Awareness of the newest shifts and patterns is vital in the fast-changing world of cyber threats. This rings particularly true with ransomware, known for its quick changes and intricate tactics. This past August, our MDR team at SentinelOne stumbled upon something unusual in the wild: new instances of LOLKEK, or GlobeImposter as it’s also known, signaling fresh changes within this longstanding ransomware family.
This article takes you on an exploratory journey through the recent LOLKEK payloads, spotlighting key features, alterations in strategies, and shrewd observations in Indicators of Compromise (IoCs). We’ll also highlight a persistent OPSEC mistake that keeps giving away the ransomware operators’ game.
The knowledge and real-world examples provided here paint a complete picture of LOLKEK’s evolution and present-day situation. From its modest approach to ransom demands to its occasional connection with more elaborate financial assaults, comprehending LOLKEK provides insight into the wider landscape of ransomware.

LOLKEK | A Brief History
LOLKEK, also referred to as GlobeImposter, made its first appearance in 2016. In the fast-paced world of ransomware, where things change in the blink of an eye, this is like looking back to ancient history. This timeline even predates the ‘name-and-shame’ blogs that surfaced years later. To give you a perspective, Maze ransomware didn’t see the light of day until 2019. The GlobeImposter tag was a clever way to describe how this new ransomware imitated the methods of the then-known Globe ransomware.
LOLKEK can be considered a sort of ‘off-the-shelf’ ransomware. It’s something that’s frequently changed, tinkered with, and used, even by those with limited skills or resources. It’s often associated with what we might call a ‘small-time’ approach, especially regarding its targets and the ransom demands. In recent escapades, for example, the ransoms asked were often less than $2000 USD. Compare this to the eye-watering sums requested by heavyweights like Cl0p, LockBit, and Royal, and you see a sharp contrast.
