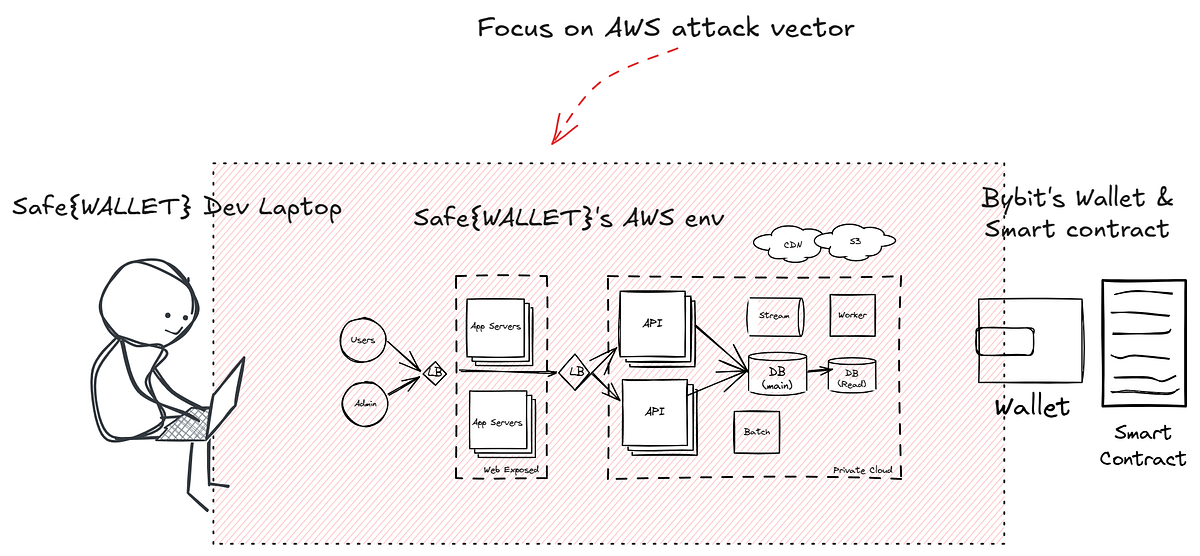
On February 21st, a significant cryptocurrency theft occurred involving Bybit, where hackers from the Lazarus Group infiltrated a supplier’s system to redirect 401,000 Ethereum coins worth approximately .5 billion. The attack exemplifies a supply chain vulnerability that permitted hackers to exploit AWS services while leaving the Bybit system itself secure.…
Read More 



 Day 1-7: Network+Watch videos from Professor Messer’s N10-008 Playlist: https://youtube.com/playlist?list=PLG49S3nxzAnlCJiCrOYuRYb6cne864a7G
Day 1-7: Network+Watch videos from Professor Messer’s N10-008 Playlist: https://youtube.com/playlist?list=PLG49S3nxzAnlCJiCrOYuRYb6cne864a7G CORE
CORE