
Key Takeaways
- Cyble Research and Intelligence Labs (CRIL) has uncovered a novel phishing campaign tailored to cryptocurrency users.
- This campaign was deploying a well-known FatalRAT along with additional malware such as Clipper and Keylogger.
- The Threat Actors (TAs) orchestrating this campaign employ the DLL side-loading technique to load and execute FatalRAT, Clipper, and Keylogger modules.
- FatalRAT is a Remote Access Trojan that provides attackers with control over the victim’s computer and is equipped with extensive capabilities for stealing sensitive information.
- The inclusion of a clipper module alongside FatalRAT suggests a targeted strategy aimed at cryptocurrency users, and the addition of a keylogger module enhances data interception capabilities.
- The TAs behind this campaign are targeting Chinese-speaking individuals or organizations, as evidenced by using Chinese-language installers.
Overview
CRIL has recently uncovered a sophisticated phishing campaign that specifically targets cryptocurrency users, with a notable emphasis on users of the Exodus platform. In this intricate scheme, threat actors (TAs) have employed a deceptive website meticulously designed to mimic legitimate cryptocurrency applications.
The deceptive site, resembling the interface of the Exodus crypto wallet, aims to lure unsuspecting users into divulging their sensitive information. Exodus offers users the ability to manage their cryptocurrency holdings and conduct transactions. Available as both a desktop application and a mobile app.
The image below shows the deceptive phishing site, mimicking the authentic application interface.
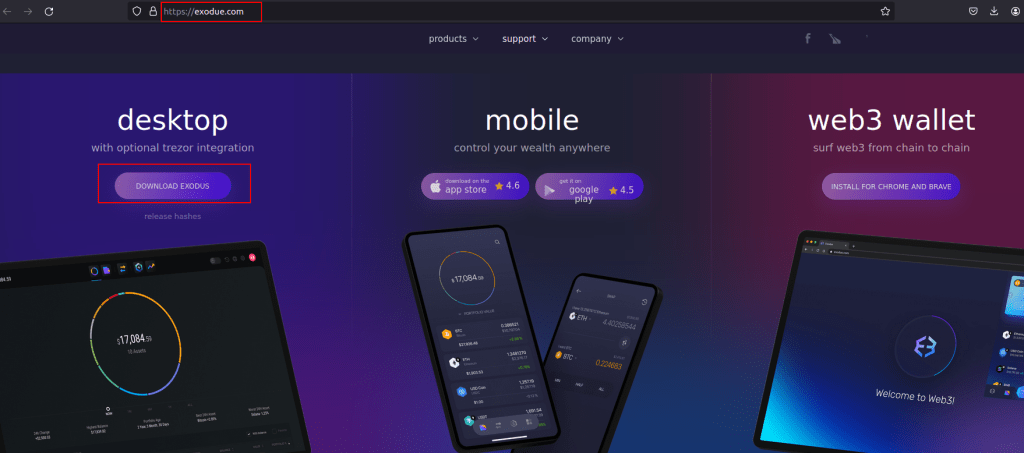
Figure 1 – Phishing site
Once unsuspecting users are lured into downloading the software disguised as genuine Exodus installers from the phishing site, they inadvertently install a Remote Access Trojan known as FatalRAT. Additionally, this installer also deploys other malicious components, such as Clipper and Keylogger, marking a new development compared to previous campaigns.
The TAs have executed a multi-staged attack incorporating multiple components packaged within a single installer file, culminating in the installation of the FatalRAT malware, a clipper, and a keylogger. Notably, the TAs have employed DLL side-loading techniques as part of their strategy to evade detection, a method that has been observed in previous campaigns as well. The image below shows the infection chain observed in the current campaign.

Figure 2 – Infection chain
Upon installation on a victim’s system, the Trojanized Exodus crypto-wallet installer application grants the attackers unauthorized access and control, enabling them to steal sensitive information from web browsers, capturing keystrokes, data manipulation—particularly concerning wallet addresses in the clipboard—and other malicious activities, all concealed from users in the background.
This operation is further enhanced by launching the Exodus installation in the foreground, tactically employing it as a diversion to mislead and distract users, as illustrated in the accompanying figure.