LOLKEK’s primary targets tend to be small to medium-sized businesses (SMBs) and individual users. Despite this focus, there have been times when this ransomware played a part in more complex and calculated financial attacks. 2017 for example, the infamous TA505 (also known as G0092, GOLD TAHOE) group began employing GlobeImposter, moving away from Jaff, GandCrab, and Snatch. This allowed them to widen their net and boost the power of their operations, showcasing LOLKEK’s adaptability and role in the broader ransomware landscape.
Technical Details
We recently observed the following new LOLKEK samples in the wild:
08029396eb9aef9b413582d103b070c3f422e2b56e1326fe318bef60bdc382ed58ac26d62653a648d69d1bcaed1b43d209e037e6d79f62a65eb5d059e8d0fc3f
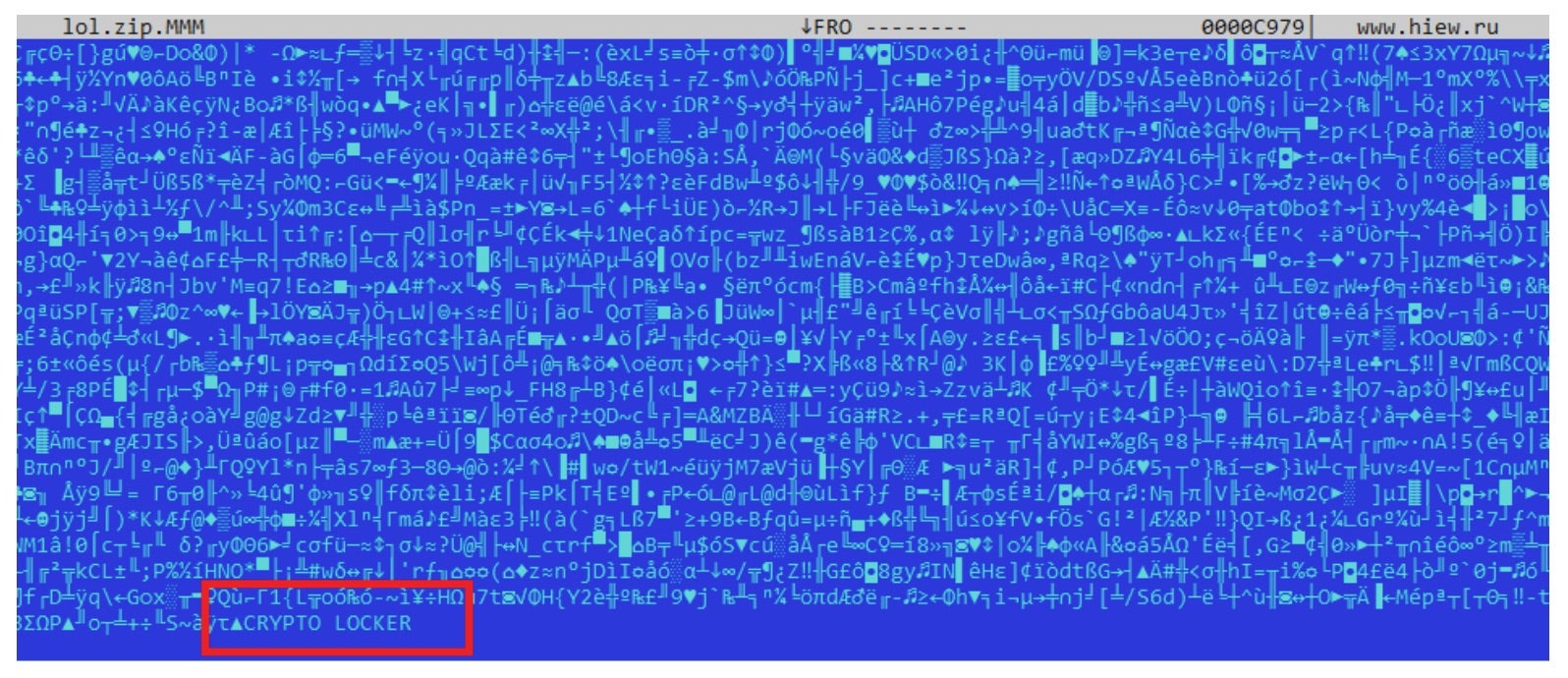
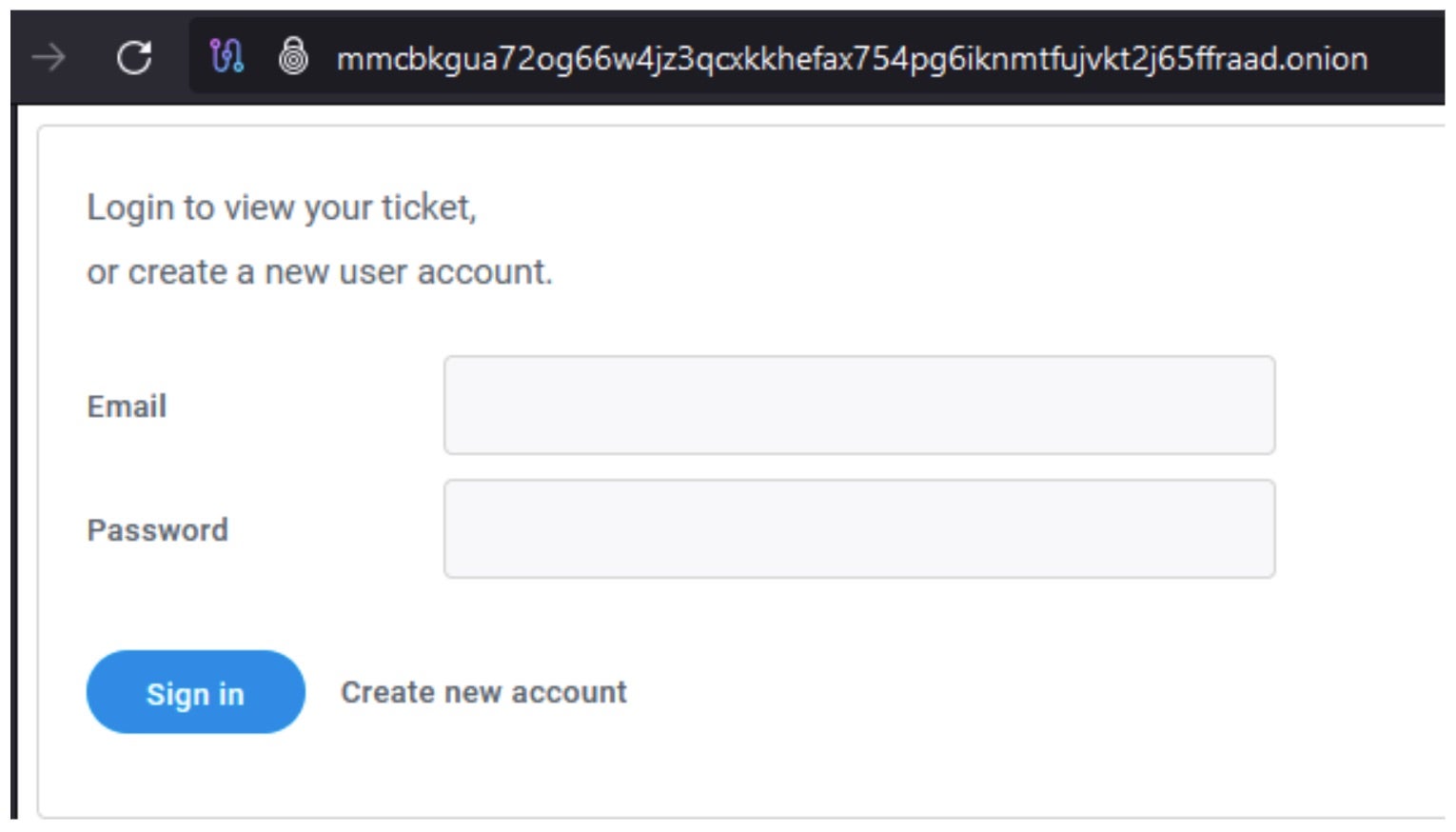
These samples identify themselves as “W3CRYPTO LOCKER” while also directing victims to a new TOR-based victim portal mmcbkgua72og66w4jz3qcxkkhefax754pg6iknmtfujvkt2j65ffraad[.]onion
Both newly observed samples were compiled in May of 2023. It is worth noting that only the 58AC26D62653A648D69D1BCAED1B43D209E037E6D79F62A65EB5D059E8D0FC3F sample is fully functional. The 08029396eb9aef9b413582d103b070c3f422e2b56e1326fe318bef60bdc382ed sample does not fully execute and appears to have some structural corruption.
08029396eb9aef9b413582d103b070c3f422e2b56e1326fe318bef60bdc382ed(possibly corrupt)Compile time: Thu May 11 06:15:13 2023
58AC26D62653A648D69D1BCAED1B43D209E037E6D79F62A65EB5D059E8D0FC3FCompile time: Thu May 11 06:15:13 2023
When launched, the new LOLKEK payloads will discover and subsequently encrypt any locally available drive including mounted network shares in sequence.
