Category: Interesting Stuff




Keypoints :
The rise of Large Language Models (LLMs) has created new security vulnerabilities.…
Keypoints :
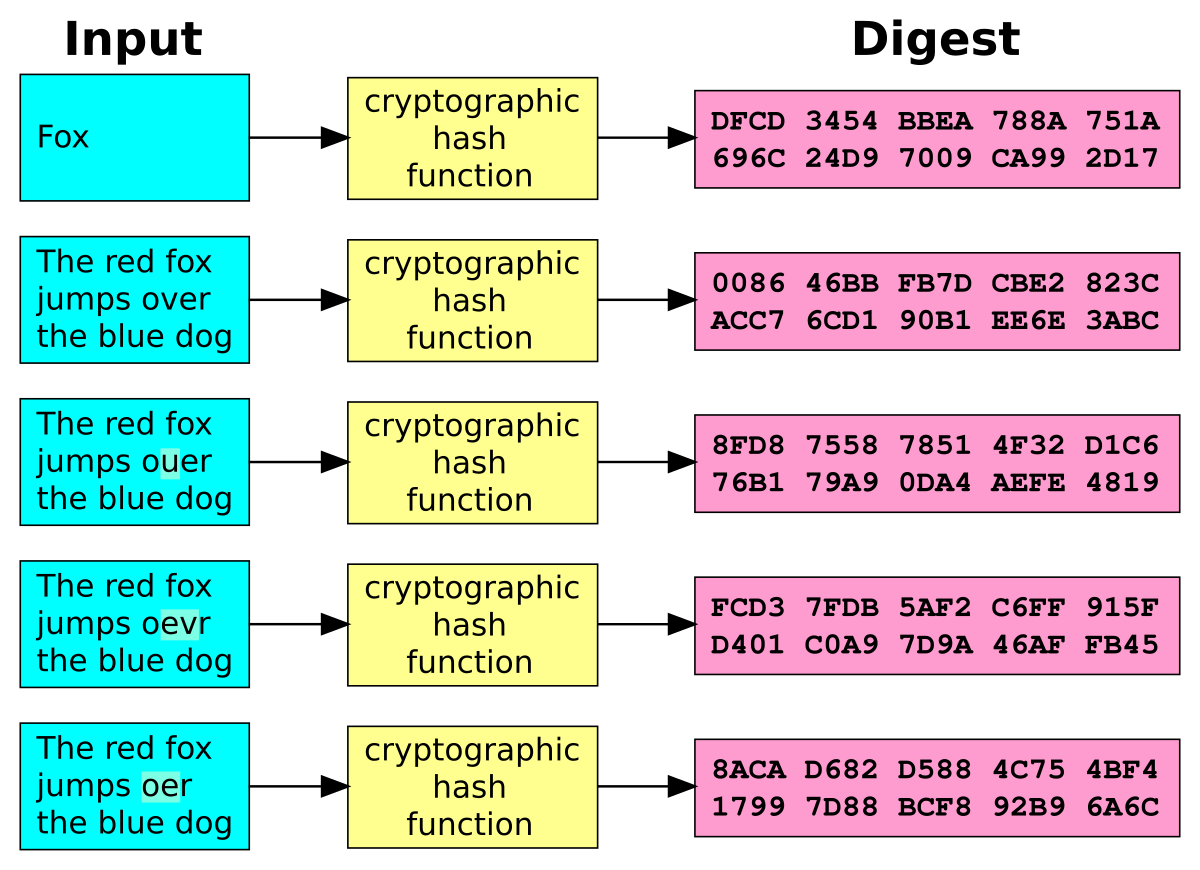
Hashing converts any input into a fixed-size string called a hash value, which is a one-way function.…