Figure 3 – Displaying the Exodus application in the victim’s machine
Technical Analysis
Upon execution of the downloaded malicious installer (.msi), it drops numerous files into two distinct directories within the C:ProgramData folder, named MoCo and Mo. The image below displays all the files along with their respective folder names.
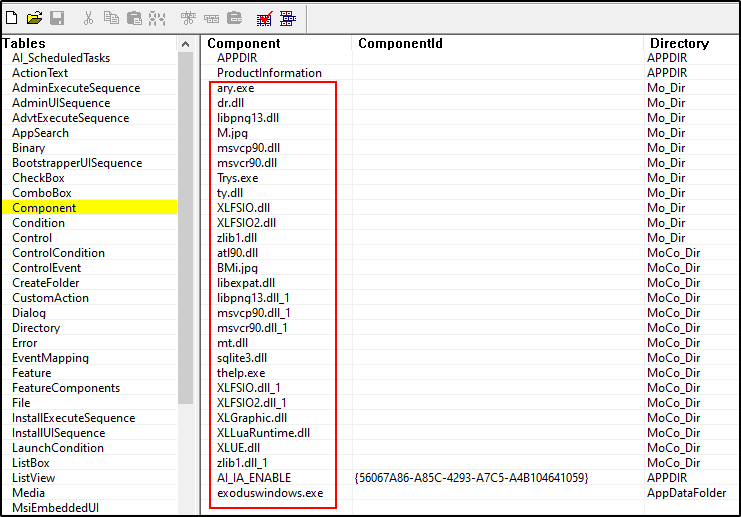
Figure 4 – Extracted files from the installer
All files listed are components of a multi-staged attack primarily utilizing the DLL side-loading method to execute the final payloads aimed at evading detection by security software. The attack chain unfolds as follows:
- A legitimate executable, thelp.exe (Browser Support Module), is launched by the installer. Following this, thelp.exe utilizes DLL sideloading to load a malicious DLL file named “XLFSIO.dll,” which subsequently loads the loader module named “mt.dll” during runtime, as depicted in the figure below.
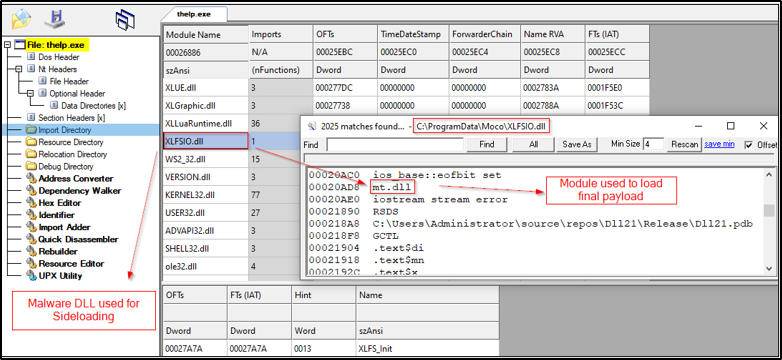
Figure 5 – Malicious files used for DLL Sideloading
- The file mt.dll is responsible for launching and executing two additional files named “Mi.JPG” and “BMi.jpg.” However, instead of images, these files contain a shellcode along with an embedded DLL, as shown below.
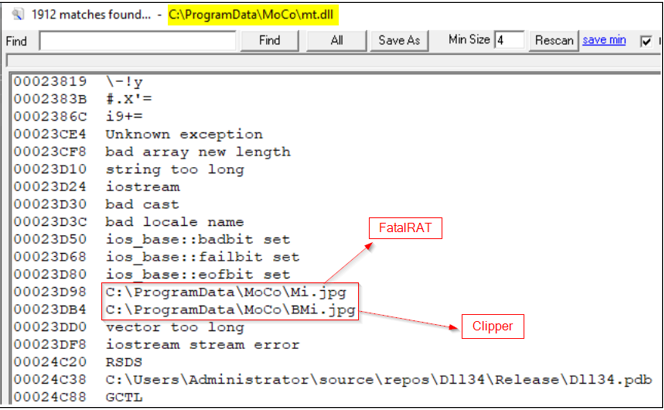
Figure 6 – Loader file containing the Shellcode filenames
- This shellcode’s objective is to load and execute the embedded DLL in memory by invoking an export function named SignalChromeElf.
