
Threat Actor: Unknown | unknown
Victim: Ukrainian military personnel | Ukrainian military personnel
Key Point :
- The malicious installer disguises itself as a legitimate application, requesting administrative privileges to gain user trust.
- PowerShell scripts are used to modify execution policies and conceal malicious activities from the user.
- The malware establishes a persistent backdoor using Tor for covert communication, allowing attackers to execute commands remotely.
- Components of the malware are distributed across different folders, with critical scripts hidden within the installation package.
Researchers recently discovered a malicious campaign targeting Ukrainian military personnel through fake “Army+” application websites, which host a malicious installer that, upon execution, extracts the legitimate application alongside the Tor browser.
The installer includes a PowerShell script that indicates the Tor browser’s inclusion is not for legitimate use, suggesting it’s likely intended for covert communication or data exfiltration by the attackers.
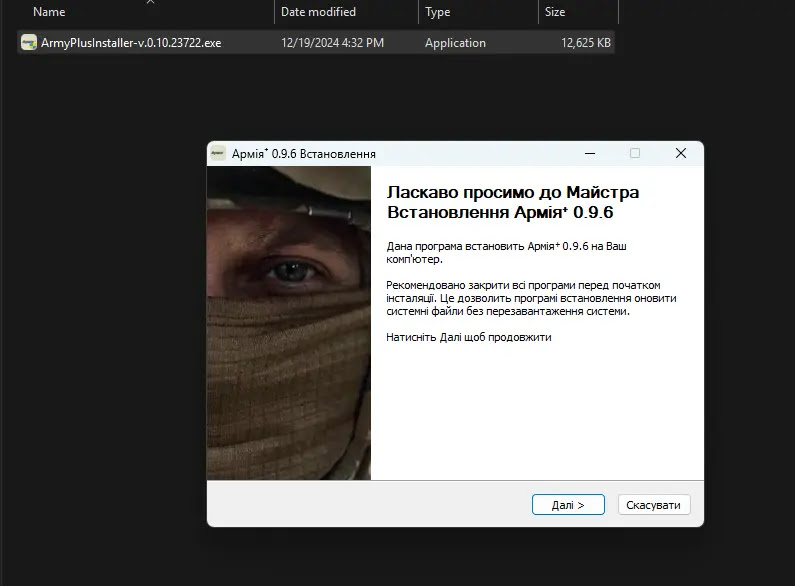
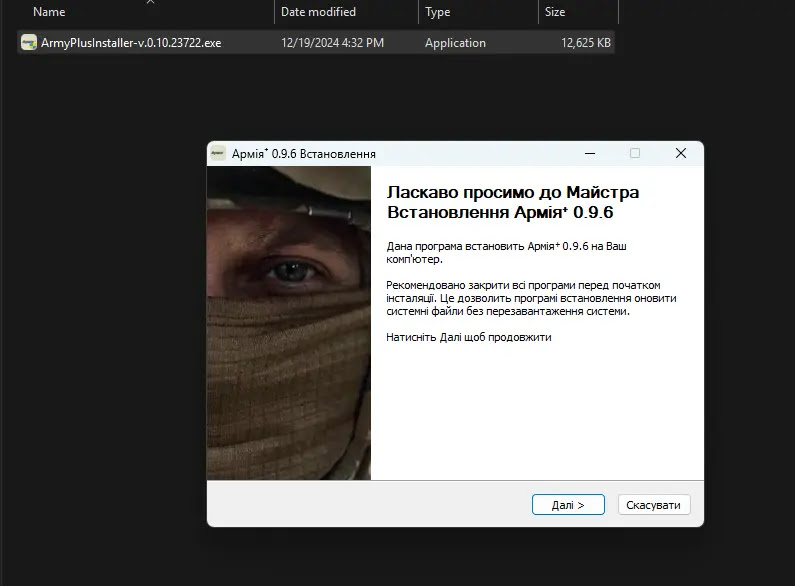
ArmyPlusInstaller initiates the installation process by launching a decoy application, ArmyPlus.exe, while simultaneously running a PowerShell script named init.ps1 in the background.


Investigate Real-World Malicious Links, Malware & Phishing Attacks With ANY.RUN – Try for Free
To conceal its activity, ArmyPlusInstaller executes cmd with the /min parameter, minimizing the console window and enabling PowerShell to bypass its default security restrictions, which is crucial as PowerShell, unlike the Windows Command Prompt, has stringent security measures in place for script execution.
To override these safeguards, the script utilizes cmdlets like Get-ExecutionPolicy and Set-ExecutionPolicy to modify the execution policy and grant itself the necessary permissions to proceed.


The malware stealthily distributes its components across three distinct folders and the ArmyPlus directory houses decoy files alongside init.ps1, the core script.
Init.ps1 orchestrates the setup, where it extracts the Tor browser into the OneDriveData folder, configures it for covert operation, and launches it without a visible window.
Simultaneously, OpenSSH files are placed in the ssh directory, establishing a backdoor for command-and-control.
Tor’s hostname file within OneDriveData reveals the address of this hidden Tor instance, facilitating secure and anonymous communication over the SSH channel.