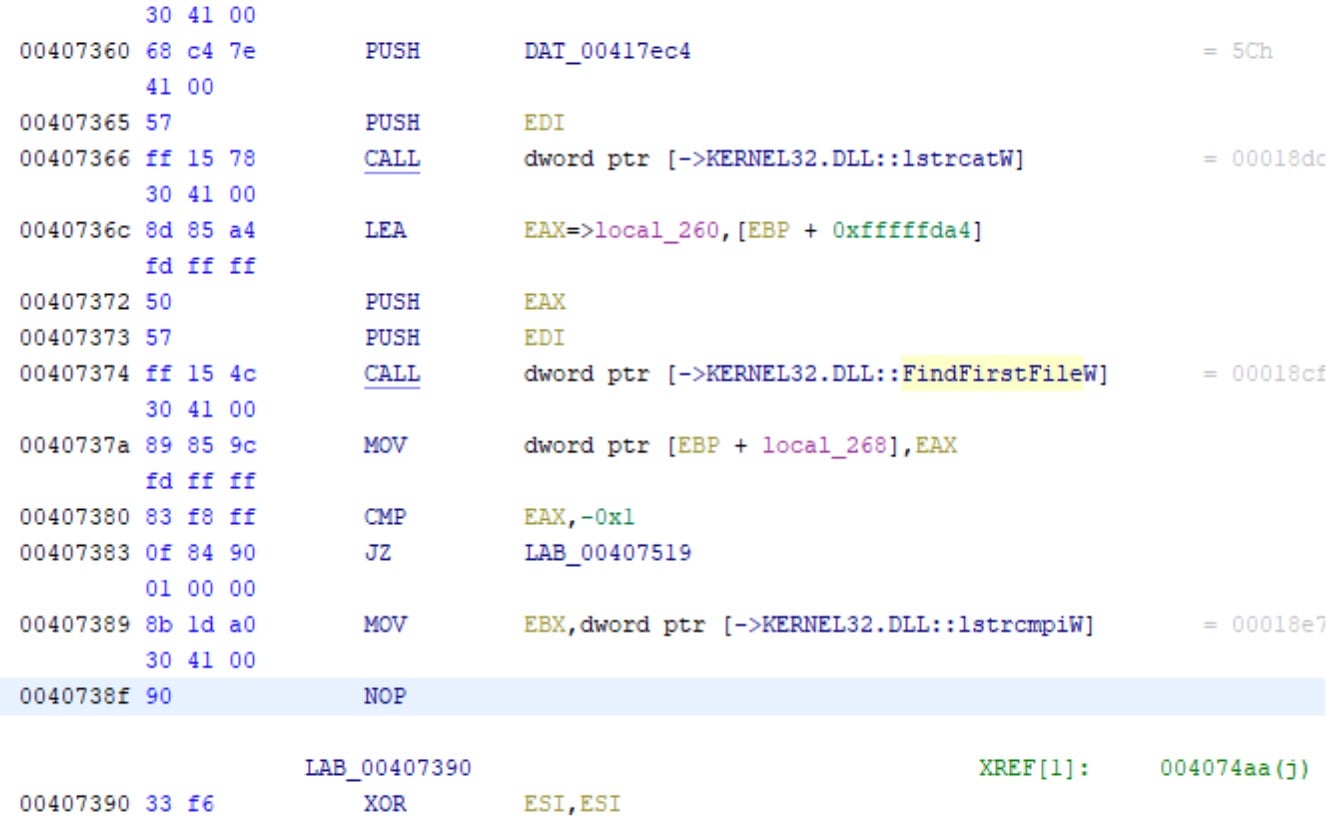
The payloads also contain exclusions carried over from previous variants of the ransomware. These include the Windows, System Volume Information, and ProgramData folders.
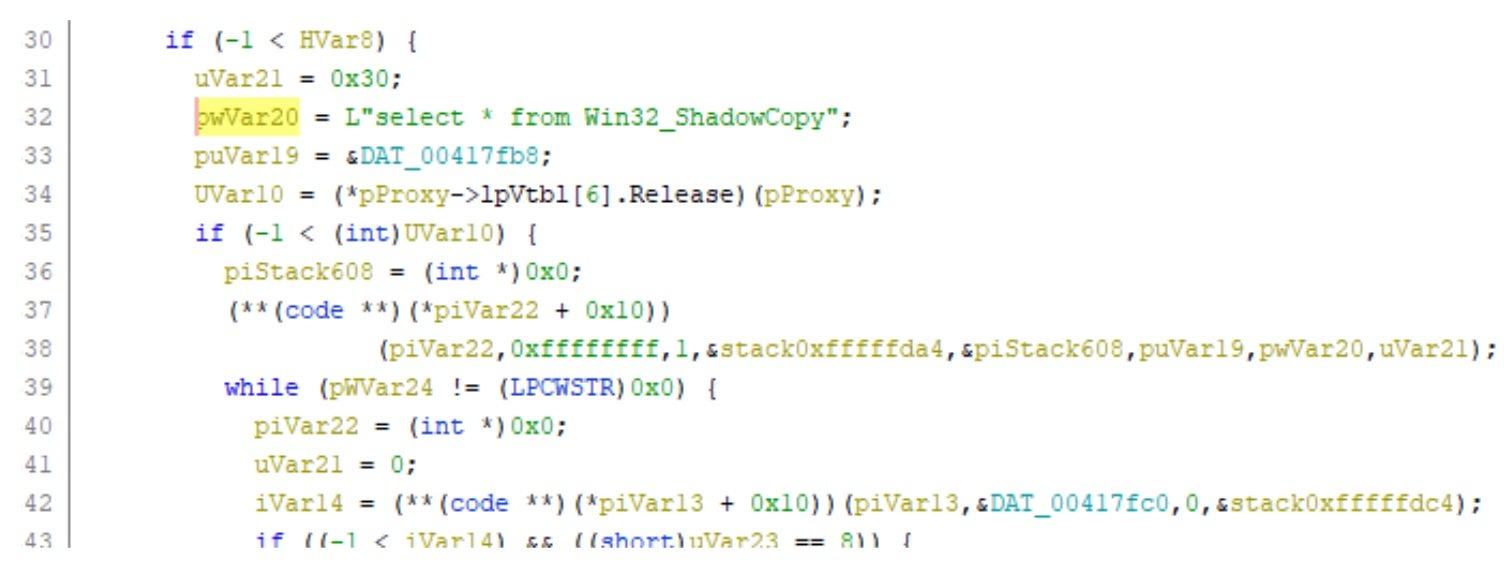
These payloads appear to contain the functionality to discover and remove Volume Shadow Copies (VSS). However, this behavior was not observed when dynamically analyzing the sample 58ac26d62653a648d69d1bcaed1b43d209e037e6d79f62a65eb5d059e8d0fc3f. WMIC-formatted calls to remove VSS are found in the samples’ code.