- SignalChromeElf function performs decryption, loading, and execution of an encrypted payload present within the embedded DLL. This encrypted payload corresponds to the FatalRAT malware.
Similarly, other components such as Clipper and Keylogger are also observed being loaded into memory using similar methods.
Fatal RAT
FatalRAT is a Remote Access Trojan endowed with a broad spectrum of capabilities, allowing remote execution by an attacker. Initially detected in August 2021, the FatalRAT malware possesses capabilities including keystroke logging, screen resolution manipulation, downloading and executing files, as well as stealing data stored within web browsers.
Before commencing its infiltration procedures, the malware meticulously conducts a series of evaluations. These checks encompass assessments for virtual machine environments, processor types, and active processes, among other factors. Once successfully passing these checks, FatalRAT proceeds to decrypt configuration strings containing the Command and Control (C&C) server address as shown in the image below. Subsequently, any pilfered information is swiftly transmitted to the designated C&C server.

Figure 7 – FatalRAT Configuration strings
Based on our analysis, we’ve concluded that the version of FatalRAT employed in this campaign closely resembles the variant previously identified by AT&T and ESET. In this analysis, we will dive deeper into the Clipper and the keylogger modules.
Clipper
When thelp.exe is executed, it concurrently initiates the execution of the “BMi.jpg” file directly into memory through the utilization of the DLL “mt.dll.”
The file “BMi.jpg” contains a shellcode along with an embedded DLL (like FatalRAT), which is identified as Clipper. This shellcode is designed to load and execute the embedded DLL in memory by invoking DllEntryPoint(), as shown in the figure below.
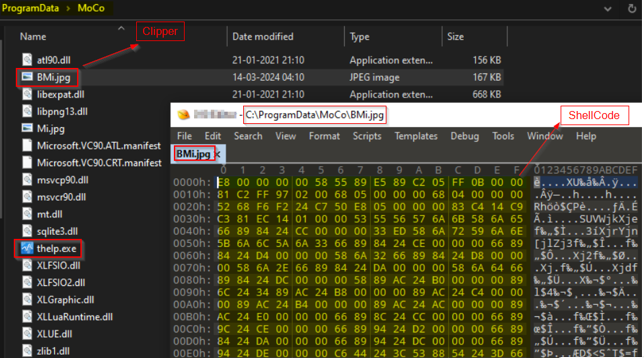
Figure 8 – Shellcode content with Clipper DLL
After the Clipper content is executed in memory, it utilizes API functions associated with the Windows Clipboard, as depicted in the figure below, to carry out its Clipper activities.
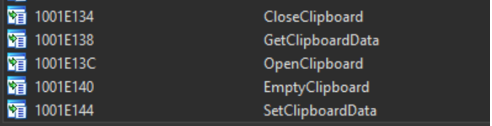
Figure 9 – Clipper functions
The table below shows the details of targeted cryptocurrencies and their regular expressions.
| Crypto currencies | Regular Expression | TAs Crypto wallet address |
| BTC (Bitcoin) | ^(1|3|bc1|tb1)[a-zA-Z0-9]{25,61}$ | 3CRsnPAe1NkhMDaxYNvm61s8DKh79WrwDL |
| ETH (Ethereum) | ^0x[a-fA-F0-9]{40}$ | 0x5C4b06FcfA8c3417E6F6248c32101a8Abd7936eE |
The aforementioned Clipper malware performs the following activities:
- The malware continuously monitors clipboard activity by calling OpenClipboard() to gain access to the clipboard.
- Once the clipboard is open, it uses GetClipBoardData() to retrieve the content stored in the clipboard.
- It then checks if the clipboard content matches any cryptocurrency address patterns defined by the regular expressions mentioned in the above table.
- If a cryptocurrency address is matched, the malware replaces it with a pre-defined malicious wallet address controlled by the Threat Actor.
