This report analyzes various cyber threats targeting diverse sectors, with a focus on malicious campaigns and tools utilized by actors from different regions. Notably, the Sandworm APT’s espionage against Ukrainian users highlights threats to national security, while other reported incidents reveal exploitation of vulnerabilities and the increasing sophistication of ransomware tactics. Overall, these threats pose significant risks to individual users, organizations, and critical infrastructure. Affected: Ukrainian users, cryptocurrency entities, sectors including manufacturing, healthcare, finance, civil society, foreign ministries, software and services companies
Keypoints :
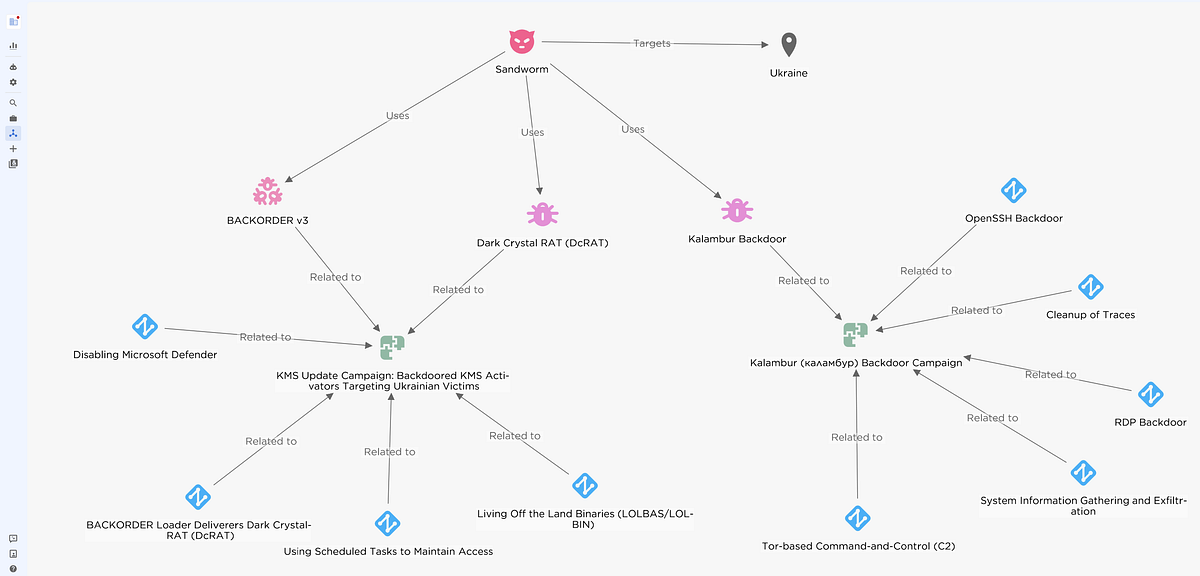
- Sandworm APT targets Ukrainian users with trojanized KMS activation tools, compromising security and enabling data exfiltration.
- Recent NetSupport RAT distribution exploits social engineering to manipulate users into executing malicious commands.
- North Korean group PurpleBravo exploits remote work to target cryptocurrency industries, emphasizing fraud and data theft.
- Ivanti CSA vulnerabilities allow unauthorized access, impacting critical sectors across the U.S. and France.
- Escalating cyber threats from North Korean APTs against civil society organizations reveal social engineering tactics.
- REF7707 campaign employing advanced malware specifically targets governmental and political institutions.
- FINALDRAFT malware utilizes Outlook for command and control, exhibiting advanced data exfiltration techniques.
- Pyramid C2 framework assists cyber actors in evading detection while executing stealthy operations.
- BadPilot campaign of the Seashell Blizzard subgroup primarily targets sensitive governmental and telecommunications sectors.
- RA World ransomware incident indicates a tactical shift among Chinese espionage actors towards financially motivated cybercrime.
MITRE Techniques :
- Initial Access: Tactic: Phishing (Spear Phishing) – Technique ID: T1566, Procedure: North Korean group targets users with spear-phishing techniques.
- Execution: Tactic: PowerShell (T1086) – Technique ID: TA569 uses PowerShell commands to execute the NetSupport RAT.
- Persistence: Tactic: Backdoor (T1100) – Sandworm uses Kalambur RDP backdoor for establishing persistent access.
- Command and Control: Tactic: Exfiltration Over Command and Control Channel (T1041) – Pyramid C2 acts as a command and control server.
- Data Exfiltration: Tactic: Data Exfiltration (T1041) – Technique: FINALDRAFT transmits sensitive information through named pipes.
Indicator of Compromise :
- [IP Address] 5.255.122.118
- [Domain] kalambur.net
- [URL] https://activationsmicrosoft.com/activationsmicrosoft.php
- [SHA256] afc6131b17138a6132685617aa60293a40f2462dc3a810a4cf745977498e0255
- [Email Address] alexander@agencyhill99.com
Full Story: https://medium.com/@rst_cloud/rst-ti-report-digest-17-feb-2025-0da240597f4e?source=rss——cybersecurity-5