The Splunk Threat Research Team has uncovered a widespread cyber campaign targeting ISP infrastructure providers in the United States and China, originating from Eastern Europe. The campaign exploits weak credentials for initial access, installs cryptomining malware, and employs various strategies to evade detection while performing data exfiltration and credential abuse. Affected: ISP infrastructure providers in the U.S. and China
Keypoints :
- Cyber campaign targeting ISP infrastructure on West Coast of the U.S. and China.
- Originates from Eastern Europe, using weak credentials to gain initial access.
- Employs cryptomining payloads and other malicious functions such as credential theft and data exfiltration.
- Makes use of common scripting languages like Python and PowerShell for operations.
- Targets over 4,000 specific IP addresses associated with ISPs.
- Utilizes Command and Control (C2) servers, specifically employing Telegram for communication.
- Employs mitigative strategies to avoid detection, including self-termination and disguising executables.
MITRE Techniques :
- Initial Access (T1078): Malicious actor uses brute force attacks against ISP infrastructure.
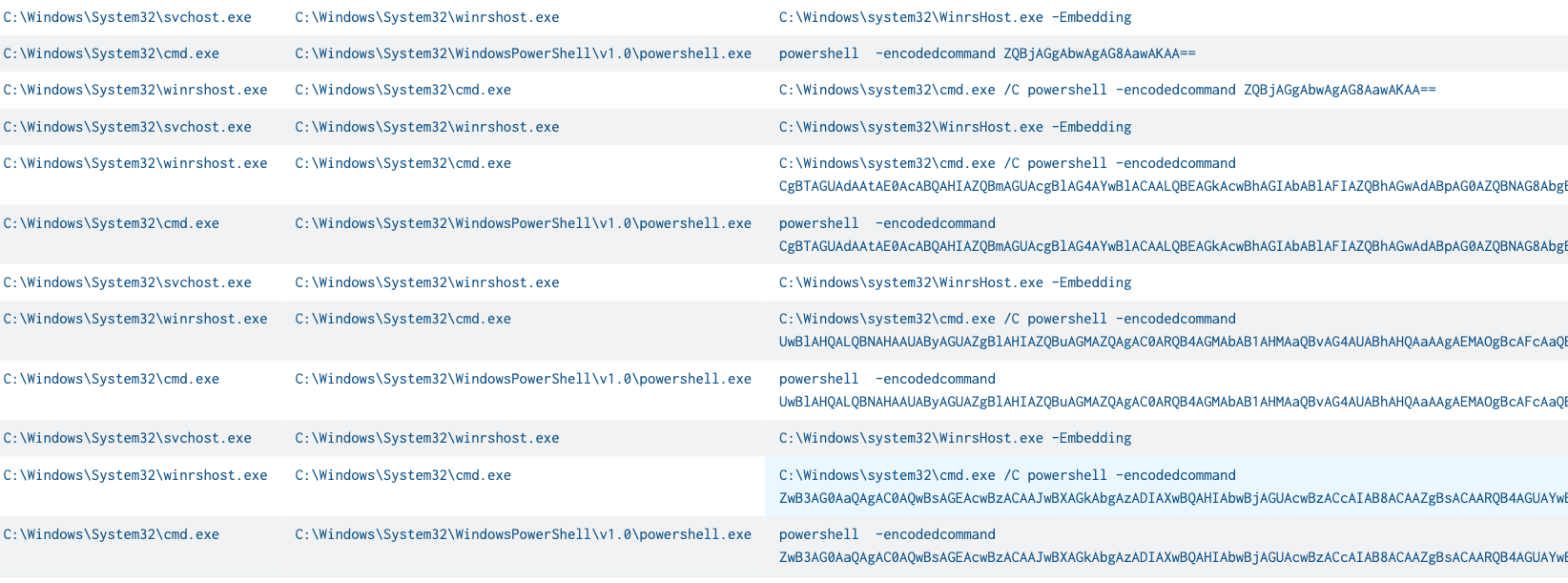
- Remote Services: Windows Remote Management (T1021.006): Leverages WINRM service to execute payloads on targeted hosts.
- Command and Scripting Interpreter (T1059.001, T1059.003): Executes PowerShell scripts to download and run malicious payloads.
- User Execution: Malicious File (T1204.002): User executes the mig.rdp.exe file, which drops additional malicious files.
- File and Directory Permissions Modification (T1222.001): Uses ICACLS to modify folder permissions to evade detection.
- Automated Collection (T1119): MicrosoftPrt.exe steals cryptocurrency wallet information from the clipboard.
- Automated Exfiltration (T1020): Sends stolen data, including clipboard content, to a Telegram C2 server.
- Ingress Tool Transfer (T1105): Downloads additional malware components from C2 server.
- Account Access Removal (T1531): Attempts to log off active users to disrupt detection of malicious activities.
Indicator of Compromise :
- [SHA256] ru.bat 76b1237d26b94eb75ed600ba51d4b2414a8da48a30d06973921bcd0ee9fac761
- [SHA256] st.bat 76b1237d26b94eb75ed600ba51d4b2414a8da48a30d06973921bcd0ee9fac761
- [SHA256] migrate.exe 76b1237d26b94eb75ed600ba51d4b2414a8da48a30d06973921bcd0ee9fac761
- [SHA256] ApplicationsFrameHost.exe 4d084a7e0c656d038d3176e97a4f807d094ce78f6b1f92a6ada7b93cf6a7cf03
- [SHA256] MicrosoftPrt.exe 16d2f6194d1b1989fbef4572055dbf62a0d6a2570b316ac15722192f1c559a50
Full Story: https://www.splunk.com/en_us/blog/security/infostealer-campaign-against-isps.html