Recent findings indicate a resurgence of fake CAPTCHA malware delivery methods, where users unknowingly execute malicious code from compromised websites, resulting in infostealer payloads. This malware utilizes advanced techniques like social engineering and blockchain-based code hosting to achieve its goals. Affected: WordPress websites, Windows devices, users of infostealer malware.
Keypoints :
- Resurgence of fake CAPTCHA malware delivery detected.
- Maliсious code execution occurs via a compromised legitimate WordPress site.
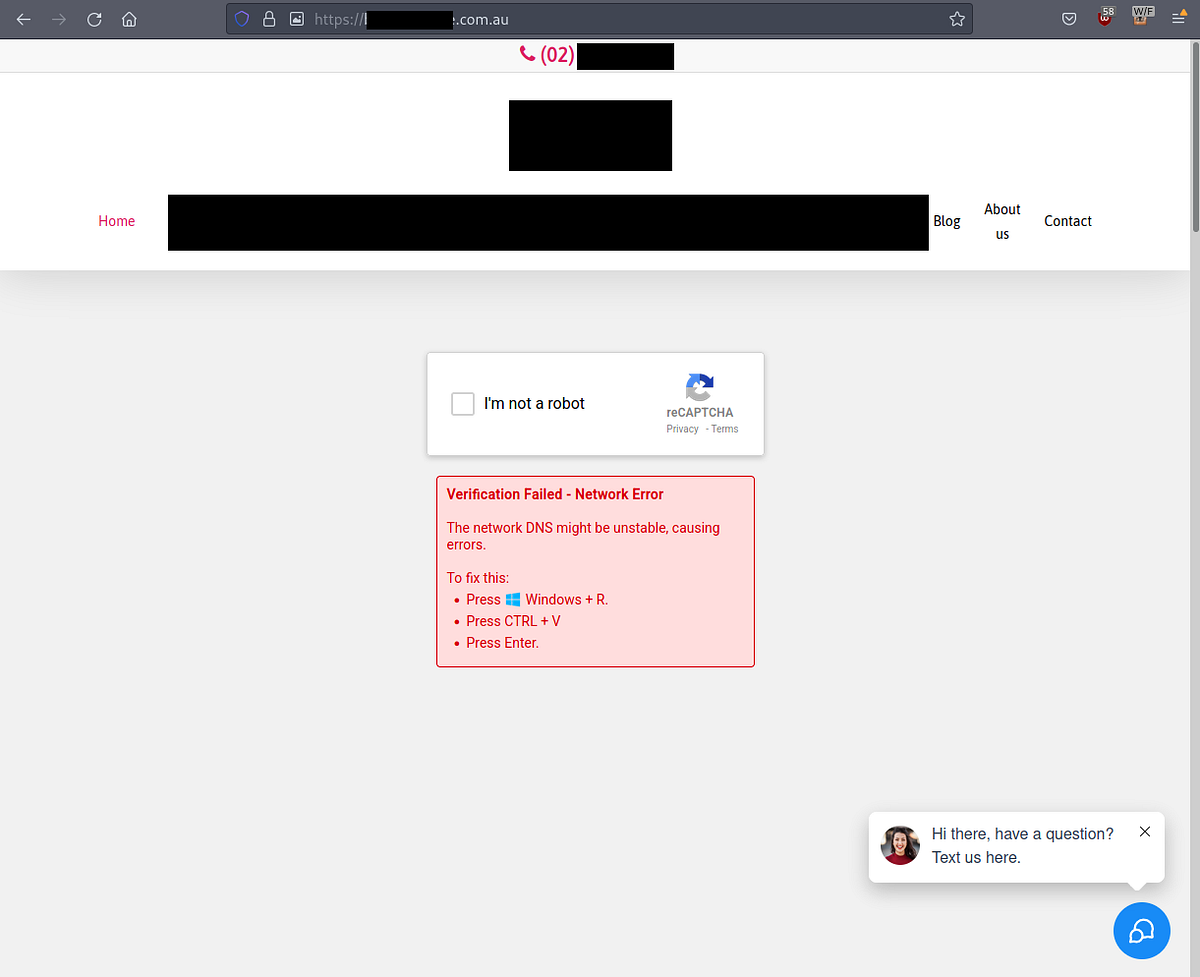
- Social engineering trickery is employed to deceive users into executing payloads.
- The malware operates in memory, avoiding detection through disk access.
- Threat actors leverage blockchain technology to host malicious code within smart contracts.
- Execution starts when a user interacts with a fake CAPTCHA on a compromised site.
- Multiple stages of execution are involved, ultimately delivering an infostealer payload.
- Powershell scripts are used for secondary payload execution and further obfuscation.
- Final payload analysis reveals common indicators of infostealer malware behavior.
- Preventative measures include monitoring device process events and blocking the Windows Run box via group policy.
MITRE Techniques :
- Execution (T1203): The fake CAPTCHA trick employs user interaction to execute the malicious command.
- Command and Control (T1071): The malware communicates with remote servers for payloads and instructions.
- Exploitation of Public-Facing Application (T1190): A compromised WordPress website serves as the attack vector.
- Obfuscated Files or Information (T1005): The payloads utilize obfuscation techniques to hide malicious behavior.
- Credential Dumping (T1003): The infostealer targets browser credentials and wallet information.
Indicator of Compromise :
- [URL] hxxp://83[.]217[.]208[.]130/xfiles/Ohio.mp4
- [SHA256] d1e6c627f96ebe45ef06713fbc2b8eabc48115b99a82205c04914aff5d7cb3de
- [URL] hxxps://scionoutmatchsmoked[.]shop/b313d4a4588bd2e7bc9ece877caba58a.png
- [SHA256] 90dbf6ae63b89de6dd8d1d662a575c924d4d4ed6016871ff212bd1fd50106f13
- [SHA256] b45cce152576ee61505e7e39f815d8e1794484d07c06544b62ebcc8eeeccba35
Full Story: https://medium.com/@rcgatenby/fake-captcha-leads-to-vidar-stealer-e40fb8e42019?source=rss——malware-5