The article provides walkthroughs for various challenges in the PicoCTF 2025 competition, focusing on different aspects of cybersecurity such as cryptography, reverse engineering, and web exploitation. It details methods for cracking hashes, decoding encrypted messages, analyzing binaries, and exploiting web vulnerabilities to capture flags. Affected: cybersecurity sector, educational platforms
Keypoints :
- The first challenge involves cracking an MD5 hash using online tools.
- Subsequent hashes include SHA-1 and SHA-256, which are also cracked using decoding tools.
- The RCA challenge shows that an RSA cipher can be easily broken.
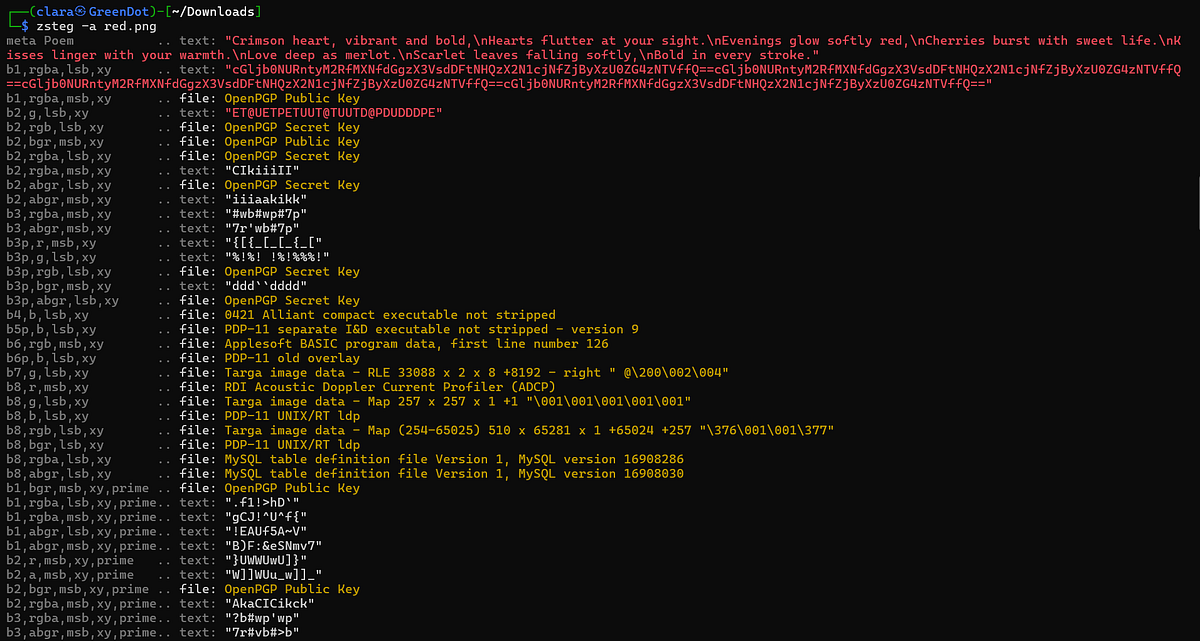
- Binary Instrumentation challenges examine Windows executables for embedded data.
- Extraction of data from .ATOM sections in binaries suggests the use of unknown packers.
- Exploitation of web vulnerabilities in the SSTI challenges involves executing payloads to retrieve hidden information.
- File upload vulnerabilities allow for the deployment of web shells to execute commands on the server.
- Indicator for RCE (Remote Code Execution) was found through the eval function in Python.
- The SHAttered exploit allows for SHA1 hash collisions to obtain flags.
- API exploration shows potential weaknesses that expose sensitive data.
- Cookie manipulation post-login reveals encoded flags hidden within session cookies.
Full Story: https://infosecwriteups.com/picoctf-2025-walkthrough-24b753e81721?source=rss—-7b722bfd1b8d—4