A personalized phishing attack targeting employees could result in significant credential theft, as attackers exploit interest in bonuses through deceptive emails. The attack involves a fraudulent PDF attachment and a QR code that directs victims to a convincing fake Microsoft login page. Affected: organizations, employees, corporate networks
Keypoints :
- Phishing attacks remain a significant concern for organizations due to the ongoing use of email for sensitive communications.
- Attackers are using personalized emails related to employee bonuses to lure victims into phishing traps.
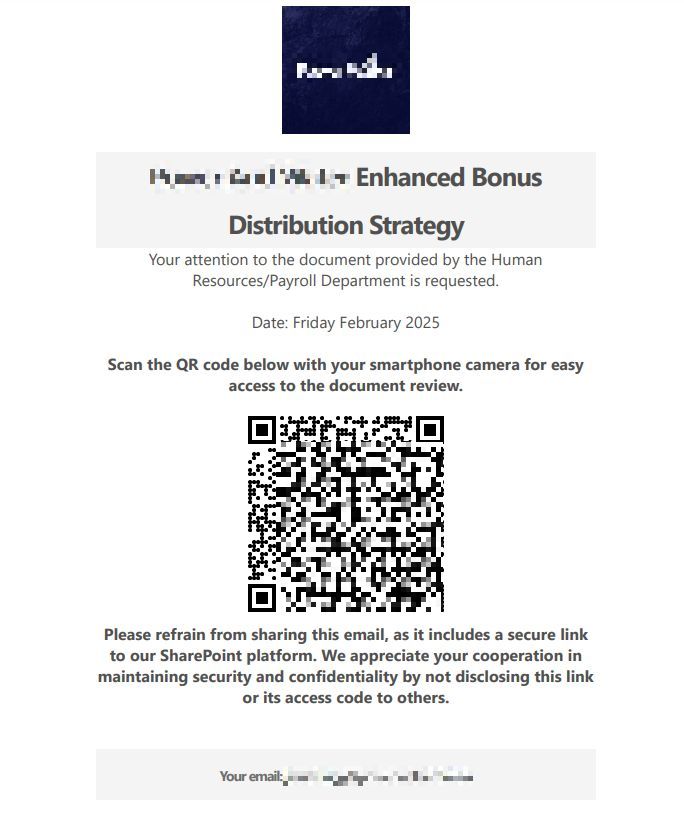
- The phishing attempt featured a PDF document framed as an “Enhanced Bonus Distribution Strategy” from HR.
- A QR code in the email led to a malicious URL that attempted to harvest Microsoft credentials.
- The phishing site displayed a fake login interface that accepted only corporate email addresses, increasing the likelihood of success.
- Upon entering their email and password, victims unknowingly transmitted their credentials to the attackers.
- Attackers benefit from using QR codes to bypass certain email security filters.
MITRE Techniques :
- Credential Dumping (T1003) – Attackers target employees’ credentials through phishing emails, requesting victims to log in via fake interfaces.
- Phishing (T1566) – The use of deceptive emails containing malicious links and attachments to trick individuals into disclosing their credentials.
- Exploitation of Application Layer Protocol (T1071) – Utilization of HTTP/S phishing websites for credential harvesting, facilitating communication with the command and control server.
Indicator of Compromise :
- [Domain] qn.s19pk[.]com
- [Domain] ecshag[.]ru
- [Domain] wh5nbx.revishbos[.]ru
- [Domain] o3mfqg.warthydri[.]ru
- [Domain] cemh.urj7zq[.]com
Full Story: https://www.threatdown.com/blog/enhanced-bonus-qr-code-phish-steals-microsoft-credentials/