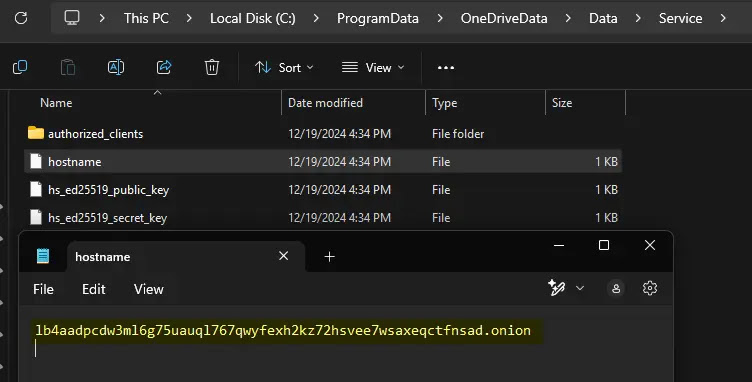
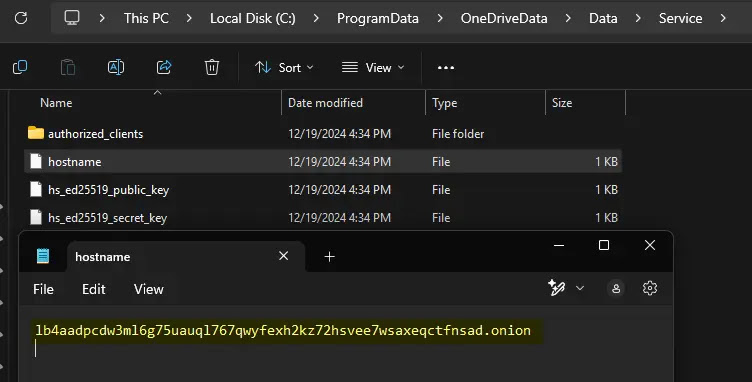
The malware establishes a persistent backdoor on a Windows 11 system by leveraging Tor for covert communication, which generates an RSA key pair, configures and starts the OpenSSH server, and then sends system information, the public key, and its Tor onion address to a remote server via the Tor network.
According to the researcher, the remote server uses the private key to securely send commands to the compromised system over the SSH connection, enabling attackers to execute arbitrary commands with high privileges.
It leverages social engineering by disguising malicious activity within a seemingly legitimate application installer, where the installer requests administrative privileges, a common requirement for Windows applications, to establish trust with the user.
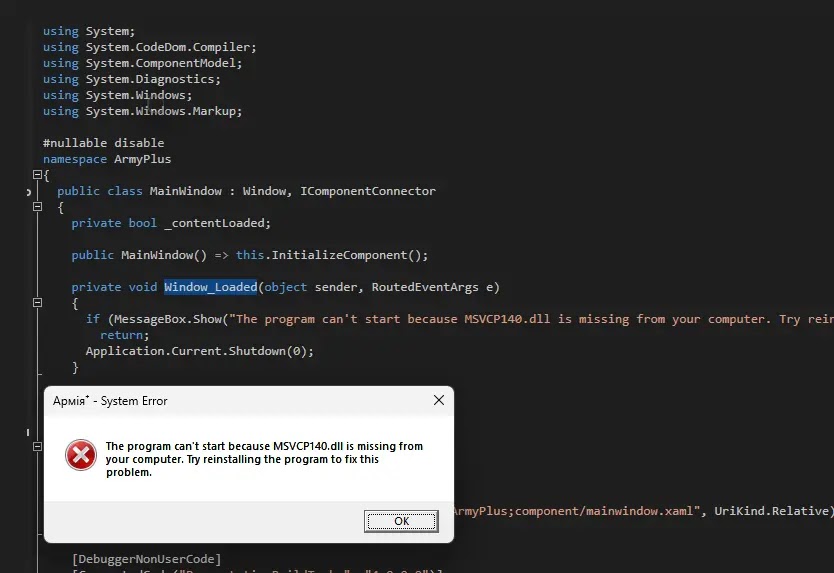
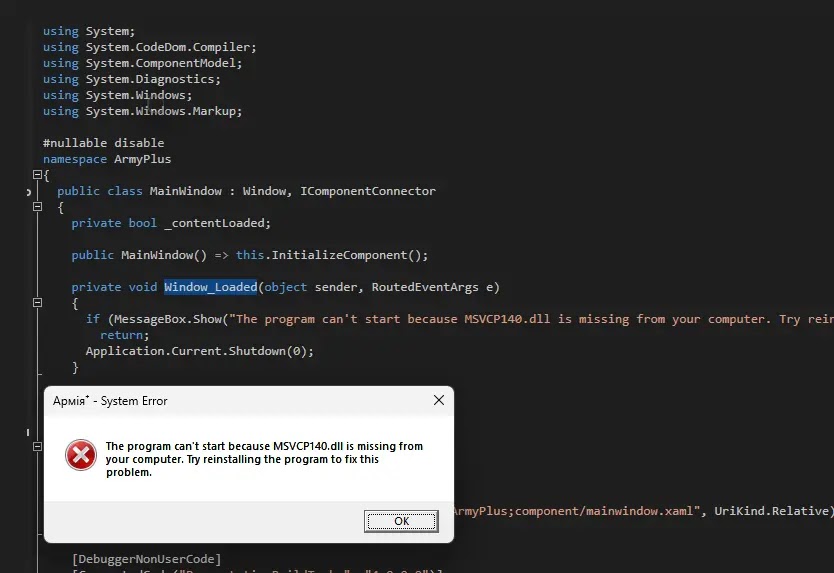
While the main executable displays a deceptive error message, the true payload resides in a PowerShell script (init.ps1) hidden within the installation package, which effectively conceals the malicious activity from the user while maintaining the appearance of a legitimate software installation.
The attackers exploited legitimate software and native Windows binaries to establish a backdoor on a compromised system and used PowerShell scripts to compress system information into a zip file and send it to the attacker’s TOR control server.
Source:
https://gbhackers.com/ssh-tor-malware-ukraine