This report provides a comprehensive overview of recent cybersecurity threats from various actors, detailing their tactics, techniques, and indicators of compromise. The analysis covers sophisticated groups like XE Group, MuddyWater, and others, revealing their complex operations and targeting sectors affected by ongoing geopolitical tensions, particularly within financial and governmental infrastructures. The report highlights key IOCs associated with their operations for enhanced detection and response measures. Affected: Cybersecurity, Financial Sector, Governmental Agencies
Keypoints :
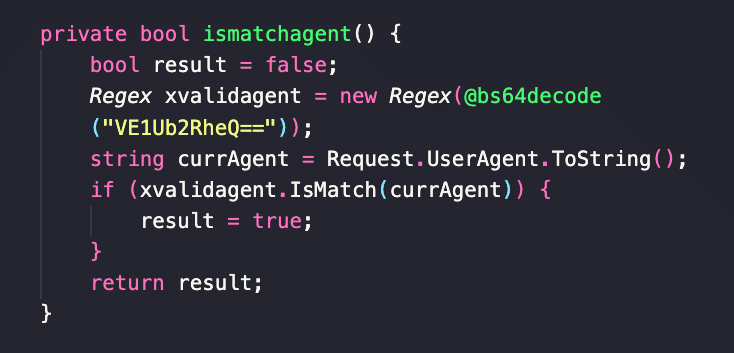
- XE Group has shifted focus from credit card skimming to targeted information theft, exploiting zero-days.
- MuddyWater conducts spear-phishing campaigns primarily targeting Israeli entities and employs advanced malware tactics.
- UAC-0006 targets Ukraine’s largest state-owned bank with phishing tactics and SmokeLoader malware.
- LockBit’s influence endures, as it evolves with persistent TTPs and tools for data exfiltration.
- ValleyRAT malware employs multi-stage attacks through phishing, targeting financial roles.
- Zero-day vulnerabilities in 7-Zip were exploited in attacks against Ukrainian organizations.
- SmokeLoader malware was identified in open directories targeting Ukraine’s banking and automotive industries.
- Premium Panel phishing tools have been operational targeting multiple financial sectors.
- Reports of cloned university sites to distribute malware under the guise of legitimate tools.
- Vidar malware is adopting advanced techniques for dynamic domain generation and variable payload distribution.
MITRE Techniques :
- Initial Access: Spear Phishing (T1566) – Used by MuddyWater to deliver malware.
- Exploitation for Client Execution (T1203) – Used in CVE-2025-0411 exploitation.
- Command and Control (T1071) – Used by XE Group for ASPX webshells.
- Data Exfiltration (T1041) – LockBit employs it for sensitive data extraction.
- Credential Dumping (T1003) – Utilized by UAC-0006 in attacks against PrivatBank.
- SQL Injection (T1190) – Not explicitly mentioned but implied in exploiting web vulnerabilities.
- Phishing (T1566) – Common tactic used across various reported incidents.
Indicator of Compromise :
- [IP Address] 171[.]227[.]250[.]249
- [Domain] xegroups[.]com
- [URL] https://hivnd[.]com/software/7z[.]exe
- [SHA-256] 884c394c7b3eb757ae57050ac2e6a75385a361555e8e4272de1a3cf24746eec7
- [Email Address] xecloud@icloud[.]com
Full Story: https://medium.com/@rst_cloud/rst-ti-report-digest-10-feb-2025-2b0188998044?source=rss——cybersecurity-5