Using our static config extractor, we extracted the final payload, a 64-bit executable. During initial analysis of the final payload, we observed that the program utilized the API functions VirtualAlloc and VirtualProtect. During execution of the program, it utilized VirtualAlloc to read in and store additional code, including encrypted data, into a new region of memory. The program then called upon the function VirtualProtect, changing the newly allocated region of memory (containing the new code) to be executable. We also observed the 64 bit executable (obtained from the IDAT Loader python script) had the capability to perform process hollowing by starting a new process, notepad.exe, and injecting the code into the newly created process.
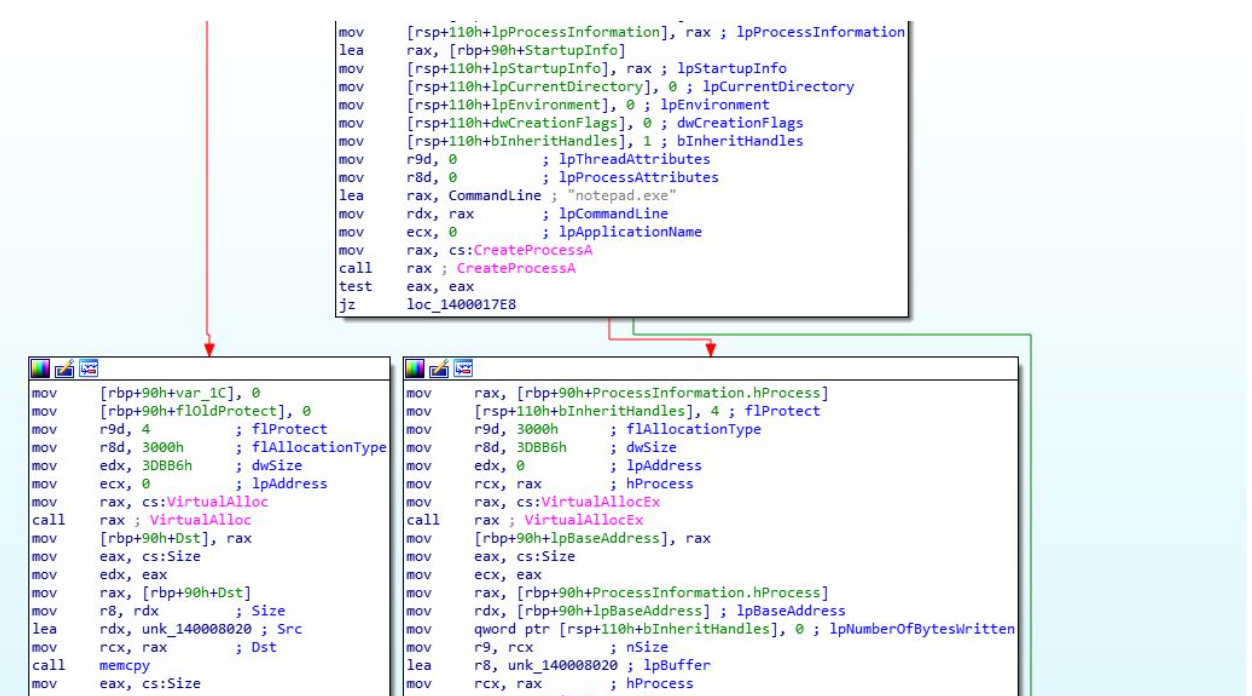
The newly allocated code was responsible for decrypting the encrypted data using RC4, copying the decrypted code into an allocated memory buffer via VirtualAlloc, and setting the memory buffer to have executable permission using VirtualProtect. Rapid7 determined the decrypted code was a Brute Ratel C4 (BRC4) “badger”.
Brute Ratel originated as a post-exploitation tool intended for penetration testers, designed to mimic adversary tactics as of December 2020. Its development aimed to replicate the functionality of established Command and Control (C2) software like Cobalt Strike, Mythic and Sliver. Following a successful compromise of a target, the attacker deploys the Brute Ratel “badger,” tasked with establishing communication with the attacker’s Command and Control domain.
During execution of the BRC4 program, we observed that it reached out to the domain updatenazure[.]com.
After the BRC4 program was executed, we observed the threat actor attempting to enumerate the domain controller by using the command nltest /dclist.
