The article discusses a sophisticated ransomware attack involving Qilin ransomware, which utilizes the technique of bring-your-own-vulnerable-driver (BYOVD) to bypass traditional Endpoint Detection and Response (EDR) measures. The analysis uncovers the exploitation of a lesser-known driver, TPwSav.sys, in the context of a ransomware-as-a-service model. It emphasizes the vulnerabilities exploited, the attack chain, and the retaliation measures taken by Blackpoint’s Security Operations Center (SOC). Affected: Industries (Construction & Engineering), Cybersecurity, Windows and Linux operating systems
Keypoints :
- Qilin ransomware employs a double extortion method targeting both Windows and Linux systems.
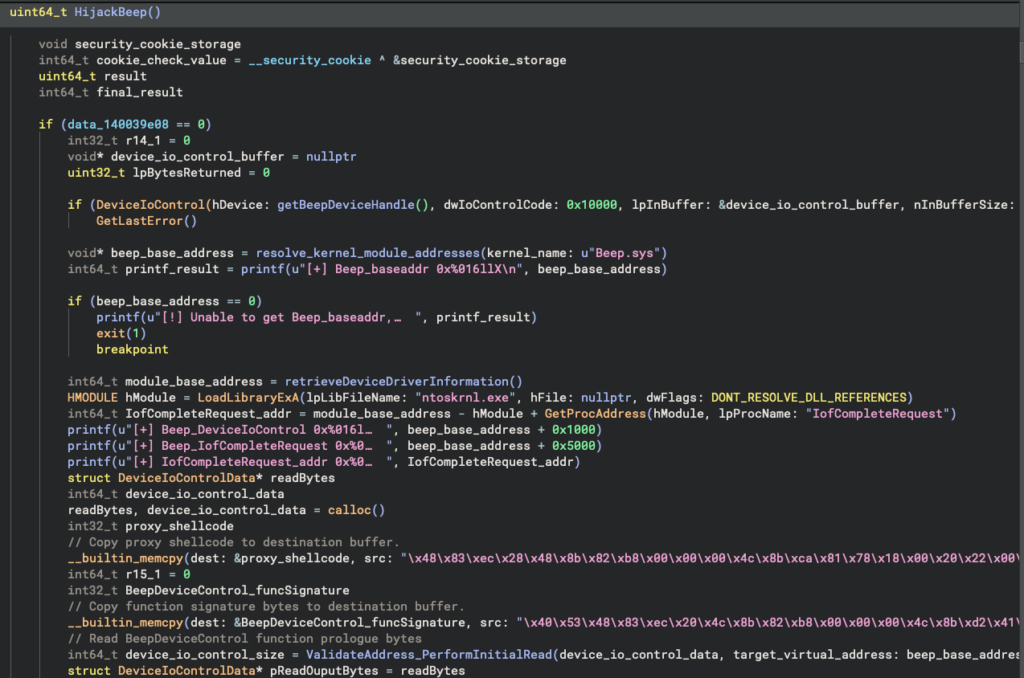
- The ransomware uses a BYOVD technique to disable EDR protections with the TPwSav.sys driver.
- Initial access is typically obtained via social engineering, such as phishing attacks.
- The defense strategy of Blackpoint’s SOC successfully curtailed the attackers’ efforts through isolation and proactive measures.
- Qilin ransomware has multiple customization options for affiliates, including file selection and encryption methods.
- Recent versions, like Qilin.B, introduced new defenses and credential harvesting tactics.
- The incident reveals an ongoing trend where cybercriminals continuously refine their tactics to evade detection.
- Attack methodologies can lead to significant dwell times within victim environments.
MITRE Techniques :
- T1071: Application Layer Protocol – Qilin incorporates various communication protocols for command and control.
- T1068: Exploitation of Privileged Instructions – The attack uses the TPwSav.sys driver for system-level exploitation.
- T1211: Exploitation for Client Execution – The usage of a legitimate signed executable to sideload malicious DLLs.
- T1543.003: Create or Modify System Process: Windows Service – The deployment of a PowerShell script to aid credential harvesting.
- T1083: File and Directory Discovery – Gathering system and file information before launching the attack.
Indicator of Compromise :
- [IP Address] 216.120.203[.]26 (Shock Hosting – U.S)
- [IP Address] 31.192.107[.]144 (HostKey – Russia)
- [SHA-256] 011df46e94218cbb2f0b8da13ab3cec397246fdc63436e58b1bf597550a647f6 (TPwSav.sys)
- [SHA-256] d3af11d6bb6382717bf7b6a3aceada24f42f49a9489811a66505e03dd76fd1af (avupdate.dll)
- [SHA-256] aeddd8240c09777a84bb24b5be98e9f5465dc7638bec41fb67bbc209c3960ae1 (main.exe)