- After modifying the clipboard content, the malware uses SetClipBoardData() to update the clipboard with the manipulated data, which now contains the TA’s wallet address instead of the original one.
- When the user attempts to paste the cryptocurrency address into a transaction field, they unknowingly paste the TA’s address instead, resulting in the redirection of funds to the attacker’s wallet.
The figure below shows the code snippet used to perform the malicious Clipper activity.
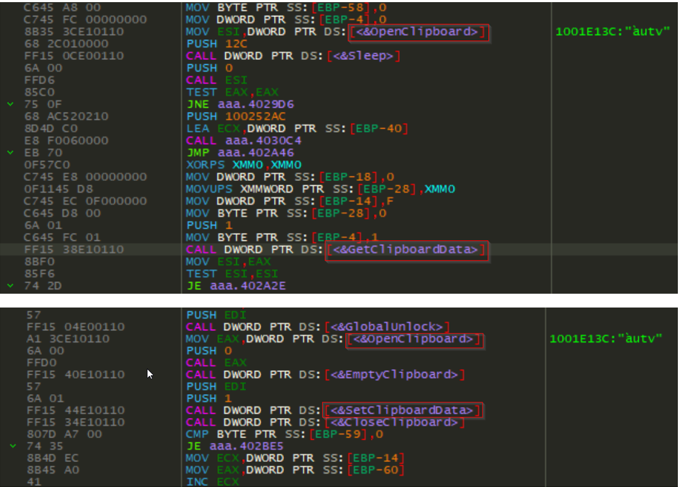
Figure 10 – Code snippet of Clipper’s functionalities
The figure below illustrates the presence of Clipper malware strings within the memory of the “thelp.exe” file.
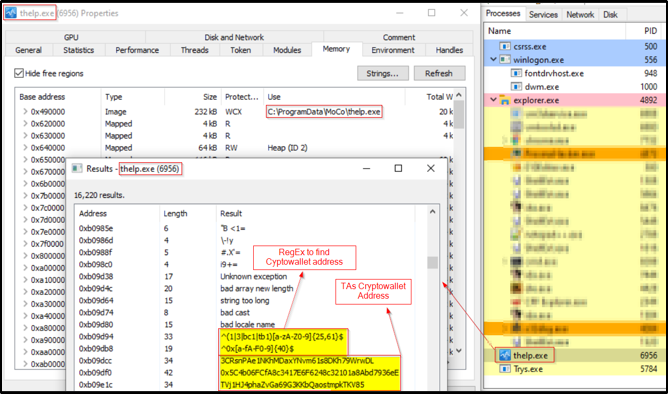
Figure 11 – Presence of Clipper strings in the memory of thelp.exe
Keylogger Module
In this campaign, we have observed that TAs have placed the keylogger module in an additional directory (C:ProgramDataMo) intended to log all keystrokes and system events. Although the FatalRAT malware already encompasses the keylogging function, this module operates independently without requiring direct intervention from the attacker.
Upon execution of the Trys.exe file, it employs DLL sideloading to dynamically load the “ty.dll” file. Subsequently, this action starts the execution of the “M.jpg” shellcode, which in turn executes the embedded Keylogger module within the memory, as shown below.
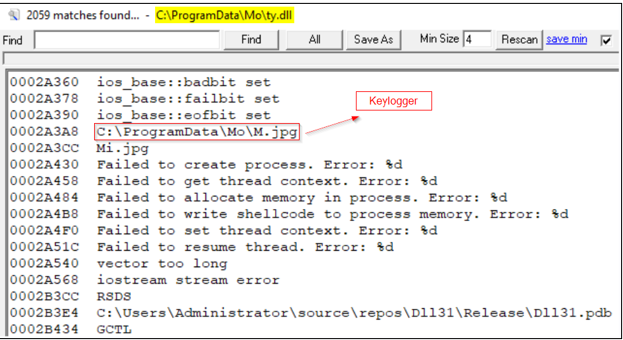
Figure 12 – Presence of M.JPG shellcode filename in ty.dll
The following figure illustrates the presence of keylogger module strings within the memory of the “Trys.exe” process.
