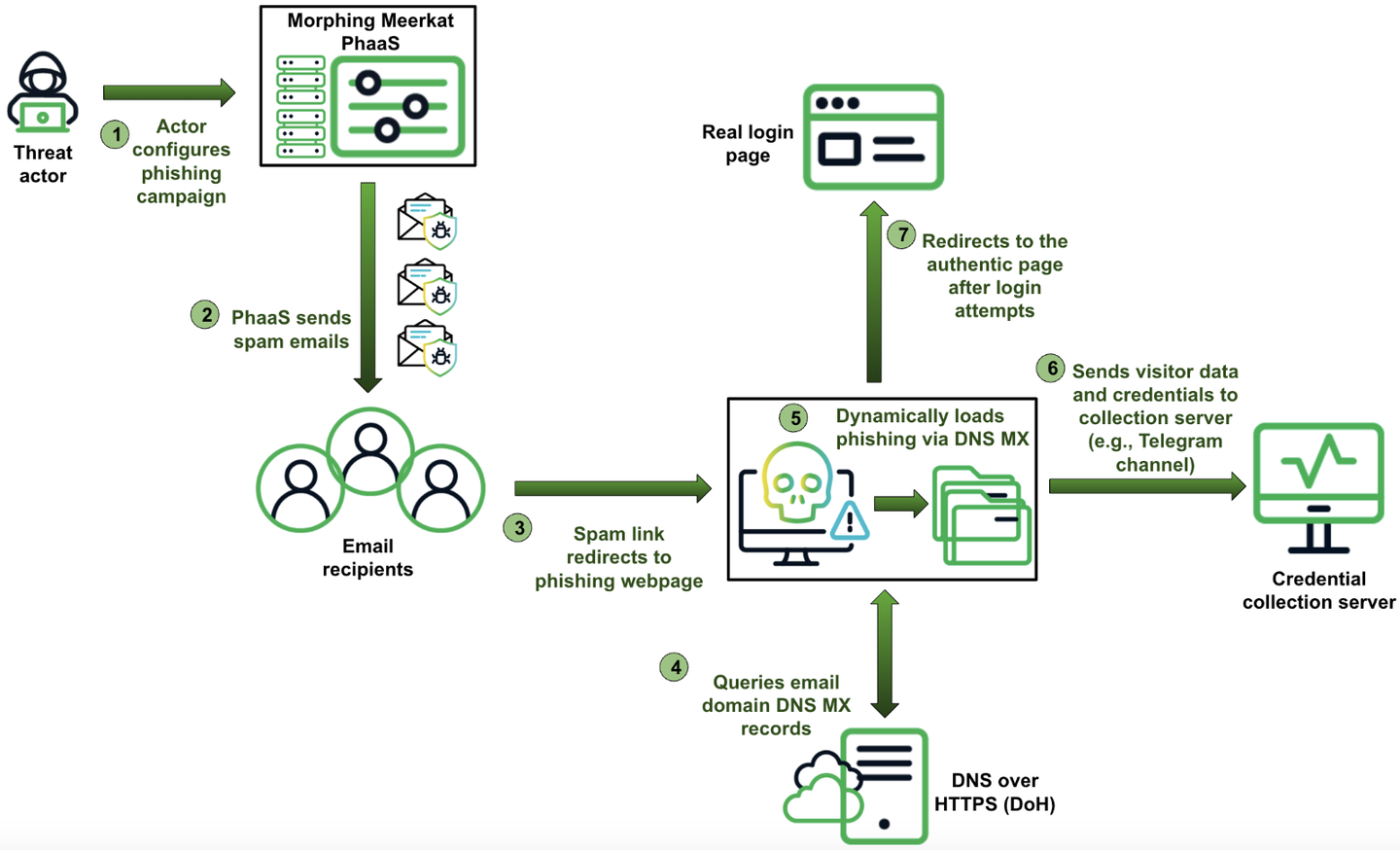
Summary: A recent report by Infoblox Threat Intelligence details a sophisticated phishing operation named Morphing Meerkat, which utilizes DNS techniques to create tailored phishing content for victims. The operation dynamically serves fake login pages mimicking over 100 brands, employing advanced methods to evade detection and enhance effectiveness. The report highlights several exfiltration methods and the challenge of identifying such threats due to their sophisticated nature.
Affected: Organizations relying on email communications and various online services
Keypoints :
- Uses DNS MX records to target victims based on their email service provider.
- Employs dynamic phishing campaigns with spoofed brands and localization in multiple languages.
- Incorporates advanced techniques like obfuscation, real-time monitoring, and infrastructure from service providers for stealth.
- Utilizes multiple exfiltration methods including EmailJS, PHP scripts, AJAX requests, and Telegram bots.
- Recommends organizations block DoH traffic, monitor MX record queries, and invest in security tools for better threat detection.
Source: https://securityonline.info/morphing-meerkats-phishing-tactics-abusing-dns-mx-records/