Encrypted files, once fully processed, will have the “.MMM” extension appended to them.
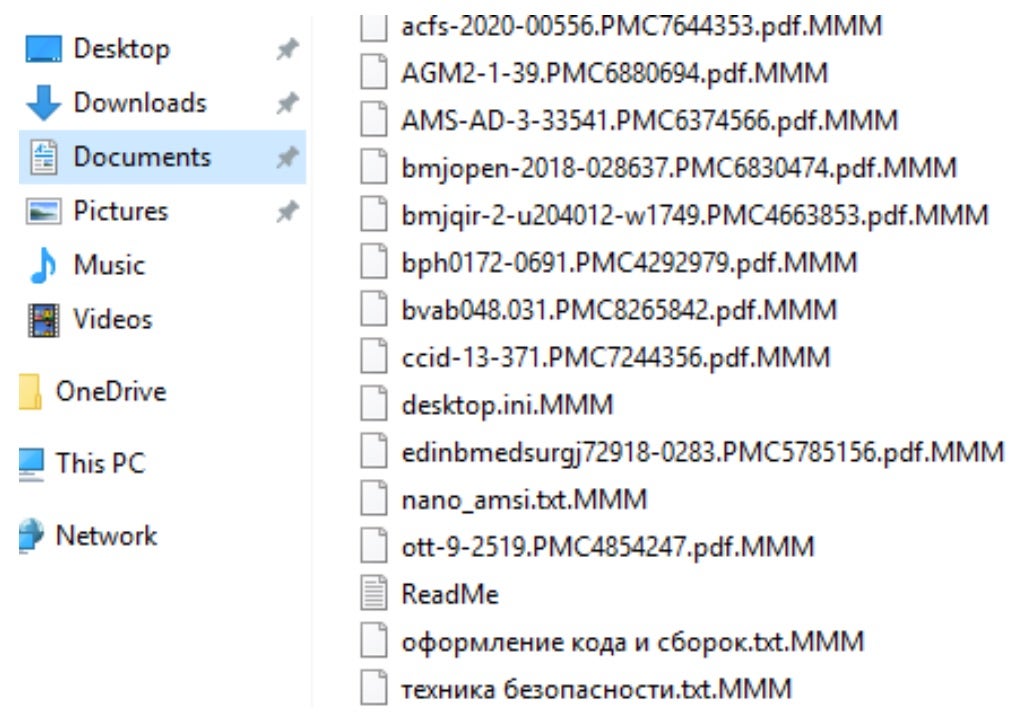
When looking deeper into the encrypted files themselves, we see another identifying marker linking them to previous generations of LOLKEK/GlobeImposter. Encrypted files contain the same “CRYPTO LOCKER” string seen in said prior generations.
LOLKEK Victim Portal and Notes
The LOLKEK ransom notes are written as ReadMe.txt to all locations containing encrypted files and data. The format and construction of the ransom notes is identical to what we have seen previously with this ransomware family.
The supplied .ONION URIs all contain a string at the end, unique to each execution of the ransomware.