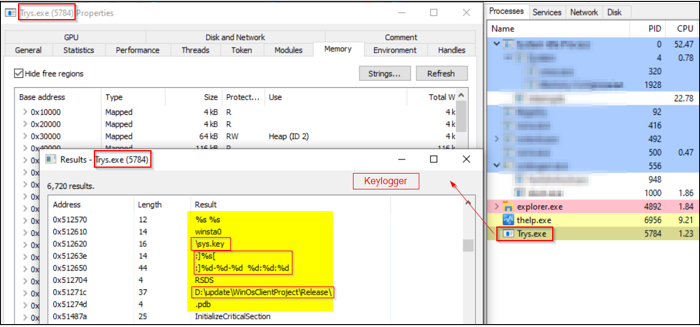
Figure 13 – Presence of Keylogger strings in the memory of Trys.exe
Prior to initiating the keylogger functions, the malware attempts to identify virtual environments by checking VMware-related processes, paths, and other indicators. If such a virtual environment is detected, the code exits without executing further actions, as shown in the figure below.
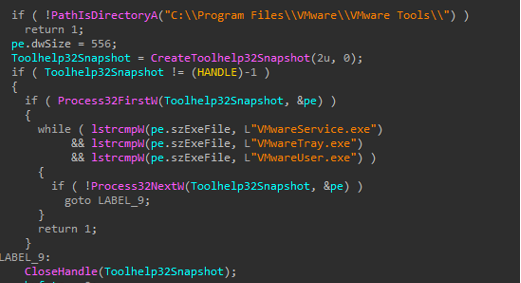
Figure 14 – Anti-Vm methods
After that, the malware proceeds to capture keystrokes and system events on the victim’s system. It then saves this information with the filename “sys.key” in the %programdata% folder. The following image depicts the data recorded by the keylogger malware.

Figure 15 – Saved Keylogger file
Within the keylogger, the remote server’s name is encoded in reverse, as shown in the figure below. During runtime, it retrieves the exact domain name from the reversed string and establishes a connection to it for data exfiltration.
- 1-27.qq-weixin[.]org

Figure 16 – Hardcoded server name in reverse order
Attribution
It’s plausible that the group responsible for the previous campaign may be behind this recent attack. This speculation is based on similarities such as the infection chain, file names, and an error observed in the scheduled tasks created. Additionally, the targeting of Chinese individuals, evident Chinese language versions of software used, and the C&C server pattern look similar.
Conclusion
The increasing popularity of cryptocurrency has attracted the interest of this group, leading them to transition from creating fake websites mimicking popular applications to targeting crypto users directly. Given the behavior of this campaign, we can safely conclude that the primary targets of this campaign are cryptocurrency users.
With the incorporation of a potent blend of the RAT (Remote Access Trojan) and a dedicated clipper module, the attackers can seamlessly extract sensitive information from their victims. Clipper malware poses a notable danger to individuals engaged in cryptocurrency activities, as it specifically focuses on intercepting their transactions and redirecting funds to the wallets of TAs. In light of these threats, crypto users must remain vigilant and proactive against such attacks.
Recommendations
- Before accessing or downloading from any site, it is essential to diligently verify the URLs.
- Crypto users should carefully check their wallet addresses before making any cryptocurrency transaction to ensure there is no change when copying and pasting the actual wallet addresses.
- The seeds for wallets should be stored safely and encrypted on any device.
- Before submitting the cryptocurrency wallet information, verify the authenticity source.
- Use strong passwords and enforce multi-factor authentication wherever possible.
- Keep a close eye on your cryptocurrency accounts for any unauthorized activity or suspicious transactions.
- Review and update advertising policies on major platforms like Google and social media networks to prevent the dissemination of malicious ads promoting cryptocurrency scams.
