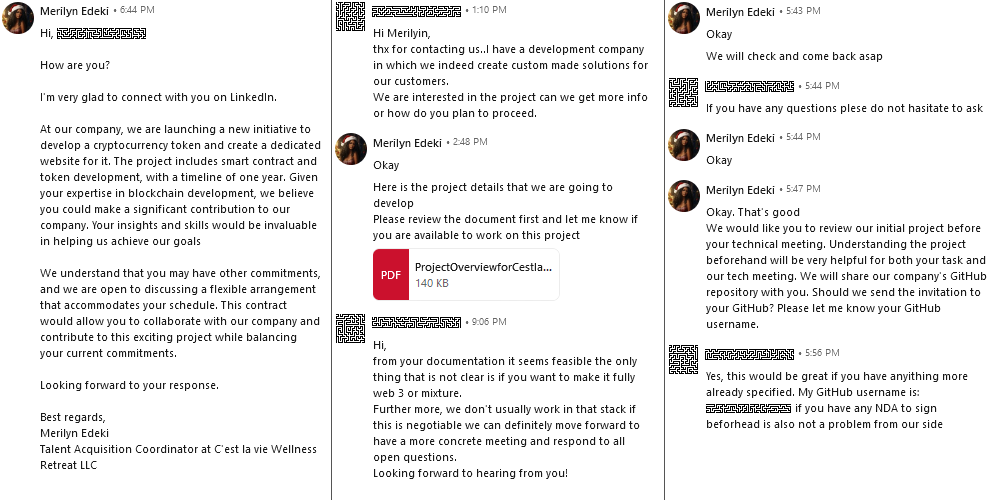
This article discusses a sophisticated cyber attack involving threat actors posing as job seekers via LinkedIn to lure victims into executing malicious code. The attack primarily targets individuals and companies engaged in Web3 technologies, utilizing malicious scripts named BeaverTail (Node.js) and InvisibleFerret (Python), which steal data and maintain backdoors in infected systems. Affected: Web3 companies, individual users
Keypoints :
- Attackers impersonate job seekers on LinkedIn to initiate contact.
- Malicious links lead to the execution of harmful scripts that steal data.
- Targets include firms working with smart contracts, cryptocurrencies, and blockchain technology.
- The malware operates in two main parts: BeaverTail (Node.js) and InvisibleFerret (Python).
- Reports link the attack methodology to state-sponsored actors from North Korea.
- Analysis shows use of Node.js Package Manager (NPM) for packaging malicious code.
- Obfuscation techniques are used to hide malicious code within legitimate projects.
- Data is exfiltrated to a Command and Control (C2) server via HTTP POST requests.
- Specific data can include system information, browser credentials, and other sensitive information.
- Malware can execute remote commands via the C2 server after establishing a connection.
MITRE Techniques :
- T1041 – Exfiltration Over Command and Control Channel: The malware sends system information and stolen credentials to the attacker’s server via HTTP POST requests.
- T1210 – Exploitation of Remote Services: Attackers exploit vulnerabilities in an application to execute malicious code.
- T1071 – Application Layer Protocol: Command and control communications are established via standard HTTP/S protocols.
- T1105 – Ingress Tool Transfer: Transferring malicious payloads from the C2 server to the infected system for execution.
- T1030 – Data Transfer Size Limits: The malware collects data in phases, limiting the size of transferred data to evade detection.
Indicator of Compromise :
- [URL] hxxp://23[.]106.253.221:1244/keys
- [URL] hxxp://23[.]106.253.221:1244/j/ZU1RINz7
- [URL] hxxp://23[.]106.253.221:1244/pdown
- [URL] hxxp://23[.]106.253.221:1244/uploads
- [SHA256] userRoutes.js 4f632429fedb39fa2addaeff3ba900679ebff99e45353d523776831e2558df80
Full Story: https://www.cert.si/tz016/