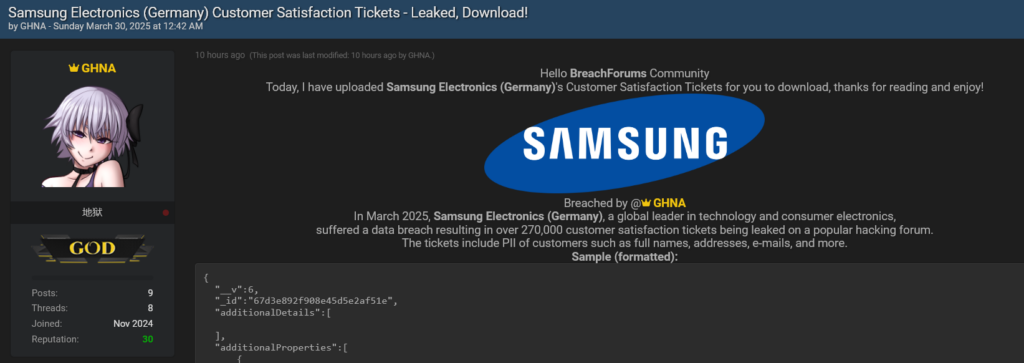
This article discusses a massive data breach impacting Samsung Germany, where a hacker known as “GHNA” leaked approximately 270,000 customer tickets due to credentials stolen by infostealer malware back in 2021. The breach highlights the dangers of unmonitored and unrotated credentials, leading to potential exploitation and privacy violations for thousands of customers. This incident serves as a wake-up call for companies to actively monitor and protect against infostealers. Affected: Samsung Germany, Customers, Cybersecurity Sector
Keypoints :
- 270,000 customer tickets from Samsung Germany were leaked online.
- The breach resulted from stolen credentials acquired by Raccoon Infostealer malware in 2021.
- Credentials were stored and remained unmonitored until exploited by the hacker “GHNA”.
- Leaked data included PII, transactional details, and support interactions.
- The breach showcases the vulnerability of companies failing to rotate and monitor login credentials.
- Implications for victims include potential physical attacks and hyper-targeted phishing scams.
- AI can be used to extract and exploit data from breaches at scale rapidly.
- Companies need to proactively manage stolen credentials to avoid such breaches.
- The incident has significant implications for Samsung regarding PR and GDPR compliance.
MITRE Techniques :
- Credential Dumping (T1003) – Credentials stolen by infostealer malware from employee devices.
- Credential Dumping through Infostealer (T1003.003) – Raccoon Infostealer harvested login credentials over extended periods.
- Account Manipulation (T1071.001) – Potential for hackers to impersonate customer support using stolen credentials for account takeovers.
Indicator of Compromise :
- [Email Address] josi_92@gmx.de
- [Email Address] Tilo.Schmidt@telusinternational.com
- [Ticket ID] 230406.0095829
- [Ticket ID] 230621.0105676
- [Order Number] DE2213214-32511544