MITRE ATT&CK® Techniques
| Tactic | Technique ID | Technique Name |
| Initial Access (TA0027) | Phishing (T1660) | Malware distribution via phishing site |
| Execution (TA0002) | User Execution (T1204) | The user needs to manually execute the file downloaded from the phishing site. |
| Defense Evasion (TA0005) | Masquerading (T1036.008) | Downloads file disguised as a legitimate application. |
| Defense Evasion (TA0005) | Hijack Execution Flow: DLL Side-Loading (T1574.002) | Malware uses DLL sideloading for payload execution |
| Defense Evasion (TA0005) | Disable or Modify Tools (T1562.001) | Uses taskkill to terminate processes |
| Collection (TA0009) | Clipboard Data (T1115) | Monitors clipboard data and replaces crypto addresses with their address. |
| Exfiltration (TA0036) | Exfiltration Over C2 Channel (T1646) | Sending exfiltrated data over C&C server |
| Impact (TA0040) | Financial Theft (T1657) | Swaps crypto address to transfer funds to TA’s crypto address. |
Indicators of Compromise (IOCs)
| Indicators | Indicator Type | Description |
| hxxps://exodue[.]com | URL | Phishing Site |
| f80f8a725028bcc09639f7b1ff9439436d974f0bf92871048092eaec5d7458f0 | SHA256 | Downloaded malicious installer |
| d56471adbfd095d1be1d4b8288d14283efbf6414912064a97423751a69c1427f | SHA256 | BMi.jpg (Clipper) |
| 715138e6cb30bd18cc6afad6322e35f6f1a3d40ac135a1a9bc76cb884508c686 | SHA256 | M.jpg (Keylogger) |
| 8b0fde6e42ba17b0b475bb8dd54b8554cc6682d81b9e632f8890daa9ceefd48d | SHA256 | Mi.jpg (FatalRAT) |
| a5ca7b8af70d6e483007c6c9c60b0a2002e150b0f479744989fdd58ad2fc62d3 | SHA256 | malicious installer |
| 03e8610b95753eee43179b1ccc3fb72c8595a7d76e9b0290ea765f8e6372d4f9 | SHA256 | malicious installer |
| 0555ba582ffdb07a3e93a4d936d2d0d2bd506040f12e5b55e042e82d4bc169ad | SHA256 | malicious installer |
| fba1b353b063a068bd8a191ce699d335158028a6c94282a27f86b784cd4e94e5 | SHA256 | malicious installer |
| b3c47e48facfb1d6e4f93b1e9b91c1a931f5e491c5ab4aa0fc5c10ed077674b4 | SHA256 | malicious installer |
| 149271557eec7f5b17cd046d1f9936dca1654be1edd7835f005fbba145d65b8c | SHA256 | malicious installer |
| 1b6ab4d69332a041109c9a8b7bc1d12dd28566a0614363f7887d9044e4345a2e | SHA256 | malicious installer |
| e1368e893c44b29acfe7e9e190bbe448deda18d1847ed697b01c17a373207053 | SHA256 | malicious installer |
| efc27a42e520918f83b041f81975e8dbca9916d159dfc41380112c20b43bcd39 | SHA256 | malicious installer |
| c03a524b4e0561141012a6dc17f09bc8d0bf772cf2c94731971a50d67dccb2f4 | SHA256 | malicious installer |
| 47835bbb98d4660ffa225000797e22c3cfd48ae43af8ccf0999a760b8c3a92ba | SHA256 | malicious installer |
| 1-27[.]qq-weixin[.]org | Domain | C&C |
| 38[.]181[.]70[.]178 | IP | C&C |
| 1-31.qq-weixin[.]org | Domain | Sibling Domains |
| 1-8.qq-weixin[.]org | Domain | Sibling domains |
Yara Rule
rule FatalRAT
{
meta:
author = “Cyble Research and Intelligence Labs”
description = “Detects FatalRAT dll files”
date = “2024-04-10”
os = “Windows”
hash = “69cbdb401d6c03f3d64b3bf48d527cb4bf507952f34b170a3d020707fc4ff7be”
strings:
$a1 = “SVP7” ascii nocase
$a2 = “SVP7-Thread running” ascii nocase
$a3 = “DisableLockWorkstation” ascii nocase
condition:
uint16(0) == 0x5a4d and all of them
}The post FatalRAT’s New Prey: Cryptocurrency Users in the Crosshairs appeared first on Cyble.
Source: Original Post