This research by Bitdefender Labs introduces the QWCrypt ransomware campaign, linked to the RedCurl group, marking a significant shift in their tactics from data exfiltration to ransomware. RedCurl has been operating since 2018 but has historically utilized Living-off-the-Land techniques for corporate espionage. Their targeting of specific infrastructures and the use of hypervisor encryption underscores a sophisticated evolution in their operational strategy, raising questions regarding their motivations and business model. Affected: ransomware, corporate espionage, cybersecurity sector, IT infrastructure.
Keypoints :
- RedCurl, also known as Earth Kapre or Red Wolf, has transitioned from corporate cyber espionage to ransomware attacks.
- The new ransomware strain, QWCrypt, is distinct and previously undocumented.
- RedCurl’s operations have persisted since 2018, primarily targeting organizations in the US, Germany, Spain, and Mexico.
- Data exfiltration without public ransom demands suggests a more discreet operational strategy.
- RedCurl may be acting as a ‘gun-for-hire’ group, potentially motivated by financial gain through ransomware.
- The ransomware specifically targets hypervisors, caused massive disruption by encrypting virtual machines.
- The operational strategy involves customizing scripts and attacks based on the victim’s environment.
- Attackers utilize LOTL techniques and Windows tools to evade detection.
MITRE Techniques :
- Initial Access (T1071.001): Phishing emails with IMG files that mount as virtual drives.
- Execution (T1203): Execution occurs via the exploitation of a DLL sideloading vulnerability within Adobe executables.
- Persistence (T1053): Scheduled tasks for executing persistent malware components.
- Lateral Movement (T1086): Utilization of WMI and built-in Windows tools for remote command execution.
- Exfiltration (T1041): Utilization of curl.exe for data transfer to remote locations.
- Impact (T1486): Deployment of ransomware targeting hypervisors to disrupt IT infrastructure.
Indicator of Compromise :
- [File] %AppData%RoamingBrowserSpecBrowserSpec_.dll
- [Hash] a806df529a111fb453175ecdcb230d96
- [File] C:ProgramDatarbcw.exe
- [Hash] 27927a73b8273dc796ddfc309ec8ecaf
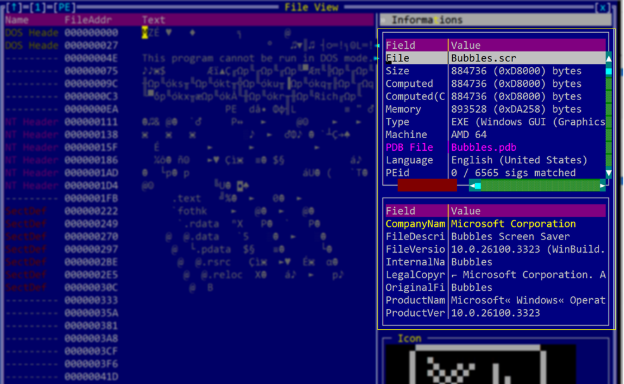
- [Hash] 9f7b1afce9c8c7d9282c5e791c69e369 (for CV_APPLICANT_7802-91542.SCR)
Full Story: https://www.bitdefender.com/en-us/blog/businessinsights/redcurl-qwcrypt-ransomware-technical-deep-dive