Rapid7 Customers
InsightIDR and Managed Detection and Response customers have existing detection coverage through Rapid7’s expansive library of detection rules. Rapid7 recommends installing the Insight Agent on all applicable hosts to ensure visibility into suspicious processes and proper detection coverage. Below is a non-exhaustive list of detections deployed and alerting on activity described:
- Network Discovery – Nltest Enumerate Domain Controllers
- Suspicious Process – Execution From Root of ProgramData
- Suspicious Process – PowerShell Uncommon Upper And Lower Case Combinations
- Suspicious Process – explorer.exe in Non-Standard Location
| Usernames | Processes |
|---|---|
| hbyldjtckyn1 | httpdebuggerui.exe |
| lubi53an14cu | immunitydebugger.exe |
| rgzcbuyrznreg | ksdumperclient.exe |
| 8lnfaai9qdjr | httpanalyzerstdv7.exe |
| j6sha37ka | ida64.exe |
| keecfmwgj | 32dbg.exe |
| pwouqdtdq | 64dbg.exe |
| qmis5df7u | protection_id.exe |
| txwas1m2t | vmsrvc.exe |
| uox1tzamo | x32dbg.exe |
| rb5bnfur2 | x64dbg.exe |
| cm0uegn4do | x96dbg.exe |
| douyo8rv71 | prl_cc.exe |
| paul jones | windbg.exe |
| pxmduopvyx | scylla.exe |
| fnbdsldtxy | idau64.exe |
| gexwjqdjxg | idaq64.exe |
| gjam1nxxvm | idag64.exe |
| jcotj17dzx | taskmgr.exe |
| 05kvauqkpqk5 | procexp.exe |
| 64f2tkiqo5k5h | procmon.exe |
| of20xqh4vl | fiddler.exe |
| harry johnson | dumpcap.exe |
| 4tgiizslims | df5serv.exe |
| bvjchrpnsxn | ollydbg.exe |
| kfu0lqwgx5p | rdpclip.exe |
| nok4zg7zhof | vmusrvc.exe |
| ogjb6gqgk0o5 | qemu-ga.exe |
| xplyvzr8sgc | vboxtray.exe |
| ykj0egq7fze | vmtoolsd.exe |
| ryjijkiroms | pestudio.exe |
| nzap7ubvas1 | vmacthlp.exe |
| 9yjcpseyimh | procexp64.exe |
| uhuqiuwoefu | wireshark.exe |
| 6o4kyhhjxbir | prl_tools.exe |
| 7wjlgx7pjlw4 | importrec.exe |
| 8nl0colnq5bq | vmwaretray.exe |
| g2dbyldgzz8yo | vmwareuser.exe |
| pqonjhvwexsst | xenservice.exe |
| rdhj0cnfevzxf | scylla_x86.exe |
| xmimmckziitdl | scylla_x64.exe |
| l3cnbb8ar5b8 | vboxservice.exe |
| vzy4jmh0jw02 | |
| 21zlucunfi85 | |
| sal.rosenburg | |
| defaultaccount | |
| wdagutilityaccount |
MITRE ATT&CK Techniques
| Tactics | Techniques | Details |
|---|---|---|
| Initial Access | Drive-by Compromise (T1189) | Threat Actors utilize drive-by downloads in order to direct browsers to download their initial payloads without users consent |
| Execution | User Execution: Malicious File (T1204.002) | Users execute the binary AppFile_v1.1.exe |
| Execution | Native API (T1106) | The IDAT injector and IDAT loader are using Heaven’s Gate technique to evade detection |
| Defense Evasion | Hijack Execution Flow: DLL Search Order Hijacking (T1574.001) | run.exe loads a malicious wbxtrace.dll |
| Defense Evasion | Process Injection (T1055) | IDAT injector implements NtCreateSection + NtMapViewOfSection Code Injection technique to inject into cmd.exe process |
| Defense Evasion | Deobfuscate/Decode Files or Information (T1140) | msidcrl40.dll decrypts dynatron.mdb |
| Defense Evasion | Process Injection: Process Doppelgänging (T1055.013) | IDAT loader implements Process Doppelgänging technique to load the SecTop RAT |
| Defense Evasion | Masquerading (T1036) | dynatron.mdb file masqueraded to a .png file |
| Defense Evasion | Virtualization/Sandbox Evasion: Time Based Evasion (T1497.003) | Execution delays are performed by several stages throughout the attack flow |
IOCs
| IOC | Sha256 | Notes |
|---|---|---|
| AppFile_v1.1.exe | A3A5E7011335A2284E2D4F73FD464FF129F0C9276878A054C1932BC50608584B | Rust Loader responsible for downloading IDAT Loader |
| msidcrl40.dll | 02D5E281689EC2D4AB8AC19C93321A09113E5D8FA39380A7021580EA1887B7A5 | Malicious DLL executed by live.exe |
| dynatron.mdb | C5C52331B208CAD19DC710786E26AC55090FFCA937410D76C53569D731F0BB92 | Encrypted payload decrypted by msidcrl40.dll |
| vmtools.dll | BEFE0DF365F0E2DC05225470E45FDF03609F098A526D617C478B81AC6BB9147F | Malicious DLL executed by rvm.exe |
| spank.mpg | E05E561C5118EFDBCA113CA231C527B62E59A4BFFAE3BD374F7B4FCDD10E7D90 | Encrypted payload decrypted by vmtools.dll |
| hxxps://cdn-network-services-001[.]com/update/minor/1/release.json | Downloads additional Rust binary containing IDAT Loader | |
| 152.89.217[.]215 | SecTop RAT domain | |
| updatenazure[.]com | BRC4 Domain |
Rapid7 Labs GitHub
https://github.com/rapid7/Rapid7-Labs/blob/main/Malware Config Extractors/IDAT_Loader_extractor.py
Source: Original Post