Examples (defanged):http[:]//mmcbkgua72og66w4jz3qcxkkhefax754pg6iknmtfujvkt2j65ffraad[.]onion/[?]M01YOOOOOOO http[:]//mmcbkgua72og66w4jz3qcxkkhefax754pg6iknmtfujvkt2j65ffraad[.]onion/[?]m01TGRFBRRRR http[:]//mmcbkgua72og66w4jz3qcxkkhefax754pg6iknmtfujvkt2j65ffraad[.]onion/[?]M01VXOQRTKM
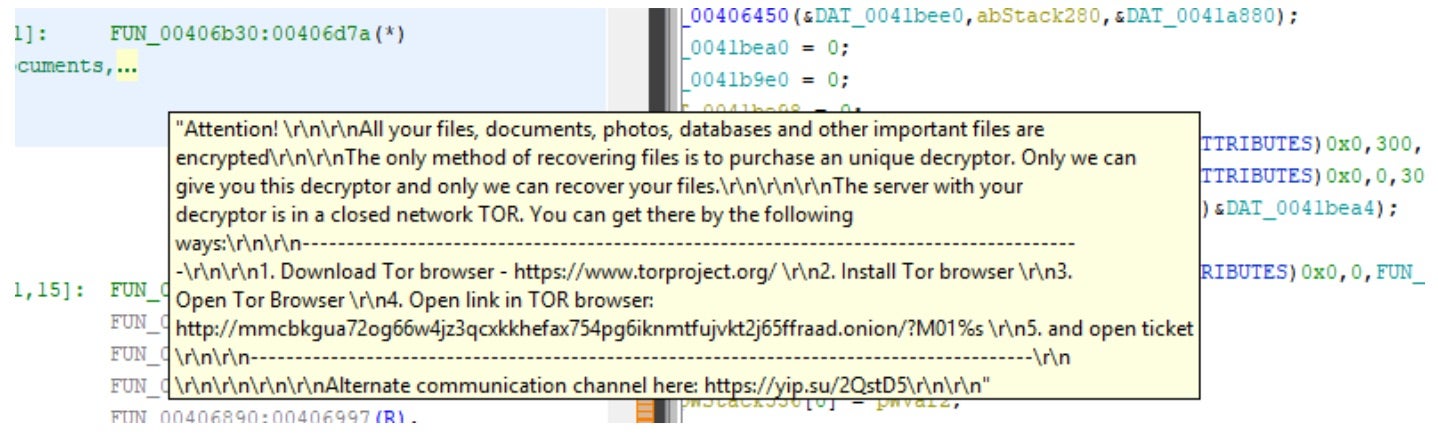
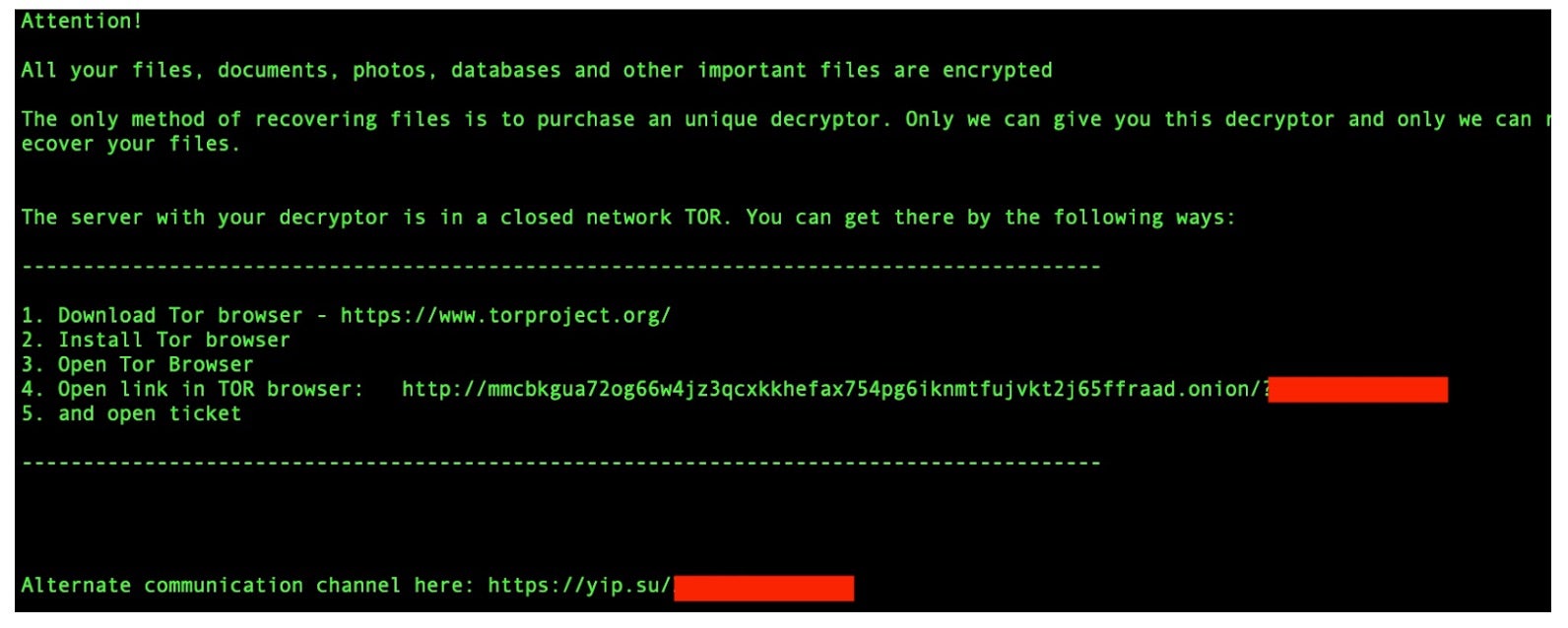
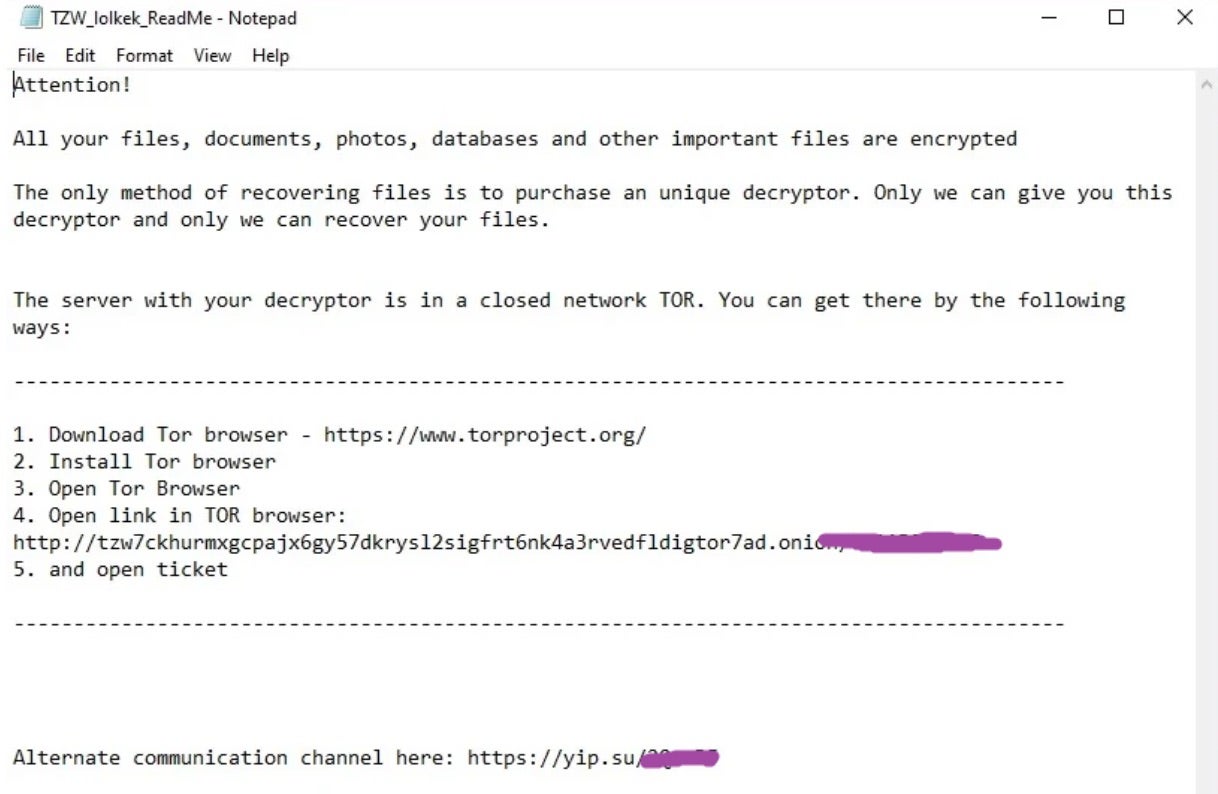
Current LOLKEK victims are instructed to navigate to the TOR-based victim portal where they must register an account to engage in a ‘private’ chat session with the attackers. Again, we note that the newly staged portal is functionally identical to previous victim portals staged by this operation. The look, feel, and process has not changed.
