Summary: Google Chrome has introduced app-bound encryption to enhance cookie protection on Windows systems, improving defenses against information-stealing malware. This new feature ties encrypted data to app identity, making it more difficult for malicious tools to access sensitive information.
Threat Actor: Infostealer Malware | infostealer malware
Victim: Google Chrome Users | Google Chrome users
Key Point :
- Chrome’s app-bound encryption ties sensitive data to app identity, enhancing security against unauthorized access.
- The new encryption method requires attackers to gain system privileges, making detection by antivirus software easier.
- This feature will be expanded to protect passwords, payment data, and other authentication tokens.
- Recent initiatives include improved download protection and alerts for potentially malicious files.

Google Chrome has added app-bound encryption for better cookie protection on Windows systems and improved defenses against information-stealing malware attacks.
As Chrome software engineer Will Harris explained in a blog post published today, Chrome currently uses the most robust techniques provided by each operating system to safeguard sensitive data such as cookies and passwords: Keychain services on macOS, kwallet or gnome-libsecret on Linux, and the Data Protection API (DPAPI) on Windows.
However, while DPAPI can protect data at rest from cold boot attacks or from other users on Windows systems, it does not protect against malicious tools or scripts designed to execute code as the logged-in user, which is something that infostealer malware exploits.
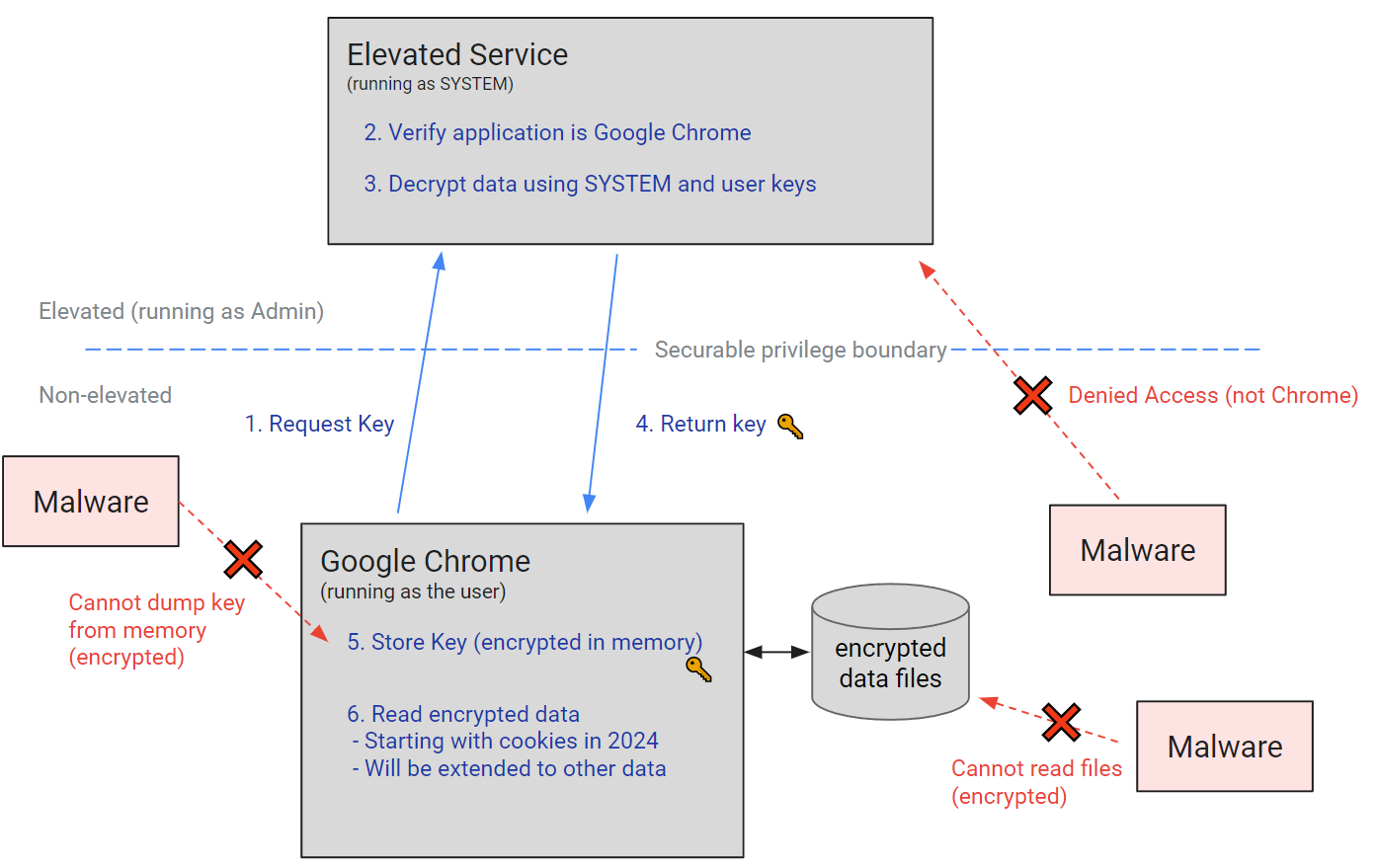
“In Chrome 127 we are introducing a new protection on Windows that improves on the DPAPI by providing Application-Bound (App-Bound) Encryption primitives,” said Harris.
“Rather than allowing any app running as the logged in user to access this data, Chrome can now encrypt data tied to app identity, similar to how the Keychain operates on macOS.”
Chrome’s App-Bound Encryption uses a new Windows service running under ‘SYSTEM’ privileges to confirm an app’s identity when it requests encryption. The service encodes the app’s identity into the encrypted data and ensures that only the intended app can decrypt it, causing other apps to fail when attempting to decrypt the data.
Since the service operates with system privileges, attackers would also need to gain system privileges or inject code into an app like Chrome, which is not a typical or legitimate action and makes it easier for antivirus software to detect when malware is used to steal data.
This improved protection capability will be expanded to passwords, payment data, and other persistent authentication tokens to better defend users’ sensitive data from infostealer malware attacks.
It also adds to other recent initiatives and features announced by Google to protect user data, such as Chrome’s download protection using Safe Browsing, Device Bound Session Credentials, and account-based threat detection to flag the use of stolen cookies.
“App-Bound Encryption increases the cost of data theft to attackers and also makes their actions far noisier on the system. It helps defenders draw a clear line in the sand for what is acceptable behavior for other apps on the system,” Harris added.
“As the malware landscape continually evolves we are keen to continue engaging with others in the security community on improving detections and strengthening operating system protections, such as stronger app isolation primitives, for any bypasses.”
Last week, Google also rolled out new Chrome warnings when downloading password-protected archives and implemented improved alerts with more information about potentially malicious downloaded files.
Views: 0