This article discusses the tactic of attackers using fake WordPress plugins to inject malware, particularly casino spam, into websites. By disguising malicious plugins as innocuous, attackers evade detection and compromise site integrity. The narrative follows an investigation into a client’s compromised site, examining the methods of detection and removal of the fake plugin, emphasizing the importance of website security. Affected: WordPress websites, website owners, casino sector
Keypoints :
- Attackers have been injecting malware through fake WordPress plugins.
- Malicious plugins are designed to bypass integrity checks and detection methods.
- The article describes a specific case of casino spam being injected into a client’s website.
- Attackers disguise malicious plugins with innocent-sounding names and hide them within the plugin directory.
- The investigation involved identifying uncommon plugins to find the malicious one.
- Malware uses a combination of obfuscation and cURL to execute malicious actions.
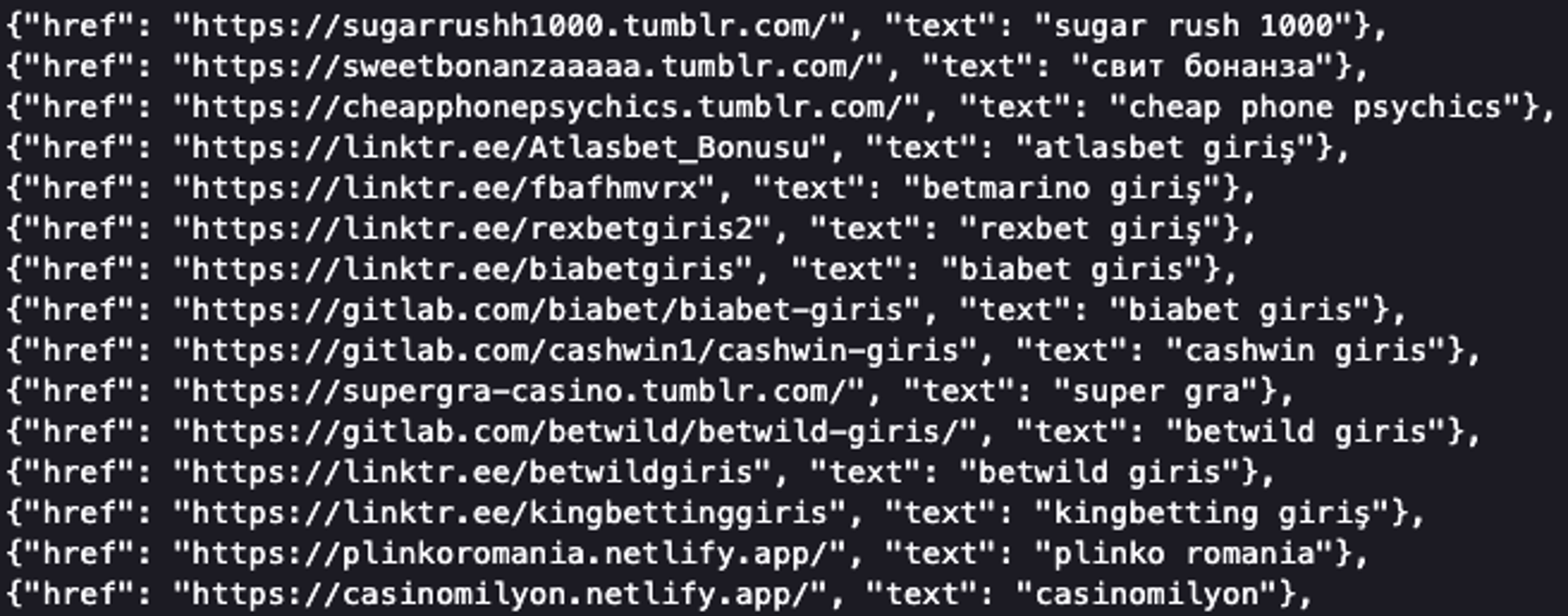
- The malicious plugin fetches and injects spammy links into the footer of the victim’s website.
- Potential goals of the attack include black hat SEO, driving traffic to malicious sites, and paid link building.
- Website owners are encouraged to maintain security and regularly monitor plugins.
- Steps to mitigate risks include updating software, using unique passwords, removing unused admin accounts, and regularly scanning for malware.
MITRE Techniques :
- Technique: Command and Control (T1071) – The malware uses cURL to fetch data from the malicious server for executing its payload.
- Technique: Data Obfuscation (T1027) – The code employs multiple layers of obfuscation, including base64 and XOR encryption, to hide its true purpose.
- Technique: Input Data Manipulation (T1203) – By injecting links into the website footer, the malware manipulates web content to mislead visitors.
- Technique: Supply Chain Compromise (T1195) – By introducing a fake plugin into the WordPress environment, the attacker compromises the trusted supply chain of the website’s functionalities.
Indicator of Compromise :
- [Domain] jsscript[.]top
- [URL] https://jsscript[.]top/links.json
- [IOC File Name] security-wordpress.php
Full Story: https://blog.sucuri.net/2025/02/fake-wordpress-plugin-impacts-seo-by-injecting-casino-spam.html