Summary: An extensive security audit of QNAP QTS, the operating system for the company’s NAS products, has uncovered fifteen vulnerabilities, with eleven remaining unfixed.
Threat Actor: WatchTowr Labs | WatchTowr Labs
Victim: QNAP | QNAP
Key Point :
- An extensive security audit of QNAP QTS has uncovered fifteen vulnerabilities, including an unpatched stack buffer overflow vulnerability in the ‘No_Support_ACL’ function of ‘share.cgi’ that could enable remote code execution.
- The vendor has only fixed four of the fifteen vulnerabilities and has responded to the reports with multiple delays.
- The vulnerabilities were discovered by WatchTowr Labs, who published the complete details of their findings and a proof of concept (PoC) exploit for one of the vulnerabilities.
- The flaws primarily relate to code execution, buffer overflows, memory corruption, authentication bypass, and XSS issues.

An extensive security audit of QNAP QTS, the operating system for the company’s NAS products, has uncovered fifteen vulnerabilities of varying severity, with eleven remaining unfixed.
Among them is CVE-2024-27130, an unpatched stack buffer overflow vulnerability in the ‘No_Support_ACL’ function of ‘share.cgi,’ which could enable an attacker to perform remote code execution when specific prerequisites are met.
The vendor responded to the vulnerability reports submitted between December 12, 2023, and January 23, 2024, with multiple delays and has fixed only four of the fifteen flaws.
The vulnerabilities were discovered by WatchTowr Labs, who published the complete details of their findings and a proof of concept (PoC) exploit for CVE-2024-27130 on Friday.
The QTS vulnerabilities
The flaws uncovered by WatchTowr analysts are primarily related to code execution, buffer overflows, memory corruption, authentication bypass, and XSS issues, impacting the security of Network Attached Storage (NAS) devices across different deployment environments.
WatchTowr lists a total of fifteen flaws, summarized as follows:
- CVE-2023-50361: Unsafe use of sprintf in getQpkgDir invoked from userConfig.cgi.
- CVE-2023-50362: Unsafe use of SQLite functions accessible via parameter addPersonalSmtp to userConfig.cgi.
- CVE-2023-50363: Missing authentication allows two-factor authentication to be disabled for arbitrary users.
- CVE-2023-50364: Heap overflow via long directory name when file listing is viewed by get_dirs function of privWizard.cgi.
- CVE-2024-21902: Missing authentication allows all users to view or clear system logs and perform additional actions.
- CVE-2024-27127: A double-free in utilRequest.cgi via the delete_share function.
- CVE-2024-27128: Stack overflow in check_email function, reachable via the share_file and send_share_mail actions of utilRequest.cgi.
- CVE-2024-27129: Unsafe use of strcpy in get_tree function of utilRequest.cgi.
- CVE-2024-27130: Unsafe use of strcpy in No_Support_ACL accessible by get_file_size function of share.cgi.
- CVE-2024-27131: Log spoofing via x-forwarded-for allows users to cause downloads to be recorded as requested from arbitrary source locations.
- WT-2023-0050: Under extended embargo due to an unexpectedly complex issue.
- WT-2024-0004: Stored XSS via remote syslog messages.
- WT-2024-0005: Stored XSS via remote device discovery.
- WT-2024-0006: Lack of rate-limiting on authentication API.
- WT-2024-00XX: Under 90-day embargo as per VDP.
The above bugs impact QTS, the NAS operating system on QNAP devices, QuTScloud, the VM-optimized version of QTS, and QTS hero, a specialized version focused on high performance.
QNAP has addressed CVE-2023-50361 through CVE-2023-50364 in a security update released in April 2024, in versions QTS 5.1.6.2722 build 20240402 and later, and QuTS hero h5.1.6.2734 build 20240414 and later.
However, all the other vulnerabilities discovered by WatchTowr remain unaddressed.
PoC for zero-day RCE
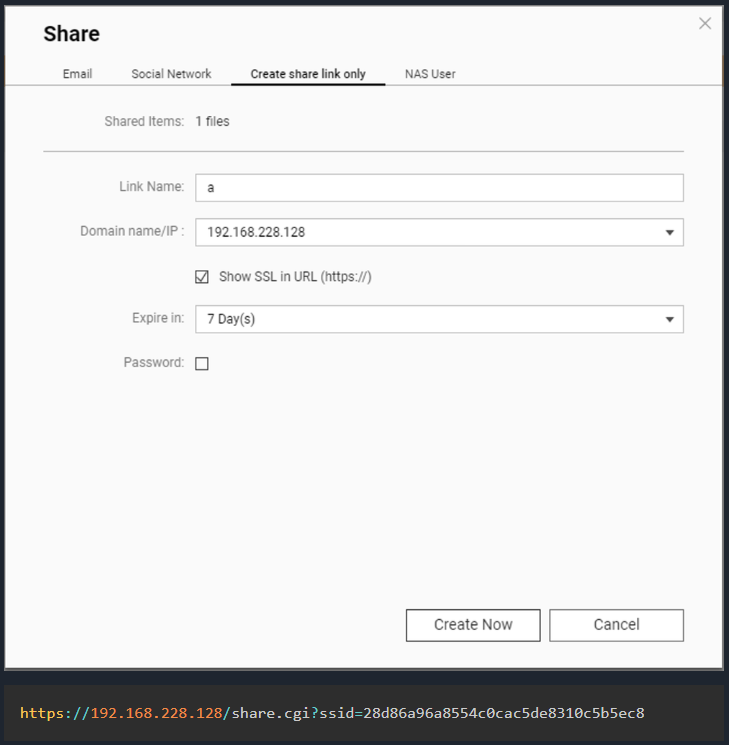
The QNAP CVE-2024-27130 vulnerability is caused by the unsafe use of the ‘strcpy’ function in the No_Support_ACL function. This function is utilized by the get_file_size request in the share.cgi script, used when sharing media with external users.
An attacker can craft a malicious request with a specially crafted ‘name’ parameter, causing the buffer overflow leading to remote code execution.
To exploit CVE-2024-27130, the attacker needs a valid ‘ssid’ parameter, which is generated when a NAS user shares a file from their QNAP device.
This parameter is included in the URL of the ‘share’ link created on a device, so an attacker would be required to use some social engineering to gain access to it. However, BleepingComputer found that users sometimes share these links online, allowing them to be indexed and retrieved from a simple Google search.
Source: WatchTowr
In summary, CVE-2024-27130 isn’t straightforward to exploit, yet the SSID prerequisite can be met for determined actors.
WatchTowr published an exploit on GitHub, in which they demonstrate how to craft a payload that creates a ‘watchtowr’ account to a QNAP device and adds them to the sudoers for elevated privileges.
BleepingComputer has contacted QNAP for a statement on the disclosed flaws, but a comment wasn’t immediately available.
“An interesting youtube video that may be related to the article above”