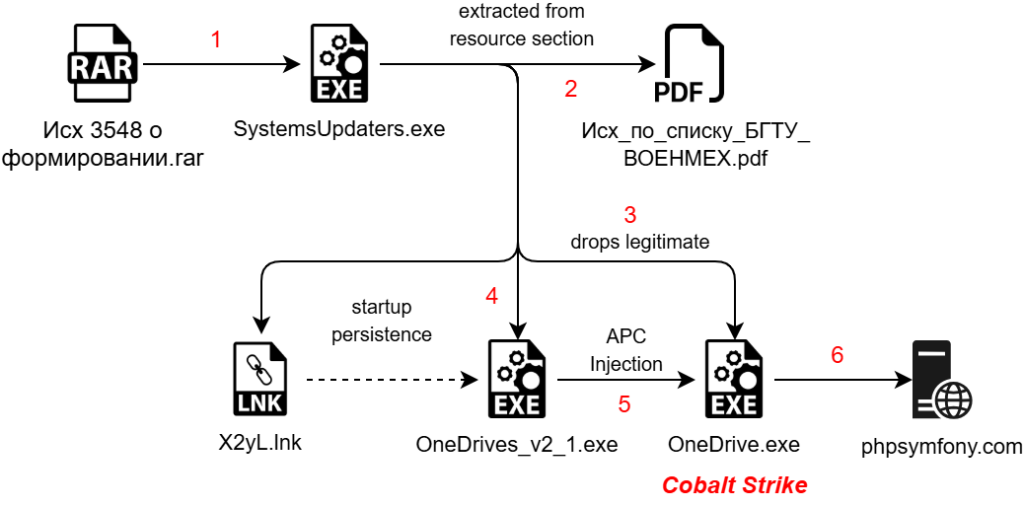
The article discusses Operation HollowQuill, a targeted cyber campaign against the Baltic State Technical University, designed to infiltrate academic and defense networks through weaponized decoy documents. The attack utilizes a multi-stage infection chain, including a malicious RAR file, a .NET malware dropper, Golang shellcode, and a Cobalt Strike payload. Affected: Baltic State Technical University, Academic Institutions, Military & Defense Industry, Government Research Entities, Russian Federation
Keypoints :
- Operation HollowQuill targets the Baltic State Technical University.
- Utilizes weaponized decoy documents posing as official research invitations.
- Infection chain includes a malicious RAR file containing a .NET dropper and Golang shellcode.
- The final payload delivered is a Cobalt Strike beacon.
- Geographical focus is on the Russian Federation.
- Technical analysis reveals multiple stages of the malware, including infection mechanisms and persistence techniques.
- Indicators of compromise (IOCs) include malicious file hashes and command-and-control server details.
- The attack employs various MITRE ATT&CK techniques for effective execution.
MITRE Techniques :
- T1566.001 – Phishing: Spear phishing Attachment – Exploits spear phishing attachments to gain initial access.
- T1204.002 – User Execution: Malicious File – Requires user interaction to execute the malicious file.
- T1053.005 – Scheduled Task – Utilizes scheduled tasks for execution persistence.
- T1547.001 – Registry Run Keys / Startup Folder – Uses startup folder placement for persistence.
- T1036 – Masquerading – Masquerades known applications to evade detection.
- T1027.009 – Embedded Payloads – Uses embedded payloads within legitimate files.
- T1055.004 – Asynchronous Procedure Call – Implements APC injection for code execution in legitimate processes.
- T1497.003 – Time Based Evasion – Uses time-based checks to evade analysis.
- T1132.001 – Data Encoding: Standard Encoding – Encodes data to evade detection in command-and-control communications.
Indicator of Compromise:
- [MD5] ab310ddf9267ed5d613bcc0e52c71a08 – Исх 3548 о формировании государственных заданий на проведение фундаментальных и поисковых исследований БГТУ «ВОЕНМЕХ» им. Д.Ф. Устинова.rar
- [MD5] fad1ddfb40a8786c1dd2b50dc9615275 – SystemsUpdaters.exe
- [MD5] cac4db5c6ecfffe984d5d1df1bc73fdb – OneDrives_v2_1.exe
- [C2] phpsymfony[.]com
- [URL] hxxps://phpsymfony[.]com/css3/index2.shtml
Full Story: https://www.seqrite.com/blog/operation-hollowquill-russian-rd-networks-malware-pdf/