Aqua Nautilus researchers have uncovered a new multi-stage attack campaign focused on interactive computing environments like Jupyter Notebooks. The attackers exploit unauthenticated instances to deploy malicious tools, hijack system resources, and maintain persistence, posing significant risks to cloud-native environments. Enhanced security measures are crucial to defend against such threats.
Affected: Jupyter Notebooks, JupyterLab, Apache Zeppelin, Google Colab, Databricks Notebooks
Affected: Jupyter Notebooks, JupyterLab, Apache Zeppelin, Google Colab, Databricks Notebooks
Keypoints :
- New attack campaign targets interactive computing environments, particularly Jupyter Notebooks.
- Initial access achieved through unauthenticated JupyterLab instances.
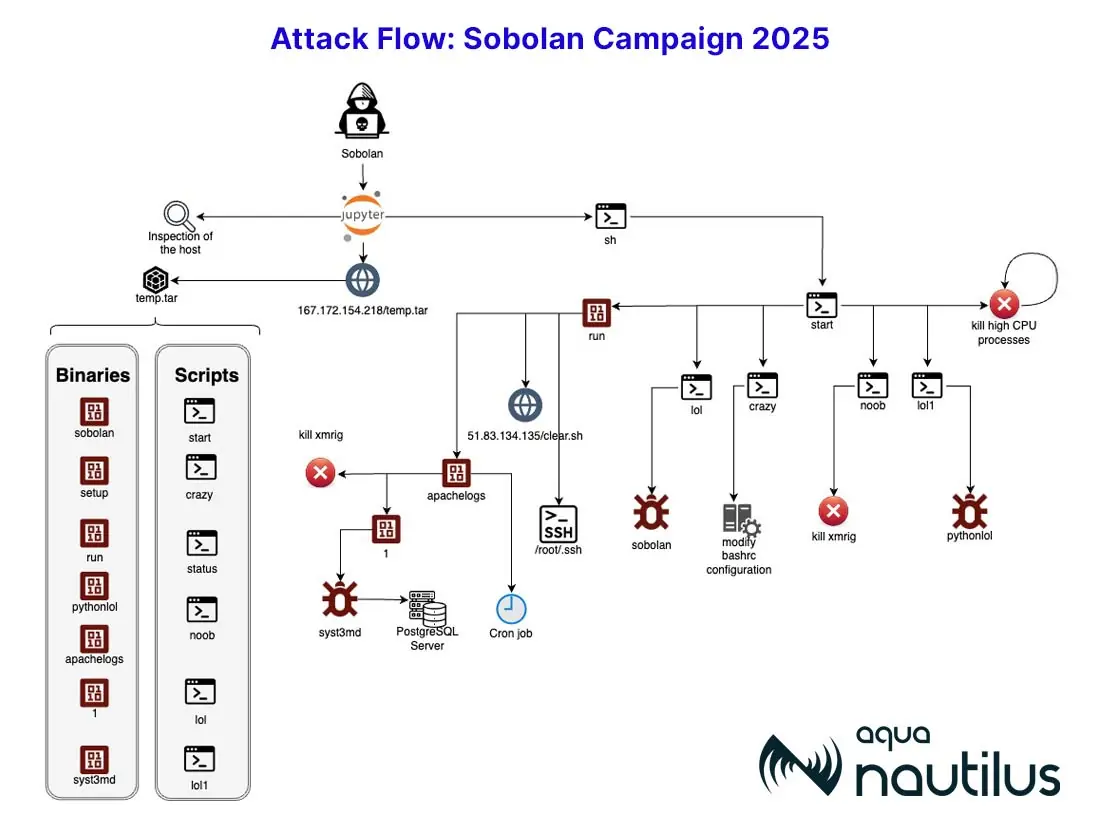
- Attack involves downloading a compressed file containing 13 malicious files.
- Attacker executes scripts to establish persistence and hijack system resources for cryptomining.
- Mitigation strategies include customizing threat intelligence feeds and configuring runtime policies.
- Aqua’s Runtime Protection detected and blocked multiple threats during the attack.
MITRE Techniques :
- TA0001: Initial Access – Exploited unauthenticated JupyterLab instance to gain entry.
- TA0010: Execution – Executed malicious scripts from the downloaded compressed archive.
- TA0034: Persistence – Implemented multiple processes to maintain control over the compromised system.
- TA0043: Reconnaissance – Scanned for .ssh credentials and other sensitive information.
- TA0040: Impact – Hijacked system resources for cryptomining operations.
Indicator of Compromise :
- [IP Address] 37.201.213.226 (Attacker IP)
- [IP Address] 167.172.154.218 (Download server)
- [Binary file] MD5: 305f278eaf452f7e0b8d788e433278c6 (pythonlol)
- [Binary file] MD5: 7849983d77b052de90558feeefb3078d (sobolan)
- [Binary file] MD5: 9e39b0a7baca08a77c4716e5581660b2 (apachlogs)
Full Story: https://blog.aquasec.com/stopping-sobolan-with-aqua-runtime-protection