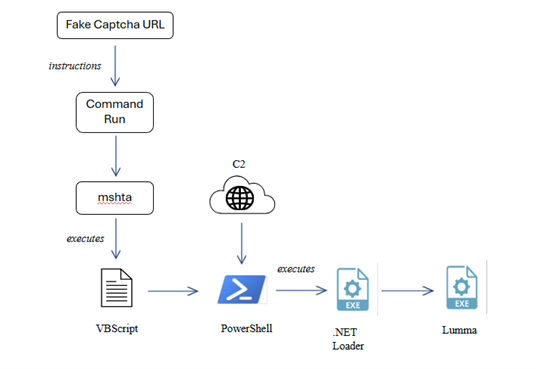
A new malware campaign has been discovered that utilizes fake CAPTCHA pages to deliver Lumma Stealer. The attackers employ phishing techniques with misleading Cloudflare verification prompts, tricking victims into executing malicious commands. The attack heavily relies on social engineering tactics and various Windows utilities. Affected: Lumma Stealer, phishing sectors, cybersecurity.
Keypoints :
- Recent identification of malware campaign using fake CAPTCHA pages.
- Lumma Stealer operates as malware-as-a-service (MaaS).
- Attackers impersonate Cloudflare verification pages to deceive victims.
- Utilization of mshta.exe and PowerShell to deliver the payload.
- The infection process begins with a fake CAPTCHA page prompting execution of malicious commands.
- Clipboard hijacking is employed to facilitate command execution by the user.
- The .NET loader utilizes anti-debugging techniques to evade detection.
- Stealer captures screenshots and extracts clipboard data to exfiltrate sensitive information.
- Multiple hardcoded domains are used for command-and-control communications.
- Global targeting evident through multi-language script implementation.
MITRE Techniques :
- Phishing (T1566): Fake captcha verification tactics used to deceive users.
- User Execution – Command and Scripting Interpreter: PowerShell (T1204, T1059.001): Execution of malicious PowerShell commands.
- System Binary Proxy Execution: Mshta (T1218.005): MSHTA used to run embedded scripts.
- Obfuscated Files or Information: Embedded Payloads (T1027.009): Malicious payloads hidden in scripts.
- Screen Capture (T1113): Malware captures screenshots of the user’s device.
- Process Hollowing (T1055.012): Injected processes used to evade detection.
- Command Execution Using PowerShell (T1059.001): Encrypted payload executed via PowerShell.
- Input Capture (T1056): Keylogging capabilities to steal information.
- Content Injection (T1659): Injecting malicious code into trusted processes.
- Application Layer Protocol: Web Protocols (T1071.001): Use of web protocols for command-and-control communication.
Indicator of Compromise :
- [MD5] 9A926390B4E4EF1EEC4E9E6C80382D41 (Filename: v.exe)
- [MD5] 049F8BF92786B0AFF493BC8533EE4FBC (Filename: Lumma payload)
- [C2C Domain] ignoredshee.com
- [C2C Domain] breedertremnd.com
- [C2C Domain] garulouscuto.com
Full Story: https://www.seqrite.com/blog/fake-captcha-lures-victims-lumma-stealer-abuses-clipboard-and-powershell/