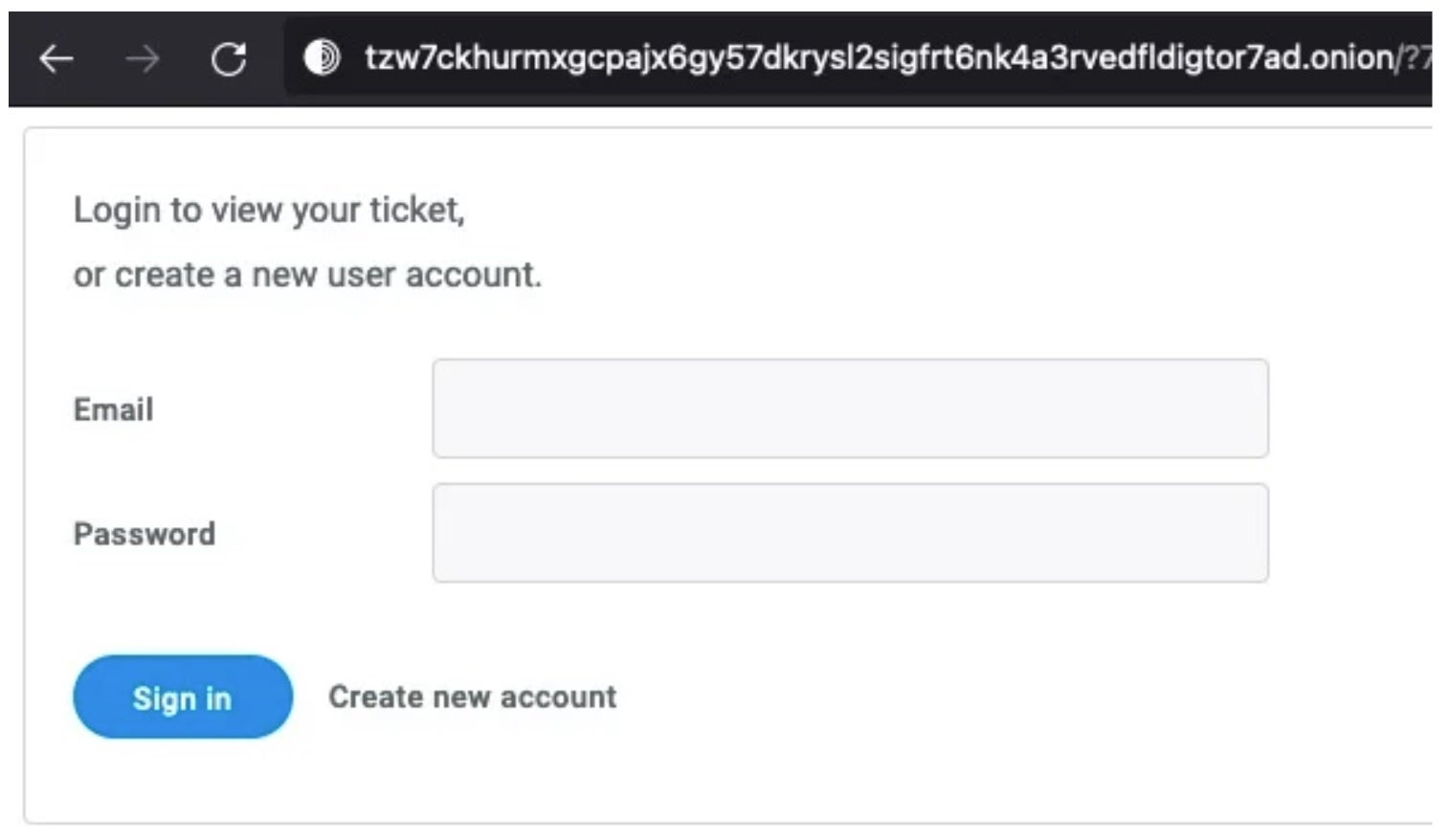
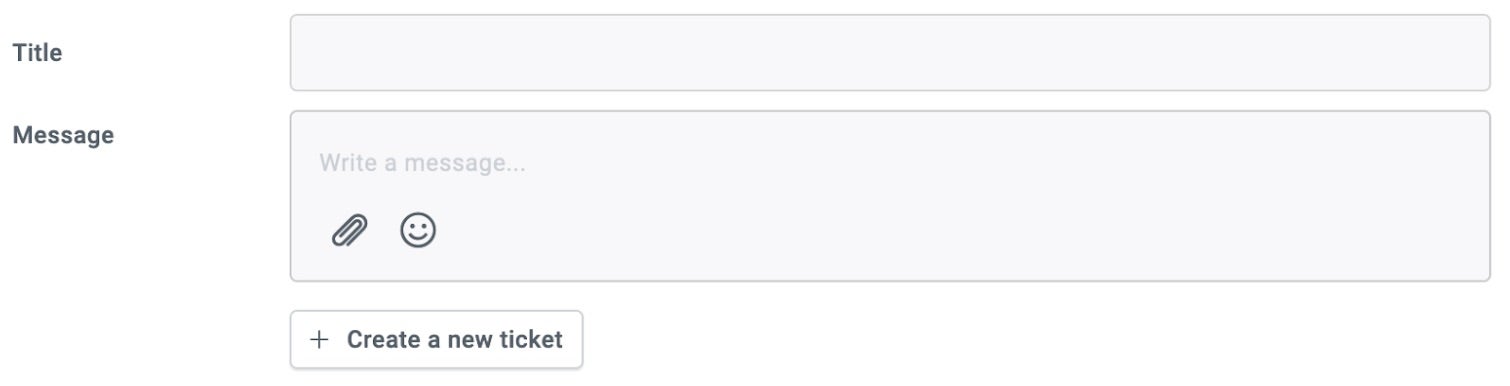
At this point, victims are able to chat with their attacker. Small files can be decrypted for free as ‘proof’ of functional decryption. Should the victim choose to comply, they will receive details on how and where to pay via a ticketing-like interface.
