Summary: The content discusses a vulnerability in Ariane Systems self-check-in systems used in hotels that allows access to guests’ personal information and keys for other rooms.
Threat Actor: N/A
Victim: Hotel guests using Ariane Systems self-check-in systems
Key Point:
- Ariane Systems self-check-in systems installed at hotels worldwide have a vulnerability that allows access to guests’ personal information and keys for other rooms.
- The flaw was discovered by a security researcher who has not received a proper response from the vendor about the issue.

Ariane Systems self check-in systems installed at thousands of hotels worldwide are vulnerable to a kiosk mode bypass flaw that could allow access to guests’ personal information and the keys for other rooms.
These terminals allow people to book and check into the hotel themselves, handle the payment process via a POS subsystem, print invoices, and provision RFID transponders used as room keys.
Back in March, Pentagrid security researcher Martin Schobert discovered that he could easily bypass the Ariane Allegro Scenario Player running in kiosk mode on the self check-in terminal at the hotel he was staying, and access the underlying Windows desktop with all customer details.
Despite multiple attempts to alert the vendor, the researcher has yet to receive a proper response from the vendor about the firmware version that addresses the issue.
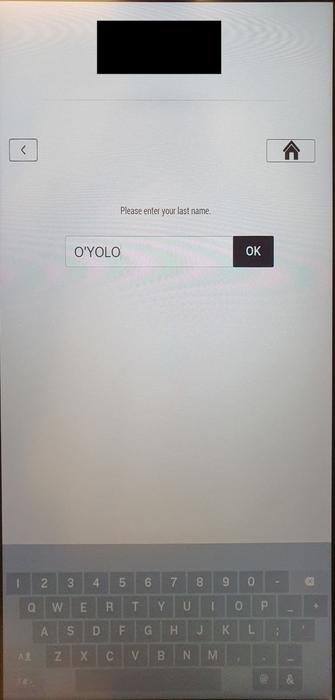
Single quote escape
Schobert discovered that the application hangs when entering a single quote on the reservations look-up screen of the terminal.
When touching the screen again, the underlying Windows operating system offers the user the option to end the app’s process, which terminates the Ariane Allegro Scenario Player and gives access to the desktop.
From there, the user may access any files stored on the device, which could include anything from reservation entries with personally identifiable information (PII) to invoices.
Source: Pentagrid
“With access to the Windows desktop, attacks on the hotel network could become possible as well as access to data stored on the terminal, which includes PII, reservations, and invoices,” explains the Pentagrid report.
“With the ability to inject and execute program code, it seems possible to get room keys created for other rooms because the functionality of provisioning RFID transponders is implemented in the terminal.”
Impact and fixing
The vulnerable terminals are typically used in small to medium-sized establishments where emplying check-in staff 24/7 would be to costly for the business.
According to Ariane Systems, its self-checkout solutions are currently used by 3,000 hotels in 25 countries, which collectively have over 500,000 rooms. Among their clients are one-third of the world’s top 100 hotel chains.
Schobert attempted multiple times to communicate his findings to Ariane since discovering the issue in early March but he only got a short response claiming that the issues had been fixed.
Currently, it is unknown which version of the application fixes the problem, how many terminals are using a vulnerable version, and which hotel chains are impacted.
BleepingComputer has contacted Ariane Systems with questions about the remediation effort but a statement wasn’t immediately available.
Hotel operators using Ariane Systems terminals are recommended to isolate the self check-in machines from the hotel network and other critical systems and contact the vendor to determine if they are running a secure version.
In April, Schobert discovered a similar issue at a self check-in terminal used by a German Ibis hotel. He found that an input of six consecutive dashes for the booking reference number would cause the terminal to return booking details such as price, room number, and valid entry keycodes.
“An interesting youtube video that may be related to the article above”