Good Source from Raj Chandel’s Blog
Comprehensive Guide on Autopsy Tool (Windows)Memory Forensics using Volatility WorkbenchComprehensive Guide on FTK ImagerMemory Forensics: Using Volatility FrameworkForensic Investigation: ShellbagsForensic Investigation: Pagefile.sysForensic Investigation: Disk Drive SignatureForensic Investigation : Prefetch FileFast Incident Response and Data CollectionDigital Forensics: An Introduction (Part 2)Digital Forensics: An IntroductionForensic Investigation: Preserve TimeStampUSB Forensics: Detection & InvestigationAnti-Forensic: Swipe Footprint with TimestompForensic Investigation: Autopsy Forensic Browser in LinuxForensic Investigation: Examine Corrupt File MetadataForensic Investigation: Windows Registry AnalysisForensic Investigation: Ghiro for Image AnalysisForensic Investigation: Examining Corrupted File ExtensionForensic Investigation: Extract Volatile Data (Manually)Multiple Ways to Mount Raw Images (Windows)Forensic Investigation of Social Networking Evidence using IEFMultiple Ways to Create Image file for Forensics InvestigationMultiple ways to Capture Memory for AnalysisDigital Forensics Investigation through OS Forensics (Part 3)Convert Virtual Machine to Raw Images for Forensics (Qemu-Img)Digital Forensics Investigation through OS Forensics (Part 2)Digital Forensics Investigation using OS Forensics (Part1)Forensic Imaging through Encase ImagerForensic Data Carving using ForemostNetwork Packet Forensic using WiresharkForensics Tools in KaliMobile Forensics Investigation using Cellebrite UFEDForensic Investigation of Any Mobile Phone with MOBILedit ForensicAndroid Mobile Device Forensics with Mobile Phone Examiner PlusHow to Retrieve Saved Password from RAW Evidence ImageHow to Create a Forensic Image of Andorid Phone using Magnet AcquireForensics Investigation of Android Phone using AndrillerLogical Forensics of an Android Device using AFLogicalSANTOKU Linux- Overview of Mobile Forensics Operating SystemHow to Recover Deleted File from RAW Image using FTK Imager and Recover My FileForensic Investigation of RAW Image using Forensics Explorer (Part 1)Forensic Investigation Tutorial Using DEFTForensics Investigon of RAW Images using Belkasoft Evidence CenterHow to Clone Drive for Forensics PurposeComparison of two Files for forensics investigation by Compare ITHow to Install Digital Forensics Framework in SystemHow to Create Drive Image for Forensic Purpose using Forensic ReplicatorOutlook Forensics Investigation using E-Mail ExaminerHow to Create and Convert RAW Image in Encase and AFF Format using Forensics ImagerHow to Mount Forensics image as a Drive using P2 eXplorer ProHow to Convert Encase, FTK, DD, RAW, VMWare and other image file as Windows DriveHow to gather Forensics Investigation Evidence using ProDiscover BasicHow to Collect Forensics Evidence of PC using P2 Commander (Part 1)How to Create Forensics Image of PC using R-Drive ImageHow to Collect Telephonic Evidence in Victim PCHow to Collect Email Evidence in Victim PC (Email Forensics)Forensics Analysis of Social Media Sites like Facebook, Twitter, LinkedInViews: 10…

This repository will contain many mindmaps for cyber security technologies, methodologies, courses, and certifications in a tree structure to give brief details about them. Please share this with your connections and direct queries and feedback to Hacking Articles.
Burp SuiteCensysCrackmapexecDevopsDocker CheatSheetEmpireEnumerationFeroxbusterFirefox Pentest AddonsForensicsGithub DorksGoogle DorksGoogle Search OperatorsGtfobinHTBHTTP Status CodeICMPIDAProISO ControlImpacketJohnMetasploitMimikatzMitre AttackNmapOSINTOtherOwaspPrivacy ToolsRansomwareRed Team DorksSSRF ToolsSecurity 360Serach Engine for PentesterShodanSocial EngineeringSqlmapSubdomain EnumerationTcpdumpToolsTryHackMeTsharkVulnerability ScannersVulnhubWindows PrivilegesWiresharkXSS ToolsZero-Day CVEs (2023)aircrackffufgobusterhashcathttpxhydramedusanistwfuzzwpscanActive Directory Pentesting.pngBurpsuite.pngOSCP…Courses to become a “Zero to Hero” in Cyber Security without marketing , you will have to:
study a lot (we are talking about a “Hero” right?)study “non-technical” and “unconventional” things (Quality = Hard Skills + Soft Skills)study the same thing more than once (Learn = Repeat + Repeat + Repeat)Good point:
The only investment is your time, everything is “on the line”, “free”, “no cost”.…General • Servers • Vulnerabilities • Exploits • Attack surface • Code • Email addresses • Domains • URLs • DNS • Certificates • WiFi networks • Device Info • Credentials • Leaks • Hidden Services • Social Networks • Phone numbers • Images • Threat Intelligence • Web History • Files • Surveillance cameras • Crypto • People
General Search EnginesGoogleBingYahoo!YandexAskBaiduSearXNGEXALeadDuckDuckGoSwisscowsNaverAOLBraveYepGibiruKagiStractServersShodan – Search Engine for the Internet of EverythingCensys Search – Search Engine for every server on the Internet to reduce exposure and improve securityOnyphe.io …
Keypoints :
Exam commenced at 10 a.m.…