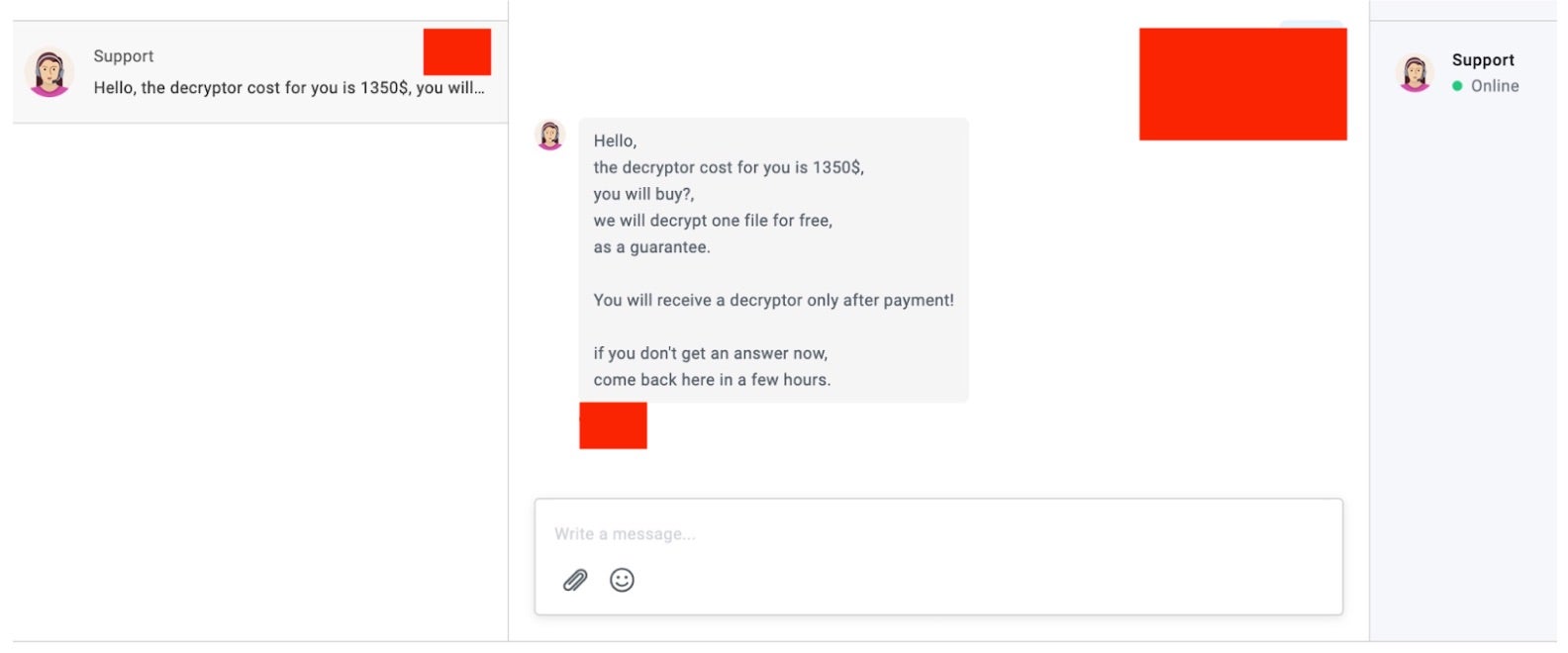
Upon ticket creation, the ransom details are automatically provided in the victim chat. As we see in this example, the ransom demanded is $1350 USD. Payments must be made via Bitcoin (BTC).
A LOLKEK OPSEC Misstep
The operators behind this campaign appear to have followed the same steps, process, and template as their pre-existing counterparts with regards to misconfiguration of Apache. The status page of the server is visible on the TOR-based victim page.
