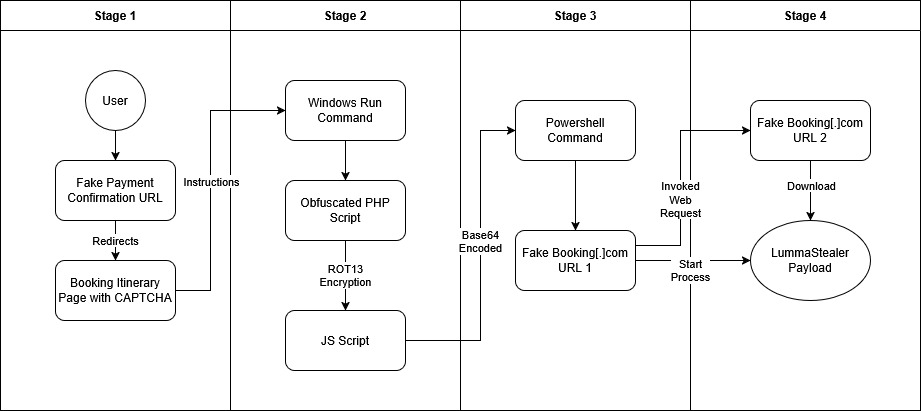
Cybercriminals are exploiting the travel industry’s rising demand by creating fake booking websites and utilizing phishing scams to deceive travelers. They have employed an advanced attack strategy through malicious booking sites, using techniques like fake CAPTCHAs to deploy LummaStealer, a malware designed to steal information. Affected: users in the travel sector, individuals in the Philippines, individuals in Germany
Keypoints :
- New campaign using fake booking websites to deliver LummaStealer.
- Global targeting of victims in various countries, including the Philippines and Germany.
- LummaStealer samples in this attack are significantly larger than previous versions.
- User deception occurs through execution of malicious PowerShell commands.
- The malware employs social engineering techniques, such as fake CAPTCHA prompts.
- Malware has shown rapid evolution in attack methods and capabilities.
MITRE Techniques :
- Command and Scripting Interpreter: Windows Command Shell – T1059.003 – Powershell commands are executed through user input.
- Command and Scripting Interpreter: PowerShell – T1059.001 – Malicious PowerShell scripts are downloaded and executed.
- Ingress Tool Transfer – T1105 – Command and control mechanisms used to transfer tools for payload delivery.
- Clipboard Data – T1115 – Information is copied to the clipboard for execution by the user.
- Command Obfuscation – T1027.010 – Scripts and commands are obfuscated to evade detection.
- Masquerading – T1036 – Malicious files disguised as legitimate installers to trick users.
- Defense Evasion – T1045 – Evasion techniques are employed to avoid antivirus detection.
- Discovery – T1057 – The malware discovers potential targets and exploit pathways.
- Binary Padding – T1027.001 – The technique adds junk data to evade size-based detection mechanisms.
Indicator of Compromise :
- [URL] hxxps://payment-confirmation.82736[.]store/pgg46
- [URL] hxxps://booking[.]procedeed-verific[.]com/goo_pdf
- [SHA256] 7b3bd767ff532b3593e28085940646f145b9f32f2ae97dfa7cdd652a6494257d
- [Filename] FakeCaptcha HTML 71fe618a360c3d077af47ddb17b35de5300c94d3f46fb173a039c01d8ca6b86c
- [SHA1] bfdffcee5951982691af1678f899b39b851b6fd3167d3354c62385fb9b7eac02