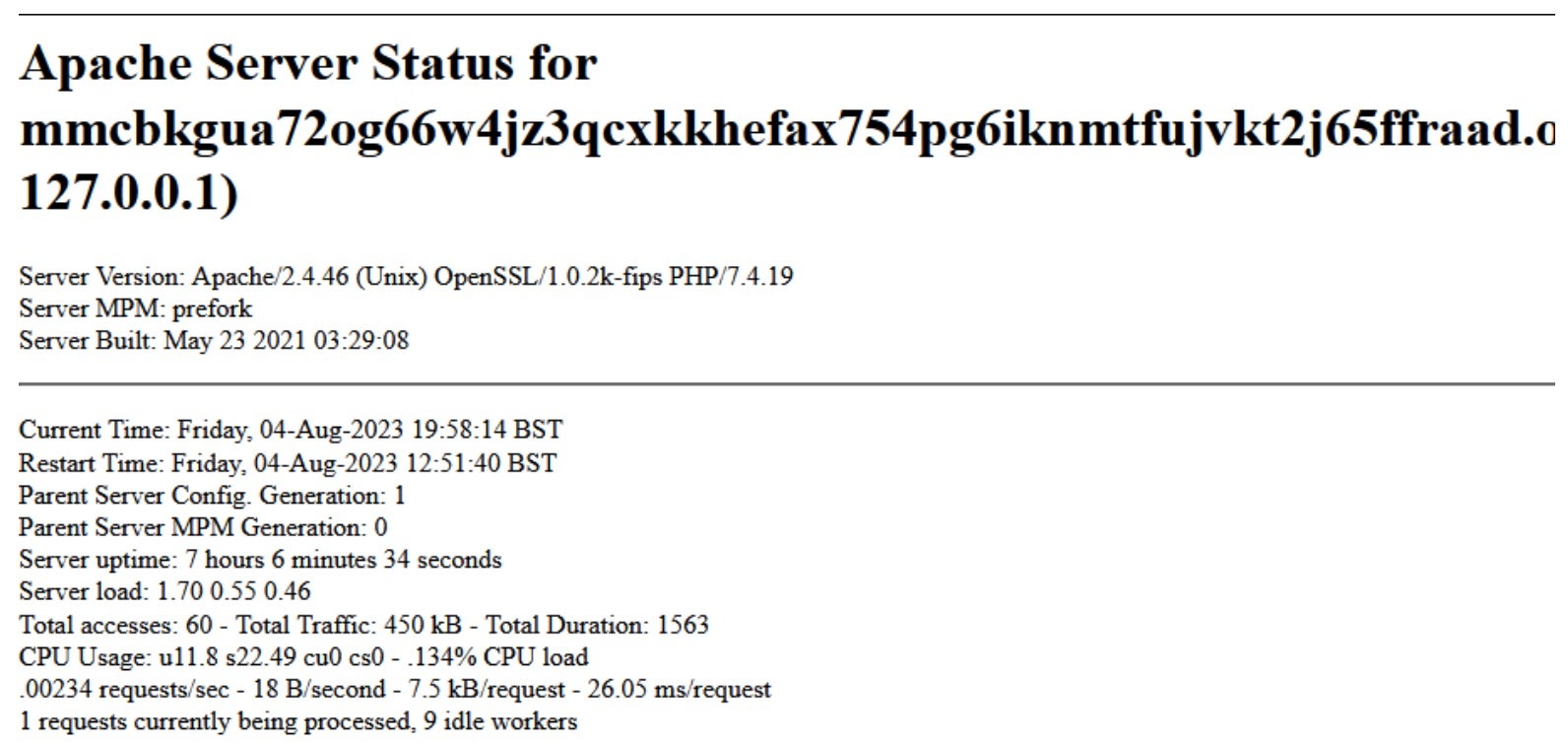
From here, we can see that the server went live on May 23, 2023; just a short time after the related samples’ compilation date on May 11, 2023. When analyzing these threats, it is always worthwhile to examine these surface-level misconfigurations. A great deal can be learned about a campaign and threat actor just through this step alone. In this case, this detail pointed to the same configuration misstep that helps us solidify the link of relation between previous TZW and GlobeImposter campaigns.
Conclusion
The journey of LOLKEK, or GlobeImposter, through the ever-shifting landscape of commodity ransomware is fascinating. While giants like LockBit and Cl0p dominate the headlines with their sophisticated schemes, it’s essential not to overlook the small-scale but persistent operations like LOLKEK. These lesser-known threats continue to evolve, find new ways to attack, and pose very real risks.
What we’re observing with LOLKEK is not a stagnant picture. Its operators are relentlessly exploring new strategies, pivoting to fresh infrastructure, and experimenting with innovative payloads. The examples we’ve highlighted may very well be the first stirrings of a new chapter for this adaptable threat. Although smaller in scale, it has shown the potential to align with more targeted, sophisticated campaigns. It’s not unthinkable that we could see LOLKEK targeting larger organizations and demanding higher ransoms in the future.
Protection against ever-adaptive threats like LOLKEK demands a robust defense. The SentinelOne Singularity XDR Platform is designed to recognize, counter, and eliminate all malicious behaviors and elements associated with LOLKEK/GlobeImposter-based attacks. If you wish to arm yourself with the technology that stays one step ahead of threats like these, contact us today or book a demo. We’re here to help ensure that the next chapter in the ransomware story doesn’t include you.
Indicators of Compromise
SHA1
768b8d81a6b0f779394e4af48755ca3ad77ed951
ed247b58c0680b7c92632209181733e92f1b0721
SHA256
08029396eb9aef9b413582d103b070c3f422e2b56e1326fe318bef60bdc382ed
58ac26d62653a648d69d1bcaed1b43d209e037e6d79f62a65eb5d059e8d0fc3f
Ransom Notes SHA256
0b179973dc267d9c300e9b7d3c27c67a18d7c79b2cc34927cbe5a465f83c6190
2c66e5f96470526219f40c6adfd6990cc28d520975da1fdb6bb5497d55a54117
Ransom Notes SHA1
456b0bda3f6d9ec9a874daac050b75fc28174510
88baff4e1751bd364cdb1a4bb5fda4a37ee127c4
IPs/URLs/Domains
filessupport@onionmail[.]org
https[:]//yip[.]su/2QstD5
Mmcbkgua72og66w4jz3qcxkkhefax754pg6iknmtfujvkt2j65ffraad[.]onion
MITRE ATT&CK
T1005 – Data from Local System
T1012 – Query Registry
T1027.002 – Obfuscated Files or Information: Software Packing
T1070.004 – Indicator Removal: File Deletion
T1082 – System Information Discovery
T1083 – File and Directory Discovery
T1112 – Modify Registry
T1202 – Indirect Command Execution
T1486 – Data Encrypted for Impact
T1490 – Inhibit System Recovery
T1547.001 – Boot or Logon Autostart Execution: Registry Run Keys / Startup Folder